The Rise Of RaaS by Ellis Casey
Show transcript [en]
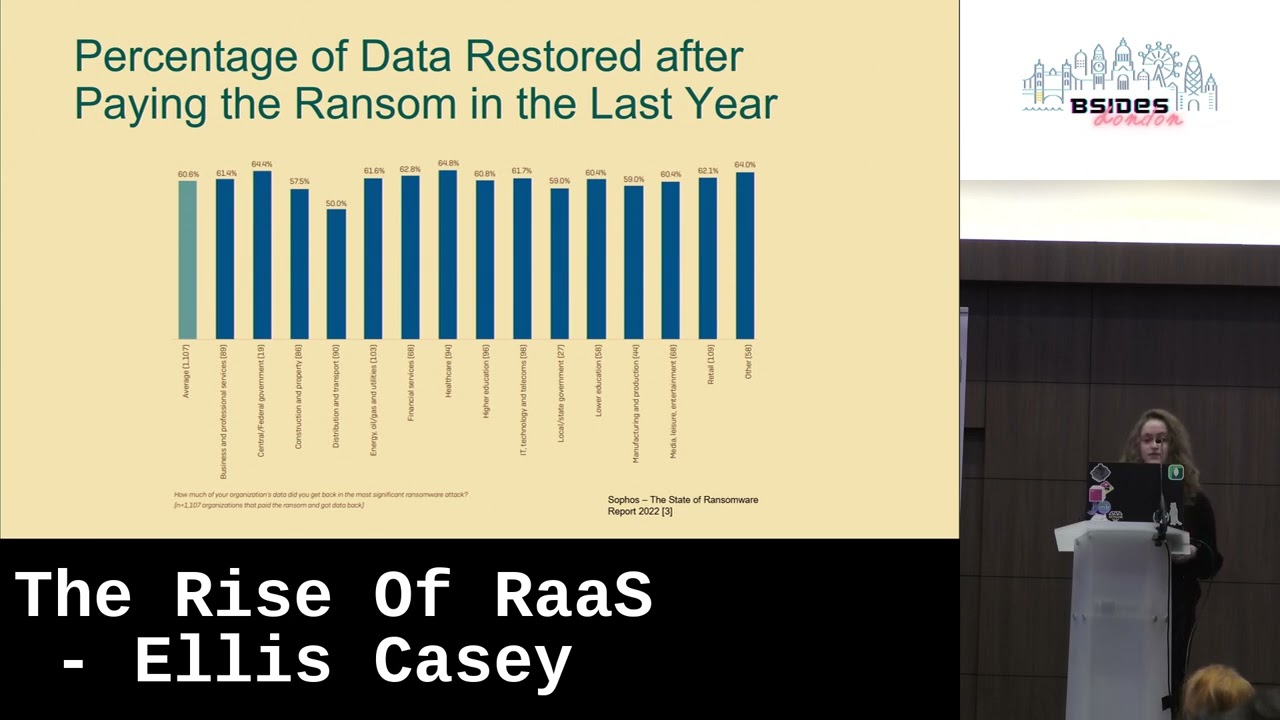
so hello I'm Ellis firstly I'd like to say that this is my first talk at a conference so I'm really sorry if I appear nervous because I really am um to start with I thought I'd give a brief introduction to myself I'm a cyber security research intern at Airbus and I'm currently an undergraduate student studying ethical hacking and cyber security at Coventry University my main areas of Interest are red teaming and networking and in my free time I enjoy playing video games and taking part in ctfs and as you can see I'm a huge keyboard Enthusiast to be honest this slide is mostly here so I could show you some of my keyboards I've built um but anyway on to the main topic one of the projects I'm involved with at work is about endpoint malware detection and Analysis and my research has led me to learning about the emerging threat of ransomware as a service or Raz so I've compiled a timeline of some of the key moments in the evolution of ransomware the definition of ransomware is Shifting with the Innovations in technology used to carry out these attacks in 1989 the first known instance of a ransomware attack was distributed to twenty thousand attendees at the World Health Organization AIDS conference it was released on floppy disks and it didn't rely on any sort of exploit only the Curiosity of attendees at what was on the disk after installing the program everything ran fine until the 90th reboot where the Trojan would encrypt the victim's file names although not the contents of the files and demand a 189 fee to restore the files then there's the archivist Trojan which first appeared in 2006 and was primarily primarily distributed by a spam emails and file sharing sites the first ransomware to use RSA encryption which is commonly used to uh as it was difficult to decrypt because unlocking an RSA file it needs a specific alphanumeric string of characters the archivist Trojan encrypted everything in the my documents directory and can say them in a single file for ransom it required victims to buy items from specific websites in order to receive a key to unlock their files and this crypto Locker that appeared in 2013 this ransomware propagated by an email attachment which was a zip file that contained an executable executable disguise as a PDF when activated this was a that ransomware encrypted certain files stored on the local network drives using RSA encryption the reason this was noteworthy in ransomware history is because it was the first to demand payment in Bitcoin if the deadline wasn't met it offered to decrypt data via an online service provided by The Operators but for a significantly higher price and take your mind back to May 2017 when wannada cry affected devices in more than 150 countries it contained a crypto worm virus that propagated across a computer network using the SMB version 1 exploit known as Eternal blue it demanded a payment of 300 in Bitcoin but no encryption key was available so the victims who paid weren't actually able to recover their files Lazarus a North Korean state-sponsored cyberc threat group is known to use wannacry and it was believed to be behind this attack because of how widespread this ransomware was it brought public attention to not only the threat of ransomware but the importance of good cyber security practices Dark Side largely operates on the ransomware as a service model and it was responsible for the colonial pipeline attack back in 2021 attackers got access to their Network through an exposed password for a VPN account and stole 100 gigabytes of data within a two within a two hour window Colonial pipeline paid the 4.4 million dollars Ransom hoping to restore their it systems faster and while they managed to recover after the attack and got most of the ransom payment back they will forever have the reputation of being the victims of one of the largest and most successful cyber attacks in history so far the stages of a ransomware attack vary depending on the strain deployed but generally speaking it's a similar order of operation first phase of an attack is the distribution of the ransomware some common vectors according to the micro attack framework include a network being compromised by a phishing email exploiting a public-facing application or through external remote services such as RDP once there is a foothold on the target system a connection is established with the attacker's command and control server which is then used to send commands to a compromised system and the next phase the ransomware sets the stage for Attack by credential harvesting and moving through the network providing of course it's not just looking at the local file system an exfiltrating data it finds which is then sent back to the attacker through the command and control server it also searches for files to encrypt and then the payload is executed and all the files are encrypted on the systems it's gained access to through lateral movement depending on the adversary's focus and who their target is they might switch to primarily identifying valuable data and Axle trading it and then finally The Ransom request is displayed where the attacker demands payment to decrypt the victim's files [Music] ransomware as a service or browse is based on the software software as a service model and is advertised as indistinguishable from regular software vendors it allows attackers to Outsource the infrastructure required for these attacks and paying in cryptocurrency allows criminal organizations to operate at such a large scale due to there being no limitations on transaction value in fact billions of dollars in crypto is tied to the top 10 ransomware attacks the problem is that an attacker of any skill level or black thereof can launch an attack making them more accessible and therefore more prevalent as mentioned before the rars model is similar to the software as a service model these services are often advertised on underground track groups and dark web forums and there are several ways in which affiliates um can access the service a monthly subscription for a flat fee or through affiliate programs where an attacker earns commission for each successful Ransom payment there is also a profit sharing model where a portion of the commission goes to the original developer or operator or simply through a one-time license fee [Music] attackers are using Raz to sell exfiltrated data as a form of secondary monetization and as Sir Francis Bacon famously said knowledge itself is power as it can command obedience if a company's sensitive data was leaked their reputation would be tarnished and it would force compliance in order to get that data back sounds like a PR nightmare to me in some cases instead of holding data for ransom it's immediately exfiltrated and sold as it would be more valuable to the hackers this is perhaps related to the somewhat recent Plunge in the value of cryptocurrencies like Bitcoin and ethereum exfiltration tools also in the process of being updated with data corruption capabilities which can also be used to evade security measures I'm now going to talk about an Infamous Saras operation known as our evil deployments of this malware type were first observed in April 2019. they operate predominantly in Eastern Europe or Russia and they avoid targeting systems in CIS countries even using code to detect where a user is located even if you're not familiar with Ross you might have heard of them and if not you're almost certainly familiar with some of the cyber attacks they've conducted they infamously could have conducted a ransomware attack against and the source was identified to be BSA or virtual system administrator which is a remote monitoring and management software package developed by casaya there are approximately between 800 and 1500 Downstream businesses that were impacted by the attack Ari will offered a universal decryption key for the record price of 70 million dollars however Casey received a universal decrypted tool from an unnamed trusted third party and was helping victims restore their files as of 2022 the Russian Federal Security Service says they dismantled our evil and have charged several of its members although I don't believe this is the last we'll see of this ransomware gang as some leads suggest they might return just rebranded according to the Sophos ransomware 2022 report within the last year there's been a 57 increase in cyber attacks overall 66 of organizations were hit with ransomware in the last year which is an increase from 37 in 2020. this means that there was a 78 increase in ransomware attacks this shows the adversaries are upping their rate and the rate and complexity of these attacks in 2021 65 percent of attacks resulted in successful data encryption which was an increase from 54 reported in 2020. it demonstrates that adversaries have become more capable of executing significant attacks at scale and reflects the growing success of the rars model this graph shows the percentage of data restored after companies across various sectors pay the ransom across all Industries an average of only 60.6 percent of company data was restored after the most significant ransomware attack if ransomware hits your organization it's Paramount to follow Disaster Recovery procedures firstly it's essential to isolate any affected devices in order to prevent further spread generally speaking by the time ransomware is deployed attackers are already embedded in the environment so it becomes a race against a Race Against Time to contain the attack it impacts it's important to identify the entry point as it might be due to a known vulnerability which can then be patched along with any other holes in security you might have to make the important decision whether to pay the ransom like Colonial pipeline or immediate however it must be noted that paying the ransom doesn't guarantee that you'll recover your files so I hope you have backups you should check that attackers have not compromised the backup system and if they've been compromised you can avoid pain if they've not been compromised you can avoid paying the ransom and restore the data after the breaches be contained of course [Music] the problem with digitizing everything is that there is little emphasis placed on security and the threat of these attacks are only going to continue to escalate countermeasures should be taken by both the organization and the individuals to improve opsec prevention strategies could involve monitoring application behavior and identifying abnormal processes like notepad opening up Powershell for example not only should there be backups it's also imperative that these backups are tested frequently backups can also be used to detect if there are an excessive number of changes and to alert if something is flagged as suspicious it's also important to secure any layer rate vulnerabilities by Implement implementing regular security awareness training ensuring that users know what actions they should take in the event of a Cyber attack or if they identify a phishing email it's important to use a combination of these techniques and countermeasures because One Security measure is simply not enough think of it like a medieval castle a castle with a strong defense or to have high outer walls a moat a drawbridge turrets and towers with archers in order to prevent a breach into the Castle's core it's best to adopt a worst case scenario tactic by using each next layer as an assumption the previous one will fail the aim is to minimize the area of attack surface layer by layer having layers of defense is critical for safeguarding systems especially against ransomware which works its way through an affected system causing more damage as it goes if an adversary breaks through one wall at least there are other layers of Defense in place to hold back the attacker see Raz is a multifaceted offensive campaign that is on the rise and it's not going anywhere anytime soon the impacts of an attack goes beyond what is paid in Ransom the issue is potential effects of the attack it's imperative that not only you invest in the right technology but have the skills and know how to use it effectively and lastly be proactive this is where threat hunting comes in so you can stop adversaries before they can execute their attack now I know there's so much more I can talk about I haven't even scratched the surface of this topic but thank you for listening to me ramble and I really hope this talk has been interesting and I hope you learned something new [Applause] [Music] has anybody got any questions foreign [Music] what might incentivize someone to offer ransomware as a service instead of doing the campaigns themselves uh well I mean ransomware as a service it offers the ability for people who don't even know how to code or don't really have any technological experience to launch an attack against anyone they want really so it allows it for allows for people who don't really know what they're doing to even launch an attack and basically monetize it [Music] is there any more thank you very much my question is about the creators um of Sid ransomware um with their um what would you think mother motivation would be for Distributing their malware versus just using themselves and getting big payouts if you say that they offer flat fees or subscriptions for their services sorry would you be able to repeat that oh yeah um would it be more profitable for the for them to do their own campaigns and get big payouts in ransons versus just getting a subscription fee from their users I mean there are different strains of like ransomware types that offer these different types of like subscription fees and that so I mean I guess it depends on like what the adversary wants to get out of it I suppose I'm not okay I'm not I'm not too familiar with this um topic as a whole this is just my first initial Research into the topics as I say I've only just started like the project I worked on at work and this is all like really new to me yeah excellent thank you but thank you for your questions yeah anymore does the runs in my service offer a complete end-to-end so somebody effectively off the street could say I want you to go and Target Airbus for example or do they have to have some expertise behind them and they have to get an entry in uh sure there are like any particular entry requirements I mean I mean possessed to these like particular track groups I guess anything's possible really you don't need like a specific Target or anything you can Target just any individual really it doesn't necessarily need to be like a company or anything oh thank you very much I just want to oh okay I just want to say the castle reference I did my first talk on the castle compared to cyber security and all of that Bloody good reference that was really good to see as well so yeah congratulations you're doing a crack until





