Do Loop Back In Anger
Show original YouTube description
Show transcript [en]
so yeah I'm I'm Shane I'll introduce myself in a minute but I'm currently doing I would like to present to you do loop back and anger and hopefully this will make a bit more sense in a couple of minutes so who am I um I'm Shane I also go online by the handle Spyro I'm a longtime lurker I've been in the industry for just over 10 years now it's a bit of a blessing in a curse because I know quite a few faces in this room so I don't know if that's a good or bad thing um spent my first eight years as a you know the classic CTL um uh consultant living off living up and down the
country and then in the last couple of years I've come in from the rain and I'm now working the internal um security team within the finance sector um I'm a Creator the Creator and maintainer of automated Bad Lab which is I guess comparable to ludus um but it's all written in pure Powershell so anywhere that's got hyperv Windows you can spin our vulnerable labs and nessus to XL which as you can probably imagine just another nessus P first speaker so we'll see how this goes um and yeah just another point on altimative Bad Lab um these are all the sort of attacks that are presented um in one of the scripts and what we'll be
looking at today is the S&B reflection attack and then there's a few more there so story time um we were on a pen uh a purple team engagement on the corporate ad um just over a year ago now Beauty about purple team is we're not too worried about the opsec we leave that to the red team Team guys um we humble brag was already da so we're looking at Brett for attacks at this point um we're just seeing what what sticks what doesn't um helping The Blue Team guys with their detection opportunities previously we had some um success with machine coersion attacks I mean Microsoft have given up playing whacka moole with Petty patam or the DSR
PC attacks and the beauty you about again being purple team no opsc we you know as things happen you you're quickly running things you're just seeing what sticks uh for those who don't know when you run nlm relay with no no Flags you just send you just do a Return to Sender so whatever you get received like an nlm hash you just send it straight back so we had that um zor configured and we were doing our attacks and to our complete surprise we dropped the Sam which we were not expecting whatsoever so we've done some investigations with um our infrastructure team uh we found a GP and embedded in there was this disabled loot back check
registry key so what I'm going to do is I'm going to show you the attack and action cuz that can tell you everything more than I can um and then any remaining time I'll just try and do a deep dive and try and get through as much as I can so if you can see it's a fully patched window 2012 uh 22 box um and then just want to pause it here because there's a lot going on here so top left we've got our petty patam on the right we have our enm relay and then down here we have um just some code execution so basically it's just Powershell just reading the register key now disabled loot back check in modern
os's doesn't exist because implicitly is zero um and I'll come to Y in a minute um for the sake of this demo just explicitly put it to zero so we're going to run the attack as we normally would um so we are going to do petty batam on this box we're going to get the machine account uh relay back and see what
happens so as expected we get a failure so again what we're going to do at the bottom left hand corner just another bit of code execution all I'm doing here is flipping the bit uh just using um CR map ex exec to do a code execution so we setting the registry key to one again I just want to confirm that that's Now set to one over drum roll please here so we've got our loot back checkers one we then rerun the attack
and if by pure magic we get the
S don't play that again there we go so the PRX for this attack so obviously the disabled loot back check needs to be set to one S&B signing needs to be disabled so a reason I picked 2022 as the Box see 2025 these days Microsoft are finally pushing out some secure by Design um and the ability to form perform machine coercion attacks now I'm going to not going to go into this um but essentially typically you require some form of authentication you never know sometimes you don't um so sometimes if there is RPC or name pipes you can access you don't even need authentication you can just do this so what is the vulnerability we're
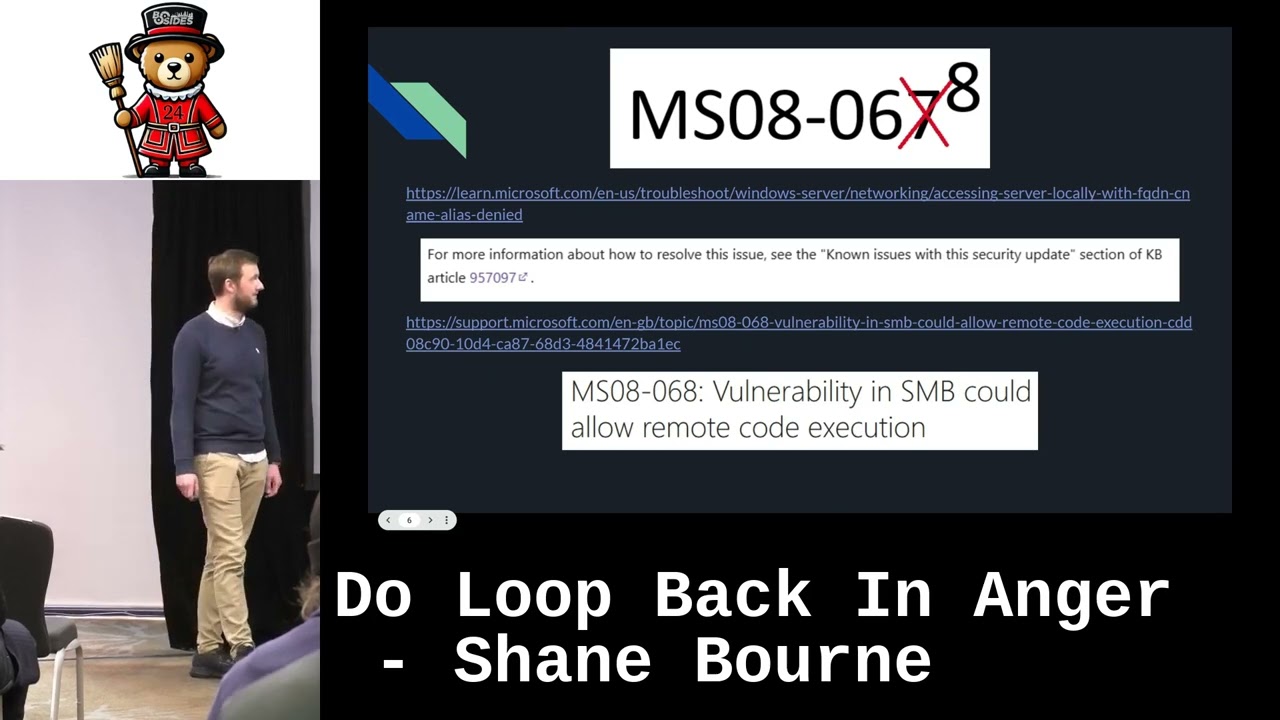
actually exploiting so I'm sure maybe not but ms08 067 very popular sure a lot of people got their Stars and Stripes using this um but we're actually going to talk today about ms868 now this is one of the first SMB relay attacks um that was mitigated back in the day and I basically just want to drive home the point that this is well documented online uh Microsoft have released plenty of knowledge based articles mainly with um Exchange SharePoint um and other services that do use this loot back check and as you can quite clearly see like at the bottom of this page um there is a footnote and it points you straight at the KB
article so I'm just going to quickly go into why this works so back in well again we're talking nearly 15 years now um show my age a bit but before the time of containers microservices and you know arguably virtual machines we used to have to log around very heavy for you delr 200 servers and plug them in and they were multifaceted you had your web server and your database server on the same machine Heavens so when you perform your sort of like delegation or your service account authentication between sort of like you log into your web server that logs into the backend database server typically uses a service account that because it's all happening on the same box it's
happening on the loot back address so because this is happening it's you can see by my great paintwork here it's happening on the same server which allows the nlm authentication and to happen on the loot P address now if we reenable this when we're sending it again Return to Sender we are effectively Local Host so this is why it works so what is the mission for today basically as I said Microsoft is well documented um this isn't a a secret this is probably the worst kept secret but the thing is again like as I said like here is a very Niche attack we happen to come across it but in the security industry I personally I don't think this
is very well known so our mission today is sort of get this either added to your scripts or we have raised this with CIS over a year ago this isn't the mudsling contest it just is what it is we haven't had the best um communication back with them so I mean spoiler alert it's no it's still not in the CIS benchmarks if anyone does happen to know people in C CIS maybe Point them towards us I think this is quite important um but yeah I mean in the meantime just trying to push like sort of um this knowledge and you never know like it could be out there more than more than you actually think
um said like if I've been doing this for 10 years there probably has been other instances where this completely flown Me by um and again like with tenable because they sit on top of the CIS benchmarks they're they're not keen to sort of add their own checks or or anything like that although there is an exchange escalation of privilege that actually does use this disabled loot back check as part of their um attack chain so it is referenced and again it's it's a worst kept secret so that's basically it um so the main takeaway from this if you just if you have your scpt I'm sure a lot of you do have your sort of infrastructure scripts your
checking scripts if you just add this if anyone does Happ no CIS give him a bell tell him who I am um not in a threatening way uh but um and that's it thank you very [Applause]
much question rapid fire y h there uh is there a legitimate use for this setting because it's got to be there for a reason sorry where does that actually come from oh hello sorry I'm looking at the seats well hi there um yes so there there is so I mean as I said like with the where there's an architecture where they both reside on the same host there is that sort of loop back um I guess shortest path almost algorithm so you can relay the entm authentication between the two on the same host so that's the typical use case any more if that's it I mean I can I can just leave this running while people do
their thing and thank you very much thanks for sending [Applause]