The Top 5 Ways I Own Your Internal Network
Show original YouTube description
Show transcript [en]
hi everybody so today we're gonna be talking about the top 5 ways I own your internal network my name is Heath Adams quick Who am I so I am a husband got my wife here with me hacker veteran gamer sports fan and animal dad I am a former accountant turned cybersecurity geek so wasn't accountant hated it and then decided that it's gonna become a penetration tester so here I am on the day-to-day I am a senior security engineer and a business owner at TCM security and I run two projects so project one is called veteran SEC or vet SEC that is a non-profit so if anybody in here is a military veteran or even in
the military basically it is a slack channel that there's closing in on thousand members now so it's just a place to network with other people who are in the same position interested in cyber security you know there's old hats in there that work in the field or people still trying to get in the field people transitioning out as well so it's good good resource for military veterans the other project that I run is called the cyber mentor so that's my youtube / twitch personality so if you're interested in becoming a penetration tester there's a lot of videos on that a lot of how-to guides and a lot of advice there so we do weekly streams usually on Twitch and
most of my content gets uploaded to YouTube so you can check me out twitch YouTube Twitter at the cyber mentor and then the blogs I write for veterans a calm and then visits website of TCM tech comm so why this talk so there's three reasons there's offensive side of things which is you know how can we leverage these and tasks inside of a network and the defensive side is how can we defend against those and the overall big thing is awareness so if you're not on offense you're not on defense at least knowing about these even in your personal life some of these tips in this talk and can really help you out so with that being
said so we're saying internal that means inside of the network so there's usually two types of network penetration test ones a external that's kind of hacking from the outside internals hacking from the inside so I typically you place a laptop on site or a Dropbox but we can say assume breach how we got in regardless we're inside the network so that's what we're defining here for this talk so this talk is also based on my experiences Ben duster you're a pen tester you've been doing it your top five may vary this is just what I've seen when I've been doing pen tests and then please hold any questions until after the end you can come see me I have stickers you want
stickers so the first one is a lemon are poisoning so what is a lemon are that is link-local multicast name resolution so it is basically acts as DNS when DNS fails to do so it was previously known as what's called MB TNS NetBIOS so the key flaw here is that when a the service utilizes a user's hash to actually respond to so you'll see here in an example when we use a tool called responder we can actually capture ntlm v2 hashes and we can take those offline try to crack them and do some other malicious things with them here so let's take a look at an overview of this so let's say that we have a victim and this
victim is trying to connect to a file share in the file share it's called hackney but for whatever reason they type in hack em DNS doesn't know what hack em is and the server doesn't know what hack em is so it's gonna say I have no idea what you're talkin about so it's the victim we're gonna send out a broadcast message to everybody we're gonna say hey does anybody know how to connect to this and we're gonna be sitting in the middle with responder we're gonna respond to that room say yeah I do send me send me your credentials I'll get you over there and then the victim is gonna send over the hash so let's take a look at what that
looks like from me real life perspective so this is what responder looks like with just a Python tool will run responder will listen for these events on the network and this is something that is an attacker if we're doing a penetration test this is probably one of the first things I I run before I do scanning before I do anything I'm running this because around 8 o'clock when people are getting in a lot of traffic around lunchtime loud traffic events are generated and we start pulling in hashes pretty easily so let's say an event occurs here's again somebody trying to access a file share that they can't access and we get a hash so old Frank Castle here on the Marvel
domain we could see his IP address his domain and his user name and you get this really long hash so what we could do with that hash is we could take it and we can put it into something like hash Pat and if your passwords weak we're gonna crack it so you can see password 1 here we get it cracked and no problem now we have Frank we could try to pass that password around the network or do other malicious item which we'll talk about here in a second so when we talk about mitigation with this the best defense is to turn off LM n R and M be T and s you got to turn
them both off is he going to turn one or the other they'll still be in play if the company cannot for whatever reason turn these things off then we do recommend network access control so at least that there's some prevention on site and we require strong password so ideally the password policy and you should utilize this in anything is at least 14 characters if not longer the longer and more complex without using common words so the longest password I've cracked is 19 characters and that's because it was a Bible verse so just because it's long doesn't mean it's it's good and you know just because it's complex doesn't mean it's long enough so we really need that that length plus
that complexity if you got like a 40 character sentence or something crazy that will work really really well so it doesn't have to be crazy complex of yet length but you do have to have a link therefore for us to be able to not crack these so moving on into number two number two is past the password or past the hash so if we do crack a password or we can dump Sam hashes we can leverage these for a lateral movement in the network and so here's what passed the passer looks like you see that we are passing this password now of the user F Castle with the marble domain and we're taking that password one that we found and all
we're doing is we're spraying the entire subnet to see if that password works on any other machines because we know it works on his machine but what about everywhere else so if he isn't a local administrator on another machine you're gonna see that pwned light up there and basically we know we can go access that machine as that user and gain a shell and that machine as well so you see this a lot in networks password reuse big time especially local administrators or like a tech support account there was a pen test a couple weeks ago I had that had cyber-ark on it and all their passwords were insanely long weren't cracking them but their local passwords
were really bad and they were reusing them all over the place so we were able to leverage those to get around the network even though they had amazing you know spent millions of dollars on security the local administrator side of it really really took him down so other option here is we can get the hash so say we do have a shell say we grabbed you know grab the shell and we can dump that administrator that F Castle or if there's a new minister of hash that hasn't been disabled we could dump that hash and we could also run that through crack map exec here and same thing instead of supplying the you know the
domain we're just gonna supply a local user hash with capital H and - - local fire that away and see where we own the only machine that we owned here was his own so we didn't really get anywhere but a lot of times this does work so when we talk about pass the hash pass the password where comes the mitigation these are hard to completely prevent but we can do some things to make it more difficult so one thing is to a limit account for you so if you've got local administrators you know really don't give people local administrators and absolutely need it there's not really good reason for a lot of people to have
it another thing is disabling that guest in administrator account and just limiting access and again limit who is a local administrator at least privilege here a lot of users want that to install stuff and it just it just ends up bad for more reasons than just this so that's one reason another reason is another mitigation is to utilize strong passwords again so if we can't crack a password or even get onto them then it's gonna be really hard for us to actually pass a password around in the first place and the last one is Pam so I talked about cyber-ark so Pam's privileged access management basically that's like an account check-in checkout things so you store your accounts in
something like cyber-ark and then you go and you log in you say I want to check this account out you check that account out it belongs to you it gives you a password that's like 15 to 30 characters long and you own that account with that password for 8 hours or so and then it checks itself back in if you don't check it back in so that password is always rotating so even if we get on to a machine we dump ashes dump passwords they're constantly rotating we're not gonna be able to do anything so that's why when I was in that engagement at least on the Active Directory side of things I had no chance
against cracking those accounts they're way too long way too complex but again the local admin accounts can be dangerous so third one is what is called token or personation so those are temporary keys that allow you access to a system and you could think of these basically as cookies these are cookies for your computer so there are two types that you can see one is called delegate the other one is called impersonate so delegate is like you logged in with Remote Desktop you're gonna leave a delegate token behind the other one is non interactive so if you have like a network drive or some kind of logon script that you use then you're gonna leave behind it in a person a cookie now
these cookies stay there as long as that computer has not been restarted so if you have a computer up and you call helpdesk helpdesk this domain admin they login to your computer through a remote desktop you're leaving behind a delegate token as that user so let's take a look at why it's bad so let's say we get on to a system and at the top you can see that we are authority system so we own the machine but there are tokens available to impersonate here with this tool called incognito this is actually built into Metasploit or meterpreter so I'm going to impersonate this user of Marvel F castle and we're gonna go into a shell
we're gonna say Who am I and now we are Marvel F Castle great from here I'm gonna try to run me me cats which is just going to try to dump passwords so I'm trying to dump passwords off of the domain controller and if this is domain administrator this might be able to work for us here you see that we have an access denied the access is dying because Frank Castle is not actually a domain administrator but what if a domain admin token was available so now you see that the administrator has Remote Desktop in this machine left the token behind and we're gonna go ahead and impersonate that token now we say Who am I Marvel administrator
try this one more time and we just dump all the hashes and in this sense we basically own we own everything we can take these offline and try to crack them this Kerberos ticket granting ticket hash can lead to what is called a golden ticket attack and that we own every single every single computer in the network with a golden ticket attack at least in the domain so a big big deal if you capture that hash there and so when we talk about mitigation we can limit the user group tokens here a bigger strategy is account tearing so you'll see some places utilize this and more and more are moving to it but like you might have Bob
and Bob's a domain admin so Bob will have a regular account user account and then he'll have a domain atom account and that domain I have an account only logs into the domain administrator or like domain controller or where they're needed and they won't be utilizing that to log into something like you know a user's computer or a server or something else they'll be using their local account to do that or there there's a locally or their domain user account to do it not a domain admin account so again local admin account restriction is big here because we need a system shell to actually pull this off so if we're not a system on the account like a
highest level then we're not going to pull this off and the reason we get the high level system access is when a user is a local administrator so once we get that local administrator shell then we own this we can start doing token impersonation and this attack becomes pretty dangerous so number four so this plays back into number one number one was LM in R and if you remember we actually gathered the hashes took them offline and cracked them instead of doing that we can actually pass these hashes and just let's do what's called a relay so we're gonna use SMB relay attack so there's two requirements here so one thing is that SMB signing has to
be disabled a good thing for us is SMB signing is disabled by default on all workstations servers it is enabled so basically that SMB signing says you are who you say you are so what we're gonna do is we're just going to pass this hash along and say hey we are this person let us into your machine if that person is a local admin on that machine we can dump ashes we can get a shell there's a lot of malicious things that we can do with this so I we need we need that signing to be disabled so this is mainly a lateral movement attack and then we need that local admin privilege again so let's
take a look at what it looks like so a couple things we're going to turn off in the responder configuration we're going to turn off SMB and HTTP is we're actually gonna pass those along instead of actively listening we're gonna run responder again just this time you can see the there's a little bit more red in the offs down there in the middle under the servers we're listening on and we're also gonna spin up what's called an TL and relay X pi another part of this impact toolkit all these tools I've been using here are part of impacted tool kit for the most part so we're gonna specify a target file and we're just gonna let it fly so
again when an event occurs like this instead of the hash coming to us the hash goes to that machine that we specified in the targets file and if that user is a local admin you can see down there we just accessed another machine Peter Parker's machine and we started dumping all the hashes on Peter Parker's machine so now we've got new hashes available to us so we can go and try to pass around see maybe where Peter Parker has access to repeat step two that we saw and keep trying to move laterally along until we find that domain credential or something that we can get access to inside the network so a lot of this is about lateral movement
until you find that way to escalate up there's a bunch of different strategies we can we can have here the enabling SNP signing will stop this attack you will have some some admins complain about that because there is what they say it's about a 15% increase in the time it takes to transfer a file to a file share although the file share but for security purposes I don't think that's that bad you can also disable ntlm authentication but if you use that it stops the attack but if if that fails and it falls back to Kerberos then it's going to it's gonna be happening all over the place again so again we could talk about
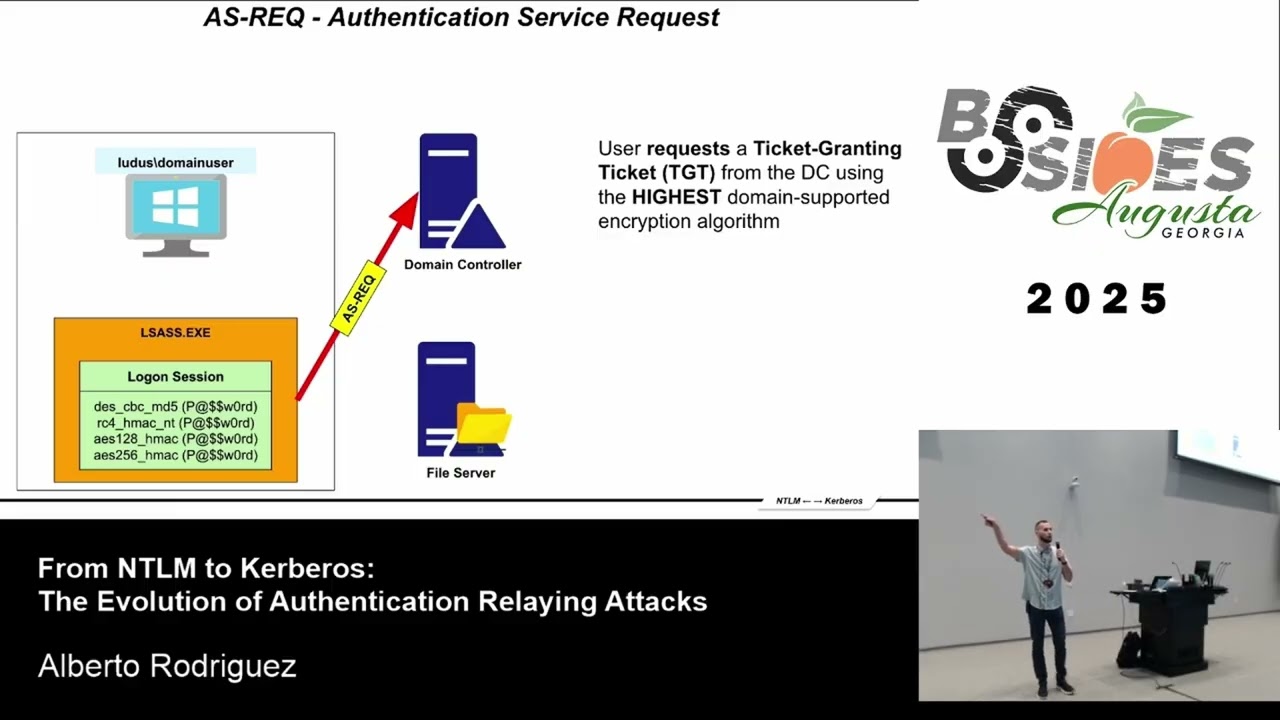
account tearing if we're not utilizing domain administrator accounts or utilizing those on machines we're still gonna have issues with this and the local admin restriction if we're not a local admin we can't have this happen so again it all plays down to these local admins and a lot of its local admin and password is really how we we navigate these networks okay and the last one is Kerberos tting so Kerberos is a authentication method for Windows it's how you use it in a domain so let's talk about how it works and we'll talk about why this is bad so we have a late domain controller and we call it domain controller the KDC which is the key distribution center and
if we have a valid credential so say Frank castle with password 1 we can request a what's called a t GG it's a ticket granting ticket so we as the user can say hey KD C I want to request a ticket the KDC is going to send back that ticket to us and we are going to have a ticket then we say ok there's maybe an application server or something like a sequel server whatever it is or something running that we maybe want access to now what these have is what's called a service principle name or an SP n so say we want to access this application server we're gonna act ask for a service ticket or a TGS so we're
gonna take that we're gonna say hey domain controller here's my ticket my TGT can you give me a TGS while you're at it and the domain controllers going to say sure and while I'm at it since I have no idea if you can authenticate to that I'm going to encrypt the hash of that that server account or that that account with this ticket so then what you're gonna do is you're going to present that ticket to the application server it's going to decrypt it check your permissions and then say if yes you can can access me or no you can access me we never need to do five and six because we have valid authentication or
we have a valid ticket we just get that that ticket back with that encrypted hash and then we take it offline and try to crack so let's take a look at this and make more sense of it so we've got this this marble frank castle with password 1 and the domain controller is living at 10.0 point 3 point 4 and we're just making a request and what comes down here are the you see the service principal names so there is one sequel server running here a sequel service running and you can see the member of says domain admins all the time we see this people put service counts in their domain admins and if we're able to now
take this hash that we just got because this happens regardless as long as we have a valid ticket we have this hash we can go take it offline if we can crack it we now own a domain admin account so take this offline this is a 14 character password again this is why even 14 characters isn't that great because this will run with RockYou and bracket so crack this password and we could take that and leverage it so when it comes to mitigation strategies really because this is a feature built into Windows already you need strong passwords really strong passwords for your service accounts and again it comes down to lease privilege with with all this
question
good thank you guys [Applause]