Hunting Defense Against The Dark Arts
Show transcript [en]
[Music]
okay cool [ __ ] all right all right all right how you guys doing today you guys having fun the first Philly b-sides or what yeah I got to start it out I can't tell you how excited I am to be presenting at the first-ever Philly b-sides I started my career here in Philly both NIT and security so to be a part of event like this is is really pretty awesome obviously I'm pandering to my Philly crowd here I I haven't followed the the roster for a long time but I go back to like curse and and Westbrook and all those guys so a little bit ago so who the hell am i well my name is Daniel
Kowski and at DIA Kowski on twitter also important the note that I didn't write this alone I wrote it with Jacky Stokes and Stephen Hank you guys can find them respectively at find evil and Stephen Hank what do I do I hunt stuff I have fun in stuff a bunch of different places right now I work for a company who either doesn't want to be named or doesn't want to be associated with me so I don't put it in I don't blame them you know any club that I'm a member of I worked at mandiant actually a couple times and g4 a little bit down in New Orleans yeah I've got a long sordid love affair with with Philly like
I said started my career here both IT and security proposed to a girl in the Art Museum steps she said no so and uh enthusiastic awkward hugger as you can see in there too so I can also show you on the PA Turnpike where I tell us to ring off the bridge so there's that but I love this city and I'm really happy to be here to talk about hunting so let's get to it what's the problem set we want to find evil or we want to find ways for evil to do evil things right it's not all about sex Capt Russia China whatever hun things about a lot more than that and it's about ways that your environment is
going to be vulnerable in ways that you really even have aren't paying attention to and the end goal of all this is to is to build a program and mature it working complement your capabilities of monitoring and detection so it's not just a one-off thing this has to be a constant feedback loop right and it's it's something that never stops but it has to feed into all other aspects of average security program so what have we done so far and what we try and do now so pretty much what we've done so far that I've noticed when I was at mandiant as a consultant see a lot of different environments and it really is it's been just kind of
trying to throw a tool at the problem right and that's that's not gonna work anymore it hasn't worked for a long time the central theme really has to be people process and technology with the emphasis on people with the emphasis on the hands behind the keyboard because inevitably your tools are gonna fall down your tool of choice will fall down at some point and you're gonna have to pivot to something else so even me I've fully admitted I've been heavily depend on a single tool when I was a mandiant it's their product called a threat analytics platform and now that I'm not there I have to pivot to something else so this is really what it's all about
it's not tools it's definitely not alerts alerts are important and alerts are a potent part of triage and it's not necessarily about the automation although it's a it's a set of methodologies that's gonna bleed into all three of those and for analyzing large datasets in search of incidents and to add context to your future detections right so you can go back look at your after-action look at your lessons learn and fear then that way this isn't gonna be this whole presentation is going to be a a B and C okay how do i hon how do I do a B C and D it's really going to be a lot more spread out than that and this is to
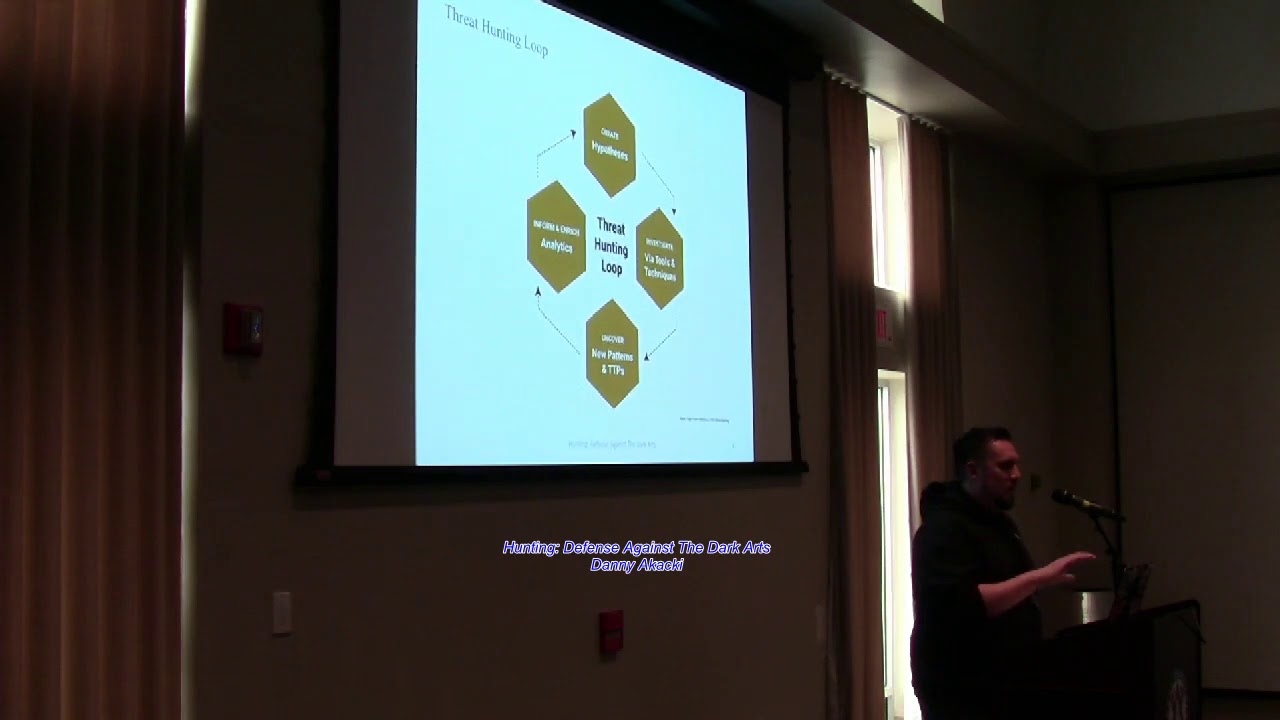
build a use case that when thinking about spinning up your programs and your processes hunting has a methodology so what exactly do I mean when I talk about methodologies right it's it's not a linear process it's more think of it as like a Rorschach painting as opposed to you know whoever paints stuff in straight lines I'm not a historian assuming it's really about being able to pivot through a lot of different data sets and through a lot of different points and it's also gonna be iterative so you're gonna have to go through the same process again and again improving each and every time it's also gonna be a hypothesis driven right so you have to start with an idea whether
that's something like I want to look for you know large outbound data transfers right you have to start with at least a kernel of an idea and what we kind of centered this presentation on was you know disproving something like your hypothesis can be I know that all of my controls are solid I know I don't have any wonky protocols on my network all right well now go and prove that because I guarantee you're gonna find something I can't tell you how many times through our engagements we found hi RC running on corporate networks or RDP coming out of a domain controller like it happens and it's their ID no matter how much the clients are gonna tell you that no man
we're good it doesn't happen and you got to think about layering your hunt methodology is just another layer to your overall detection strategy and it's going to be outside of the pre-existing definitions and since it's going to be outside your your your normal signatures and that kind of thing so this is this is one of the kind of the best TLT LDRs of hunting that I've seen it comes from squirrel show hands people familiar with squirrel there you go a few of you if you aren't highly recommend going out to the squirrel blog they're doing some really great things on hunting analytics machine learning that's stuff stole over my head but they've got a great blog so I definitely
recommend going to that so you start with your hypothesis right you you want to attempt to debunk your assumptions about your environment which I'm gonna go over a lot later in the presentation so you start with an idea you start with you know just really anything and if you're a small org you can you know you can think a little bit smaller you know I want to look at like I said you know bad bad protocols going across your network should be controls I think my proxy is configured properly right I'm gonna see true destination on everything and then you really go look at the logs and all and all you see is like hey maybe my sensors aren't really
placed in the right place because I don't see I see true true destination I don't see true source so that's something that's that's gonna be revealed through this and then from there you have to go through your your tools and your analysis techniques right to attack the problem set because you want to validate what you think is or isn't happening on your network and from there you will your gonna uncover new patterns and new tactics that weren't initially covered by what you already had for your donation detection strategy and from there we're gonna use that to inform it and enrich your process and you're gonna start all over again right this entire loop is useless if you don't
have the end game of putting it back into your processes that you already have so we need some certain things to build a foundation by the way if you see the Harry Potter theme that was Jackie's idea so that that's going to be kind of going through the presentation more pyramids anybody familiar with David Bianco one two three okay cool again if you're really interested in hunting hunt process this hunt methodology look up David Bianco and read everything he's ever written he started with this thing called the pyramid of pain and we kind of bit off of that style a little bit so from here we start at the very bottom of what the foundations are right if you're gonna be
building a mature robust hunt capability you have to work your way all the way up this pyramid now this isn't to say that you can't be hunt capable because you can do you can do hunting with just the minimum minimum amount of budget and people you can do it with one guy and like an elk stack set up but if you're going to want to have this matured you're gonna want to try to go up to this pyramid so first we start with a formalized security program right it's most important here you're gonna need a sponsor right you're gonna need somebody in leadership that buys into what you're doing and you're gonna have to explain
it to them because it's not their job to know what you do but it is your job to explain it to them why is this important what's our end game how is this going to protect us moving up the pyramid a sock and a cert right you're gonna have some kind of formalized process or at least hopefully some kind of group that's eyes on glass you're going to want to have analysts in the seats and hopefully some kind of process for if you do have an incident and and and some that's it to go through your IR and from there you'll see right on the third thing kind of must be this tall to ride when it comes
to building a capability right you're gonna want all of these things pretty solidly in your favor before you can even think about doing any kind of proactive hunting which is you know your technology and tools you're gonna have to have your stack in place because you know reppin through 20 terabytes of logs doesn't manage we've done it and it sucks and it's not conducive so you're going to want to have your technology stack set up before you get to this point use cases and play books right none all of this is useless if you don't build new play books new use cases you want to be able to sit a junior analyst down and iron her back when I first
started all this or I worked for David Bianco and he taught me pretty much everything I know and the the the prevailing thought was it doesn't matter how you get there just that everybody got to the same thing and that's totally not the case it shouldn't have been the case then it's not the case now you want to be able to at least build these in such a way where you can sit any junior analyst down and say hey here's how you can start and get their brains thinking about it there's another guy Chris Sanders look him up Chris Sanders 88 on Twitter he does a lot of work not only with hunting and securing
all that but he's also doing like his PhD in psychology and applying it to all this so that that goes into it as well and so now we mature we have a program where we have those capabilities where you can improve things like governance overall detection and again you can do let me see it over here is that not coming through yeah cool so you can be like right around here and be hunt capable right you can stand up elk you can stand up security onion put sensors out you could have one dude in charge of it and at least you've started something so it's not like oh I need all this and or else I'm useless no it's like it's not
that at all which I'll cover that later on as well so too long didn't read tools information and somebody who's gonna care and be able to bankroll you for all the stuff that you're going to want to do so another really handy thing from squirrel is a hunting maturity model to kind of give you guys a baseline of where a lot of companies are right now so as they see it and I happen to agree with a lot of this is you know most orgs right now they're they're out a battle one you start at zero you're primarily you have a sim and it's cool when you have alerts coming through some some random Intel service that you have and
that's alright then you move up to maybe it getting your own Intel putting it back through you know talking to your IR teams your red teams and putting that information back into into your own hunt programs moving up to three and four there's really not a lot of orgs that are even past one or two just now from people I've talked to industry you're gonna look at the guys like Target and like the GES of the world they're the guys that are really that are really killing it on this so this is just kind of like a level set about if you want to establish where you think your hunk capability might be so building a hunt
program so where do we start where are we going and what's this actually going to take to get there at a minimum we have to iterate through with your few projects before you actually get to the point where you can hunt I mean it's gonna be a lot of trial and error and you're gonna be able to but in that in that process you're gonna be able to find the gaps some of these will be easier than others based on the resources that you have available to hopefully you have that executive buy-in establish and implement an enterprise logging strategy right so it's gonna be what devices do we have do we even know what we have once the last time we
talked to net ops when's the last time we update our network diagram these are all things you're gonna have to take into consideration if you're going to want to move to the next level what do other departments have I worked in places that have that have such a large Splunk instance that you have multiple search heads and I buy a time I left the place I still didn't know who had what search head and what data I could get from them so communication is key right you you can't operate hunting in a bubble you're gonna need to talk to your departments considering things like logging levels right not everything logs equally and some devices have security
settings that aren't even turned on to log or maybe they're not at the proper levels you can talk about PowerShell right like who knows that all of their all of their windows boxes have the most recent version of PowerShell turned on that have more features than the lower versions let's let's you have to kind of take into consideration and then from there you have all your data you have to have a centralized place to aggregate it and process it and mention Splunk earlier ELQ stack and mandiant we had tap and then it has to get normalized right because you're gonna have a lot of spare log sources coming through that might not that might not jive with each
other right like you might have a few different you know Cisco devices you know a SAS and routers and such that are gonna maybe call certain fields certain ways I remember back in my first time at mandiant you had you know with stuff coming from arc site and this was in the very infancy of tap right where we were still building the parsing on our own and just a few different spaces broke the parsing and nothing was coming out and you couldn't pivot on anything so that's something you got to take into consideration and then none of this does do any good if you can't search it fast anybody you Splunk a lot sure hands
alright few people so you probably know you've done searches that you can spin up and go to lunch for an hour and a half and they still won't be done by the time you get back and then you get an email from your Splunk admins cursing your name so you know it's it's not it's it's not it's not convenient to have to regex and grep transforms manually when you can have a tool that can manage that for you I really put too many notes on my slides so from here this all drives for maturity right being able to develop those use cases determining if you're actually getting the right and then going through your tool sets
right you you might you might say hey we don't have anything that can do what we needed to do and you're gonna find that out as you go through this process and then you can reintegrate that into your hunting mission and then from this you're gonna the most important thing you're gonna get from this is metrics right because at a certain point you have to answer to somebody and somebody's gonna be like hey why are you concentrating on this when you could have been doing this and you're gonna the sad thing is you're gonna have to go to them and say hey everything is working great we have 300% more incidents and they're gonna look at you like you're an idiot
but that's a good thing because you're gonna find more things but your time to detect is going to go down so that's going to be a really important part of that and it's it's gonna be a total team effort right you're gonna have to communicate with you know your your IR team your your your sock and your your cert and it's not always there's politics involved right so you're gonna have to navigate that but communication is is really really key and so just to kind of visualize how this process should go when you're hunting you're gonna find really kind of one of two forms of data either it's gonna be well actually three it's gonna be nothing at all it's gonna
be your run-of-the-mill stuff or it's gonna be evil you know you're gonna say hey this is really wonky we have to we escalate this IR or it's gonna be not evil but it's gonna be it's going to be visibly a risk right so one of the in in the engagements that I've done one of the biggest risks that we had is out-of-date software right so you have 75 different versions of Firefox going but nobody's looking at that like their patch management just isn't there but through the engagement we were able to show the client that and when we showed it to him he just said hey we have a business to run we can't worry about
Firefox I said okay let me try to come up with a better way to explain this to you because that's a huge attack surface and it's and then from there you know your your IR you you can feed your hunt feed your IR and vice versa right so how does that GE we work shoulder-to-shoulder with IR if they were going through an active incident they would ask us to help scope it like hey we saw these boxes for pop go through Splunk see if you can scope this otherwise or if we were working something say hey have you guys seen this yet and that maybe they were literally the aisle over and that was awesome but that's not
always the case but it definitely helps and then and then this has to and I our outcomes will affect your security operations who should be updating your lessons learned your use cases they should be an active part of the process all with the intention of upping your detection capabilities so use cases I've talked a lot about them so far they are scenarios to help you uncover your problems and guide your thinking right so having having a set playbook a set amount of use cases and how are we going to construct them right so here's the goal I need to fulfill the goal and who's gonna care about this and why what has to be what has to be there for that
detection to occur is it a rule and sim is it kind of you know a choose-your-own-adventure for your analyst where they can go through their own mental steps to get through the process it doesn't have to be complex use case doesn't have to be a 75-page PDF that's notarized by four different people it could be something as simple as an Excel spreadsheet right but it's important that these things start getting written down it doesn't really matter how you got there that there she got there now that doesn't that doesn't really Jam anymore but the eventual goal is with each use case to get it further away from the human where you have it automated enough so that you can work on
something new and then do it all over again and then yeah so these are going to contain your internal tactics techniques and and procedures your tools and your logic and your data what are the events of interest that are going to prove or disprove your use case and just kind of expanding on the use cases again that use case is kind of a wrapper right or and then from there you're going to look for your events of interest that can prove or disprove it and then if you find it it's going to turn in to an incident so to kind of outline we didn't used to have these slides in this presentation but we got a lot of
questions on what exactly is a use case how do you construct it right so here's a little example of it what we did a lot at at mandiant is we would base our use cases off of one of the different kilt change whether it's the mitre model the Lockheed model but it helps to kind of have something to build around it and so say you want to do a use case around you know establishing footholds completing their mission data X all that kind of thing and then you can stage it through each of these separate ones and say okay if I want to look for the initial compromise what am I gonna need to see I'm going to
see beaconing malware installation see two servers that kind of thing so it's really sent around the behaviors from the throw actors as they try to complete their mission in this example we can drill down a little further into that and see okay what do we need to make this happen so if I want to detect an initial compromise and by the way the Aoi is activities of interest that's just it's just another piece of terminology that they use so you do this by doing a design tree and suppose I can help you identify where your gaps exist if I want to detect this and I want to detect you know beaconing and tools in situ okay do I have do I have net flow
because not everybody has full pcap for you know six months and net flow can be very very valuable you have AV logs even coming in how's your sim configured and all those different kinds of things to help build those individual use cases so for the outcomes what do we think that we want to accomplish here and what are you gonna have to tell your management when you sit down in your meetings right the most important thing and I really want you to remember this there is no such thing as a failed hunt right nothing is still something it's not about something for the fences I mentioned that earlier a lot of people want the want the sexiest thing possible
so that they can justify their existence but it's not always about that so if you go to the no detection it's either hey you're clean or you're just not being effective enough so you have to seek to prove or disprove that and if it's not malicious you're looking at things like policy violations a date software compliance issues I can't tell you how many times I just saw you know gigs and gigs of data going out of or coming in and people just downloading movies onto servers like it happens it sounds stupid and it shouldn't happen but it has been there too hopefully you know not hopefully but if you find if you find something malicious then that's
where you use cases and your playbooks and your communication with other departments that will come in so those are pretty much the outcomes that you're gonna hope to accomplish with this so now that you've got your data in your lake or reservoir cluster of puppies whatever you want to call it how do we collect and process and analyze it so this is kind of a visualization to tell you all the different places that your data can hide all different kinds that maybe you might not have even thought of to kind of get what you need but you know just says like not enough is a problem too much is also a problem you need the right data so you can get
things like from security like your web proxy IDs Network so the first three here security endpoint and network there's a kind of most popular ones right those are where a lot of us always go to and we tend not to think about data sources from IT but that's really kind of where I should start right because you need to focus your energy somewhere because you're just gonna start going down out the rabbit hole off the rabbit hole like what are your crown jewels what are your critical assets you're not gonna know that and the sock might not even know that but I t's going to know it you're your domain admins are probably going to know that so that's that's
definitely a very rich source of Intel all the way up to HR right we don't ever really think about that are you keeping track of your terminated users you know are you keeping track of you know what what work hours that your employees should be doing like like what if you see an admin who's usually on 9:00 to 5:00 and all of a sudden at 4 o'clock in the morning you see them log in and then a bunch of data getting transferred a look at RAR file now that's something you're going to want to look for and then all the way up to you know access along for the building well why is somebody coming in it you know one
o'clock in the morning when they usually don't come in till 6:00 you know that's definitely something that's so these are all different types of data sources that you could take into consideration so when it comes to events we've kind of categorize this in into two types of events of observed events and synthetic events what I mean by observed events is kind of data straight from the tap right stuff that's gonna come in directly from your firewalls your proxies you know your mail servers and they directly process the data there's nothing else being done to it and so from here you can kind of see an example of a observed event coming from Apache server with a bunch of the
metadata in it from there this is this is a synthetic event created by by the way Oliver lawless we were using bro so so these this synthetic output came from burrow sensor and and that's just kind of broked at people familiar with burrow in the room ok cool same people raising their hands all the time awesome no but no but that's cool because I I need to I want to get a baseline of who kind of doesn't know what so hopefully you guys learned something from this so bro sensor basically it just sits at your egress points sniffs your traffic and tries to categorize it right so you're gonna see here you know this actually this
synthetic event came in via bro into the threat analytics platform again I'm not shilling for them so don't work for many more but it was a pretty badass hunting platform and the metadata is really the most important things because that's what you're going to be able to pivot on right so this is like their class analytics as classifying it as data X Ville with you know received bytes and sent bytes so you can pivot off of that say you know if you know that there's a you know as a certain class of malware out there or a exploit kit that comes in or goes at a certain byte count that stuff is really really really important
and if you can't get direct log sources because I have found it's not as easy as it sounds right you can't just call up any department and be like hey can you start feeding us logs from you know very your email server because it's gonna take six nine eight months depending on the kind of red tape you have to go through so sometimes you know I've seen places that just kind of nuts throw up their own shadow IT but like hey Bros free and hey we need a VM can we have it for a while oh yeah no problem you know we'll own that and then that's kind of how you get at least some kind of fun
capability going so what's the right data right it's gonna be the original data whenever possible you want it straight a tab because it's going to come with less processing less manipulation and it's gonna be closer to your source truth proxy and firewall data obviously going to contain different things but they're gonna complement each other and so you in so you have to review to make sure you're getting what you need is the parsing working or are you getting the right metadata out of it and the most important thing to be able to have when you're hunting and getting this data in is to be able to pivot right I'll give you a quick example you could do
something as simple as like you know you want to pivot off the destination ipv4 right nor did it do who to talk to who else talked to it when did you do the thing that I think I saw it do and that way you can create that timeline right because the timelines one of the most important things about this and then from there you can pivot through hey I saw this come in via you know a proxy log do I have a firewall log that's gonna give me the you know the original source does it have a V log so look it trigger a trigger Navy alert oh it was clean but it's doing this over and over
and over again so that's something you're gonna want to be able to look at and these are the kinds of things you can start thinking about as you're hunting through your data I hate when I do that so you've got your plan you've got your data but you know you're still not ready because you still have to learn your critical assets develop that strategy and you know again with trying to find out the different log levels the time lining is important and then again I'm gonna keep harping on the communication point because you're never gonna think of everything so account for other kind of use cases right so that it's also where to kind of justify your
existence because this is still relatively new this whole I mean it isn't it isn't but in this form hunting is still kind of a new endeavor so in order to justify your time on it how can you complement this with like your compliance people your friends expires your ir guys and that's really going to help your case and then from there you have to clean up your data set normalize it D dupit parse it this is all work that has to go in to everything all the time and all this is to enrich your data set so your data and your events are are utterly useless without context right so say hey yeah we saw
this you know this malicious domain a year ago but there's no other notes in it why like why do we think it's malicious I mean you get this a lot with a lot of they're like the paid Intel feeds right nor snorts used to do this they would put like oh it's got a score of 85 we should block everything okay why it's got a score of 85 what more do you need to know like that's just that's how it happens so building context is really really key anything from malware analysis right and that's kind of the more advanced part of it being able to pull out those those domains of see two domains out of the malware what kind of
adjustments you know that the malware might make to you know reg keys and that kind of thing analytics it's a sexy word it's new it's not perfect that's promising and so the best Intel you're ever gonna get is going to be internal you can pay for all the feeds in the world and I'll tell you from experience you're never going to get anything better than what you're getting from your other departments right the one of one of the one of the one of the given takes that I really stress is working with your red team it's been for a long time red teams and blue teams you know sometimes I don't get along all that well or a team
you know that they want to hold hold their tricks tight to the vest and I've seen blue teams that only concentrate on the red team and you say well okay that's fine you found them but like it's not how a real attacker might come at you like they're not gonna mimic a nation-state like oh yeah but we found the red team we're gold that's not it but it's important to to to build a good rapport with your red team TTP's from your previous incidents baselining is huge right so even if you have to spend you know one or two months base lining your network that's how you're gonna find the normal or the abnormal from the
normal like when you know what business-as-usual is and then of course you have a you know your external your paid subscriptions free feeds passive dns geographical data for stuff you know there's this analyst called the geolocation right not particularly refined just yet but if if you can make it happen if you see a login from somebody who's usually in india and all of a sudden two minutes later he's coming from you know Palo Alto that's kind of a big red flag so and then of course you have your ice axe and four guards all that kind of stuff so your tools what are we going to yield tax to get the job done your criteria
for for your working hunting platform something with a rapid surge preferably with an API or geeks like I said grepping and a terminal all day it's just not going to manage it being able to stack it right so it might it might seem you know obvious to some of us but if you if you have the ability to stack your data and then just sort it by what has happened the least that's one of the easiest wins that you can get to find those outliers and then you're gonna want to pivot you you have to build context you have to see the whole picture I've worked with analysts who just said hey here's a Chinese IP and
it's you know it's blasting all is coming from China or it's coming just just saw the are you address okay cool but like they're real countries too it's real data coming in like it's not it's not just not enough right you have to be able to move laterally into that whole picture and your nice-to-haves or being able to tag things right so what I recommend I love jeera deer has been my jam for a long time and what we used to do is do research on current families of malware currents exploit gets out in the wild right and then be able to tag them with you know what part of the kill chain we we thought they were coming
from what what what are some one there where some the IOC is like hey it drops you know this specific dropper with this md5 at this so that helps feed like those signature base things so that they're still important they're not the end-all but they're important and then what the end goal of having that into the automation of course it's all about the all about the galleons right and for those not familiar with Harry Potter money we realize not everybody is a big Harry Potter fan so yeah it really it's all about the budget especially when you're going through you know a big thing is a vendor selection versus rolling your own icy environments do
both and at a certain point every vendor wants an agent every vendor wants to put an agent on your endpoints and that's just not going to manage so you have to you have to kind of determine what's acceptable use for you and it's important to have multiple multiple diverse tools right can't rely on one things like I said earlier it's gonna fall down that's gonna fail you and you're gonna have to pivot to something else most important thing on this slide I think is you can do this stuff was little to no budget you've got things like NX log Moloch Wireshark bro ELQ security onion look that up if you've never played with it spin up in a lab at work spin up at a
lab at home and you can do this stuff it's you don't have to spend a billion dollars to go on that and I can say that cuz I'm gonna work for a vendor anymore so you got the tech you've got by and you've got structure and now you have to actually do the damn thing so this is wall of text engage I'm not going to go through all of this I blame Jackie for this so if you find her on Twitter you can harass her for that so these are just you know a few of the sample things that we've actually done through our engagements right and it's it's ways to start thinking about how to imply apply
this to your own environment right so some of the some of the things I've highlighted here large or extended outbound data transfers VPN logins that are geographically infeasible like I mentioned earlier service credentials doing not service related stuff web proxies tunneling and endpoints and I had to network with that visibility by security it's amazing how often that happens and I've actually found from being from being a consultant I've worked mainly at the network level so when I do get endpoint logs it's gold so I can actually build that context I can go to a client all day long do we have any consultants in the room I do consulting work one okay cool well then you might feel this pain too
so if you're going to be doing these engagements and and only working at that network level I can I can give them my best guess and my best professional opinion and just hope that they don't think it's the completely stupidest thing because I can't see what their entire network looks like and you have to this is kind of the purpose of hunting and doing this over and over again is to build your best guess to the best point possible so yeah your your your your kernels here might might be driven by you know the threat Intel reports vulnerability scans or just you know your your company wide trends knowing what your attack surface is for
your specific industry is one of the most important things and never thinking that hey nobody's gonna target us this can't happen to me because yeah it's gonna happen to you I hate that one of the most - when people say oh we're small nobody's coming after us no because they need places to stage things like it's this is important for everybody so more data more problems right this is one of my favorite ones that I found I'll give you a second to read that one so the evil versus eath ways for evil to do evil things this guy's not active nearly enough on Twitter here's where we come to finding the interesting versus the evil versus
just the plain stupid and so I'm gonna go through a couple different use cases I'm coming up on time pretty soon actually anybody know how much time I have ten minutes all right thank you so this is actually stuff that we found in client environments relying mostly on bro right bro is super super powerful and I still again I highly recommend you should look into it if you can only do one thing next week if you can only study one thing it's setting up bro do that so remote access right it's conducted using only approved terms well then we have you know VNC to and from our prod Network RDP to a domains you know log me and go to my PC you know
they're legit programs sometimes but you know depending on the environment that that's that could just be shadow IT right so that's a hypothesis that we say we know this is the fact when deep down we know we're gonna find something contrary to that data storage right that is only ever stored it corporately approved locations right yeah I hear chuckles that one always gets a couple chuckles stored an unencrypted infected external media unmanaged source code repositories for intellectual property are absolutely huge because we all know that all development is done securely maybe proxy infrastructure make sure it's properly configured not not blocking no malicious categories you're just letting everything through one of the coolest things to kind of stack for
when he comes to proxy data is allowed versus denied we've had clients I had way more loud than denies they're just kind of letting everything through and hoping for the best you know no categories I talked a little bit earlier about true story sources true destination right I I've seen more true destination than shoe stores and I've seen so many X forward for not configured that I won't hang myself it's just one of those little things that you want to know where it's coming from approved protocols right we've seen unencrypted telnet FTP clear Tex SMTP IRC I've seen a lot of IRC is still out there and it could be something benign right it could be some nerd down in the
basement that that was on that was on like a like a gaming IRC channel we should actually know that like it justice because it says it's a gaming channel we once took some of the IRC traffic and one of my colleagues connected to the IRC server and you just saw bought after bought after bought and like Turkish or some [ __ ] like that and like they swore up and down this was not happening and that's when you can show them these things and and this is where the hunting use case is really really come into play internet access is using known and approved client software know you know I've seen out of it software client
browsers flash and Java I've one of the easiest wins search for user agent strings I've seen custom user agent strings coming from from from outside from just other companies are doing scans on your network giving you their free pen test and they'll give you the full results if you buy their services that should happens way too often privilege management you know service accounts all that stuff up here I'm gonna post all these slides to because not to go through the whole wall of text security architecture you know you're a SAS don't have skin detection probably should your sensors are place where they really shouldn't be process execution on your endpoints I I stress the the value
of of your endpoint login before PowerShell execution me me cats you know all we've literally done searches for me me cats the most basic search you can do and it was there and like hey that wasn't our red team they weren't doing that we don't even have a red team I was like okay well I think it turned out to be you know some guy just testing something but it was there plain text but something they're gonna want to know about DNS of course is huge everybody knows about DNS anything important here yeah so resolutions too suspicious don't Ange plus of random communications you know see to that kind of thing so thinking ahead we want to reduce the
attack surface right we want to shift our mindsets from finding incidents to finding new ways finding incidents don't bother doing this if you're not gonna document it we hate documentation does anybody here love writing documentation dawg you're lying no you're lying actually you might not you actually might be you might enjoy it lessons learned loop in your IR guys metrics again super super important time to detectives going to go down but your instance might go up that's a really important one to kind of hammer home so here's something we're trying to kind of get to now from that system one thinking right where we're intuitive we're fast we're doing it based on our knowledge right you're our muscle memory and this
is kind of where I talked about earlier like oh doesn't matter how you get there at your experience that matters to kind of moving toward that system to type of thinking there's a there's a good book I forget the guys name think it's Daniel came in or something Thinking Fast and Slow great book I recommend it I need Fox he talks a little bit about this too being conscious being slow and deliberate and and and and actually trying to apply some of that really slow thinking to what you're doing so now for a show of hands Jackie did this and I thought it was kind of fun has anybody done if you've done some kind of hunting in the past raise your
hand cool keep your hand raised if your current organization has some type of hunting program in place today awesome raise your hand if your org doesn't have a program but it's thinking about one that's the reason you're sitting in here all right awesome one more question and I hope I see some hands for this how many of you feel like you learn something new yes god you guys make me feel good so there's stammering like an idiot awesome thanks guys so just a quick couple resource slides if you guys want to take your pictures real quick or I'll post them later this you know like I said the the tap program is awesome mitre throw hunting net check that out
people are contributing to me all the time to really help you along on those use cases Longley security onion and then look up bro a couple cool blogs Jack crook awesome for hunting like he's the man elasticsearch and then an article about that book I mentioned of Thinking Fast and Slow and probably my most important slide is I want to lead you leave you with at least a few of the following points building a program is hard this shit's not easy you're gonna run into a lot of politics you're gonna run into a lot of roadblocks but building that capability is a little less hard because you can do this stuff for free the tools and the knowledge are out
there context is king silos are gonna kill you share early share off and it's the only way you're gonna get anywhere and not related but kind of while you're here meet somebody new talk to people strike up a conversation so what this thing is all about I love that b-sides is here this year and at the same time like shit's weird be kind to one another right like everybody's having a hard time a lot a lot of time lately work as hard life's harder give as many hugs as you want jason says it's okay that's it