Bsides Tallinn 2024 - Jarrad Pemberton & Tormi Tuuling ( Saturday Night Phishing Show)
Show transcript [en]
seems to me we are ready for the Grande finale uh maybe some gang signs will be involved and uh this thur day is going to end with Saturday night fishing show uh we're going to find out about how threat actors exploit verified advertising services to fish customers sounds something like happens in every nightclub All Around the Globe coming from somebody for 25 years of nightclub working experience but Saturday night fishing show by dormy duing and Jared pton [Music] please hello can you hear us well can you hear me awesome all right so this is more or less an easy talk because it's been a long day and you guys want to take it easy and drink beer right so we
thought we're just going to tell you a tiny bit what we saw happening on the fishing landscape so firstly about us uh I'm tormi I work in security operations I'm a dad of two curs uh I like to play Magic the Gathering and of course I like rocks who doesn't like rocks right I prefer rooll honestly um I'm Jared I'm the token American in the security team at WISE I'm the only one uh and I make everyone aware of that which is why I like guns um I also am a father of a lovely cat I also play Magic the Gathering uh Dungeons and Dragons and I'm a powerlifter uh it's the only reason that I know the metric system and
he's a power Napper I'm a power Napper too I missed lunch to go take a nap I'm very jet lagged firstly who doesn't know what what we do why essentially believes in money without bers you can use us for any of your transaction purposes account you use it as a daily account if you want uh we last year we moved 105 billion GDP so that's this number of Euros uh and we have what around 6,000 employees right now so to really start the stock off of course we have to start from the beginning which starts in curan age when the earliest fishes were created around btic continent with this rock I promised to bring a rock so I
brought a rock I collected it behind the stage and this is a lie we're not going to start in here so trust this guy he's very trustworthy uh yeah let's go so we wanted to do a demo with cougar fishing we worked very hard on it and it got patched we found out what about an hour ago that it has been patched so you guys can't do this now but luckily we have a backup video yeah so Google doesn't allow us to abuse the same Vector in live any longer uh so this is a video of Google ads and you trying to search
wise notice you get your typical results and then your sponsored ads look at the URL it's shown it's wi.com
right now when you click it notice where you end up that's not us ouch what the [ __ ] Google you lied you said it's what now you as a customer who is not de Savvy and does not notice R directions how are you supposed to detect that that's so we asked the same question what is wrong in here so how did they do it uh first off they created an ad through legit Service uh Google ads was one of the ones that we caught that's the one that we showed you they went in they had an account they started the ad and they set up some redirects uh they used Firebase Dynamic links for this uh so it could check if
you're a bot if you're a person and redirect accordingly so if Google was scraping it for something malicious it probably just got sent off somewhere um those are deprecated so they'd been getting a little bit Fancy with it recently through Cloud flare uh but they kind of worked through this redirect chain until finally it ended at an attacker on fishing site and the reason it was sponsored is you can put in redirects uh for tracking purposes when you submit an ad through Google uh they are kind of expecting that it's going to be uh your tracker that you can get metrics from but if you just put in a malicious site they'll still verify if
somewhere along that chain is a legitimate site and you can Target your audience very well like you can only target the fishing site let's say for estonians in Talan and all the rest get redirected to the original site it is advertising it is so it's very hard to pick up and you as a Defender are go always going to have a fun times so how would you detect this uh well that's the thing so we didn't uh we did not catch this at first the reports came from customers that realized what was going on uh and we kind of got our asses handed to it to us by it honestly um the the intelligence around this is kind of
evolving at the moment um we haven't seen this talk about a lot so we haven't seen much knowledge share going on um that's fun thing because actually there's been like ready posts about that's true and medium articles yes and then when you talk to Google Google is like that's not real what is this first time hearing but by our good threat Intel service we're offering we know everything but not what is used against us exactly so a while ago we also noticed ads about about sites advertising malware so when you try to download the app you actually get like any desk wrapper uh we've heard this is now becoming more of a thing so more
companies are being targeted with any desk rapper so keep an eye out um yeah and these even downloaded a profile for the IOS app which was very interesting so if on iOS devices in your organization you don't detect new profiles being added have fun somebody's getting poned yeah so where do we hit these threat actors when they're doing this uh something I like to look at is the Pyramid of pain uh invented by David biano and it kind of demonstrates indicators that are easier uh if we block them for the attacker to just change and then start doing things all over again uh so it goes from trivial all the way up to tough uh hashes being
the easiest and the the actual ttps being the most challenging for them to deal with so first off uh you mind hashes uh those are very very easy to change uh the SSL and TLS hashes uh can very easily be faked especially the ja3 hash um so maybe what a day later after we take them down or we we block that hash yeah they're back it's the same people up next IP addresses and domain names uh they can burn and re-register something in 15 minutes on name cheap and spend 9 even less yeah even less so domain name same thing just new domains different IPS different locations for everything uh and they're back up and
running then once you get to these hosted Network artifacts uh you're noticing things that are a little bit out of place you're seeing maybe weird end points in your API being hit um for example you might have an open redirect somewhere that you didn't find uh this could be something that is a little bit harder if you patch that not going to be super easy for them to come in and fix it and redeploy what they're doing and then the tools if we can fingerprint these tools that they're using we know exactly what traffic from one thing looks like uh if we pull the source of a fishing page and we start looking for things to fingerprint there once we
change that they have to change their whole strategy for what they're actually building and then hardest is the ttps themselves so the tactics techniques and procedures uh specific ways that their tools perform and these specific tools that they're buying off of the dark web uh usually they spend a couple 100 bucks on them uh and they're not usually the most skilled so if we can actually fingerprint that and block anything related to their techniques and procedures they're going to have to take a while to get back up and running yeah so now I want to ask like from the friendly Legolas guy we saw before like let's let's make him search wise again what what does he
find oh a revel oh [ __ ] straight to the feels uh okay legal what does your L5 see now oh [ __ ] so what the hell is happening here what is true wise if you didn't know we went through the rebranding of from transfer way to yse and in the process there happened a lot of things so question to you what is correct from the previous picture none of those anyone else well actually all of them are correct which makes our job even more fun yeah if you don't know even yourself what your brand is it's fun yeah because people were clicking on from the uh the original logo and everything still so what they recognize
right yeah luckily we're settled in with these colors like the time table is showing us the our prand colors we like it everyone's copying the same green thingy nowadays so go through what we have seen yeah so here's some of the methods that we've seen uh and we're going to go from stuff that's kind of bad to the things that keep us awake at night um SMS fake support calls and fake support centers they'll usually get people that are not that techsavvy but we can kind of detect it we can get rid of them uh email-based fishing as well um especially if it's on the internal side uh we're actually doing pretty good against that um or people that are being
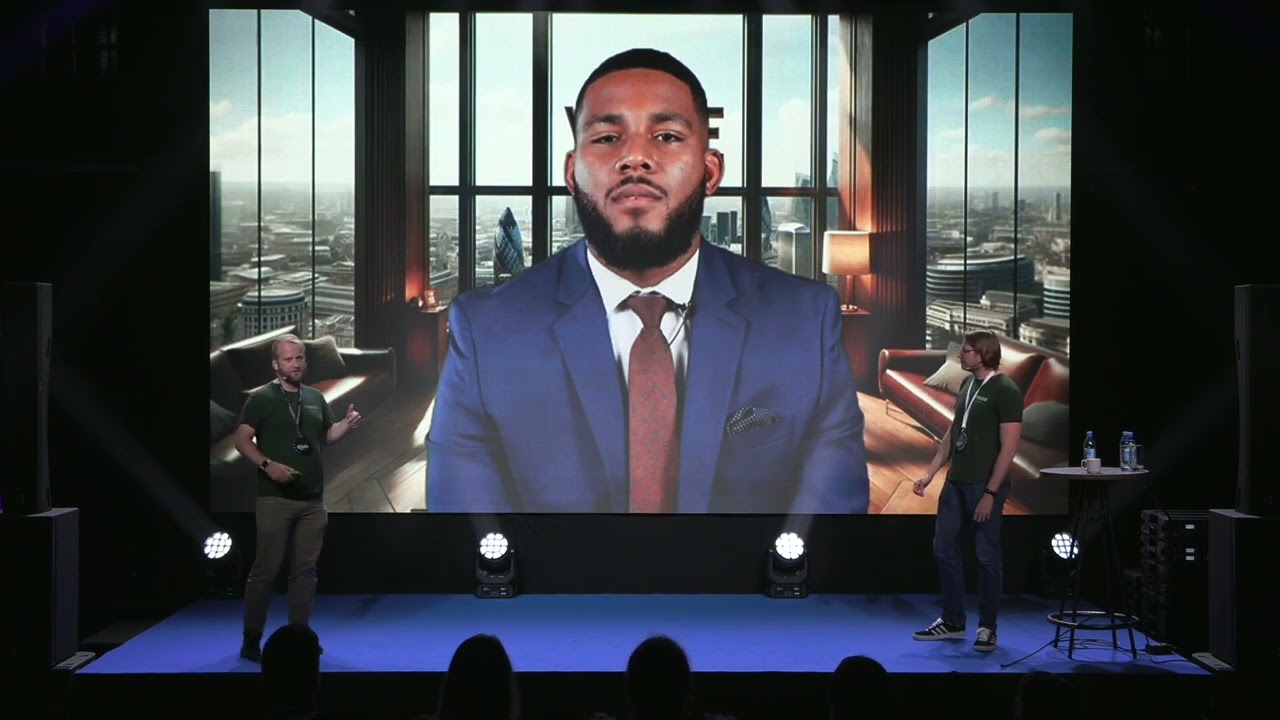
fished we get a lot of reports from email fishing that they're sending things that just look awful in which is great for us because we can just immediately send takedowns then it gets a little bit worse uh fake videos they start to get a little bit better a little more skilled uh the investment schemes uh we'll touch on those a little bit more when we talk about kristo um chat GPT generated stuff is all over the place we'll even find sites that are just filled with chat GPT generated text now uh that they're just filling out uh like a quick web page and getting it up and running uh and the CEO and HR scams
but then the things that keep us up at night obviously the fake ads that we've seen on all these platforms absolutely terrifying but also calling back to the last talk AI generated videos these deep fake videos that we have been seeing uh anything you can name it we've seen essentially this is what we come down to so this this is one example of a fake video we' have seen that is used against the customers I'm not going to show the whole video but yeah essentially you can kind of see it's bad yeah you can see the AI generated background but that also could just be a zoom background right so let's get more to Estonian
landscape so many of you probably have seen in Facebook like kisto crypto offerings have you seen anyone raise hands what seen oh whoa very good so we those of you who don't know Christo is our founder and CEO he's the Estonian Elon Musk let's say uh and uh if you go and look like there's these articles everywhere and at while ago it was very annoying like my mom got like what three or four in a day so a challenge for you take your phones go to any social media search for Christo Garman and see can you f spot fakes cuz that Crystal there is fake that Instagram one there that is fake that is not real
okay that Lego is starting to be annoying it's creepy a bit yeah a little bit I'm glad I'm blocking him from some people yeah so uh tell us a bit Yeah fishing as a service like what what we have seen yeah so nowadays you can get anything as a service and that includes fishing uh you can go buy it and it will be done mostly for you by somebody else we've seen 26 Frameworks for this that people can go uh they can buy for a reasonably low amount of money and then turn and make a bunch off of it so typo squatting not really a big thing anymore people are pretty conscious of that we do our
best to keep that clear it up um subdomains are more common like a subdomain takeover or leaving up some DNS records when you take something down that's what we see a lot more of um and then there's the telegram Bots that are being used to harvest these credentials um someone can go in they'll click somewhere on This fishing site they're directed to Telegram and it will say wise support oh I need your username and password to do XYZ to help you and then they log in um Cloud flare Turn Style is also used and as you can see here uh people can actually change the wording of this a little bit to make it more
convincing um and then they kind of have the weak obsc that's where we can kind of get them uh because you can just go search online and find it uh you can go find forums or people are doing this you can find the telegrams and everything uh so their obsc is pretty bad but it doesn't matter when they're selling to dozens or hundreds of people they don't need to be good cuz they only need to be live for one day like 72 hours they've gotten a few thousand pounds okay so they win this is yeah example of Turn Style used to look like a fishing for this kind this domain that use this Turn Style Oh again this annoying level yep
here he is okay so we researched a bit how much the average fishing as a service costs and it's we we figured it's around 200 to 300 yeah yeah more or less it's not too bad is it so and then we researched a bit how much they might be earning so we a rough estimate or rough guess is they might be earning around 2 to 4,000 be site uh yeah this is very very rough yeah the return on investment is immediate and it is large so we can see the business model where it's coming from so that made us think obviously we're in a wrong job um last year I talked about SMS how to earn money with that now this like
what the [ __ ] I'm doing yeah you're giving people ideas but this is a security conference and a community we're informing you to for you to learn so obviously let's talk about the earliest fishes we know uh and uh oh sorry dude yeah I meant the other this is a paleontology lesson okay we've been over this yeah I'll stop talking about rocks it's it's my thing we can do that later I'll tell after party I'll talk talk you later about this one but we have the Casablanca thread actor group uh what they mostly do is they reuse the same mobile devices uh as much as they can um most of them are operating out of Morocco um that's kind
of the the location for all of this and using vpns are exiting on residential proxies um so basically they are one of the one of the groups is Zone 51 um we think that it's like a Moroccan Arabic speaker that's what we've kind of been able to figure out um using and selling these different PHP based fishing kits uh they've been around for almost half a decade now since about 2020 uh and we've noticed that Within 24 hours they can pivot and start doing like they can set everything back up again uh they learn fast we figure out what they're doing and they pivot uh these guys have been a thorn on our side for a long time
they're pretty persistent they're pretty good uh in general we have seen this year a level up uh in fishing in a sense that our previous spikes uh are now a new normality uh and when we get new spikes they're like really big SP uh so in a sense we got the level up yay are we big enough it seems we're now big enough we have enough customer base that random targeting of any random email works yay uh so I hope it's the last time I see this guy uh I hope so too but you're the one that put them on the slides I don't know it's the AI but uh there's no more nigarian printing right like clearly they they
become so sophisticated that no longer this easy stuff right okay let's let's read this uh fishing email for a second unfortunately you won't be able to use wi furthermore we will confiscate the amount unless you claim it we will have to donate it to Ukrainian support forces helping them fighting the oppression of the Russian forces the Deno donation will happen from European Central Bank that's nice of them what the [ __ ] we get p i can get paid from European Central Bank okay well sadly some people actually fell for it so what can we actually do about fishing like any ideas what what are good methods to prevent fishing maybe like using du fa right
nope so we've seen they can steal almost any kind of Dua except like yub Kei so unless I get physical access which happened last week so there's not much you can do on that part okay so maybe let's throw more heads at the problem like hire more people to deal with fishing to prevent it more could we that's not that simple cuz like you know Finding good security people it's hard not many people want to work in the field unless it's one of you who wants to work uh so and there's a bit more problems around that cuz hiring won't solve the problem you're just postponing the problem so we need to be a bit more wise about it and I
know the pun is intentional uh so yeah so ah this is getting old yeah AI is not going to solve this problem what we care about are the two metrics time to validate and time to take down so these are the two time constraints that are in our control we cannot really control how fast hosting providers react but we can control how fast we validate a potential fishing site and report it so so and that process cannot be solved by humans really you need to automate it that's only scalable way to do that so how would you go at it is firstly let's collect the data yeah we work smarter not harder so these are some samples
where you can gather fishing sites uh if you don't use use them certificate transparency is a very good place most of you have heard about it probably uh then you can obviously gather your own customer based reports don't be stupid about it it's free information take it and then there's a new thing called ad transparency if you didn't know about it almost every ad provider has ad transparency page where you can search any AD they're offering and see what it's targeting and who bought the ad it's for political reasons but it's very effective for against fishing as well uh the former video you saw about the fishing in Google funny thing that ad was actually bought by using wise
account uh and of course your own logs you they they tend to just copy the page so they still use your own image our own colors that we use yeah and then once you gathered your sourcers you can run automations against it like for example check if the potential site has your brand colors and it's most likely a fishing unless it's a very similar looking site uh so but we'll learn as much about them as we can yeah but how well I think we have a plan what's what's your plan how how would you learn more about them we beat them at their own game you mean this exactly so we can play the fishing game too you know uh so we can
fish them back uh essentially we learned the very effective way is to fish them give them credentials to use and let them validate them and then gather all sorts of metadata about them and because they don't want change the devices that often let them burn them out
okay what are canaries an island chain right Birds who would die for you very good Birds
yes obviously me as a geologist will answer you it's a island chain okay what are I I have you seen or heard about this ter sure okay so an I uh is an indicator of a kit a fishing kit that someone has purchased and spun up uh that uses a framework that we can fingerprint so once we have the data from a site we can analyze the kit and find different indicators from it uh a lot of these people are very vain so somewhere in the source code you'll just find what they call themselves you know maybe the comments are in the their native language you can figure out where they live um then you'll also find things
like they tell you okay use name cheep uh register here put it behind Cloud flare do all of this um and then all like the locations where it's hosted are indicators of this specific kit because everyone buys it and they follow the book uh and that's what we need to fingerprint so we can also match the sites that use our brand keywords like tmy said um they're figuring out what we use to make it seem as legitimate as possible they're taking the language that we use because most companies have their design documents and branding guides on their website yeah and some companies aren't even good enough that they offer their own branding sites you can get the
images from yeah not talk Talking which companies uh uh yeah and iok are also open sourced if you search for them you'll find quite a lot of fingerprinting already done in the online yeah and then we have Canary accounts as that person over there said that is exactly correct we create an account that we want them to get the credentials for we let them fish us and we watch what happens we analyze everything that they use web routes we monitor all their redirects we note any infrastructure that they use and we fingerprint exactly what happens when they get these credentials and we just follow the chain yeah so but what are like other companies doing in the wild like is
there anything else done like for example cuz we operate also in Australia uh we know they have quite a big anti- fishing campaign going on right now and they're pushing passwordless use heavily uh if you can go passwordless go your thank yourself uh UK takes another Direction UK forces companies to reimburse all of the V victims that hurts so that makes literally every customer who fell for a fishing your problem it's not their problem anymore now it's our problem okay so but what is like us doing you know more yeah I uh nothing Freedom baby yeah you know they tell you don't click on stuff kind of I mean we still use fax machines but you can buy a gun
no okay so that was it right but that stupid guy is back he won't leave us alone okay we've seen him enough we surely we trust him right okay why not use your bank card as your 2 FAA have you thought about this do you think it's possible can you make your bank card function as a 2fa token answer is yes you can buy one mhm okay what the [ __ ] okay like he's that persistent he must be a true guy right okay obviously like let's scan the CER code in a security conference what what can happen this isn't the first time it's been asked today so so who got rickoll right
[Laughter] now okay so anyway we're hiring if you're looking for a job talk to us uh thank you all thank you
Estonian Elan musk hash cult um I'm just I mean it's a brave thing to compare your boss to a mus if I would have a boss I would maybe have a second F but there's a reason I don't have one I I make comparisons like this but then again I don't do security so they don't really need me um anybody wants to and as a huge Lord of the Rings fan what you did there I'm gonna remember that I'm like I support Nicholas Cage but there is a bloody line you do not cross it I mean it's not Star Wars or anything sorry I'm digressing here so any suggestions you know I know everybody is the damn UK you have to pay
back the customers as a as a lawyer I kind of get that it's a bad but as a customer maybe not um any questions any recent fishing Expedition do you want to drink yeah that that's that's an honest question as well want to go change your foot yeah yeah yeah you know while you're there in a comfy slippers win win win three two all right if not then um happy fishing gentlemen thank you thank
you it amazes me I'm here second year and like for the second year wi comes up with a story which I usually would read from Stephen King or somebody and they're still in business amazing no I mean with this kind of a security team I'm no no wonder but it's like wow what's next like have you heard about those things called Transformers we caught one yesterday we we want to show you it looks like a vacuum cleaner but there goes four grand I know it's digital economy all I'm saying you know we started with phone calls now my grandmother has Skype whatever so this is it with the presentations before we're going to let you go it seems to me that the
organizers want to do something because they have a huge box I'm scared to think what's or who is in it so just let's get them on
stage we have some deep fake
voices actually yeah you're still here right contract come on come on well oh Jesus you have been trying to get the Estonian people to wake up and react so this is a uh effort that you know is you will never succeed at it we know but still half Russian I'm trying thank you for hosting again great job calories yes yes and actually what will happen now is that the official part is over we're going to start moving to the Afterparty section at what to about the gloy that's like 200 M this way T will be here there we will be there you will be there I hope there will be uh some program some entertainment snacks
drinks Jeopardy yeah hacker Jeopardy uh there are couple of ending remarks and and message about this box here that I want to say so our friends at Basta Brewery yesterday brewed this very special beer sides Be sides Brew um I just tasted it it was like really fresh really good beer you you never had