Show Me the Money: Getting Business Buy-in for Security
Show transcript [en]
good afternoon we have a very interesting speaker coming up next miss carlotta sage she is a fractional ciso raised in the wilds of alabama by angry chickens and crazy people wolfpack educated in the tar heel blue devil state and indoctrinated into security by silicon valley appliance vendors which are either wolves or angry chickens or maybe both carlota has returned to the east coast where she serves as a vciso principal for fractional ciso when not picking other people's brains for minutia she strings beads destroys cars drinks whiskey and screams into the dark dark void that is twitter you'll find her at carlotta sage my welcome color to the stage would show me the money thank you jane
that's fantastic if i had realized somebody was going to have to read that out i might have been more kind to them but jane did such an amazing job thank you very much this is called show me the money this is getting business buy-in to secure your organization a lot of the talks that you've heard this weekend or this week and and that you'll hear in the lock note this afternoon are more geared towards larger organizations i'm going to tell you a little bit more about securing smaller organizations that's my mug with my mug i am a virtual cso with fractional cso we help small to mid-sized companies build out cyber security and compliance programs the way that our model works is
that usually a company 50 to 150 people are coming to us they want to get a sock to compliance often the driving factor there is they're trying to sell to larger companies that are asking for sock 2 compliance and we help them build that out before they're ready to hire a full-time cso we assume that if we do our job very well we will be there fractional ciso for about three to five years at which point we will help them hire their first full-time cso or head of security at which point we should have built a good enough cyber security program that that person can actually focus on building the security team rather than getting the fundamentals
done uh i like myself so i'm going to tell you about me i'm pretty awesome these are some of the logos of companies i have worked for in silicon valley netgear my history is actually in doing large-scale content management systems so if you go to support.netgear.com i originally did that website uh help.netflix.com i also did their help center i advised facebook on their help center and so my history is in something called knowledge strategy that's getting information flowing through a company out to partners and customers in an efficient and cost-effective manner those help centers with netgear for example a phone call for netgear support at the time was costing 18 a call they were getting 42 000 calls a month
and by redoing their support website i was able to get that down to um 24 000 calls a month at a savings of eighteen dollars per call so it's very cost effective it's very easy to prove the roi on on that kind of situation same thing with netflix of course they don't have you could not and still to my knowledge cannot call netflix for help but they have their application runs on at the time nearly 900 different devices they were very concerned how do we support our call centers and how to do art we support our customers and supporting themselves with a knowledge base or a help center a very different kind of structure and
you have to think about from that perspective what can the customer do there are four things a netflix customer can do on those 900 devices they can stop and restart the movie or show they're watching they can stop and restart the application they can stop and restart the device that they're on and then they can reach out to netflix those are the four options and at the time you could only reach out to netflix via email they were implementing chat at the time very cost effective solution for for helping those uh those folks eventually facebook was a short contract but i i went from facebook to fireeye i went to fireeye on a six-week contract
all i had to do was help them break a stalemate internally on choosing their content management system and their collaboration platform their communities at that point six-week contract i had it done in two i sat around because i'm very good at architecture i helped determine here are your needs for sso here are needs for federated search here all of your infrastructure that you don't have has a 300 person company at the time by the end of the year i came in to fireeye april of uh 2013 by the end of that year they were 1200 people and in january of 2014 they bought mandiant i was a part of that m a so so that's kind of how i got into
security just to give you a little history about myself i also attended a lot of different schools i'm a college dropout i dropped out of auburn university it is not a university i applied to i love my mother a little bit controlling um i was not allowed to take the full scholarship offer to caltech mom wanted me to stay local i ended up at auburn got the best advice of my life and that was when you're 18 you're an adult i'm not telling you it's going to be easy said my professor but it will be your life and you do what that what you want so i dropped out of school and ran to north carolina ran
away to north carolina i ended up at a community college called durham tech fantastic experience highly recommend the community college experience if you are in the united states i don't know how that equates here in the cayman islands i ended up at a public school north carolina state university wolfpack i graduated with a degree in textile chemistry i was a research chemist for eight months after that i had put myself through school doing that web development which is how i ended up later in those content management systems but what that gave me that continues to serve me very well other than knowing how to wash my clothes that degree in textiles chemistry textiles understands that
your clothing your furniture your fabric in your home evokes an emotional response and that all has changes in your response to that fabric has to be mapped back to not just the fabric itself but to the yarn the fabric's made of to the dyes and finishes that went into the yarn all the way back to the fiber that's grown in a cotton field somewhere in alabama so it gives you a really what i got from that was just a really good sense of holistic systems and looking at that from a consumer point of view i eventually because i was so good with netgear and netflix and i was so good at building those large-scale content
management systems and so good with those knowledge bases i wanted to understand why it was so good and i my degree my master's degree from columbia university in new york is in something called information and knowledge strategy you hear [Music] people processes technology a lot in the security industry that is knowledge strategy at its core information security cyber security we are knowledge intensive industry highly recommend picking up some books on knowledge strategy if you want to really be effective in cyber security i joined fractional cso last year last july i've been having a very good time there they've been very giving with the mugs i'm enjoying it um but you can see me you can find me
on linkedin as carlos sage on twitter has carlota sage linkedin you get the more professional posts uh i'll be honest on twitter you get more [ __ ] posting so show me the money i want to give you a little context on why i developed this particular talk in the united states pre-covered as of 2016 there were 5.6 million employer firms that were under well sorry 5.6 million businesses in the united states 99.7 of which have less than 500 employees the majority of those have less than 100 employees but we hear from that upper crust those enterprises that can really afford to do security effectively at scale very valuable really doesn't apply to 99.7 of the businesses in america
i imagine it's very comparable here in in the cayman islands you have a very small set of very large enterprise companies that can afford to do security well you you hear from them a lot they don't apply to most of your business models i think it's very important that we hear from those security vendors and from the enterprises that can do security at scale it brings security and has in the last 10 years certainly brought security into a mainstream conversation and now we're starting to see some of the effects of that in the small and midsize business market and here we go knowledge strategy people processes technology at the center of that lives the data that we his
information security professionals need to protect uh unless you're with a hospital system then you have lives in that lives and data in that center overlap the security vendor is one as focused on the technology because they want to sell us the technology it's they need us to believe that that technology is going to solve all of our problems but the reality is that technology solves a very small amount of our problems because the majority of our problems live in the people and process side so this conversation today i'm going to assume that you either know technology or have technology or can't afford technology so we're not going to talk about technology we're going to talk about people and
processes that drive good cyber security programs for small to mid-sized businesses this does translate to larger organizations as well but more importantly what you don't see on the slide we're going to talk about the money aspect of this we'll start with the people lens everyone feeling good i'm seeing awake people this is great i appreciate it people i have three mantras that i live by whether i was in i.t operations support operations through security operations and that first mantra is you are not your average customer your customer doesn't care about security that is not their job they've been hired by your company to be very good at accounting or marketing or something else so you as a security professional already
are not your average customer if you were you would not be doing security you cannot succeed until others in your organization are invested in your success there is no good way to roll out a security program and not involve your internal customers you can't do it and expect it to be successful well we can talk about that more in a little bit but more importantly as you're rolling out your security program any friction that you introduce to somebody else's process is immediately an insurmountable obstacle any friction is an obstacle i cannot say that enough over 25-ish 30 years in tech i've seen so many multi-factor authentication programs roll out in companies from 40 people to 4 000 people
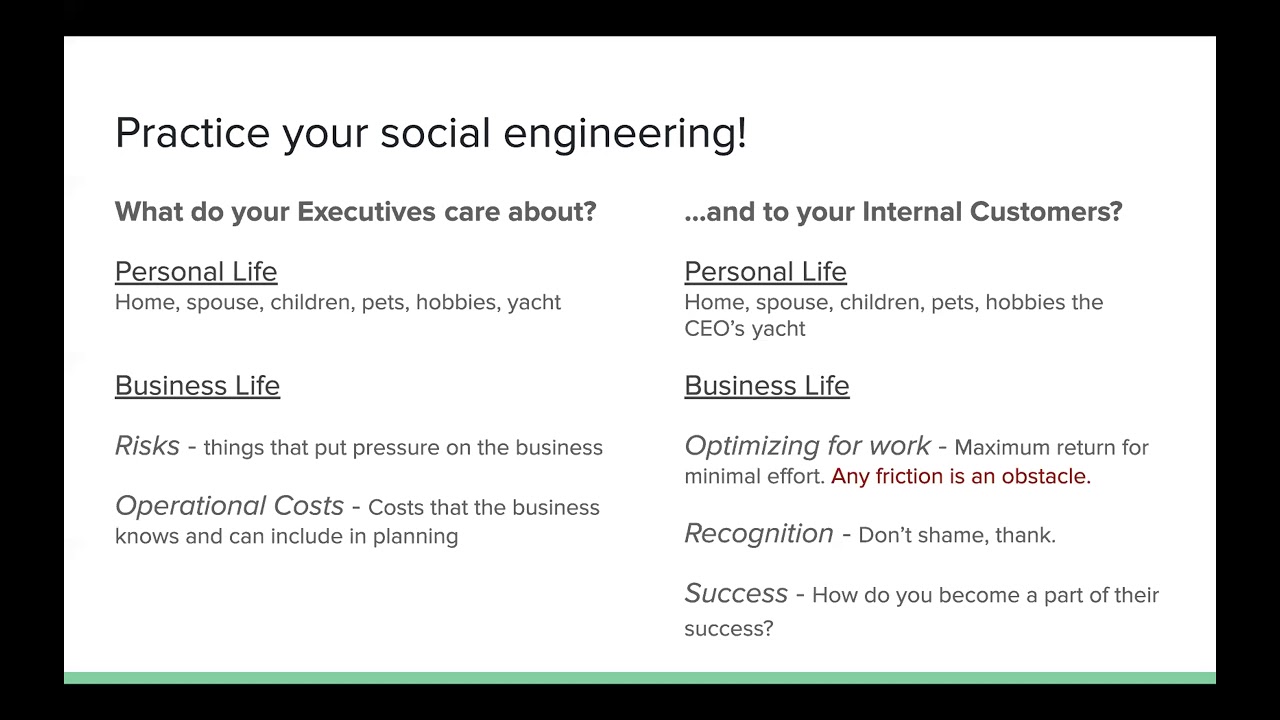
and half of them would fail because you roll out this thing and people will spend more time figuring out a way around it than just doing it because you have not engaged them you've not made this a part of their process you've introduced friction to their process and therefore you've tried to give them an obstacle that now they're pissed about so in short none of this is about you it's about your customer your internal customer your external customer not you so you has a security professional you need to understand and empathize with your audience what do your executives care about they care about operational costs how much is this going to cost me that's fine
if they can plan for it that's one thing it's when all of these unexpected costs come up that they get really cranky risks are another really big thing that your executive team cares about this is anything that's going to put pressure on your business and may spur that spending above those expected operational costs right so risk it still comes down to money for your internal customers it's different they want maximum return for minimal effort when it comes to their work so again when you add friction to their processes you make them do more work even if it's an imaginary work even if it's two seconds of multi-factor authentication you have now interrupted their ability to optimize their work
they want recognition they want to know that they're doing a good job historically cyber security has a bad habit we're known as the team of no we tend to shame people we tend to put them down we still get organizations sending out internal phishing you know testing campaigns right where they're promising bonuses and then when people click on it firing them and that is stupid because you are eroding that trust and you are not recognizing that this person is an adult that you have hired to do a job that may not be as a security professional so shaming people fundamentally does not work what does work is thinking them i have a former client a non-profit of about 80
people didn't have a lot of money right but had a really committed it team who were very open to talking and engaging with their internal audience and what they would do in their slack channel whenever somebody sent them something that said hey i think this might be like a phishing email thing that you guys keep talking about they would screenshot it they'd drop it in the slack channel and go thanks bob thanks sue you're absolutely correct this is a legitimate phishing email and that did two things it says to everyone thank you you are part of my process i am involving you in my job you are making me as a security professional more successful thank you but it's also
saying hey folks here's a phishing campaign that's active right now and here's what it looks like don't click on it right very simple takes a couple extra minutes a day very effective learning tool and again success how do you become a part of their success that team did a really great job when you were a part of my success as a security professional and i thank you publicly for making me successful now you've just become a part of my success now you feel like i'm invested in your success as well anything that you do that erodes that when i hear people call their internal users cow workers you know or stupid users or the problem
exists between the keyboard and chair pebcak i get it it's not their job to be security professor professionals and when you say [ __ ] like that you erode trust and you make it clear to them that you are not invested in their success in their role you cannot expect them to help you as a security professional if you cannot respect them for the reason that the company hired them i can harp on this all day but we have a lot of other topics to cover so anyone who has a good example or a question here jump up all right i'm going to move on people processes technology we're going to talk about processes now
cyber security health model i have a chapter in this book called reinventing cyber security you can download a pdf of this for free from jupiter one's website they are a vendor they were very kind and footed the bill for this in the u.s this is available for 10 off of amazon in there i go over the cyber security health model the reason i wrote this model and originally i was calling it the maturity model and i'll tell you a little bit more about that in a moment the reason i developed this model is that i would go into a client and try to talk about cyber security maturity and their eyes would glaze over and so i would pull out the nist
maturity model and their eyes would glaze over the nist maturity model is fantastic for a security professional when you look at that model you as a security professional with some experience understand what that model was trying to convey to a business person that model is completely meaningless so this i wrote is very verbose but it's very meaningful to a board to a group of investors and to the c-suite because they understand that when i say hey client right now there is someone in your organization who is trying their best to do things in a secure way but it's maybe one person and i need you to move over into this middle column i need you to be either
team driven or compliance driven i need a team to own your security and to drive that within your organization and if you have enough money i want you over in that risk-based or risk management informed column where you're actually using your cyber security information to make business decisions my clients are usually like i said sub 250 person organizations i usually see them coming in on that grassroots or ad hoc side there's somebody in there who has some vague clue about security and they're trying to do things in a secure way on the technical side maybe they've got a compliance program maybe they've done sock too and they're a little bit more in that that middle
section i don't expect any of my clients to be on the right hand side of this model until they are big enough making enough money to actually invest in security tooling at 50 people i'm not telling them to spend 200 000 a year on security tooling unless they are very well healed that is not the majority of my clients i take that model and i make a scale and it's a one to five scale again one is going to be that left hand side three is the middle five is that right hand side i want my clients to be a three so when i do the gap analysis with them and we talk about how does a business
talk about security you know are you doing any kind of security awareness and training do you know what your compliance needs are like i'm rating them on a one to five scale and then i'm giving that to the leadership and saying here's where i need you to be threes i don't need them to be fives and by saying by having shown them that previous model and now giving them this i'm saying you're here i need you here and i'm going to give you a path to get there all of those talking points are going to be very consistent when i do and i don't cover this in this particular talk when i do secure software development life cycle
assessments same one to five scale same cross-functional relationships cyber security operations and then we go a little bit more into developer behavior infrastructure for your development and your your production environments and then the the security behavior your application supports once it's in production this is a great tool for an early early program gives you some sense of metrics of okay we want to be a three in compliance well you know maybe we need to hire a compliance person and maybe we need to invest 30 000 a year in a compliance platform like a vanta or a bike check or something like that drata there's lots of them out there you can now tie measurements to outcomes of some sort i if i spend
thirty thousand dollars here i expect to go from a two to three there and that's really valuable when you're a very small organization because you can't buy for security tooling until you have some kind of metrics saying you need this security tool right so if you have no security tooling whatsoever this is a great start security roadmap ideally and again you'll see i'm using the same verbiage over and over again business alignment awareness and training compliance and audit program and people development you know program and people development if you don't have a security team which 95 of my clients do not this tells you hey great you're working with fractional cso for the next 18 months
at some point we at fractional cso expect you to actually hire somebody internally who is dedicated to security and we put that on their roadmap so leadership knows it's coming i once posted an example security roadmap on linkedin and i had a ciso say attackers don't care about your roadmap and i'm like you are absolutely correct attackers give zero shits about your roadmap but you know what your ceo cares a lot because they can't budget for anything without this and it doesn't have to be exactly this format maybe you've got a format internally that you're already using ask if you're not sure ask whatever it takes put something together so you can say to your
leadership i'm one person i'm doing this over here in order for us to do these other things in order for us to get to threes on that health check i need to hire people in these spaces i need tooling in that space here's how much it's going to cost me right here's how much it's going to cost us to get from ones and twos to threes across the board all of these things that i'm going to show you today i'll just take a quick side note all of these things are available has excel spreadsheets they're under creative commons license in my github you can download them you can use them you can alter them to
whatever is meaningful to you you can share them i don't care do something that helps you communicate to the business if these are not meaningful figure something out talk to me i'll help you and before actually before i go too far security health check security health check my plugging shameless plug my chapter in this anthology and this is a great anthology of mostly women's cyber security professionals my chapter is literally called [ __ ] security maturity let's call it security health let's talk about security health because maturity to a business person implies that we only ever get better we only ever get more mature we only ever get more sophisticated and we know in security that is not true
go back one more these driving factors the likely change drivers here there are things that push you back down and make you less secure if your executive leadership stops caring about your security program i guarantee you you are not going to be five anymore but what you're really here for is the money lens the money lends it's hard as security professionals i think to talk about money because we just know okay we have to spend a certain amount of money on a certain amount of tooling your organization has already decided that it is worth it to them to spend fifteen hundred dollars every three years to buy everybody in the company a macbook pro or a macbook air
your company has already decided that it's worth twelve dollars per person per head per month to have gmail or microsoft office um sorry microsoft 365 is this being called down because email is important that is no longer a cost center that is a an operational cost that is core to us having to do business my people need an email address my people need laptops you need to be able to say i need security to be a part of your operating cost instead of having people look at security as a cost center security is not about losing money security is about being core to the business function i do this in a couple of different ways
when i'm talking to a an executive for a simple project an roi calculator very simple i have 80 numbers 80 employees um how much time how much does that person make per year how much time do i think i can save them in effort and for a lot of security professionals these numbers look imaginary but to a cfo these numbers are very real and they may not agree with the exact numbers but i've rarely had anyone in fact i've never had a cfo change the formula i've had them change okay well only certain number of employees will actually get you know productivity out of this this is only additive for this roi you can't use
this to replace people with tooling which you should not be doing anyway your tooling should always be presented to your leadership has i need to use my existing team more effectively and if i put this tooling in i can free them up to do these other initiatives that is how you should be positioning your security tooling to your leadership this ties in at a higher level when you get more people and you're more enterprise driven to automation now if i can spend x amount of money automating things i can now redirect my folks to focus their effort on these other initiatives so that's a very simple conversation starter to get a little more interesting especially with
a cfo i like to talk about risk and recovery estimates i need that cfo to accept that there is a cost for not doing security if you are not going to invest in security you need to be aware that this is going to cost you at some point that point may be in a month that point point may be in a year that point maybe in five or ten years but at some point your lack of attention your lack of funding to your security program is going to cost you money here i have incident response calculations that not just cover and the the incident response costs um come from adrian sinabria and tennessee it's not just about what your ir team if
you're big enough to have an ir team it's not just what those people are are spending in terms of effort because when they are responding to an incident they are not doing their day job ideally or their ideal day job and that productivity that loss in productivity costs money in the cfo's head i also want to make it clear that if there is something that's impacting your productivity across your organization like a ransomware event you're losing money because folks are not able to do their job and at what point does this number get big enough that it shuts your company down and for a very small company that number may be well under a million dollars it
may be under two hundred thousand dollars by taking this to your cfo and starting a conversation very helpful again i've never had a cfa cfo push back and say i don't believe in these numbers maybe they've adjusted them but they've not adjusted the formula underneath them as a part of this particular spreadsheet in my github there are a couple of tabs that actually have um uh kind of yearly information from like the fbi sofo secure world on what companies or costs what bec and ransomware are costing companies so you can say to your your cfo over here on this tab you know the average vec is costing a company 200 000 a year and if you can get them to accept that
if they don't do security that one day they're going to have to pay that 200 000 you can really get a lot more buy-in come on wherever [Laughter] and that those risk and recovery estimates can also be used to determine how much cyber insurance you need because one of the biggest things that my clients ask me is how do i know if i've got enough cyber security insurance and the answer is you never have enough cyber insurance insurance because something always screws that up it's the landscape is changing constantly but i can get you in a ballpark so if for example you are a service provider of some sort and you have a subscription service you've got seven
customers these are your subscriptions this is just an example this is your impact cost per day if suddenly you are not able to deliver services that fifty three hundred dollars multiplied by seven days that is the minimum amount of cyber security insurance that you want because i have to assume that if you get ransomware and you can't deliver services for seven days that you're you're going to lose a lot of those customers you may lose all of those customers if you're only down for four hours or a day very high likelihood that 80 or more of your customers will will come back or be retained but you're still going to lose some customers but if you're down for a week or two
weeks even if it if that number is not big enough to kill the business as a whole you have fundamentally changed your revenue model so for a company like this you know i shall i'll give you an actual example i have an e-commerce customer their revenue generated is six hundred and fifty thousand dollars a day from their e-commerce commerce website multiply that by seven is 4.6 million dollars their cyber insurance was a million dollars i want their cyber insurance to be at least five million dollars to cover that four and a half million that they're out ideally i want it to be 10 million but that's a business decision because for that particular customer getting a 5
million dollar policy was sixty thousand dollars getting a ten million dollar policies a hundred and thirty thousand dollars very big difference how do i wanna spend that money they chose to go with a five million dollar policy but it also means now they're aware that they may get hung out to dry if they have an incident big enough that it's going to be more than 5 billion i will say if you ever have to look at cyber security insurance you will see you know what you're insured for five million is usually your cap maybe you're insured for 250 000 for a wire transfer maybe you're insured for you know a million for fishing that may leads to
some major major incident but you'll see a retention clause of your million dollars a hundred thousand dollar retention that's not like a deductible kind of like a deductible not exactly in a health insurance deductible in the states at least if my bill is five thousand dollars and my deductible is a thousand dollars i pay a thousand dollars the insurance company pays for in cyber insurance if my bill's a million dollars and my retention's a hundred thousand i pay a hundred thousand they don't pay until it's over a hundred thousand so if i have four incidents that are right around a hundred thousand dollars they don't pay for those you know right so my first incident is 97 000 99 000
100 100 and 2 000 guess what i pay i pay i pay a hundred thousand they pay one thousand right i i pay a hundred thousand they pay 2 000. that's what a retention is so it's really important to dial in your cyber insurance i'm also going to pause here and talk about why customers come to us not trying to pitch my my service here i'm trying to help you understand the market's place 85 percent of my customers uh sub 250 person companies are coming to me because a bigger company one of their potential clients is asking them for stock 2 compliance great that's fantastic because now they have tied security and compliance to sales
that's great if i can get everyone to put in their crm a sock to flag or a security flag where not having security or not having talked to has cost us a deal it's very easy to get that funding it's a lot easier to get funding for security and i've done that with clients of the remaining clients that come to me or prospects that come to me i'd say the majority of that 15 percent is boards or investors saying hey you need a security program fantastic they're looking ahead very small percentage one prospect can't has come to me in the last year because they had an incident and i'll be honest i laughed because when they told me what happened i
couldn't help myself i said how did you get breached and they said they compromised a a cold fusion 2012 server this is in november right and i loved because in 2002 i was decommissioning cold fusion servers i didn't even know that cold fusion still had you know as around michelas had a 2012 server that you're now still running and why are you running it in ec2 oh okay well you know we'll get there but i laughed and i was embarrassed because i'm supposed to treat people with empathy and this is prospect i might just lose a cell of all right um and the guy says no no it's fine i'm the new cto i've only been here three
months this is what i'm inheriting honestly of all things that could have happened it turned out really well and they actually did come to us as a client tools and suggestions you don't have to spend money to get started if you're in a really small organization there's plenty of open source tools out there i'm sure you've heard of lots of suggestions over the course of the last two days as well security onion is one of my favorites the folks driving security onion are old school mandiant consultants some of the original gang the security onion is free they charge for for support basically although if you're in the community it's free you can just buy a support
contract if you really want one fireeye which is now trellix used to have a page full of freeware i haven't gone to check and see if it's still there know before i'm not a fan of their stuff i'll be blunt but they've got free stuff um like it's free you get what you pay for and i don't recommend paying for it you know lots of other things facebook's os query github stuff you know sniper rit app great for um it's asset inventory kind of things and that's it i'm carlo de sage does anyone have any questions was there anything here that didn't make sense i know i moved through things pretty rapidly everyone felt good about that
all right do you want like anything else damon are we good no questions all right i explained everything beautifully i'm so glad i could help hit me up if you have questions please do feel free to connect with me on linkedin please do feel free to slide into my dms on linkedin and twitter you're always welcome to ask me questions i will always answer thank you everyone
you