BSidesCharm -2017 - Tazz - Threat Hunting Thinking About Tomorrow
Show transcript [en]
thank you guys for coming for those of you who don't know me my name is taz that's my twitter handle at the bottom grc underscore ninja um i'm in a dress in heels because i lost a bet this is not anybody else knows that i would be in a baseball cap and jeans so we're going to work with it so um the reason the reason i did this talk is i went out to um naval post graduate school for in monterey and i went down to socom which special operations command down in florida uh last month and had a lot of interest in conversations with those individuals and a few sea levels talking to some
attorneys and things like that and one of the things that i found was the way we think about threats is very tactical oriented and a lot of the threat intelligence that we are required to provide for our consumers and our customers is all about fighting the fight right now like what's the threat in front of us what's going to bring down my network today and i'd find that we don't do a lot of strategic style thinking when it comes to threat intelligence and we never forgive me if i use absolute terms i'm these are i should say majority we usually don't take the time to view ourselves through our adversaries eyes and understand the value
that we are to them from a strategic perspective um how many of you in here spend your days trying to protect your own assets your own network how many of you have been told what's of value and what's critical in your in your network how many of you have ever walked over and asked not china if they thought that what you thought was important is important one person okay but seriously a lot of times we see ourselves as a target we rarely take the time to think of ourselves as the third domino in somebody's longer game and that's kind of what i'm here for today is to try to just challenge the way we think
of things and not to say that anything we're doing is wrong i just think it's time for us to start doing more okay so i want to ask if you can even imagine motives goals structure organization methods of an adversary what does this sound like motives goals structure organization and methods ttps right if you can't even imagine it how can you possibly defend against it right if you can't think of an original idea how could you ever build something the wheel wouldn't exist if somebody hadn't thought of it first right so if we can't think like our adversary if we can't even play the imaginary game go home with your five-year-old and and have an imagination then how are we
going to defend against things that we can't even think might be possible right and i'm talking serious tinfoil hat stuff sometimes but your imagination as you get older is one of the things that we have a tendency to not do i sit and i look at little kids and they're playing with their imaginary friends and they've got a whole set of imaginary rules for the castle and the moat and the alligators and the spaceship that's coming in over the wall of the castle and i makes me sit and think back to like man i remember when somebody was asking how would you defend this castle and a whole bunch of people come up with all these rules about how they would
defend the castle and then somebody throws them a monkey wretch and he says well you just got bombed by a spaceship didn't see that coming right and so but the point is that we have a tendency to stop using our imagination as we get older and if you sit and you if you if you have kids they'll keep you young but then i encourage you like seriously ask a five-year-old how would they attack you you'd be amazed at some of the things that they would come up with especially a five-year-old that can write python i'm telling you they're dangerous kids so um i really want to try to have a conversation today i don't like agendas
and plans and being rigid um i this is to invoke and provoke thinking today so please feel free to raise your hand if you have a comment or a question um if i had mentioned something and you guys have done it and you've succeeded or even if you failed share your story here today i want us to i want this to be a thinking room today not a task sits here and preaches to people so we'll go over a little bit of the difference between tactical and strategic digital threat intelligence and i don't like the word cyber but cyber gets you funding so if you need to use cyber cyber is authorized for funding discussions only
okay and we'll talk about target development how many military people in here do i have they've ever done targeting or target development okay so you guys will understand some of my phrasing duet i broke up sick right so um but we'll talk a little bit about doing target development from a cyber perspective right and then we'll take some questions so if you have pen and paper if you have a cell phone feel free to take a picture of this slide jot this down this was written many years ago and the irony is that everything he says in this about what we don't do and how we're not doing strategic intelligence right is still true today
i've learned a lot from this individual and from his writings and third party knowledge nuggets he's passed down but this if you are doing threat intelligence or you want to do threat intelligence i strongly encourage you to read his white paper this is a book for those of you who may be building a threat intelligence organization this is a really awesome book it's an easy read one of the things that i think is a really good take away from his book is he helps you communicate security to sea levels a lot some of us struggle with that verbiage and bridging that gap in saying things well no we need to protect this or this is important i need
money to buy this tool to buy this widget or to hire this person to hire this talent or go to this class well why because i want to make that i want we need to protect stuff well he helps you translate the how to protect and how to build an organization and how to build a team that's another really good book i think it's like 299 on amazon on kindle like seriously three dollars to invest into your knowledge base so we'll talk a little bit about the objectives there's two objectives for this talk yes sir
sure it can you say the title slow i see some people writing security and privacy in computer systems willis where is the author from rand corporation thank you for sharing anybody else have us a reading suggestion awesome okay so two objectives a day challenge the way you think now and encourage critical thinking i think critical thinking is this skill that a lot of us lack i see a lot of people coming out of um technical hands-on classes or degree programs and i get around these like super whiz kids smart like they could red team and make your network look like swiss cheese right but then when i asked them so what you made it look like swiss cheese but
to what end like so what like even if a bad guy could walk through every one of the holes that you've punched in this network so what what would he be after what was what would his objective be what's the secondary and tertiary effects of these holes not being plugged what's the business impact to this not being plugged what leverage or strategic advantage does being in your network give the bad guy if you're not his target and a lot of them can't think past oh my god i got domain admin on a domain controller and so you own the network now what what are you going after in here now what's important that's not on your list of things that's
important and trying to get people to do that critical thinking beyond just the immediate threat is something that i find a lot of us don't do we have a tweet goes out here's a new o day somebody didn't do responsible disclosure they cause fud everybody's hair's on fire did we plug it yes we plugged it okay and we're done and we we we stopped thinking beyond that it's plugged is it patches patches done so critical thinking if you're interviewing people try to find a way get with your hr people to have some sort of interview set of questions that actually helps reveal whether or not somebody can actually do critical thinking let them tell you areas that they're
strong in and weaken and then give them something that they're weak in but just see can they figure out a solution i did an interview i do not write pearl okay pearl i was like uh they showed this man i was like i have no [ __ ] clue what that is and they're like well what do you what do you think i looked and i was like well let's see program or basics teach me this anything on the right side of an equal sign goes into what's on the left side of an equal sign and i just started you know taking it down by the basics and could i tear it apart and i said well i don't know for
sure that this is what it does but this is what i think it might be doing but to get an answer i would go here i would go here i would research this i'd research this and i would figure it out and at the end of that interview they were like you were the only person who was ever literally piece picked it apart step by step to try to figure out what you could you identified what you know what you don't know and then you figured out how to go get the answers for what you don't know and i find that we don't have a lot of people that can do that that's not a
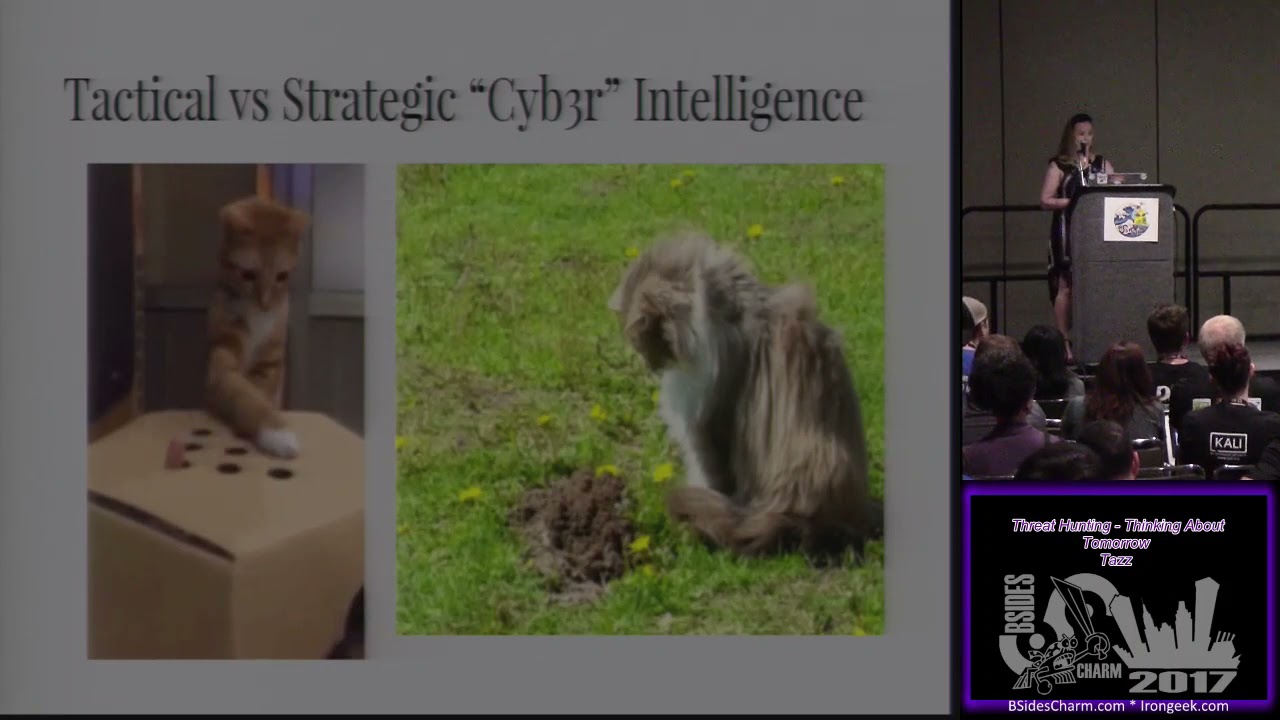
skill set we have we're good at one thing we stick at that one thing and we don't want to go outside of our box so critical thinking is something that i'm really trying to encourage with this talk here so tactical versus strategic if you are on the left side of the screen you are playing whack-a-mole with iocs and malware and viruses and threats and trojans if you are on the right side of the screen you are probably doing some level of strategic but intelligence something tells you there is a hole here that probably shouldn't be here you don't know what's in that hole but there's an interesting hole in front of you and you are going to figure out a way to
determine what either went in the hole is still in the hole or came out of the hole the hole is here i have evidence that something was here i don't know what it was but it's going to take that cat on the right a little bit longer to get his answer but he can still get his answer right how many of you are cat fans okay yes i got i got one brownie appointment okay so a little bit of difference between um strategic and tactical most of us i would say 90 percent of us that are infosec live on the right hand side of this slide you're always being asked what what's wrong now what's going on
what's you know what's the threat landscape look like what's the latest threat and you're dealing with answering what's current and what's now the threat intelligence you have to derive is iocs ttps network artifacts forensics they want the bottom line up front that's what the bluff is and it pays immediate dividends and it's really easy to get funding for dividend for things that are going to show immediate return right how many attacks did we block on the network right when you start turning over your metrics dealing with the right now and the number one differentiators are at the bottom in red you have indicators of compromise which means what somebody's already got you right but i'm trying to get us to start
thinking about indicators of attack and i'm not necessarily talking about the fact that yes somebody nmap scanned your your network right i'm not talking about that i'm talking from it a little a little bit bigger than that but the difference is that strategic investigations are timely timely doesn't mean it's a long time it just means it's on time usually now if you've ever done military intelligence or threat until of any intel of any kind people are always complaining well why didn't you tell me well i did try to tell you but you didn't want to listen well why didn't you tell me sooner well because we couldn't know that we don't have a magic eight ball and you
can't predict everything okay so there it's timely just meaning like you say you know what there's a lot going on in the south china seas right now i wonder how much of what we make is manufactured in that region do we have any third or fourth order elements that come from any factories out there do we own any assets in that area might somebody want to use us as a pivot point to get into somebody else's stuff and that's what i'm saying timely being aware of what's going on in the world strategic is also about making connections and it's not always a to b it's normally somewhere from a to j right you're trying to connect the dots
and amongst the bread comes with strategic intelligence that's why it takes a little bit longer to develop it does pay exponentially in the long run though if you can anticipate an attack you do not widely advertise that you have put mitigations for things in place and then you see that attack that you predicted come and that attack fails miserably that pays dividends how many of you guys remember the uh denial of service attack with mirai bot okay big news right was anybody talking about the botnet attack that had happened to the provider in canada that was twice the size it wasn't on the news why because brian krebs wasn't there right okay so but brian krebs gets shut down because
whatever people are trying to ddos his site and all this other stuff but the point is that i sat and i started we started talking about that and i said you know how many people thought about the other strategic partners that were behind or locate co-located with brian krebs's website how many of them said oh well maybe there was a whole bunch of noise made over here and a lot of attention drawn to something because something else could have been going on over here how many of you guys have ever heard the theory um that maybe ransomware is used to cover other malicious activity okay well when the first piece of ransomware hit and i was and i was
sitting there i said you know what i bet you they did some other [ __ ] on that network and they just want them to not pay the ransom so that they'll nuke it right if a ransom is so high that it's cost prohibitive to pay for it they want you to nuke that system right i'm sorry if i'm holding a ransom is it my objective to get paid [Music] wouldn't if i'm going to ransom something usually an objective for somebody trying to hold a response to get paid right you don't want to price yourself out of getting paid if your true objective is to get paid so again this goes back to critical thinking a lot of a lot of people
weren't thinking like that i was approached about should i pay a ransom or not and i was like um well you're kind of effed if you don't have backups but if you do have backups i recommend just putting this on the shelf until whatever that is can be reversed or there's a solution later because you might be surprised at what you find out is actually was a bigger problem that if you nuke that system you're going to lose that evidence
yes
very good point so where does strategic threat thinking come in many of you guys have seen um david bianco's uh pyramid of pain how many people are familiar with pyramid of pain okay if you're not familiar with the pyramid of pain it's excellent um i credited james dietl on this as well because he added to this okay but basically starting from the bottom to the top it's how difficult is it for an attacker to modify what you see in the pyramid once you get past ttps though what next how many of you are actually doing target development from an attacker perspective after you have ttps not very many hands in the room are going up and that's
really why i'm here today like we stop after we identify ttp and god bless the guys that made the uh apt at the encyclopedia y'all forgive me i'm horrible with names but like going through and reading that and if you've done threat modeling and you understand where your threats come from are you us-based only are you global you know things like that i had an interesting story the other day shared with me when i was talking about my talk and i will leave the company nameless but the individual mentioned to me i said you know a lot of us don't think about the fact that we have a page on our website that says these are our strategic partners how
many of you have a strategic partner page listed on your company's website somewhere or across the bottom you list all these big name companies that your product is used with or you partner with well he and i told myself so what happens when somebody doesn't like somebody you partner with strategically you become a second or a third domino if they are the end target okay you may not be yes i was that was there's an obvious one but and the reason i didn't use the target example to be honest is because it we get hung up on the word third party service provider being a strategic partner isn't the same as being a third party service provider
there's sometimes you can be a reseller a value-added reseller of a strategic partner right how many of you are vars or know what value-added resellers okay so when you have and we'll just pick like networking technology right when one vendor can go in and do a consultation with their client and the client says i want to stand up a network right how many vendors do we have to make routers and switches okay well they could be a value-added reseller that could sell any one of those routers and switches right they're bringing them in because they feel like they should be unbiased right like you're going to give me the best recommendation to build my network
because you're not actually selling me the product you're going to get me the product that works the best so if you're a value-added reseller and you have a strategic partnership with somebody do you think you might be a target if somebody has a personal issue or a hacktivist motivated issue with somebody that you partner with and the story they shared with me was that there was a they were strategically partnered they are a security company and they're strategically partnered with somebody else and the leadership of that partner did something that human rights activists were just over the moon about right and they didn't think that they would be the target they're like oh man you did this socially unacceptable thing
you are like buddy watch out hate it for you but what they didn't realize was that they were actually becoming the domino to get to them not because they were a service provider or anything else but because they had a strategic partnership with them so what i want us to start doing is if we get to ttps and we get to that level this is where the strategic thinking starts taking place after we've done all of these things in our day-to-day infosec world
excuse me
chad that hmm is for you okay so um but so strategic thinking can come in before or after a breach before you have a breach in malware you want to ask yourselves what do you have that's critical input to someone else we talked a little bit about this and what serious vetting have you done about third party vendors notice i didn't say service provider i just said vendors um isps especially they how many of us use internet at work how many of you own your own internet not very many of us right um if it's after a breach when you think about what was taken or accessed that was not pii and why would somebody want that tinfoil
hat moment how many of you guys remember the anthem breach okay was it i know the very first one you're you're you're correct the very first one how many of you guys remember that how many of you guys remember all of the articles that followed about those health records being sold which was how many records got sold how many health records actually got sold how many of you guys remember the opm breach that followed not long after now if i wanted to assassinate somebody wouldn't it be great if i had all of that information from opm and then i had all this information about their medical health to make it look like it was a natural
death tin foil hat i told you right but these are the kinds of things that putting making connections between what are sometimes seemingly unrelated events and seeing how they may affect you right if something in your city gets hacked right how does that affect you how many of you guys heard about the sirens in dallas that got turned on oh yeah i'm on i'm on the the dc 214 group man the threads we had on that right so we had everything from people saying you know hey i think this might have been a test of the system to see how emergency responders respond to we wanted to some attacker may have wanted to see what the threshold of the
911 system was right um if you guys do military type stuff you know people will go in set up a small bomb see how long it takes for emergency responders to respond and then there were secondary attacks that used to come after that too and so and but they learned right they they did these little tests so we have every theory under the world in the world going on there and so i started saying you know how many people are keeping up on iot um air conditioning type stuff okay i have a few people keeping up on iot air conditioning can you imagine dallas texas in august if i could turn on everybody's air conditioner so that they
couldn't shut it off i can overload the power grid which can cause brownouts and blackouts which could then allow me to do what whatever the hell i damn well want to right but again can we go back to imagining these kinds of scenarios so how many of you did your c levels list your iot air conditioning control units as things that are critical to protect nobody but if we sit and we think about ourselves and what we have and how we can play a strategic role in somebody else's attack those air conditioning control elements seem a lot more important now don't they right again going back to imagination so we get hung up on breaches and pii and
let's be honest we're all numb to them now aren't we right like 10 years ago when the va guy lost the laptop that had all these veterans oh my god here on fire now it's like i literally retweet uh for two bots that do nothing but tweet breaches and i probably retweet that bot those two bots like i don't know five times a week right so we get all hung up on pii and everything else but a lot of times we're not thinking about what what else beyond pii like i'm sorry i don't think they hacked into opm because they want to make credit cards in my name or that they want to steal my identity
probably not the objective right so if you find people that are in your network or you find something unusual or anomalous a lot of us go straight to to going to the pii and we're looking in our networks at the at pii or credit card information right because we don't want to get the fine we don't want to get the whammy but what else do you have from a data perspective that could be a strategic value to somebody else i promise you it's probably not the pii that you have how many of you guys have blueprints how many of you guys have schematics how many of you guys have manuals how many of you have a library with
manuals of [ __ ] that's older than your grandmother but somebody scanned it in the pdf right so if i needed to get information from something that's not easily available on the internet and i know that you have a massive library that has all the information i need to be able to plan the next stage of my attack do you think your library might be of value to me but these are these places that we go looking for bad guys we're not looking there right so it's time to take a look at what you have that's going to be of value to an attacker where you are the second or third domino in the attack
that you are not the primary target
yes
so for not everybody here in the room is when we since we use the opm attack right if somebody in here works for a bakery they probably don't care so that wouldn't factor into their strategic thinking but if i want to think about what somebody could use with that information say i so i would think that here here i'm if i'm going to make up a scenario off the top of my tin foil hat um opm data one of the things we lost was fingerprints right okay blood types so if i am an organization that is doing anything with um uh biomed i was going to say biohacking yes biometrics so if i'm an organization that does
biometric research right or i'm a university or i'm a call you know a college um pharmaceuticals if i'm doing anything with bloodborne agents if i'm doing research in bugs and entomology or um uh like um herbal solutions right say i'm an herbal company and i'm doing research into benefits of herbal supplements or stuff like that for health conditions treating cancer or treating some life-threatening situation i might need to keep in the back of my mind that okay well if somebody has all of this information about somebody else's health condition and my research where i have failed to create a cure if you failed to create the cure what did you do to the lab rat
you killed it okay so maybe my failed research needs to be protected just as much as my ongoing successful research so i'm doing the tinfoil hat like it would so my answer to you is it would depend upon what company i'm working with as to what other things or you know historical events have occurred as the would be relevant to them does that make sense okay i think i saw a hand yes
um
is very good point yes ma'am
absolutely easy way to blackmail somebody huh okay did i have another hand back there add one more comment
um
is well from the corporate sharing perspective i i mean yes i can see those i don't say i agree i can see those arguments um but from an infosec perspective if we can't think of it nobody said we had to share it right but if we can't think of it and we can't think of those connections then how would we how can we even begin to protect or defend or justify sharing them it's okay in your own corporate boardroom to sit down and draw the breadcrumb trail out on a whiteboard and explain to somebody why this thing that you guys have that may have been not so important five years ago is probably way more important now than
what they realized because i understand we are we are all of us how many you've been called a hacker who's not been called a hacker by somebody in this room right so like and i try to tell people i'm not a hacker you guys quit calling me that but be honest they look to us as hackers for that expertise right they don't understand how somebody's going to pivot and do and cause the dominoes to fall right we have to lay that out for them if we can't lay it out for them then there's no way they're going to give us money or resources or help us hire the talent that we need into our teams to protect
these things right or that they're going to pay to take the measures now yes i'm not going to spend 10 million dollars to protect something that costs a thousand but what if i made an argument that that one thousand dollar thing really is way worth way more than one thousand dollars you think it's a thousand dollars boss man but really that's like a a one trillion dollar value to these bad guys sometimes it may be that you need to go back and help them reevaluate the value of an asset and that is something that i find is the most common because they undervalue it because they don't understand where it fits into an overall attack
strategy so now we've gone from oh i'm sorry yes
but data can also be used to uh missing data can be eliminated for example opm databases millions of federal employees
now we know why now we hear why the rat died right okay yeah that's a very good point so we've gone from being able to imagine motives goals structure organization methods of adversaries to now can we comprehend them can we actually begin to understand why not just fairy tale land let's take it to the next level let's actually comprehend that this scenario is possible we're not getting into grading far-fetched or not yet possible right so now i'm going to talk a little bit about a variety of disciplines and this is these are literally just some this is not an exhaustive exhaustive list but in taking real world events and then making you think about something that
might be a related cyber target and feel these slides are going to get posted on speaker deck so you guys will be able to have access to them i'm on speakerdeck.com forwards last year c ninja with no underscore so from an economics perspective anything that can alter the value of currency when you have trade agreements um who likes who who plays well with each other versus who doesn't play well with each other maybe you have a social uh movement going on in a particular region where maybe your company owns resources or acquires resources from and anything that's industrialization or provides access to education and information as westerners a lot of times we take for granted
our ability to google something we take it for granted that we can get a quick fast easy answer by jumping on any internet enabled or access device right there are countries that have no internet or that they have heavily modif that moderated and monitored i can't get that word out heavily monitored internet access right citizens are afraid to even um search for things because you know they think everything from the enter button on their keyboard is hacked all the way to their isp provider right and everything in between so where would a strategic threat fall that you might want to start looking for in advance there so these are more of questions and i i
always tell people from an economic perspective think about what affects your ability to have commerce not e-commerce just day-to-day commerce does your company um ship things not that you're amazon but do you ship things do do you mail products somewhere or if you're not a service oriented industry you're a physical component that you provide what affects your ability to monitor your supply chain your product when it's on a train when it's on a truck when it's on a plane what affects your ability to do that kind of monitoring those would be a strategic target if you're the person that provides another company's ability to monitor where something's being shipped and when it's there right maybe what i want to do is steal
their stuff right maybe i want to destroy it maybe i want to blow it up maybe i want to make sure they don't get the shipment okay so who am i going to go after they're my end target but who am i going after i'm going after anybody who's doing the logistics support right logistic companies i'm sorry if you work for a logistics company you are a total target all the time for everybody you are the third domino for everything um exports and imports product manufacturers if you definitely you know that you're a target um second or third order and something if you are anything that you make is controlled by export or import okay and
there's one more thought i had on this oh if you are an enabler the last one listed if you're a vendor of technology software or equipment that supports these things as well if you make a and it's a really bad example so there was a washer that was made by a government contractor and that government contractor provided that washer to airplanes for the air force and the parts kept breaking and it almost killed service members and then they had to go backwards to figure out that they were getting inferior washers okay the plane's flying something starts to fall apart plane falls off sky right we don't want that but the washers were inferior well it wasn't that the government
contractor was providing an inferior washer it was that the plant where the washers were being made had been compromised and the alloy the other metals that were being mixed into the raw liquid form of the metal before the washer was molded and formed is what had got compromised they compromised the company that provided the input to create the washer so that they could make the planes that were using these washers vulnerable or weakened again strategic thinking right second or third order steps yes
and
and if i could manipulate the counts at the person that's supplying it to you not compromising any military assets but i'm able to compromise the data that comes in right and you're just the shipper and the shipping inventory form when i scan that barcode is going to automatically update my quantities right what if i can [ __ ] with your barcode how many of you guys have ever done stocking in your life did you ever count or did you just zap zap zap zap zap that's what we do we're gonna zap zab zap and go because we want to go home manual labor sucks but seriously i mean so to his point though if if i could if i can
if i could manipulate the printer that's printing out the barcode how many people have your printers listed on your top three to five critical assets two people yay no i'm checking okay so um
okay he's mumbling he can't share it's okay so um from a business paradigm uh where threat actors may be looking to compromise something if there's an acquisition we know that when somebody's buying somebody else that's a great time to get in there and screw with stuff because everybody's counting the beans and the bean counters before they buy the new company you want to make sure that everything's on the books and all the companies resources are going into making sure that the merger and the acquisition go well and we kind of start to cut corners to make things uh work well together we start to punch holes in firewalls so uh yeah or we're just gonna
we're gonna leave that open all weekend so that you can get it done before monday yeah okay um but who who might be a strategic target if i'm if there's things going on if there's an acquisition going on or a major competitor announces a product because let's be honest strategic threat intelligence sometimes the bad guy is simply your biggest competitor i mean corporate espionage is nothing new we doesn't you don't hear a lot about it in the news but man that's some vicious stuff like i've literally been contacted and asked to commit a felony on behalf of somebody they were going to pay me a lot of money i'm like there is no amount of money you
can pay me for me to go do that no you need to find another solution that is not that is not how you do that so um but you might want to be thinking and again with the washer example for the airplanes who made the tech that's in the equipment how many of you guys remember the tsa scanners and i forget the researcher's name who went in and found the x-ray was it the x-ray machines i think it was and there were components in there that had no business it being in there made from china that were literally communicating data across the airport networks back to china anybody ever think about the tech that's in the equipment that you use
go rip it apart give it to spencer he'll reverse all of it get to josh um purchase orders also revealing your capabilities how many of you and if you're military you get this but if you're civil you might not wouldn't it be really cool if i knew that you just bought a thousand cisco switches wouldn't it be interesting if i knew that you had only bought two cisco switches ever and never bought another switch or a router for your company what do you think purchase orders say about your capabilities and your ability to defend or the lack of a purchase order what if i if i can get in to your
finance department i'm not going to go after your strategic finances but i can go in literally to a share drive and i can traverse a directory for everything that you've bought in the last 10 years because who puts that on a share drive right nobody would ever put old invoices on a share drive that everybody can have read access to right
did i say that of course intellectual property is always a strategic target and then your strategic partners lists and calendars you'd be surprised what you guys put on calendars about who's going to what conference and you make it public yeah uh military i just um a lot of strategic targets if you are key leader and this was um and when i say key leader here i'm also talking about military key leaders in foreign countries not just our own right but if your ceo or your vice president or your coo is going to fly to another country to um visit with somebody over there for selling your product line right establishing new business in a foreign
country because you're expanding or you're global it might be interesting to think about or know of the types of technology that they have in the vehicles that they're going to pick your ceo up in at the airport right well boss do you know what they're picking you up in do you know how you're getting there do you know what your travel plans are from point a to point b um by the way maybe since you're going to go visit china we don't take your corporate laptop with you let's give you a new one how about you take this ipad instead i mean a lot of times we don't think about those things or we bring them back
and how many times are we actually going through those devices after we bring them back or are we just taking them and saying thank you yes no boss you cannot put this on the network i'm putting this in the closet and then we're just going to wipe it for the next time that somebody wants to go to china but how many of you ever did any forensics on that not a lot of people do right a lot of people just have a laptop we issued out we never think about what might come back on it you'd be surprised um critical infrastructure i know i've got some scada guys in the room ics guys in the room critical
infrastructure we're always talking about that but like i said from a strategic perspective if i really wanted to bring down a power grid what's easier to hack a thermostat and control all the thermostats in the city or in major buildings or for me to go hack the power plant what's an easier target the thermostats right okay so my favorite here is don't kill the researchers okay don't kidnap them don't torture them simply socially engineer them at a bar get give the researcher a thumb drive he'll plug it in because he wants to know what the new cool research is that you have so um but again if if there are things going on from a diplomatic perspective
that are in the news you probably need to be paying attention to those especially if there's government private or government funding that gets awarded to somebody or something and i will tell you like one of the groups that we underestimate are hacktivists we think that a lot of them are out there just interested in defacing our websites there is so much more that motivates those people they're not in it for the money they're in it to invoke social and political change those are some serious emotions that run really really deep so think about what you're doing or who you're associated with that a a hacktivist group or a social activist group are really vocally screaming bloody murder about
on the internet on their blogs on their chat forums you know or they some reporter talks about it pay attention to that kind of stuff those are early indicators that something's coming uh we're not going to talk about the elections if you raised your hand for elections we're not talking about that non-joke yeah oh five minutes okay if you guys need to go i understand um i've only got a couple more slides left and we'll be done for questions um but if anybody's hungry needs to go eat i get it i'm not offended so um infrastructure we just talked about that i i wrote a tinfoil hat blog little while back about how i would how i would go about a three
level or four level stage kind of attack to try to hack ics now mind you if you read that i am not trying to say that ics hacking is easy by any stretch of the imagination that is not what the point of that blog is but it's to say that if i wanted to get into it or i wanted to affect ics stuff how would i go about doing that from a strategic perspective and it's just a different viewpoint on that but we all know that how many you guys follow the reports that dhs used to publish on their website about our critical infrastructure they stopped in january they only took them how [ __ ] long
i mean really like and now you can still go get the old reports like i don't get it like you know it's like if you're not gonna publish anymore how about you take down the ones you've got up there we don't need to know not everybody needs access to that but um one of the research projects that i did was on black energy um events in ukraine and i was surprised to be able to go out and find a source that literally listed every manufacturer for every boiler and every engine and every component that they had in every nuclear hydro gas coal power plant that they have and all i had to do was register
but like this one a single location for this information globally and we're filling it in for them like voluntarily so data manipulation that would be a great place to do it but it's just saying that that information is out there so how many of you think about um research in weather controlling weather okay that's a great strategic target for somebody okay um who would be the targets uh conferences where multiple critical infrastructure vendors are gathered because we would never hack the wi-fi at a hotel ever never right um you never socially engineer them chat them up at the bar right never do that never give them a cd of a something really cool presentation that they can go watch later we
no bad guy would ever go through that length would they give back so technology this slide was more for the non-infosec groups but basically how many shared service providers does your organization actually use and then once you can identify those find out how many of them actually use the shared service provider to provide you a service that's probably the one that one of the ones that i'm seeing more often now when i'm asked or when people are finding problems or i suggest places to go look it's not at their immediate third party service provider it's at a service provider that they use that they aggregate to provide you a service
the bottom one here you guys might laugh but i was actually actually had a volunteer target for an ocean project and he was the navy seal commander i found everything i needed in one family obituary and his knights of columbus membership but a lot of us let our guard down when we're not at work so your c levels your managers sys admins how many of you guys are providing your real information in your hobbies and we kind of let our guard down when we walk out of the office but these again are places that would be strategic targets now do you think that your bowling league secretary thinks that she's a target she probably doesn't but after this talk
how many of you think she might be yes the bowling league secretary if they're not infosec as a total target and then if there's religious events going on in the world the buildings those icons uh memorials celebrations especially in uh non-western countries that are heavily divided if you have assets there think about how your assets might be used to leverage an attack so how many guys remember the boston marathon okay so there's the boston marathon we had the bombing in the boston marathon how many of you guys think that any of the um businesses along that route ever thought that they might be a pivot point for an attack probably zero okay so these are the
kinds of things that are going on um and i it comes i don't know why i thought of it now on the religious slide but um so if there's something going on around your corporate headquarters there's going to be a march there's going to be a marathon there's going to be a march for dimes something like that you guys might want to take additional measures and start looking at things because a lot of times those are times when we try to get people out of the offices to go participate in these things for good pr right so take a thought on when you see those kinds of events going on like how somebody might use
those events as distractions for what's going on for you or use you to make a statement if they're a hacktivist activist or a terrorist and no magic eight balls you don't find strategic intelligence you guys you develop it you talk you do critical analysis there's not a single [ __ ] strategic threat until feed out there if they say they are they're full of [ __ ] okay you can't buy this stuff in a feed you have to be sitting down going through scenarios and the scenarios are going to change regularly because life changes things happen world events occur staying abreast of proposed legislation is also key how many of you guys know that there's actually
a um in the house and the senate there's proposed bill for defining a cyber act of war any of you guys in the defense industry might make life a little bit interesting once the president actually defines and they pass that and he creates a definition for what a cyber active war is staying abreast of proposed legislation is another way to understand where attacks might come from from a strategic perspective
and i get asked this question a lot i'll go through this quickly just like if somebody was going to hire a strategic threat intelligence analyst like what characteristics do did i think and i just kind of put together a list of basic skills the number one though is their ability to think creatively and critically that single-handedly is probably the biggest skill set that i think someone could use on your team now mind you this person doesn't have to be a red teamer this person can have a master's degree in history in a region that you guys operate in you can teach people cyber but you can't teach people people right so i'm just going to ask you to take
this slide with you and ask yourself if you think you actually understand motives goals structure and organization and the methods of your adversaries
and i hate to say it but i think i'm gonna say it cyber i think this is the domain where we can probably do this the worst but my greatest fear is that no war fought on the line is ever going to stay online boots will go on ground eventually and blood will be shed we will never totally fight a cyber war in cyberspace questions yes sir oh we're not talking about that that's strategic intelligence right there um i know right um so does so does did anybody learn anything today [Applause] and i am and i understand this is probably not the forum that some of you guys may want to ask me your one-on-one
questions about your organization or whatever feel free my dm is open on twitter if you want to be obscure you don't have to follow me you can message me you can find me after this and i'm happy to answer any other questions it's lunch time go eat





