Operation Grand Mars: Defending Against Carbanak

Show original YouTube description
Show transcript [en]
Good morning, and I guess we need to start, we are somehow late. I've been told that we need to go through this in English, so now any language is Greek, let's try to switch into English and see how this is going to be. So, good morning, first of all, and thanks for being here. As you may see, I'm the Kanasi Giorgos, I come from the pathway, and I'm here to give you a presentation about something that we call Operation Grand Match, and maybe So So, let's start. What is about the Operation Draft Match? Operation Draft Match is based on a report that we published in January this year and this comes after multiple investigations that we did, forensics and incident response investigations that we performed for multiple customers,
mostly that have been in Europe or in the US side. As we see over there, and maybe I need to explain a bit more what is this based on and what exactly I'm doing, this has to do with forensics and incident response. And what exactly is forensics and incident response? You know, many times when you speak about forensics, especially on incident response, people get excited. And they think, oh, that's really cool, that's really nice, I really like that kind of stuff. Yeah, I would say that's good, okay, I mean, the point that you might like this kind of job or the point that passionate about this. But what exactly this is and what we're actually
doing. As you saw before, I'm just working in the EMEA team. I'm leading the EMEA team and the point we're doing is that we get the alerts from customers that already exist in customers of ours, from customers that are under some emergency, that they feel, they know there has been some attack against their network, against their own environment. and they need to understand what happened, the extent of the attack, the extent of the common lies, if data have been stolen, if data have been leaked, and what they can do at the time that the attack is taking place in order for them to defend. So as you might already understand, forensic can erase the response,
of course not a lot of panic, not from outside but from customer side. I would say we are not panicked, that's why we are getting paid, we have customers in the site. I know It comes to the mind that we might use some very specialized and extreme tools. Yes, that's true. From time to time, or maybe almost all the time, we are using some specialized forensic tools. But don't be confused about the tools. It all has to do with the knowledge. It all has to do with your investigation instincts and how you plan to use the tools. We might be, I mean, human beings might be different from the rest of the animals because we are capable of using tools,
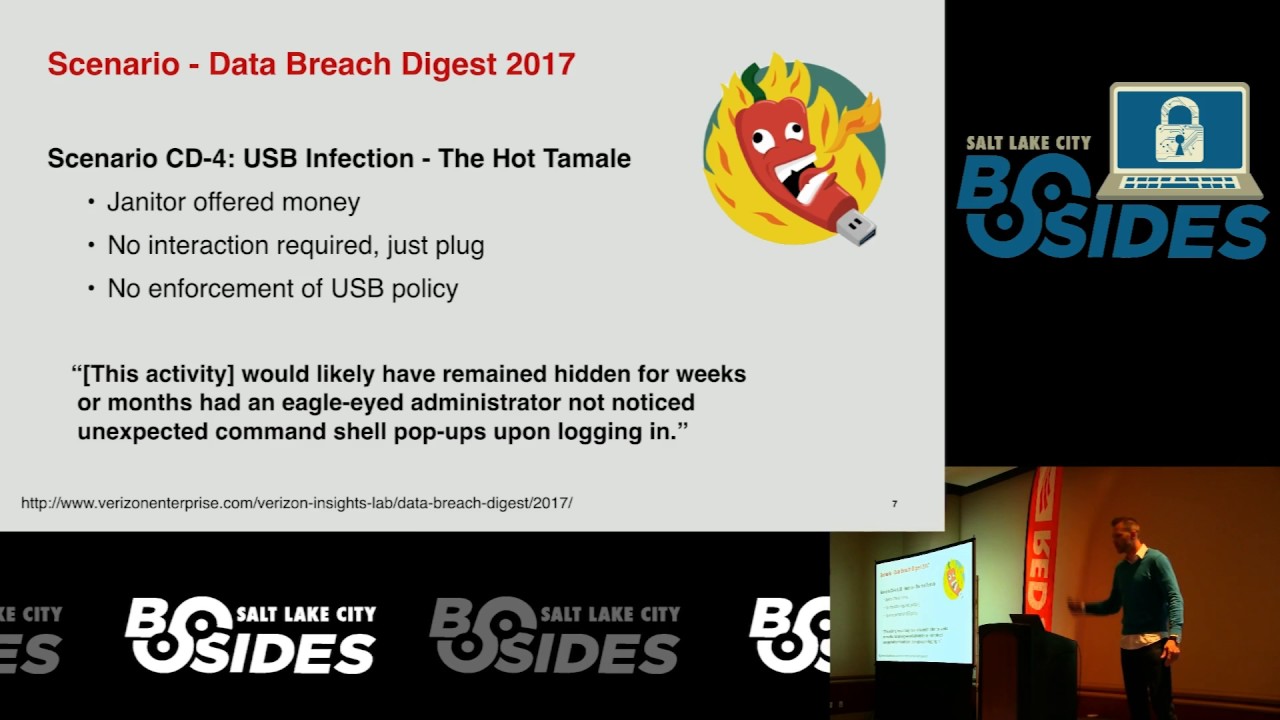
but this doesn't make us smarter. What makes us smarter is actually using the tools in an efficient manner. So, let me start after giving this short introduction about forensics and its technicals. So, let me drive you through this operation quite much and explain what happened in the whole operation. it was during the october last year october 2016 when we got a notification from an existing customer that they received something really okay the wind the projector here we may see here that's an aviator okay that they received from one of their workstations And that's another alert, okay, that receives from another system. Now, what I wanted to show here, that maybe the resolution is not yet in the log, is that we
have a difference of three days. So that happened on 24th and this happened on 21st. So there are three days difference between those two events. What is exactly the difference? The one in the back, this one, happened on a normal workstation. Okay, workstation lying somewhere in the network. This one, that triggered the actual investigation, that triggered the actual alert, a customer gave us a phone call and said, "Hey, I believe something is going wrong." This one happened on a domain controller. Most probably you are aware that domain controllers are supposed to be some kind of critical assets in our networks. Okay, why this? Because they're holding the whole database of users, permissions, tribulations, stuff like
that. But what I want to show here is that we have a three-day difference. The workstation and the domain controller. What is those three days difference? These are more than enough for the attackers to finish their job. So, what I'm trying to show you from this slide is that on 21st of October, when they had the first alert, it was the point that the attackers initially attacked or let's say That's their network. Three days later, the attackers have moved to another region, like what was in France and what was in the UK. Three days later, they managed to move to London, to the UK. UK side, they managed to compromise the domain controller but everything that they wanted to do has already been done. So you see, something
that maybe happens a lot of times with IT people and normal IT operations is that they might consider in their mind that "Okay, yes, that's a workstation AV alert, okay, that has been cleared, so don't care a lot about this." But when it comes to domain controller or to a more critical asset, then maybe we need to start alerting people and start some investigations. But we need to keep in mind that many times, many times, especially the AV alerts are at the tip of the iceberg. So there might be a whole large operation running in the background, operating back there, and we only see the tip of the iceberg, which are some minor AV alerts.
What does the customer show? They just show this kind of event as well, which is... This one is a PowerShell command, it's a long PowerShell command, encoded and this has become very very famous these days. And what exactly this is, this is maybe you have heard of this, you know, called the "gay on the news" and by security researchers, that we are getting into a season, we are getting into an era where we are not talking about malware, we are talking about fileless malware. So malware that does not exist. What exactly is this malware that does not exist? Maybe it's just an idea, you know. It doesn't exist as just an idea. It's not exactly
an idea. They exist, but they exist in a very volatile environment. And what is that very volatile environment? That is the runoff memory for operating system. So these were the events that triggered the alert for our investigation to start. Now, after we got these events, and again, talking about forensic and incident response, I can tell you for sure that what we exactly were actually doing is going the reverse way. What I mean by that, we see the tip of the iceberg and we start digging down. and most probably you know i've done many many forensic investigations and meets the response and i can tell you that i've done many many researches but i cannot tell
you how many things i missed in my investigations i didn't have an idea that they existed because i don't know But I really know that there have been a lot of things that I missed. What did I mean by that? By this is not that maybe I'm not very good in my job or stuff like that. No, it's always a game and you know, it's a, I would say, it's a real life game between good guys and bad guys. When I say bad guys, I mean real criminals that have strong motivations because of lots of money, to do and then we really try very hard in order to avoid our detection so that's why i'm
saying that we need to keep in our minds that in every forensic investigation or incident response there will be most probably lots of things that we will not be able to see why that because on the other side there are also humans and they can play the game very well so I will just skip now to the final part of the investigation, that's the entry point. So you see the contradiction here. What I just showed you before was the actual AV alerts of our customer that was the end of the operation for their own environment. But now, just taking you to the entry point, and while doing this view, I want you to see the
beginning and the end. So this is how it all started. This specific customer that I took screenshot is a large hotel chain around Europe and the US. So one day they see this email. As you may see this looks like a very typical email for a hotel business or whatever kind of business. "Oh hello, yes we want to get 20 people in Paris and we are looking for a room. Please take a look at the attached list, the attached word and document and let us know what you can do." That's okay. That's not a phishing campaign, that's not a campaign that went to many many different hotels. No, that was a targeted attack. But what
made it more unique? Maybe you have an advisor, maybe you have other security convoys in your networks that will not allow opening risky or malicious or suspicious condolences. But what happened in this case is that the actual attackers gave the phone call to the person that received the email and asked the person to open the attachment. You know what this does? This might break all of your security controls. And why it breaks all of your security controls? Because maybe most of your security controls are based on technology and not on the human factor. So what are you going to do when you have a person? So I I think it's getting really, really, really, really, really often. It contains a code in
VPS, you know, just a script, okay, just a normal visual basic script that was encrypted by using an equipment software. The software was called Script Encryptor, and you can find it out there for free, okay? So what I did, I just created a visual basic script, I will show you later on what I did. That visual basic script the word document was sent to the person also with a nice written text that we want to get some rooms from your staff like that and they gave the phone to you look what happened first of all the word document was received from the user and the user was lured somehow was forced somehow using social media to open the document After the document was opened, various scripts and other types
of documents, other types of text I would say, were created in the user's dev directory. Every user can do this. You don't need to be in domain admin or you don't even need to be in local admin. There are specific folders for every user in every operating system that they are allowed to write and execute things. After writing this, one of the core scripts from this operation which is called Transface or VBC or whatever driver was being executed. Ok, so it's JavaScript just getting executed. And you know, many times JavaScript is a visual-based script. They are not malicious in context. They might make some connections. So that's why we advise you not to stop them.
Ok, it's not that all the new everything works. No, they are, I mean the attackers, the criminals, however you can call them, they are creating, they are structuring, they are acting in such a way so that maybe each phase will evade your controls, okay? So what exactly is that space that we see here at that moment? You can see here, we populated another .txt file, but we populated this file by using data that was stored in Google Docs the normal Google Documents. So what is the problem with that? No problem. Especially for the bad guys. Why is it not a problem? Because first of all, Google Docs seems to be in our minds and most
of the people's networks or minds legitimate and no problem at all. So what they did at this point, and I will show you later on how they did that, they started downloading softwares from Google Docs. Or I might say they started interacting with Google services. And then again, they downloaded another code and that was a PowerShell script, as you can see here. PowerShell is a script that allows you some activity, some connectivity to the attacker, again from Google Docs. And again, you might think, "Oh, how can this happen? How can Google become part of a cybercrime, of a major cybercrime?" To tell you another story about that, FBI also had the same idea. still discusses with Google in order for Google to try avoiding this from happening again.
But again you understand this might not be possible. Why? Because it's always the game of the cat and the mouse. So what we have here as you may see, after this point we have some word documents, some attachments, some this kind of normal stuff, but then we get Google lost. What else did they want to do? As always, in every operation, they want first of all to log in your network and get in their hands the information that they are looking for. the information that they are targeting and they also want to gain persistence and once by gaining persistence we are here to stay we are here and we want to be here and remain
here for a long time how do they manage to do this? they manage to do it through the normal ways as the times like race, the programs or schedule tasks this is, as I said, this is very it's becoming more and more this is the normal pouch from Windows Vista and Beyond this building in your operating system, very nice scripting language, but also as you understand, every tool has a list of two sides. You can say the bright side and the dark side. So by using PowerShell's dark side, you are allowed to steal credentials, you are allowed to create connections and so on and so on. Of course, keep in mind that PowerShell is not
a tool that has problems. PowerShell's capabilities depend on the user permissions. user privileges so if we keep seeing if we keep having networks with lots of privileges given to every user then why do we think publishing is not just giving privileges or not just making the main admin everyone is creating that problem okay and of course they also have something that you might have heard already the pasta house and the meaning that you know is a very well known tool that is used for something that we call pasta house what exactly is pasta house But, as the hash is actually based on the way that we authenticate systems, how we authenticate systems, we still authenticate
most of the systems based on some password. And of course, it will be longer for the password to travel over an insecure or untrusted network, we just convert the string of the password into a hash. So that means that we actually don't authenticate ourselves with the password, but we authenticate ourselves by using the hash problem. So in that case the attackers will know this really well and they don't care about the password, they don't care about the domain name or password. They only care to get the output, the hash value of the password of the user. And we have a lot of similar events. Do you know what this event says? This event says that
the local administrator is performing something that we call in the Windows world an "export promotion". This is a really strong indicator that something bad is going on. Try to think. You have a domain in your environment and you have multiple local administrators. What are these local administrators? These are the users for each workstation, for each, you know, the local, the well-known local admin. So you would never accept a local admin user to perform network robots, okay, to connect to another system and to another system. Why is this happening? Because we still have in most of the networks one very major vulnerability. This doesn't have anything to do with software or something else. It has to
do with configuration. What I'm saying by that, maybe let's say, let me give you an example. I'm an Active Directory and your Active Directory has around 1,000 workstations. Most probably, what you're trying to figure out, what will be the local administrative password for each workstation? Most probably it's going to be the same. the same or need every system so that's why they know this oh i have that you know and they are associated they are determined and they want to persist so as they're compromising the first system maybe they didn't get information maybe they didn't get their hands on whatever they were looking but at least they got the local administrator password and by allowing
network reports that uses this network local administrator they are allowed to move from one system to the other and from one system to the other until until they get the system that And this is the first step for the operation that we are actually doing. I just told you before about the trustworthiness of the Google services. Let me show you what exactly they do by actually using Google services. So what we have here is a part of the JavaScript that I showed you before that was getting executed. At this point, it says docs.google.com. They were using these two forms. Maybe you've seen this already. If you ever were invited to participate in a live survey, you may have seen something like that. So the
attackers, the criminals, in this case, they just created moving forms in the moving infrastructure and they used this in order to register and keep track of the infected system. Very nice, very nice check over time. Do you understand why? Because your infected system will not connect to Russian IP, Korean IP, whatever you consider to be suspicious or malicious. But they will be connected in Google services. So most probably, rock sheets, firewoods, whatever you have in the middle, they will not block it. And one other very big advantage for attackers is this. Here it says HTTPS. Now we use HTTPS, TLS, SSL, and all the nationalized. So this means encryption also. This might come very close
to the example from ransomware, where ransomware is just using the normal encryption techniques and algorithms for their own reasons. So this is what they need. They use, first of all, these two forms in order to raise the rate of the infected computers. And as you can see, they didn't go very far away with the name. What we have here two different things from Google. The first one is a script from Google. And this, don't be confused, this, I would say, is exactly the same as a formula in Excel. So they were using a similar formula in a normal Google spreadsheet in order to base on some decisions that they were making in the country that they were running and stuff like
that to direct them here. And what exactly this is, this is an encoded PowerShell. So this is an encoded PowerShell. or maybe I should say this is malicious code written in browser and then code. Okay, so what can we have here? The host of actual host malicious file. It's not again the asset or the crime entity, you might not use it in your mind, but it's actually a book. Again, it's a set of as you can see from a book is fresh and it's very good because it is an SSL achievement and again it has SSL values. Very, very nice thing from the advocacy perspective. what they did and how they manipulated these services in order to move on. What else do we have here? What's a
screenshot from one of the guys, one of the criminals that registered in Pastebill? You know, Pastebill is a very well-known service. As far as I remember, this also offers HDB and HDPS. Pastebill might not be considered so legitimate. We have heard that in Pastebill, they pasted information about some password-based or information on so on and so on. How they use pastebill here? They have this code and this code was checking on pastebill for specific commands. It was checking for delete bot, get code, info and stuff like that. So again they were allowed to give commands to their bots by just publishing stuff on pastebill. So if they were just putting the string in here, delete
bot, The next time that the infected computers would check on base they would just disinfect the chip or delete their own files from the infected computers. And again, you would not see here any kind of IP address assassin attack similar. Now, what other Anissio software, because after they managed to gain control on this organization they also installed other kind of Anissio software and this is one of the most this is a version called Anunnak or Karmanak, we have heard it with different names. What exactly is Karmanak or Anunnak? This came two or three years ago, where again, one large operation, they use this kind of software in order, as you understand, to steal lots of money. Now what happens before this malicious code is that there will
be one point at a time, but this will be released, this will become somehow like open source. We don't know why. Maybe because the developer was not paid well, the developer of the malicious code, or maybe there was disagreement among the cyber criminal gang. That's why they published the code. At the moment, this code for animal, carbonate or whatever comes, every source comes public. We know for sure that we will see other and other variants. Why this? Because the cyber crime community will be notified of this and will start to use their own code or their own bandwidth. But what do we see here? You may, despite it comes familiar to you, this is the
digital certificate. So in this case, what they did, two of their core malicious files, they actually signed the code by using digital certificate. That's very good again, because I remember from the time that I was working with Microsoft, we kept telling people that you need to digitally sign your Excel documents, and you need to digitally sign your software. And why this? Because this will let you know that you trust, actually you trust this file. So what happened here, actually the attackers, they went out and bought, they purchased two certificates, at least from Komodo. Komodo, you know, it's a public certification authority and it lasted for most of the thousands operating system and so on and
so on. Komodo also, if you just do a small research, you will find out that is doing this for a long time. So what I mean by saying Komodo is doing this, I would say that Komodo is a bit relaxed, and two executives are sharing their certificates. So, I mean, if they get the money, okay, they might give the certificate, or a big issue with that. But again, that becomes a very big advantage for the attackers, because they actually can sign their code. And if you have security controls, you can say, or actually we will use only signed and trusted software, this could work against you. By the way, here is the name "Grantmask". So
the signed one with the certificate by just using a FAVOR Most probably the only name in Russia, a company that they called Grand Max. So that's the name that came up for this operation. This is what happens in this kind of operation. We find a string there or somewhere else and we name the operation by that name. So these are the certificates that they bought, they purchased from the promoter, and they used. And as you can see, the malicious software that was signed has many, many capabilities. So, software that we're just using, Cobalt Strike, because I don't know if you've heard of that, but if you ever speak with a penetration tester or a similar
guy, you keep hearing about this in Cobalt Strike. It's a very nice tool, but again, it's a very nice tool that can be used also by your bad guys. So, this is very useful, very awesome, because it allows the reverse connection and so on and so on. And finally, yes, they also use one tool that they call it Adobe Update Manager. Why do they call it Adobe Managing Group? Because we really care about Adobe updates. But this has nothing to do with Adobe updates. They are trying to understand, they are trying to play with our minds and think, oh this is something from Adobe. But what this tool was doing, as you can see, it
was downloading in Excel various files and it was doing this again by using encryption. So again, keep in your mind that they will use the deep emails. First of all, what you see here is the cost distribution. So, these are not manufactured systems, these are not the Google services or Facebook or Google These are at least the systems that we managed to detect along Europe. And what I mean by these systems, these are the systems that were actually directed by the attackers in order to spread and in order to control aggression. So if you take a look here, you can see lots of, at least six servers, six different servers. One in Scandinavia, one in the UK, one in
Paris, and so on and so on. Even if we gather a large network team from a big organization, it will take lots of time for them to just design this and put this into play. So you see, they really spend a lot of time in order to design their infrastructure and in order to design their crimes and in order to design their actions because as you understand these were all inter-communicated with each other and these were all playing a different role in the game ok so here we have some eyes the blue ones is a Kalmanak, Commander-in-Chief The green ones are the combat strike command and control, the red ones are the inversions and power changes used in order to
connect back and so on. they are also doing this, they might be doing this for a very nice reason, ok? I was talking with a customer yesterday, he was really caring a lot about data leaking from his organization. And since that was a UK based customer, he said, "Ok, I would like to know if there is some data uploaded to Russia." "Oh yes, very nice." "Well, maybe the attacker is the bad guy." What I mean by that, because they know that you were suspecting everything going on coming from Russia, they will install a server in the UK next to your office, and then we'll see how it goes okay so that's why because we have customers in france or customers
in the uk it becomes much better for everyone to attack them from the same country because the less alert or less risky for them and finally some conclusions here based on this investigation and another investigation that we are doing. I would say from the victim's side, we are still in very weak detection security. What I mean by that, first of all, is the threat of the lie, relying on antivirus. I keep seeing most of the reported lies on AV alerts. And if you also remember one of the first slides, they might rely on AV alerts, but again, there is a different priority how they are or if it's a workstation which again but again if
you get maybe an electronic workstation or a device this might be again the type of You don't expect that one day the attackers will send you a message and you will say "Oh, we managed to take control of your network". No. You will identify very small pieces of the puzzle and you need to connect them together and you need also to communicate in your organisation in order for these to understand this. What else? Missing or poor readiness for security incident. What do I mean by that? apart from the panic factor or the terror factor that we feel that customers are getting into, I would say that's an error. You understand, nobody expects that more than
you will be allowed. Apart from that, when I'm saying leasing or poor readiness, if you have a network, if you have an infrastructure that is not properly configured, what do I mean by properly configured? Keeping logs. Or keeping the correct logs, let's say for example. How do you expect that one day that you will be allowed, somebody will be able to give you an answer? Nobody will give you an answer. Because again, forensics and ethics is a discourse. When we are making an assumption, when we are getting a feeling we don't base our findings in evidence, we say that that's an assumption. And as you understand, it's really difficult to base all of your investigation
in just assumption. You really need logs. You really need evidence. Okay? So that's why I'm saying that most of the economists these days are just there for keeping their business up and they're not there for finding out what happened. Again, one small example I can give here is if you talk with customers these days and you ask them how about your rates in the response plan, they will tell you, "Oh yes, it's part of our BCP or it's part of our DRP." You know, disaster recovery planning or business planning. That's very good, that's very good. But you may miss a thing. What is that? What is that you may miss? You know, especially disaster recovery planning speaks a lot about data loss of services, okay? But maybe
it doesn't give you an example about data security. or services or service abusing or services so why would you do that if somebody actually steals your data and you still have your name so most probably the disaster government plan will not help you because as i said you still have it Yes, what were the indicators that were pointing that were dealing with organized crime activities? Yes, first of all targeted social engineering, you understand. If we see a bank, we never give you a call and we say, "Oh, I'm the actual customer, the personal certificate that we made is over the attachment." Zero malicious software, purchase of certificates, yes, the methods are passed on and so on. especially Google Docs and Facebook. If you see someone so determined,
so advanced, at that point, that they will actually use Google Docs, then that becomes more difficult for them. And finally, something that came out of my... I noticed over there is that I felt when I did that investigation, it was different parties, and when I say different parties, different cybercrime parties, different people from the cybercrime community, but they were doing the collaboration. based on my investigation that the first days it was one party that actually took over and managed to take control of the organization after they managed to upload something like 1GB of data out of their network and you know what? 1GB of data is really big. Why is it big? Because first of all they use all the time compression you understand why they use compression
because they want to minimize and secondly in some cases they are not stealing from organizations movies or everything they will just steal something that we call ASCII data if you compress ASCII data or normal TXT files you will get a really really small so try to understand how many data they manage to upload if the upload size was 1 gigabyte of data this is big and what I say is that after they manage to upload the data to steal the data that they were looking for from that customer, then we show other kinds of activities. That's why I felt that maybe some other cybercrime entities, they're trying to do other, in fact, as many computers in that network, and they can
control that network in order to use it for some distributed narrow settings and so on and so forth. Okay? Any questions? Thank you very much, Nathan.