BSidesCharm 2023 - Make Better Risk Decisions to Prevent Future Cyber Attacks - Nathan Wenzler
Show transcript [en]
foreign
[Music] we're gonna go ahead and get started thank you all for showing up and coming back from lunch uh on time and all of that hopefully uh this will give you a little time to process and take a little bit of a breather while we have a have a chat um very happy to be here um came in from the West Coast I'm from Portland Oregon or living in Portland Oregon these days so please forgive me a little bit if I'm a little slow it's still technically morning for me and I have not had enough coffee so I'm going to try to do the best I can slightly less caffeinated than normal but uh we'll go from there
um oh man I mean yes but I'm I'm talking now so I'm good I'll get it after though but thank you appreciate that um thank you guys like this is the first I've had audiences just like Pony up coffee this is gonna be great I'm gonna remember this um so before I talk about what we're going to talk about today Beyond this title let me talk a little bit about who I am and why I'm here because I want to kind of set the tone a little bit for why I'm standing back here to talk to you today um I've been in infosec for my entire career just about um actually grew up in food service with
my family but moved into Tech when I was pretty young and uh started my current government I did a little backwards where a lot of folks retire into government and end their careers there I started there spent 15 years in a variety of jobs mostly the state and local level but I got loaned out to some federal programs that gonna I'm gonna do the cliche thing I'm sorry I'm still not really able to talk a lot about it but needless to say I was building an incident response programs for some agencies like 20 years ago or so um working in government's an interesting thing when you start your career because aside from it being five
years behind in everything we always like to joke about it's a great opportunity to kind of do everything because they had nothing in fact one of the county agencies I worked for was indicted by a grand jury for showing negligence of taxpayer money because they didn't have a security program in place to protect a little over a billion dollars of tax revenue that year and a security team was formed and I got to be part of that and that's where I started I literally had to do it all install tools do the Ops side of it build policies train people all of it it was actually a really great starter for my career I touched on a lot of
different areas and as time went on I got into the private sector I led teams I was a CSO at a few small organizations I got a new executive Consulting for a while which I like to refer to as organizational psychology which is really what I was doing it's all people stuff right they come in and tell you why doesn't our security program work it's like because people are involved like there's no magic here you don't need to buy more tools you have the tools we just got to get everybody on board so I stand here today I work for tenable in full disclosure as um kind of I guess the field CSO for the
company you can kind of think of me as that way but I live in kind of this weird place where I don't work in sales or marketing I get to do this to come in places and talk to people and even for our customers I do some advisory work still to this day and uh I love that kind of role because I've seen a lot of crazy things go down over my career um we all have our stories but 15 years in government let me tell you I have some doozies but but what I've seen is a kind of a Common Thread through all the challenges and the obstacles and the why doesn't it work and how do we do it better
we always focus on the the whole people process technology thing or tools and we like tools at our heart We're All Tech Geeks right we all love our tools but people is what makes this work and so that's really what I want to talk about today you're talking about risk decision making and talking about communication is really a story about how do we leverage what we have better ways we may not be thinking and how do we talk about it to audiences that do not understand what we do because while we consider this room and talk anecdotes all day long about security stuff your Chief Financial Officer doesn't know what we do your CEO doesn't
understand what we do general counsel doesn't understand what we do and frankly we we kind of have to figure out how to talk to them better so that's what we're going to talk a little bit about today I'm going to walk you through some observations and things that I've seen um about how organizations make risk decisions which is spoiler alert not great going to show an example of uh using some some new tool or old tools and new ways specifically attack path analysis talk about it using in kind of a preventative mindset rather than a reactive post-mortem thing and then we'll talk about communication really I just want to talk about talking because at the end of the
day where I see success and failure for a lot of security teams is in how they communicate and it's something that we have to get better at we simply must uh and we'll talk about some ways to do that and some ideas and I'll show you some examples and we'll go from there sound good long-winded intro I love Notting heads you guys haven't nodded off yet we're getting there so look when I talk to c-level Executives it's the same thing I hear all the time I know it's bad there's a lot of problems I don't even know where to start that's really the the question that comes down right where do we start now we could listen you know read the news
all the time and on a given day it's a different story right some School District gets hit with some ransomware and shuts the whole thing out ransomware obviously ransomware is the problem we better focus there and the next day it's the uh was it Capital One with their data loss from a misconfigured S3 bucket up okay so Cloud Cloud's the problem better lock that down that's the problem now and the given day the given data breach whatever it is we hear all these things are the number one problems but that doesn't help me figure out where to start and I still have that problem right I have a small team small budget could be a team of one that's a really
small team right uh I can't do it all we know we can't do it all so we got to start where it matters we need to figure that out trying to answer that question about where to start is really key now some security teams have strategies for doing that um you know compliance I see that a lot in fed space whenever we don't really want to think about where to start we'll just go down a checklist but as we all know compliance is not security so yes you're doing something but are you really yeah meaning yeah kind of uh some people just figure it out right we'll just guess at what we can do this
week I don't have a good relationship with my Dev team so we're not fixing any of the code flaws but hey let's try to patch something because patching's pretty easy all right we do what we can in that regard if you're like I am or your teams are like I was when I my very first CSO job that I ever had I was the first column um based on the west coast I had a CEO that was based on the east coast and had no respect for time zones and uh I was that person who quite literally got the phone call at five o'clock in the morning
you know I'm useless when I don't have coffee and you're calling me at five o'clock in the morning what do you want but that's how it happened right and look whether I liked it or not didn't matter what I wanted to do with my team that day myself and my team we had just gotten prioritized because when the CEO says he wants to know the answer to the question are we next that's your day or maybe you're weak right so organizations try they try to figure out we know we have all this risk we know that we've got to solve it and we're kind of just struggling to figure out ways to do that where this comes though is a kind of a
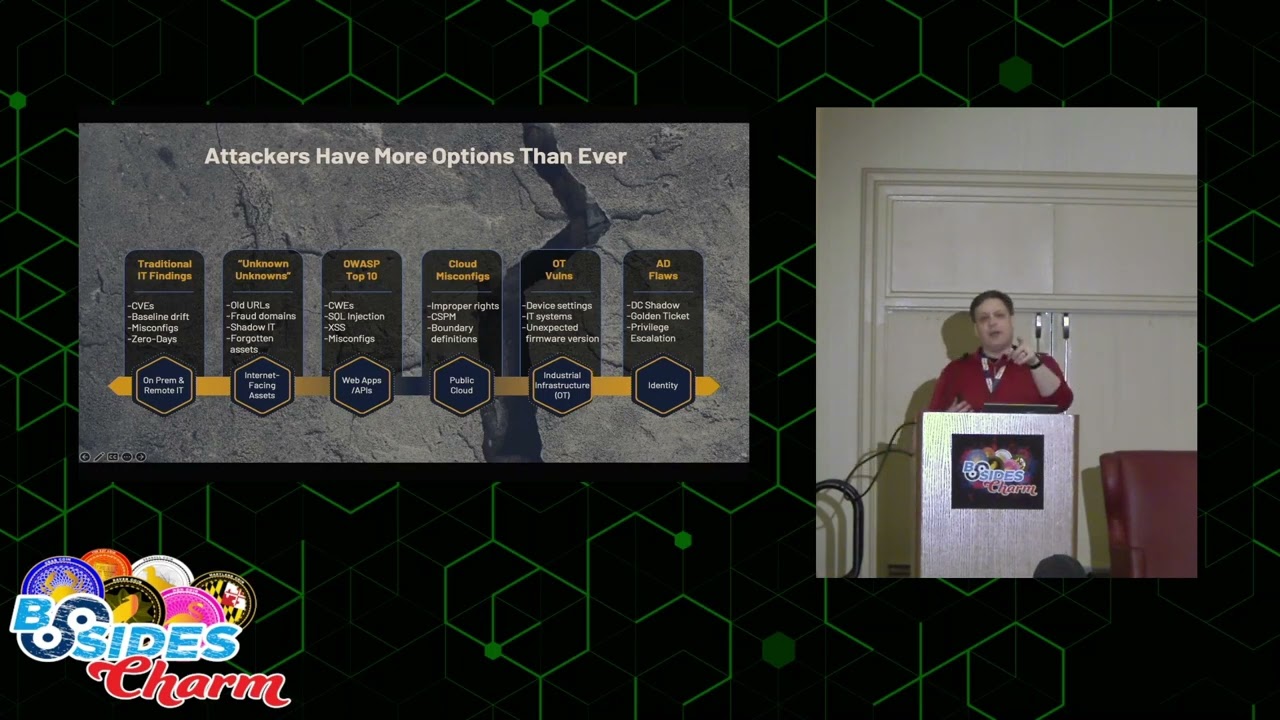
challenge is that where we've tried to protect ourselves in the past and because we're not good at this problem has left us pretty wide open the the people of course who don't have any challenge with deciding where to start first are the attackers right as Technologies expanded as we've moved into more and more uh types of Technology Cloud resources virtualization platforms web applications we're seeing more OT environments getting connected in of course credentials have really become the core of every every attack chain we see these days um we give attackers a lot of options and frankly they'll take them right they're not picky uh if you're doing a really good job patching but your web
applications are super weak I'll launch SQL injection tax I'm not I'm not picky I don't care so we give the attackers lots of options and they'll pivot to whatever matters but think about what we've done as an industry what we've done as Defenders when we build Security Programs for all this technology we tend to look at the technology level and we say well you know all right I want to solve the web application problem so I'm going to hire some pen testers who are really good at web apps I'm going to arm them with some really good pen testing tools I'll give them burp suite and you know let them go and tell them here's our web apps here's the the
space go secure it and we build ourselves an appsec team and we solve that problem and then we say okay well we need a patch so we build a threatened vulnerability management team same thing like Windows and Linux experts and we teach them to do that we give them the tools and we build that team and we do that for all these technology types and then we find ourselves in an industry today where every seal executive I know complains about how everything's siled we've siled our tools we've siled our people we don't talk to each other we don't understand each other we've we're fragmented and and it's true when I work with large organizations today you know I can go to the cloud
architects and talk to them about how they're securing the cloud platforms but if I ask the question great but if one of these things is compromised is there any chance that this can lead to back-end databases that's not my problem I'm not the database admin I'm the cloud guy I don't care so we have a disconnect here right we trying to do the right thing we created the silos that we complain about today but the attackers don't care about any of that and this is where the disconnect happens if we can start to look at our environments the threat landscape all the buzzwords we're going to use about these things in a more horizontal kind of way in a
more in a way where it all relates then we can start to give ourselves a place where we can make slightly better decisions about where we should start that's the goal of this right because if we think about defense in-depth strategies they all kind of come down to this I pick your framework of choice we've been doing this for a long time some of them have five steps some have three four whatever I like to boil it down to three these are mine you have some amount of preventative control of some amount of reactive things and of course you have a response recovery program when it all goes bad now my definition for the first two
though really comes down to the type of data that you're dealing with and this is important for the tool sets as well because in the reactive World we're looking at some kind of event taking place and responding to it trying to stop the malicious behavior or the bad packet or whatever the attack is the thing that we don't want in the environment right so there's something happening and then in the preventative side really prevention is about understanding the state of the environment where are all the holes in the walls where are the places we've left doors open and windows unlocked right I like to think of this in some regards as you know um preventative controls is locking down
your house before you leave it right your reactive controls are coming home and your neighbor steps out and says hey by the way somebody came by with a van cleaned out your house two hours ago but I got their license plate number for you well great I mean I guess I can go track this down and hopefully stop that from happening again but it's all after the fact right the event's already taken place I can Shore up my house but it's too late uh and for a long time in the industry we focused in the middle right we build walls we buy tools um we focus on this idea that hey if we can just put enough defenses in place
the attackers can't get in or we'll slow them down enough that will detect them and then the response can kick in and will stop them from doing real damage but look we've seen the landscape scale in a way that it really hasn't in the last you know 20 or so years Cloud Technologies and the and the ease of availability of all that has changed the game right we could spin up tens of thousands of assets if I want to launch an attack against somebody I can break down walls pretty easily if I want to and with that scalability we have to kind of shift our focus on how we address that because the more of those
attacks that we can stop up front we can find the ways to close the doors and lock the windows early the fewer attacks are going to be successful and actually reach those walls and that's where we can start to make them more effective if you finance folks out there we'll get a better Roi for our investment in our reactive Technologies all right but they'll be more effective there's fewer false positives they'll actually stop the things and make it through and then ideally even if something makes it through there's only so many that make it through to your response program and you're not just in constant firefighting mode this model we're seeing everything kind of shift this way nist is continues to
update the cyber security framework to use this or emphasizing more preventative strategies we're seeing uh regulatory issues in other countries hasn't quite made it here yet but India Thailand have both passed recently uh legislation for companies that manage uh microtransactions like phone based applications for doing microtransactions right they've passed law that says if you're going to be a company that handles people's finances in that way you have to have a program that looks like this with a focus on preventative now from a tooling standpoint obviously we have a lot of things that can help us we know this stuff this shouldn't become a surprise but it should draw a little bit of a line about what we're talking about
as well and what tools we have um firewalls by the way for those who are wondering I really personally feel it belongs in the reactive category some people like to argue that point I put it in the middle just to avoid that so if you're one of those people thinks it's a preventative thing great it's in the middle I've compromised yeah see I'm kind of yeah I'm a reactive guy when it comes to firewalls that's just my thing but you appreciate thank you um but the thing about this is like the tools again get siled right and so as I've mentioned I want to talk about attack path analysis today because attack path analysis is a really useful tool when done right
and typically when we've used it in the last several years we kind of do it down here right we see attack path analysis mostly used in um post-mortem events and forensic analysis for a data breach we we kind of look at it from the standpoint of let's recreate what happened through all the events and the logs and the trace files and all that good fun stuff uh and let's map out how the breach happened so that we can make sure it doesn't happen again that's a pretty good risk decision making tool I like that except the problem is the breach has already happened right the damage is done so yes we don't want to have it haven't have it happen a
second time but ideally we don't want it to happen in the first place so what I I start to propose or want people to start thinking about and this is just one example of many but the one I'm going to talk about today is what if you extend the tool to start incorporating State data what if you Leverage The tactics the techniques of attack path analysis when you're looking at State not the what's already happened because if you can do that we start to move more away from a forensic view of this world and it starts to lean more into that probability and likelihood kind of world more of a risk management kind of world
which is really where we should live as I like to remind folks and I don't think anyone here is going to shake their head at this I'll probably just set that up um you know security functions today in an organization we're not an I.T function we're a risk management function for organizations we have to be strong technologists don't get me wrong because that's where the data lives that's where the assets live but we are a risk management we are there to identify the problems and help protect that organization before it goes bad that's more aligned to finance and legal and even HR I've given another talk about how to talk with those folks but that's a
different story anyway but if we can extend out here to state right I can start to use this kind of Tooling in a way that lets me identify where risk might live in my organization make better decisions about where I should start where I should focus where we want to look instead of trying to scramble at it right so for those of you not not familiar it's been around a fairly long time this is an example from Microsoft on Exchange attack it's a visualization right if you're not if you haven't seen it I'd be surprised if anyone here hasn't but if you haven't it's a visualization of how an attacker moves through the organization what vulnerabilities were
exploited misconfigurations all that good fun stuff it's a nice way to lay out the path they took to get to the crown jewels whatever the thing might be so but this is all again post this is all based on events that have happened already let's talk about what it would look like from a state perspective I'll walk you through a really simple example um and hap and I'd like to have some uh some interaction here in a few minutes just don't get snarky I know how this is going to go all right so let's talk about a potential hypothetical attack path right if we're doing our work to assess the state we kind of know what the state of our
environment looks like we know that we probably have some users out there who are still working from home we've given them a laptop and great they're doing work for us out there there's two things we know about users in every organization worldwide they're not terribly Vigilant when it comes to security matters and they're really really good at hitting the snooze button on our patch management tools and the problem with that is the attackers know that too now look the last three years I'm not going to Regale you with stats we know that we've seen a massive increase in phishing attacks and other targeted attacks at home users their networks aren't as well protected they're easy
targets or soft targets we know that's been happening right so look if I'm an attacker I'm going to go after those things they're easy if I'm a Defender though I may have done my due diligence maybe I've scanned it or maybe I have an agent on it or something I've done some amount of vulnerability analysis and hey look at that in fact good old Joe did hit the snooze button and it is missing some patches one of which would solve a cve that's known for being exploited by ransomware command and control and a few other nasty things that lets an attacker take over the Box all right so that's one piece of data I've done some security work but we
should go patch that probably but whatever but let's walk through the attack path if I'm the attacker and I get on that box and I own it I also own Joe and everything he accesses right so what does Joe know like well I'm not going to sit there and just scan for that single vulnerability and get bored as an attacker when I don't find it anywhere else remember I'll pivot I don't care so I'm gonna go and say hey what kind of access do I have oh Joe's part of a user group that gives him access into a corporate environment and takes him to the server inside the corporate environment that happens to house an incredibly critical
business server like it's the thing that runs your whole company probably has been there 12 years no one remembers how the code is written or whatnot and but every employee uses it all your customers use it it's it's the thing that makes it all work right Joe's got to access that to get his job done but I'm the attacker I'm there now a 12 year old application sweet because 12 years ago I know developers are really good at secure coding practices and uh they would never leave hard-coded credentials in the code in the clear to access back-end databases that would never happen um I hope that coughing is because like we know it's a joke right I'm covering for
you try it so great there's a service account sitting there in the clear cool now I have an admin thing let's take that let's do some privilege escalation because that's really the goal if I can do it you become domain domain admin now I win right now look this is a very simple attack path couple different points of data I've done some active directory analysis I've done some endpoint analysis I've looked a little bit of configuration or code analysis but again if we're trying to make decisions about mitigating risk the question becomes where do you start so that's the question to ask you simple let's just stay simple because I know some of you are going to
come with really clever answers this but let's stay simple if you were going to try to solve this prevent it from happening prevent this attack path from taking place what's the first thing you do please
[Music] I love that so either train Joe to do better or make sure the technology doesn't give him the opportunity to subvert it right or both I'm good with both of those um I'm a big fan of training I'm a big fan of that I'll just say really quick um I mean I'd come for more of the people's side of security these days so I'm a big fan of training uh so yes absolutely train Joe we should do that however um have you met humans before [Music] like so you enter yeah so we know that not all of them even after training stop clicking on the links that they shouldn't uh and yes not subverting the
the stuff is a really good plan but we also know that patching tools have delays when those things check in or don't check in there's some there's stuff and if it's not Joe I'll get Jane or you know Jeff or Mary I'll get I'll find one of them and that's an easy exploit too so we should do those things but I can get around that yeah at least Pro yeah I'm a big fan of least privilege foreign sure but he he's only a member of a remote user group that is the least privilege he can have [Music] well that's the application they have to use to work if they don't have that work why did I hire Joe to do work
if I can access that app if I can't if I can access it as an attacker I can I can I can attack it and Joe's got to access that thing to work so we have to give him some amount of access if I give him none that would protect the server but then why do I have an employee I understand but he's got to have some amount right which means the attacker once compromised will have some amount what's that yeah in this example you'll consider that lease because that's we didn't make him an admin or anything they would just give them the basic rights to get there [Music] in what would Asset Management do for us
here
we know it's old yeah we already know that part is old so um I'll give you one on that one we might say like maybe we should update that application right something a little newer that is not using Code that has credentials stored in the clear uh I I have a privileged access management background as well I'm a big fan of not letting credentials like that be out in the clear but remember this is a 12 year old application that runs the whole business do we have the devs we still remember how to do it do we have a finance officer that's willing to let us take us down for a period of time or spend the
money to build a new one the business may become an obstacle here and not let us do it because the impact of either interrupting the work or taking it down to patch they may not allow it because of Revenue issues which is real right one more [Music] right
I and I totally agree but like I said in this business example you might have the challenges you can't right you do and I'm about to I'm about to get there with you you're you're half step ahead of me but you get there so you all see what we're talking about here right there's a lot of ways to address this we we could talk about do we put a WAFF in front of that thing and maybe filter traffic except that we still have access control things we have to deal with that do we you know um do we try to address the domain admin elevation thing is there is a reason that that service account is even an
admin account at all we don't know what else is attached to we might not we might break other things there's a lot of places where we could inject security controls here but even with very smart people in the room you've seen what's happened here we still don't know where to start right well I'm going to carry on if you don't mind thank you so that's part of the problem right you might be able to figure this out with a lot of work for your particular environment but it's not obvious and we're going to spend a lot of time chasing this to try to figure out what the right thing to do is let me add some more context more data
if we can relate more information it might become a little clearer right so let's say I have done some configuration work and I also know that that server in the middle that's the obvious kind of problem or seeming to be obvious also has a VPN service running on it that is misconfigured to allow access without MFA bad really bad uh and especially since I got those store credentials that let me be admin that no one's paying attention to because it's a non-human account brilliant I could go anywhere I want let's go down the tunnel what's down the tunnel some sort of critical area of your network could be your if you're a power company could be your OT network
if you're Finance of your PCI network whatever's critical to you right so you now I'm down here and I've got access to this whole thing and of course let's just use for example it is a power company uh any of you have worked in that space you know aside from all that specialty equipment there are ancient windows and Linux boxes that the engineers and controllers use in in those places and they almost never get patched because we air gap except well we have a VPN there because those employees that work in that Network have to get back to that early critical application to do their work so now I have two attack pads that come out
of that thing and it could be 20 it could be 200 it could be a lot more than that and while it's not necessarily obvious at least what this starts to do is it starts to point a finger at maybe this is the place we should focus because if I can solve the problem here then I cut off the potential for access to the domain admin elevation to that OT Network to a lot of other potential damage and harm that could be done now we're not answering the question of how so to your point build a case you might have to like do I need more budget what's the right tooling do we need more
people do we need to write a new code whatever whatever the answer is for your organization this is the next step but you can't have that conversation with your team to figure out the plan until you know where you want to start right well that's true too arguably for let's just say for fun it's super critical and we should fix it right so this is a simple example but you get what we're talking about here right if I can build an understanding of the state of the environment if I can relate these things together I can start to look at this kind of like likelihood of how risk flows through my environment and you can see how if you did this for
the entire organization you're going to have a massive map but what will come out of it are these choke points and one thing I will tell you is this you talk to a CFO to try to get budget for that fixing the problem I wouldn't necessarily show them something like this but I have done exercises where I've done this and Stripped Away the text and just told them like look I have mapped out how risk flows through this organization and where it is most likely to impact us financially CFOs understand that statement and they look at it and they go well how come there's all these lines coming out of this one little Dot I'm glad you asked that
it's the application we've been talking about that's the thing we're going to have to resolve because that's the thing that leads to all this risk that visualization can be really powerful for people who don't really understand what's going on it doesn't work for everyone but it can be but for us if I can get to this point in a minute rather than weeks of analysis work with spreadsheets and everything else I'm way ahead of the game and we still might decide not to start here this might be too much of a challenge to overcome I've been in those kinds of organizations where like you just can't touch it okay let's start talking about patchina what's the next thing we can do right
but this gives us a place to say this is where I can start this is a really important way we change the way we use the tool we already have but base it on that state data so that we can understand risk better in the environment get to that point of answering where to start make sense any questions any thoughts before I move to the communication part which I still have time for it's great [Music] perfect okay all right in the back
sure so which answer do I give you my marketing team would tell you it's tenable um you know I look realistically what we're talking about if we go further back like it's about doing assessment work right so we need to be able to understand that security state that is having some kind of vulnerability scanning that's about having web application scanning some tasks or you know a SAS is both ideally you want to have you know for your Cloud environments you should have some ways to look at you do your posture management assessment understand your configurations make sure that things are the way they are um there is a tooling requirement for all of that assessment work right once
you have that I mean look we've been aggregating that stuff for years manually right I mean every single one of us uses the most widely used security tool on the planet right anyone thank you Microsoft Excel is most widely used security tool on the planet period um kind of worked for a long time there are tools and ways to do it and today I'm not going to be I'm not going to stand up here and try to tell you some of them in some regards I don't want to go down that road but there's definitely ways to automate that process and there's a lot of different ways to do it I mean I've seen folks do this manually I've worked
with organizations that have built risk systems out to try to aggregate this and build the relationship mapping some folks do it on miter uh that's a lot of post attack and technique work which doesn't always align with business so well so there's some some rub there there's definitely ways to do it it's not a hopeless cause and I and have definitely seen it in practice so it can be done but it really needs a focus on are we doing enough assessment to have that state data so that it can build those relationships good all right so look let's talk about communication if we're making these good decisions about how to mitigate risk or where to
start we also have to be able to talk to people about risk and we need to be able to explain to them in ways that they understand so that we can all get on the same page we can get aligned oftentimes though we use a lot of words in security that do not mean the same thing to the people we talk to all right you think about words like asset and risk and all of this we use them kind of differently and that becomes a problem and whether we like it or not for all of the rhetoric of the last 20 years of infosec what do organs or organizations say Securities at the heart of everything we
do security is the thread that's woven through the organization every one of us is a security person we're all in it together right we are as security folks really at the center of communication for organizations because think about it legal is going to come to us and ask us about compliance stuff and legal like rbgdpr compliant I gotta talk legally with the general counsel and finance is going to come to us and say what's the ROI and all this stuff that you've been buying and should we give you more budget and they're going to want to hear it and the business wants to understand hey we didn't have a data breach this year that means we don't need you guys
anymore right like we talk to all these different groups and they have different requests from us but we don't always talk back to them in a way that's that they understand so one of the things we have to do is focus on not just the words we use but understanding that they mean different things to different people Let's do an exercise simply put when you see this word [Music] what's the first thing you think of what's the first object you think of a lizard that's pretty good I like that that's pretty good anyone else a screen thank you that's the obvious one right we live on these things we sit here all day like I think of a screen
um and I think anyone in technology other than the weirdos in the back well I'm going to talk about the word in the back in a second hold on but yeah screens duh except if I go and talk to someone in healthcare and I tell them that what about a monitor they're going to give me something like a heart monitor or an oxygen monitor or an IV pump monitor or something like that because that's where they live and if you're like the person in the back or a very dear friend of mine I I'm gonna lead to this you just jumped right ahead of me here I I have a very dear friend who collects
exotic pets and absolutely do collect lizards and if you say monitor they will tell you all about how Komodo dragons are part of the monitor lizard family in extensive detail right and you know if you're somebody like me who struggled in high school a little bit got bullied a lot and you know made friends with teachers so that I could get out of class A lot um when I think of monitor I usually end up with this guy um the irony is of when this episode came out that was what my home on her kind of looked like so it was really the beard the whole thing it was not good um make the point
one word four meetings depending on the audience you're talking to and as security folks we need to take the responsibility to understand this and pivot the conversation in a way that makes sense to the folks we're talking to that may mean education that might mean that we don't just assume when I go to the finance officer and I say hey this system is putting us at risk that he knows what I'm talking about I need to be able to go that a finance officer and say this this server this object puts us at risk of a financial loss of 10 million dollars per day I need to take on that responsibility we need to take on that responsibility
that's the language they understand so remember the words we use don't always mean the same thing we need to clear that up sure quick that is true I was focusing on nouns let's talk about normalization and context then right because part of what we're trying to do here with language is normalize what we say make sure that the context is has a a good understanding and to your point in the back about the aggregation of the data this is one of the places where we have to focus if we want to do that because when we talk about security risk all the different types of [Music] vulnerabilities or however you want to think of that missing patch
misconfiguration code flaw whatever it's all it's all a weakness all of it we already in the industry we have a hard time talking about those things in context with each other right we have different scoring systems we have different ways of talking about it and even this stuff we get kind of confused about and what it ends up happening is we have to start asking ourselves questions like well geez jeez you know I've got this thing that's like a you know what is it what I put up here 7.6 there we go CBS S7 but I also have a web flaw that's a high and I'm failing on this other thing which one's worse well there's no context really there and
the only way we do that is to have the analyst in the middle who's been there for 10 years who knows what all those things are who has a dozen spreadsheets sitting in front of them and is going to do that work for 20 or 30 hours ago well actually I know that laptop that has the 7.6 it's the CEO's laptop and it's bad all right this is something that we have to start to work against too um again there are techniques for doing this uh but this is what we need to start doing is figuring out ways where we can normalize this information normalize the data set so that when I talk about this
stuff to people we at least come from a a unified platform right I can talk about a high risk across the board or I talk about an 8.3 risk across the board like whatever system you want to use I don't really care but find the one that works and try to normalize that information because then it gives us context for us to do the rest of the work now some of that work is also in the way we how we not just look at the findings and understand risk in context but it's also the way we report it to everyone else and this is where I find probably the biggest challenge for security folks is here
because we have all these tools the tools are really good at generating data those data points go into spreadsheets and those spreadsheets tally up to really big numbers and we love those big numbers we're very proud of our big numbers and we love to tell people all the time oh yeah I stopped 93 000 probe attempts on the perimeter today our Ops Team deployed 12 and a half thousand patches last month yep I found 75 000 vulnerabilities fixed well it sounds great to us because we live in that world but that same first job when I was a CSO I mentioned um I learned a lot in that jobs why I talk about it a lot but
I had this problem we came on board they have really no security team um well no security program they had five people but they weren't organized and I was told by the CEO just just go fix it just go make it work all right um try to do some code review the CTO of the company just told me Point Blank like you will never your team will never touch any of my Dev systems go away all right well I have to go work on that but I need to do something today so we went low-hanging fruit like we went for a patching exercise it's the obvious you know kind of thing told the team just go patch whatever you
need to patch reboot whatever you need to reboot I will deal with Fallout that's my job now let's just get it done so we did a 30-day Sprint do as much as we could possibly do did an assessment did the prioritization we did our work right we started the month with about 300 000 open vulnerabilities just in our like server data centers work workstations just typical Windows Linux kind of stuff team in that 30-day period we we fixed and remediated about a hundred thousand a little over a hundred thousand of them mostly in the high in critical ranges so we're pretty stoked like that's a lot of work to get done even if you're only deploying some patches 100
000 bombs out of the environment 30 days it's no joke and I wanted to make sure my team got credit for it so I went to the board that next month I had my PowerPoint presentations all ready to go I had my graphs and charts and colors and all the good stuff and I was like hey check it out 300 000 at the top killed a hundred thousand of them off 34 reduction in Risk High critical stuff awesome my general counsel looked across the table for me and said so what you only did one third of your job
and yeah you had 300 000 problems there's still 200 000 problems left you suck at your job we need a new CSO they didn't fire me for what it's worth I got to stick around but you see my point right volume based metrics while we love our data they're really good for workload right if I'm trying to understand how much work needs to be done that's fine it is not the right thing when we're talking about risk to a business to finance folks to the board to other even peers in the organization who are at the board level this is not their world we have to find the ways to make this work now that could mean a lot of
different things percentages trends letter grades whatever I'm going to show you an example here in a moment it doesn't matter what it is but find something that appeals it's simple it's easy it's intuitive so that someone who doesn't live in our world can look at it and go oh the lines moving in the right direction cool that's what you want we often laugh about stoplight Graphics right stoplight colors we all I see a lot of people nodding like we all make fun already because because c-suite executives are stupid right look these people are making hundreds of decisions on a given day all they really want to know is are we okay or are we not
red yellow Green's a pretty simple way an intuitive way to show that we laugh it's a good way to show that information are we good green cool what else do you need nothing let's move on to the next thing are we bad why what do we need to do to fix it simple [Music] we need to move that direction when we talk to other folks outside of our kind of outside of our sphere so let me show you an example what it might look like I'm going to qualify this very heavily I work for a company we do some of this stuff it's the tools I have access to all right so little fair warning I
understand how that looks but I'll emphasize again you can do this a million different ways just once you share the example are we good is everyone all right with that mostly all right I'm gonna get heckled later for this I know all right so look letter grade it's not the end of the world right I don't have to understand 75 000 vulnerabilities remediated or need to be remediated to know that c is pretty average so I'm going to be asking the security team what do we need to do to get that to a b I don't know what it takes that's your job that's why we that's why I hired you and the security team go solve that
right color coding is great too because I can look at that very simply and go wow there's two in the bottom or red like United Federation of planets like what are they not doing any work or what's going on over there yeah like let's go talk to them and figure out why are they not patching or what's like now I have Focus I can literally see where I need to focus right we're not talking volume we're not even necessarily talking about what but at the business level I can I can kind of intuitively understand what's going on here and as you talk to the organizations about this is how risk maps in our organization this is who's
contributing the most potential Financial loss to the organization this starts to translate a lot into the business World it makes it easier for them to wrap their brains around how this technology stuff can put the organization at risk and where it's happening right use LINE charts use whatever you need to do right but you kind of see what I'm saying here I hope you see what I'm saying here this kind of simplistic thing lets them be very quick and it's intuitive I don't have to educate them a lot I don't have to explain what a vulnerability is or why one cve is worse than another uh we don't talk about that that's not their world this is their
world and the more we can do this the better please
it's a great it's a good question we felt that the Klingons in their very very strict sort of structured society would have enforced that they wouldn't give the option to snooze they would have turned off the patch management stuff and forced that issue where I think the Federation would have trusted a little bit more that everyone would do the right thing at the right time the right way so that leaves a little bit of a little bit of wiggle room right right I mean there's there is different incentive for end users to to patch right just saying so yeah I know but I'm gonna hold of that I think that's true I like the beheading I'm gonna I'm gonna use
that one next time by the way that's really good because patch or beheading I bet you it only takes one or two and then everyone Patches from that point forward forever so I think maybe we need to do that I like this we'll have to we'll have to start a business um oh my God it's gonna be like the best consulting firm ever like you let us murder two employees I guarantee you 100 compliance in all your patching I love that thank you all right good everybody kind of understand what I'm talking about here right we are risk management folks that's our function so we need to start speaking in a language that other risk management
folks understand simplify it normalize the information help them understand where it's going wrong and help them understand where it's going right I'm going to tell you one quick story for the takeaways about this I worked with a company several years ago big finance company for automaker they are essentially the company that loans out when you buy a car they have about a hundred and 115 of these Banks across the world one for every country they do business in and they all have their own security team they're an I.T team they all report up to the global office now in Plano I'll let you figure out who it is it's not hard um but I got brought in because this
they actually had a program like this they had nice color coding they had all the stuff there they had ways to manage the slas and all that good fun stuff and they were like look we we have some countries that we just cannot get on board and we need help and this is when I got brought in to help them figure it out and we're going down the list I was like yeah help me show me what's going on they said well look look at Germany here our SLA for patching is 30 days they're on average compliant rate is 68 days they're terrible we can't get them to patch for anything for nothing okay what else they're all France France
is just as bad 66 days because we ask them we tell them to patch they never patch they're the worst okay well look this is good we found the anomalies in the pattern right this is what we're good at we find we find anomalies in the pattern bad you guys are the worst outliers terrible I asked the deputy CSO in the CSO this company I said well tell me what's going on in Argentina and he looked at me like I was crazy and they said what are you talking about Argentina Argentina is great their SLA compliance is nine days we never have to worry about them they kill it they patch it they do it every single time
I said right why they never asked a question they never once asked them that's a good outlier what are those guys doing differently than everyone else is doing to do a nine-day SLA on a 30-day requirement so we called them up I got him on the phone like what are you guys doing they're like oh you need to talk to this guy on our team it's a little while ago mind you and he's like got him on the line he's like oh I'm a I'm a Powershell I'm a Powershell guy I just got bored wrote a couple Powershell scripts I brought one that grabs the patch and deploys into my test lab and let that burn for 24 hours
and then I had to wrote another script to grab the patch and deploy it to my pilot Group which is like 10 of us that I trust that work in the business and I let that burn for 24 hours and then uh and then let it sit for about a week and if none of the applications break after that I have a third script and I just push it out to everything and we're done 24 hours 24 hours seven days there's your nine-day SLA right so I actually thought can could we have a copy of your scripts yeah we don't care right hand it at the scripts that was it so we went and talked to these folks
right go look at the good outlier right see what they're doing right because it might be the opportunity to find a tool or a process or a workflow or something that's doing a little bit better that you can apply to the rest of the organization and help it do that and you're only going to get that when you start doing this kind of analysis at a much broader risk level you don't see that as common when you're looking at volume of patches being deployed right epilogue for that story by the way uh we did distribute that out minor adjustments for every region for all their variables um they went from I think they was originally it was like
36 countries out of compliance to one in 60 days what's that no actually it's pretty good in that company uh uh it works right risk factors let's look at that kind of stuff so look for outliers use this kind of analysis for risk outliers but don't forget about the good ones those are your opportunity to do better and to celebrate the people who are doing it right make sense okay so coming to the end of the talk thank you for sticking around um I want to reiterate again a couple of things right look everything moves super fast these days it's ridiculous we have a lot of power in our disposal and Technology but so do the attackers
and the more that we can start to move away from the reactive responses the way we do things and the more we get away from just banking on our incident response teams the more that we look forward and ahead and understand our state the better prepared we are to make decisions about where we should focus our resources where should we focus our remediation efforts where should we focus our money and our teams where do we need training all of those questions start to surface when you start to look at that we're getting out of that place of saying how many patches do I need to deploy I should be asking questions like is patching even the right answer right
now that's where we need to kind of be we need to get out of this I.T mindset of operational work and move into more of a data analysis and risk analysis mode because that's what we really honestly do best and once we're in that world just remember the communication part is key I cannot stress this enough every single organization all of them that I have consulted for or that I have run the security program the problem was never the process yeah problem is held in the process the problem was rarely the tools it was almost always a Communications problem Ops people didn't feel valued they felt the security team was just stealing all the credit for their Works they decided
not to patch anything anymore because we didn't communicate to the board that it was the Ops Team doing the work right that's not them being stubborn that was our failure for not communicating I know that it's not fun and sexy and it's not pen testing and it's not all the cool stuff we get to do but I'm telling you understanding how to communicate better making it relevant to your audiences stepping outside of our kind of comfort zone of Technology into this risk space is where we win this is the place where people start to understand what we do the value of what we do and more importantly start buying in to what we do and whether it's a large organization or
small getting people to buy into what you're doing that's where you're going to succeed and that's what we need to start moving to all right thank you very much for your time I'll happily we've got a couple minutes left here any questions any thoughts I'm happy to to entertain them um what do you guys got nothing great thank you so much
[Applause] say again [Music] oh man I I have I have friends who are Smiths I I've got this covered like if we're in on this business for beheading people I'm I think I might I might be on for this so it's funny hey how you doing





