The Triad Nexus Pig Butchering & Money Laundering Network: A Deep Dive - Kasey Best and Zach Edwards
Show transcript [en]
Thanks so much everybody for coming. Uh we're getting started here. So today we're going to be giving a presentation called a deep dive into the triad nexus pig butchering and money laundering network. And this is basically a threat emanating from China. A very complex threat which is both corporate threat with also some unknown threat actors on this network. Um, and it's quite complicated how they're getting their infrastructure. So, we're going to explain exactly what they're doing, how they're keeping this infrastructure online, and I'll give you a little teaser. Uh, they're basically stealing uh Amazon accounts and and other sort of cloud hosting accounts and uh some of the ramifications from this type of infrastructure being uh online
available uh 24/7. Good morning everyone. My name is Casey Best. I'm director of threat intelligence here at Silent Push. Uh, as you can see from the wonderful bullet points that we're going to skip past because we don't have enough time. I've been in cyber security for a hot minute and uh, Zach is one of the many phenomenal analysts on my chair. And I'm Zach Edwards. I'm a senior thread analyst. I have a lot of experience in online ad systems and various financially motivated thread actors. So, we're going to jump in real quick. We have a lot to cover. I'm going to go over what infrastructure laundering is. Um, some details about the polyfill.io supply chain attack. some folks may be
familiar with uh a little bit about the corporate entity that owns some of this called ACB group um some details about the pig button websites that they've been running um and details on the CNAME chains some infrastructure details and then a whole bunch about money laundering and then we're going to end with some details about retail fishing scam and some other sort of summary details. So briefly what is infrastructure laundering and this is an important concept. So when we talk about infrastructure laundering, everyone here is probably familiar with bulletproof hosts. So the concept of going to a host that doesn't respond to abuse complaints and they just let you man keep hosting that infrastructure. Infrastructure is a
little different. So, these thread actors are basically using a specific Chinese hosting company and for whatever reason, this Chinese hosting company is um having other criminals spin up illicit accounts on services like Amazon. And the time between when they illicitly get that account and when Amazon takes it down, they're mapping those IP addresses into their infrastructure. So they basically have a rapid effort to illicitly acquire cloud hosting accounts and then they also acquire cloud hosting accounts through uh lowquality Asian IP services. And so this is sort of a new form of obusation where the rapid acquisition of cloud accounts mapping into this uh creates some really interesting opportunities to hide their infrastructure and keep it
online and fast for western audiences. So we're going to get into a bunch of details about that here more technical stuff and what is funnel CDN and try Nexus. So funnel is basically a content delivery network like many other content delivery networks but the this is a cont delivery network that's getting online with these elicit accounts and basically uh stolen cloud accounts mapped into their infrastructure. And so we've dubbed this network Triad Nexus um because it is deeply connected to Chinese criminal schemes. And what we're basically talking about today is really the tip of the iceberg. We are going to continue this research, have some more details out later this year. Um, this is the new way that a lot of Chinese
criminal organizations are getting their infrastructure online and the CNAME chain shenanigans that we're going to talk about is getting worse and worse and more complicated. So we're basically going to give you a primer on what's happening, but what we explain here is scaling up very fast and we've been tracking this for over 2 and a half years. So we have a lot of details at Solen Push about this. Um but the whole investigation, this whole effort wouldn't have happened without other external researchers putting out information about the polyfill.io supply chain attack. Just briefly what that is basically a service polyfill.io IO was providing a developer service that was integrated into thousands of major websites from NASA to the Hulu uh
homepage to everywhere in between. Lots of people integrated this domain and this JavaScript snippet and then all of a sudden a Chinese company bought this domain and everyone was sort of um wondering what was going to happen and the person that had originally created a service started warning people in February of 2024 saying hey this bad I don't own this anymore a Chinese company has bought this and I have no clue what's going to happen. Fast forward a few months and Sanssek and Google basically said, "Wow, there's a supply chain attack going on. This service is now redirecting some mobile users to lowquality casino websites." And so a lot of security researchers said, "Ah, lowquality casino websites, that's
garbage. That's not a problem. That's not a threat." So some folks just ignored this. Um, this same organization also ended up registering quite a few other domains and were doing similar mobile redirections. Fortunately, this polyfill attack was ended. Name sheet basically took over the domain and made it so that uh nothing could resolve when it was connecting to it. Briefly, the ACCB group and we have a little typo there in the header. Um but ACB group is essentially a Chinese consortium that runs online gambling websites and also happens to have this content delivery network among portfolio. It's a very interesting organization. We're not going to get into all the details, but we are talking about the money
laundering that they support and the criminal schemes that they're hosting. So, you could maybe imagine some of these gambling networks, there are many other opportunities to research here, and I will leave that for everyone else to get into. Um, but as we got into the ACB group and some of the the entities, uh, specifically funnel CDN, we did appreciate that they were marketing this basically bragging about their infrastructure within China. So we pretty quickly realized there was some things to look in here. >> So back in 2022, uh our team initially had looked at a large cluster of fake trading apps and we gone in developed out the network saw they were impersonating the ASX,
Coinbase, a bunch of different sites in order to continue their fraud. Uh and this actually led us to different types of networks, but we didn't have the full picture of exactly what we were looking at until later on. uh at the peak of the infrastructure up here, you can see that they had thousands of act domains. And while in 2024 2025, it's a little bit more modest. They're still spinning this stuff up actively. We actually checked this morning, there's still active infrastructure hosted on Amazon. Uh it's been up for a while. And this sort of highlights the problem with infrastructure laundering. when attack or when threat actors are using these techniques, if you are still going by
old ways of detection, if you're still in that old previous mindset where you block domain or you block IP after it's been weaponized, it's not helping you get ahead of the threat and it's not actually doing anything to mitigate the threat actor. Um, so you can see this page here, this one actually went down just after we post a a public blog on it, but it was live for almost 2 years. And uh this one helped us map the different CNAME record changes across the CDN. So I won't bore you too much with too much of the technical details. We've highlighted in orange the pieces there for you to follow. So the CNAME record starts there
thevip and then in February to March it changed over to the funnel01.vip and then again it swaps over to the uh wildcard fn03.vip. And again this is the go ahead >> and briefly we are actually seeing changes here as well. So one of the more interesting things is uh this is evolving from these three to now many many other CNAMES um that the network is abusing. >> Yeah. So the network just sort of keeps getting complex as as time goes on. But what it what the snapshot here shows you is that the the client domains were all mapped at u mapped to a civic CNAME record like the FN03 right there. Then from there they would hop over to
fnvip0000.com and then they would sort of follow that entire chain until it redirects finally to the IP address point of presence which is the physical location of the server so that whoever is visiting the site has the fastest response time so that your victims are getting the best service bubble. Now this fun um diagram was a lot of fun to put together. Uh there's a lot of work in here. There's over 200,000 different unique host names that we had identified at the time being proxied through this network. More than 95% of those host names being generated via uh DGA. That's the main generation algorithm. So if it looks like somebody just rolled their hand over face over a
keyboard, that's what we're talking about. Uh but you can see the the pattern here. And I don't I don't want to point cuz I'm definitely not that tall. But you see on the left side, somebody starts over there. They get mapped one of those different C names. And then from that name, they get mapped down even further until they finally get to the point of presence IP address down there at the end. And one one thing I want to highlight here again is that when you're trying to track a thread actor, it's important to know how they manage their infrastructure because if you know how they manage their infrastructure, you can track it all. And that's what we've done here. Funnel.
Uh so this this was a snapshot from their pricing page. Uh we thought this was interesting. We always like to include this on our slide. It shows that they only appeal to very specific types of organizations because you can see down there at the bottom they have an 80% discounted rate for clients with 50 domains or more. That's that's a very specific type of customer, especially if you're trying to, you know, as a thread actor, you're trying to spin up a whole bunch of domains. You want to make sure law enforcement isn't stopping you. You've got, you know, however many people you're uh impersonating or however many brands you're impersonating, you want to make sure
that 2, three, four, five takedowns a day are bothering you. uh they're providing the prices right. Uh this fun piece as well when we're investigating funnel this shows their uh error page that they use for the CN. So if it's misconfigured uh this is the unique error page and I emphasize in foot stomp unique because you can use that for threat detection. Um and you can actually use that for a lot of different threats. If they have their unique error page that they've set up, something custom for them, you can search through that obviously with our tool, but just keep that in mind whenever you're doing hunts. Anything unique that the thread actor is doing is
something that you can use to follow them back to the rest of their infrastructure. And here we had identified over again this is a snapshot time, but there's over 500 funnel IPs that have been active in that week. And while you notice that there a decent amount of those are on the different Asian ASN about 40% of them at the time were actually hosted on Microsoft and Amazon. So that's that infrastructure laundering piece that we're talking about. They're not just hosting on Chinese ASN where in the west we might say all right well that's probably suspicious. I'm not going to go there. uh they're popping out of Microsoft and Amazon so they can hide within Amazon's traffic so that
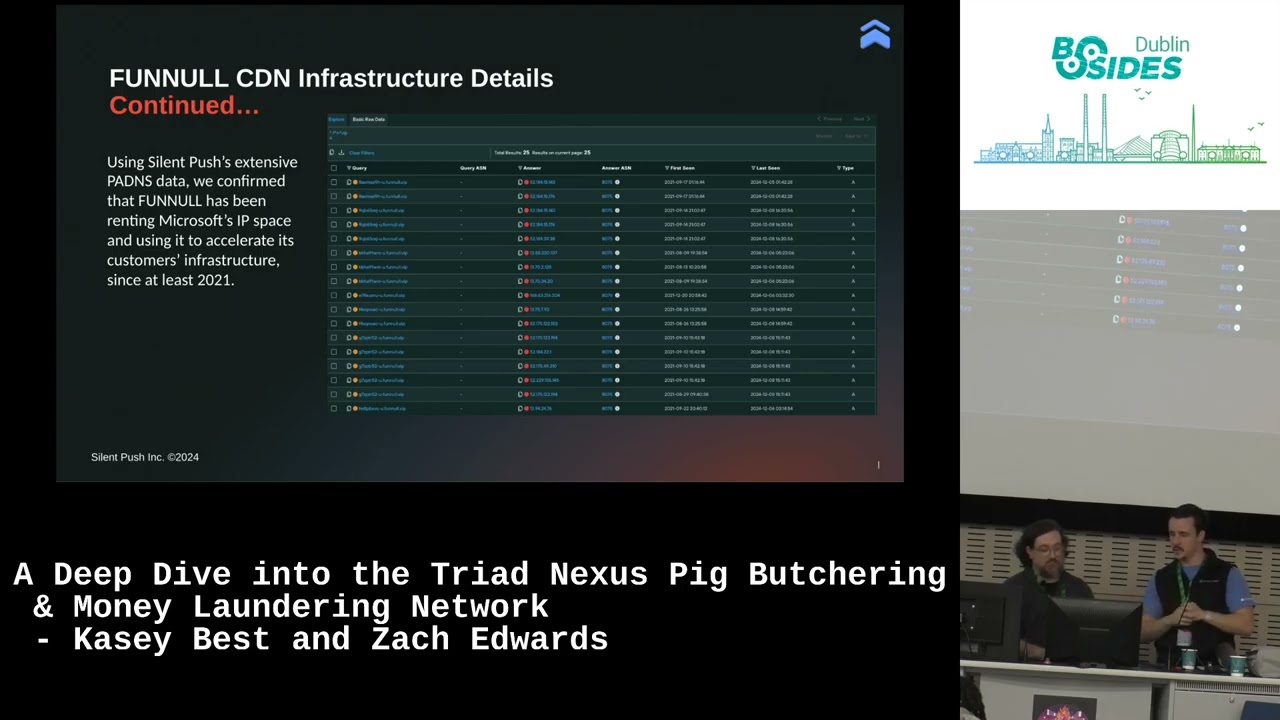
they can hide within that detection obviously what they're actually doing and make it a lot harder for us on the threat hunting side on blue side to protect our customers and enterprises. So this wow you can actually see really well. I love this screen. Um this just shows uh that funnel had been renting Microsoft's IP IP space here. Uh you can see through our PDN data and this goes back I believe to 20 >> 2021. So you can see the the length of time this infrastructure is staying up. And I will give Microsoft credit. They've been doing a really great job of trying to knock this infrastructure down and take it down as fast as it comes up.
But again, that's that, you know, punching after they're already standing up. If there's 16 guys in the room, you're not you're punch one at a time. It doesn't doesn't really work. Um, and here you can see a nice little world map of where the uh IPs had been hosted. So, 20 in the US at the time, some in Hong Kong, some in Japan, some Singapore. And the thought there as we were looking at this network is they're hosting in areas that if law enforcement wanted to work together, they don't traditionally work together too well. or if they do, right, there's a there's a little bit of a time zone difference, so it makes everything more difficult.
Now, we're going to be stepping into the money laundering side of this of this infrastructure. And so, um, as we were looking through what was actually hosted on Funnel, we started to appreciate there were tens of thousands of online gambling websites. And this is exactly the type of website that they were redirecting people to via that polyfill supply chain attack. And I'm sure a lot of folks here have stumbled across one of these lowquality gambling websites and you've just said online gambling website. I don't have any interest in this. But really we want to remind people you should be pausing on this because these are often times used for money laundering. And if you dig into
just a little beyond the the initial page, you can find something wild. And so our team found tens of thousands of gambling websites uh with dozens of unique brands. And as we started looking, they had a lot of commonalities. They have, you can see here in the bottom left, this Tether lottery that they were doing. And so across this network, we started to see, well, they're different brands, slightly different looking sites, but for some reason, they all have very common uh offers on them. And so our team basically created a query to track just these casino websites. And we realized that they were basically segmenting this by favicons or by brands. So if you figured out one brand's favicon, you
could just search for just that favicon as a filter and then get the thousands of websites where they were impersonating that casino brand. Um and we basically had strong suspicions that it was fake. And then in our process working with Wired um or with Techrunch rather on the publication of this research, they were able to reach out to all the online gambling brands and one of the major ones said this is fake. This is not us. and it further confirmed that this network was basically creating an illicit moneyaundering network abusing other people's brands to get over the finish line. Um, and as we started to realize that all of these gambling websites were created by
central actors likely tied to funnel or the clients, we started to look at the code of all these gambling websites and we found that there was a GitHub link basically embedded in uh some of the code and that GitHub link led us to a a profile that basically had every template that was used on funnel. And so we immediately said, "Wow, okay. We found a developer that for some reason they are making the templates that we're finding for the money laundering, the the pig butchering schemes, various investment stuff, just like all of us here." Um, so we looked into what they basically had in this GitHub repository and we did find that they had basic
pages in there about money moving um, and various Telegram accounts. And we were able to find that exact or very close to it actually live on the internet with their updated Telegram channels. And so we started to communicate with the telegram channels and we started to get a whole bunch more details about what they were offering, what these websites were actually doing. And it's basically a process where you deposit money at one end of this casino, you lose money, and then you can actually take the money back out in a different location. So, um it's classic money moving and these people basically um if their bank called and said, "Wow, you know, you just lost $10,000 on this
website. Are you aware of it?" Say, "Yeah, I was I was playing blackjack online. Whoopsy daisy." And the bank says, "Ah, okay. No, no good for you." And maybe you lost $10,000 the bank thinks, but you cashed out 9500 in cash somewhere else. And so these networks basically are deposit your your credit card or whatever that initial bank deposit is and then there's schemes to get that money out in the back end. Um they have many different ways to do that. Um and we just want to know that on these telegram channels they also bragged about the different casino brands. So you could pick the casino brand that you wanted to launder your money through which is a really creative
service. Um, and this is briefly what that uh process looks like of moving money. It's a quite complicated, but this is really common in China. And so, if you're doing research into Chinese threat actors, you absolutely need to appreciate this type of infrastructure because we're seeing more and more and more all of the various crimes, the crypto crimes that are going on. A lot of these folks are trying to launder money and there's with all these this triad groups, they're trying to launder the money. And so really you have to be aware of how these systems work. So when you see a website that's promising various features, you recognize it. And just again to harp on that, it's
that yes, it might be a lowquality or trash website. Yes, it's probably not going to be used by somebody to lose a couple money, a couple dollars, but it's part of their network. It's part of how they're running the entirety of their scheme. And without that extra window, you only ever have one side. So that's just something we want to encourage when you're doing your thread hunts is make sure you know the full picture. And speaking of knowing the full picture, so one of the things that we did uh or found during our research is that there was this huge retail fishing scam. And one of the ways that funnel or Triad Nexus is mapping their
infrastructure is they actually tie different types of scams or different criminal clients or different types of uh fraud to specific scam records. And so what we found on this one is that all of these different retail fishing scales are actually tied back to a single uh CNAME record. So again, that talks about that piece I said earlier where if you know how they're managing their infrastructure, now you can go uh track the rest of their infrastructure and now you can characterize it and help protect your clients. So again, the 650 domains on just that one CNAME record, right? Uh this one was a ton of butchering and investment fishing login pages. You can see them
some uh previously live examples right there. But again, just a footstep that that's an entire CNAME record just dedicated to criminal fishing, dedicated to pig butchering. And that's one of and that's how they were managing their infrastructure. So when you break that down a little bit further, we're going to get a little bit more technical. Please stay with us. Don't don't eyes glaze over too hard. I promise we're still interesting. Um you can see the different ASN that they have from highest to to lowest density. You can see Microsoft, Amazon and Cloudfare right there in the middle. And briefly as we're looking at this slide, um, so there have been changes here. Um, as we had mentioned, basically
Microsoft has been cleaning this up in real time. Cloudflare and Alami was also targeted at one point. And so if you've been targeted by this threat group, you have to come up with real time defenses or they will double down, triple down on the abuse. And Amazon, as we mentioned, we keep on telling Amazon, you're screwing up. What are you doing? We've written public blog posts. We've spoken with them. And even today, Amazon IPs are still mapped in this infrastructure. And it's it's bananas. And other brief note, the CTG server, if you're a thread analyst, look into CTG server. That's as close to a bulletproof host as you're going to find. And there's a lot of very
interesting Chinese scams out at ASN. >> Yeah. And then again, just as you're going through, if you see suspicious TLDDS, top level domains, keep an eye out for it here. A lot of the retail fishing scams are on.com, but again, they they vary as well. If you see XYZ, it's probably not good. Um, another piece of infrastructure or another infrastructure detail that is worth noting here is that 100% of the ones in this retail fishing network all had name servers that were associated with this specific registar. This one is the gname pt.ltd. LTD. This one's out of Singapore. So, they'll either be on uh the A share DNS or the B share DNS right there. And then if we go to the next
slide. Again, they're all that's cuz they're all registered out of again that same registar. So you can use those infrastructure details the name servers that they're using the registars that are using the ASN they're using uh how they move across their CNAME records are how they manage all of that to get into the mindset of the thread actor and use sit from their side to track everything that they're doing. So um what we've basically covered today is just the tip of the iceberg for what's going on. So we've explained part of this this funnel triad nexus and set of those C names that they're using as we mentioned they're expanding this rapidly and we believe that they read
our blog post they read our research on this and they s our little chart with the C names and they said what if we made it a thousand C names what if we did 50 C names every day and we used DGA domains on those as well and so there's a lot of very interesting threat research that um that is still ongoing with this and basically lots of opportunities to see this. But um we do want to point out that these types of moneyaundering networks, these fake casino websites, you're going to see them in a lot of different places. And if you see it, pause. You may have something there and you should just keep
on uncovering that on. And uh there are a lot of open questions. >> So we've got a couple open questions here that are still uh existing on Fred Nexus. One is how much money has been lost to the different scams. we see the scale of which they operate, but we don't always see all of those transactions. Um, the scale is increasing. It's been around for a long time. Uh, and it's getting more complex every day. So, it's getting harder and harder to track. Uh, how have they stayed online while abusing prominent brand names? That's a question for the brand owners. I don't want to delve too much into that one. Uh, but it is something to think about. And then who's
ultimately behind that? That's the piece that we've been trying to get to today. That's the piece that we're continuing to research. how many people will it take to keep something like active. You can use automation but a certain point you still need to make sure that your operators understand all of the pieces and then with thousand tens of thousands of different domains running different scams uh the infrastructure needed to support that just sort of grows over time. Uh, another question we have is other CDNs which we have internally noticed and we have other research on we call them malicious CDNs but how many others are focusing on it where this illicit revenue that they're getting is
part of their uh part of their business model right so they're CDN yes but they're also providing that service to thread actors specifically and we saw that 80% discount it leads you to wonder how much of their infrastructure is valid benign versus uh automatically detected is malicious. And then a couple more questions here. We got how the public is being targeted. There's obviously a wide array of different brand names and then how the cyber security industry can collaborate to take down this network. Sharing research as we here as others do elsewhere helps a lot. Whatever you can talk about publicly. Obviously there are certain things that even we omitted from this because again the threerstors do
read our blogs. We have seen in real time they our blog goes live. they see it, they change their infrastructure and because they did that, we get to track how they're doing it the new time. Uh so I appreciate that for thread actors that are out there. Uh but and really the the key to this is uh collaboration is key. So none of this research really would have started if people hadn't talked about that polyill supply chain attack. And even though people were brushing aside the redirections to lowquality casino websites, we knew from our research that there was probably something behind it. And so we're here sharing this research. We're also talking about like how Amazon is
currently behind the the uh the process. They're really not getting it as fast as we could. But CloudFare's done a great job. Microsoft Okami, there are ways to stop these folks that they stop trying to target your network. Stop trying to illicitly acquire IP addresses. Um, and as people are researching these types of networks, if you know about financial losses, um, trying to submit them to ic3.gov, that's an important service. IC3 is basically used by law enforcement and prosecutors in the US to help connect a website or a network of websites and the actual financial losses from them so that we can get the resources to prosecute those networks. So, it really does take a village to research this
type stuff and then get that in from get that in the open. So, wanted to thank everyone for uh for here for being here and and your time today. Yep. So, again, just the the key thing that we focus on here at Silent Push is getting to the pre-weaponization phase, right? Getting to the left side as they're standing up the infrastructure, understanding how threat actors are standing up their infrastructure, and then providing you with a platform that lets you do it. So, if you like try that, if you like to follow along with any of our steps, you can register for free. our community edition right here. Uh you can take a picture of the slide,
you can come ask me, you can Google silent push. All of them will get you to the same place. Uh but again, I just want to help move the direction of thinking to stop getting them after they've already got in. Ano does not help you. An indicator of compromise is probably already taken down. They might have already abandoned it and if you go after it, they don't care, right? We need to move towards indicators of future attack, which is the pre-weaponization phase. We need to be catching them as they're standing up their infrastructure and not alerting them, but just not letting them in. So, thank you everyone.





