Fangxiao, A Chinese Phishing Threat Actor by Emily Dennison and Alana Witten

Show transcript [en]
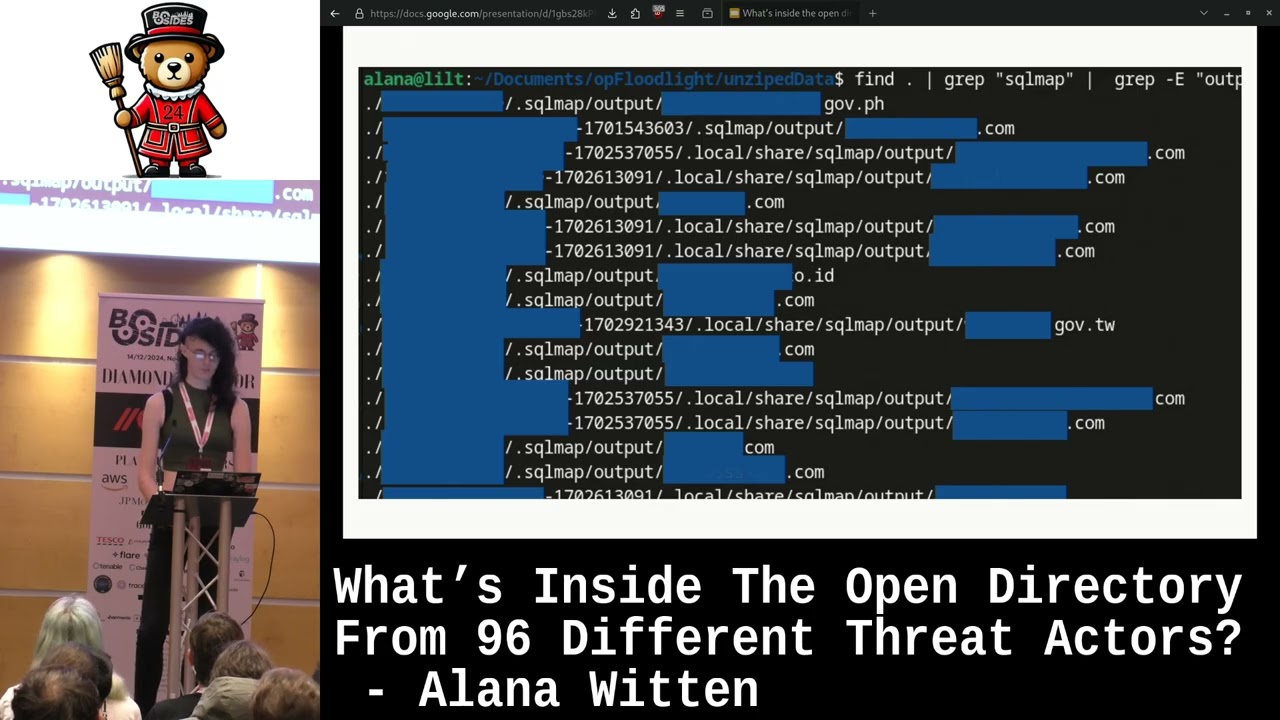
Today, we are going to be walking you through our six-month and frankly ongoing investigation into Fang Xiao, a Chinese phishing threat actor. So, who are we? Who am I? My name is Alana Witton. I am a professional Googler, so I whack things into a search engine and hope for the best. I am also a bug bounty hunter and a cyber threat intelligence analyst at Cyjax. Oh, there you go. You cut me off. I have a Twitter account where I post regex so horrific that HB Lovecraft couldn't read them. And I have a medium where I read thousands of bug reports and I condense them down into actionable summaries. So, let's talk a bit about the problem that is Fang Shao. So Fangxiao are a phishing threat actor. So the victim will be sent a URL similar to one like this, and then they will click it and be redirected through various different Fangxiao owned domains before finally landing on a campaign. We think they do this for obfuscation and for infrastructure resilience. Fangxiao own over 42,000 domains Each domain has the capacity to act as both a redirect node and the final campaign. And so the user will go to the campaign, they will answer some fairly benign questions that aren't really recorded or don't really matter. And they will then be offered with a brand specific prize. Fang Shao offers impersonate over 400 different brands. Before that, the the victim will be required to spread the campaign and send it to their contacts via WhatsApp. So it kind of operates as a self-propagating WhatsApp worm. Finally, they are rewarded for all their efforts by being sent to a domain called getprize.club, which is then used to serve payloads. Let's talk a bit about the goal, what we actually want from this. First of all, Every time you go to this URL, you seem like you get more and more domains, and it kind of seems endless. But can we kind of draw some borders on that? Can we figure out how big is their infrastructure? Secondly, what is the second thing? The second thing is, can we get some attribution for this group? Going through domains to a docs is going to be difficult, but how far can we kind of figure it out? What can we figure out about them? How they work? Who they are? Anything we can kind of get our hands on. And lastly, What is the point? This isn't some guy in a hoodie in a basement. It's ran as a collective that's considered costs and profits, logistics and scaling, risk management and contingencies. But at the end of the day, we'll go through all the trouble. So, I'm just going to run through quickly some of the payloads that we've come across from this campaign. It's really important to note this is only a snapshot of the payloads that we've seen. The payloads and the Fanchai websites as well were extensively localized based on user agent and IP address. And this was just from one point in our investigation. There's more on this in the report, which we have a QR code to at the end. So one of the things we saw as shown in this diagram is the Triada Android malware, which is a modular Android Trojan. It mainly lives in memory to avoid detection for persistence. And this was for true malware advertising on the Yelix advertising network. You can see the diagram of redirects here. Another thing we came across was an Adware Android Cleaner app. You can see here it was on the Play Store. It's one of those things that says, oh, you have a virus, download, fix your computer. We did some static analysis in it, and it had dozens of advertising networks in. I mean, opening it, anytime you tap, you would get another ad. It's this, clearly, quite a moneymaker. So one of the domains, as Lana mentioned, was getprize.club, where the domains involved in payload serving. And we noticed that every time you got redirected through getprize.club, the URL parameters were the same. See here in red, there was this like u parameter. And so we thought, what would happen if we just clicked some buttons and changed it? And it turns out that if you do that, you find an entirely new set of sites and campaigns, which are a series of fake dating sites, which are linked by redirects. You can see here, this is like on getprize.club, the kind of like same survey stuff, and you'd have about four questions like, you know, do you want to meet women in your area, you know, blah, blah, blah, blah, blah. And it would redirect you through to a series of fake dating sites. We don't know for sure that getprize.club is run by Fang Chao, We don't yet have the evidence for that, but we are continuing to investigate. And so these fake dating sites, there were dozens of them. Again, they were run by a bunch of shell companies. A lot of them were in Cyprus, like Bulgaria, Jamaica. A lot of them shared either the same address or identical terms and conditions, et cetera. So they were very clearly linked in some way or another. And you can probably guess what's going to happen. put in your card details for verification at no charge. And if you go on Google reviews, you will find lots of people who have been scammed by this. So we concluded that it's highly likely that Fang Chao is selling clicks. They're acting as lead generation. They are the bait. And then someone probably on an underground dark web forum can buy clicks to whatever you want. And so we would continue to investigate. And then one day I wake up and I get some really panicked messages on Microsoft Teams because getPrize.club like the central investigation has just gone down. So we're screwed, right? Wrong. So for those of you who don't know what URL scan is, it's effectively, they describe themselves as a sandbox to the web. You can like scan a website, it will like screenshot it, save it, give you like an object model of all the things it calls out to, and it will also allow you to pivot on things it calls out to. So we found that every single Fangchia site, it was out to a JavaScript file called yming.js, which is involved in fetching the new domains that are served. So we were able to pivot on this and find tens of thousands of URLs scans, finding a bunch of websites we hadn't found before, brands we hadn't found before, etc. And track it to be back to 2019, which was obviously significantly before we'd started investigating. And as you can see here also in this slightly complicated diagram, we found a link between the AdWare app previously mentioned and the fake dating sites. So the IP for the app developer, their website, they're called LokaMind, shares an IP with a couple of other like fake dating sites, and those we had like historic URL scan stuff showing they linked to sites redirected written getprize.club. So that's significant links suggesting that they are strongly linked if not the same actor, to be clear. We don't currently know if these are fang chow, we don't have the evidence to say getprize.club, that first link, if they're the same person, although investigations are continuing and watch this space. We were doing some investigation and we wanted to do some analysis on their IPs. However, we went to grab that IP and we saw it was Cloudflare, everybody's favorite. So the question then becomes, how do you bypass Cloudflare? And the answer to that one is you don't because it's Cloudflare. So what do we do? Well, we don't need to bypass Cloudflare. We need to bypass their implementation of Cloudflare. Bangshou were not this kind of monolithic, perfect organization that have existed for all time. They're a group that changes and improves over time. And they weren't as good as they used to. They weren't very good in the past. So what we do is we look for showdom for internet archiving data. But then the next problem is if every domain is linked to a Cloudflare IP, how do you find an IP which is in their infrastructure but not protected by Cloudflare? And the answer to that one is you look for similarities between all the campaigns. And the one thing that is constant throughout this is the favicon. If you take the hash of the favicon, you whack that into Shodan, we then found an IP which we could verify was theirs by going to it on port 80 to see it hosting a campaign. And then we did a port scan for it, and we found quad 8 was open. If we went to that via a browser, we were redirected to forward slash login, and we were presented with this. I'm not a linguist, but that doesn't look like English. and it's kind of indicative of where the threat actor might be from. So the next bit of geographic attribution that we did was TLS certificate OSINT. So some of the sites you selects encrypt certificates, it was a bit hit or miss, not all of them did, but we were able to scrape from sites that we'd identified internally and also from URL scan and build up a heat map of when certificate registrations were. And mapping it up to China standard time, as you can see in the red box, there's a pretty clear pattern of about 9am till about 10pm is when the majority of the certificate registrations happen with obviously a spike at 9am. So that is reasonably strong evidence that we're dealing with someone who's in that plus-eight time zone, which is China Standard Time. And so that's further evidence that Fangchow are in fact a Chinese threat group. So some key takeaways from this is they own over 42,000 domains and they're growing and they're getting larger and larger and they're growing. registering more and more domains every day. We have kind of evidence to suggest they're from China. And lastly, they've spent over $72,000 on domains alone. That is an employee cost, that is a maintenance cost, that is a hosting cost, that is just domains. So, yeah. Thank you everyone for watching. If you'd like to read the white paper, you can go to SciJax.com or you can scan the fancy QR code. There's also some IOCs there. I have been Alana Witten. And I've been Emily Dennison. By some IOCs, we do mean 42,000 IOCs. And yeah, thank you very much. If you have any questions, then please feel free. And please do read the white paper, because it's a really good read. Thank you. Any questions? Anybody? So you mentioned there was a trend of them redirecting to credit card scams and things like that. Obviously they're hosting what would appear to be for other people. Obviously then potentially cycling some of that to cover the hosting cost of things. Are you able to actually identify any advertising activities on criminal forums and things? That's a really good question. We did have a brief look but we wanted to have to find... Sorry, can you share mics? So we weren't able to find anything, unfortunately, but at some point we want to have another look and just make sure if we haven't missed anything. Any other questions? Just to add on to that, I think the difficulty is also that you don't know where it could be. I mean, they could be on like a raid or something, or they could be in a telegram channel and you'll never find them. it's impossible to know for sure. Maybe a really dumb question, but is there, what's the next step for you guys then? Is there a plan on building on the information that you've already accumulated today or what's the, how do you see this going forward? So firstly, continuous monitoring. They're getting more and more. They're approaching and making more and more IFCs every single day, obviously. I think last weekend we were prepping for this and we were looking at their infrastructure and they made another massive change, which is going to take a long time to figure out. It's fun. But yeah, they're just going to continue to grow and grow. They're profitable. And there's going to more and more, include more and more brands. Yeah, I think it's a good question we're just going to keep digging and seeing what we can find you know we had a running joke that oh you know we're done with this and then we click something and find a whole new you know set of leads and stuff so i think it's sort of as long as this keeps on going we'll keep on digging and just see what we can find you guys thanks uh i just build on that are you guys going to continue publishing new information as you continue to find it or are you going to time this because this is quite interesting right like it could clearly there's a lot of different opportunities, a lot of different opportunities for people to fall foul of this. So is there a kind of, I mean, is there kind of like a almost kind of like, what's the website, is have I been pawned kind of version where you kind of go, actually, I don't know this URL looks a bit suspicious. You put it in and it comes out and says, actually, this is linked to this project. Is that, do you have anything like that in mind or? It's not a bad idea. We haven't really thought about anything specific, but we're just, seeing where we end up. Yeah. I mean, the boring answer to that is talk to sales and get you in touch. Yeah. Any other questions?