Fangxiao, A Chinese Phishing Threat Actor - Emily Dennison & Alana Witten

Show transcript [en]
hello hello welcome today we're going to talking about Fang Xiao a Chinese fishing threat actor the one we've been investigating for the last God knows um so first of all who are we who am I my name is Alana Witten I am a professional googler I whack things into a search engine and I hope for the best um I'm a bug Bounty Hunter and I'm a cyber threat intelligence Analyst at psyjax I have a Twitter account go follow me my name is Emily Dennison I am a professional button Pusher I am also threat intelligence Analyst at syjax and you can find me on Twitter and on Macedon which is where I'm told all the cool kids are these days
so first of all um thank you are a fishing threat actor they own over 42 000 domains and the kind of the whole point of the scam is they will filter for high value clicks once they do that they will then convince you to spread the campaign so it acts as kind of like a self-propagating worm and then lastly a little funnel you into one domain called getprize.club which is then used to serve payloads so imagine one day you're you're doing whatever you're doing and you get a text like this one on WhatsApp on Facebook Messenger on anything and there's no context there's no nothing it's just it's just that but it's from a friend or a contact or a trusted source
um and you think I'm bored I'm curious I'll click it looks like this um some weird stuff happens with the URL uh you don't really notice who looks at the URL um some redirects happen and then suddenly you see this and you think yeah it's a scam um congratulations fake reviews kind of very very pointless it's it's very obvious um and that's great you click off and carry on with your day but they're not really after you they're kind of after people who are a bit more technologically inept a bit more uh vulnerable um and people who see a brand they like and think yeah yeah I'll trust that and when Fang Xiao impersonates over 400
Global Brands there's probably something for everyone um next in the in the scam you are awesome benign questions they're irrelevant the data is not recorded and then you are sent to this page where in order sorry and then you're offered a brand specific Prize or just money um and then in order to redeem your prize you must spread the campaign to your contacts hence the uh the cycle um what am I going from here uh yep and you were finally rewarded by being sent to the domain I mentioned earlier which is then used to serve payloads so what do we what do we want from this um earlier I mentioned that when you go to a domain you're redirected uh you
actually rejected more and more domains so they kind of seem endless whenever you do it it's more and more and more and more but we kind of wanted to know can we draw some borders on this how many domains do they actually own and can we can we kind of put a hard limit on it um next attribution going from a domains to a docs is going to be difficult but how much can we actually figure out about the group themselves and the people behind them and lastly um what's that actually the point of this uh this isn't some guy in a hurry in a basement it's it's ran as a collective that's demonstrated consideration towards costs profits uh
Logistics and scaling risk management and contingencies but at the end of the day why go through all the trouble so before I we answer those questions I think it might be useful just give you some context as to kind of the infrastructure so I mentioned there 42 000 domains they the prevailence scheme for domains is the one on the screen it's one word full of another word followed by a top level domain um they have a back-end dictionary which they pull from and the great thing about it is because it's such a scale it's all automated and they don't really check domains so here's an example but um um for example because it's automated don't really check them so we have a
generally propaganda at top which is always nice they're honest at least another one extraordinary trick and lastly my favorite uh genuinetrap.top it will send a link called genuine trap and you fall for a trap that is genuine um I think that might be on you uh next we have two types of links uh join links and end links so I mentioned earlier they have the redirection chain uh it's very important you cannot skip the three Direction chain you have to join via join link and and you cannot uh join on an end link if you do you'll just get an error so they're made up of the following you have your domain followed by your brand ID or parameters
and tracking value the brand ID is irregular which is annoying for when I want to do analysis and scraping um it's usually kind of the name of the brand abbreviated heavily plus some obfuscated stuff to make it annoying uh followed by parameter which is usually just a couple of letters and then a tracking value which is Epoch time plus some characters uh the epoch type the tracking value is used a for tracking and B for they don't want you reusing the same links um because just for making it harder for analysis so if you use the same Link in the same Epoch time you it just errors out uh the Nexus and links they're very
similar to the the join links however they have a random string which just makes obfuscation and enough fun to analyze um obviously oh one more back um and that last the reason they have this is because here uh they will host like hundreds and hundreds and hundreds of campaigns on this but change it with that um that you were random string I think uh next thing is through the anonymization methods we we've we found out that they were using Contour VPS and I think it's just like an interesting tidbit that kind of reflects how they're kind of very cost like cost oriented and how they're more of a reflection of a business uh this is just at the moment
the best um the best price for kind of resources VPS you can get we know they have a couple of them uh we don't really know how many we think it's the first few though okay so let's talk payloads so you go through the thing you share it to your friends you know get some angry text saying have you been hacked etc etc and then when that's all done you might remember there was a big red button to continue so where does that take you what you know what's the point of all of this so this redirects you to an endpoint on normally the same survey you see it here it's the ads of the web
um parameter in this Javascript file this Javascript file is called uming.js remember that it will come up later so at the start of this investigation this endpoint third um index.php endpoint redirected to a site called getprize.club that went through a bunch of further redirects to where you'd end up as a small sample of some of the pillows we saw we saw for example the Triad Android malware you can see the redirect chain here this was actually served through malvertising on an uh ad Network called elix which is owned by going to be called vertica that will also come up later another thing that we saw was an adware Android cleaner app so developed by a company called
locomind and you know you click through and you get notifications saying you have 11 million viruses down at the app it will fix everything and no surprises it doesn't fix anything but having done some Dynamic and static analysis of it it has like at least a dozen different like tracking and advertising uh sdks net and you can't click you can't do anything without at least one or two ads popping up um so I mentioned a site called getprize.club every time you've got redirected through gatprize.club all the lights are going off oh that's dark okay every time you get redirected through and they're back every time you get redirected through get prize Club um there was the same parameter the U
parameter and so we thought what if you change one a zero to what you know why not that'd be fun and of course it reveals an entirely new campaign so the first thing we need to point out here is we can't say for sure that this is sang Chao we can't say for sure that getprize.club is owned or controlled by fengchao but there are significant similarities what you see here is what we called love me but it was a bunch of fake dating sites and a different branding with the same sort of forced um like four questions feeling redirected through and promised you know to find true love or like great casual sex or you know whatever
and surprisingly uh you did not find that from this um so you get redirected through a bunch of stuff and you end up at a bunch of fake dating sites which are run by a series of shell companies and like Cyprus Bulgaria Jamaica they're all you know registered at like lawyers offices and the kinds of places where you can pay them better money for digital marketing agencies and end up having you know a company in any jurisdiction which has dodgy records oh no online records and it's hard to find information about them and again no surprise what these are for putting your credit card details for age verification you go on Google reviews everyone's complained they're being
charged and they can't you know get their money back or contact anyone so we concluded that it's highly likely that Fang Chow are profit motivated that what you see after collecting that thing is they're selling stuff to the highest bidder they're going through advertising networks their basically using this as a lead generation scam to try and you know get as much money from advertising so we thought let's continue to investigate let's keep going and then I wake up one morning um and open my laptop and see some rather panicked messages because getprize.club has gone down so we're screwed right wrong um for those of you who aren't familiar with Google tag manager or Google analytics it's a tracking thing it lets
website owners basically see how their website's performing how many people are visiting and each campaign has a unique tag you can see here um interestingly Fang Chao reused these tags across sites sorry I'm getting very close and far from the microphone um so we can use this tag ID to correlate cross sites and find all of the sites that are controlled by Fang Xiao using the same tag so opsec tick number one for cyber criminals don't reuse Google Tags um we pivoted across something called URL scan for those who aren't familiar with URL scan it's basically a web service where you can scan um a website it will log all of the quests or the assets it calls out to so
if for example it has a script which has this parameter you can filter across the entire artscan database and find every website that calls out to this tag although it has this parameter so thank you often used two or three Google tags on one site again I'm not entirely sure where they did this but this gave us a place to really you know get our teeth into it so we could you know pivot on these but most tags were only reused a couple of times so we ended up writing a little basic self propagating spider you'd give it a website your scam result it would download the HTML it rejects out to all of the Google Tags then search URL scan
for all of the sites with that Google tag and basically expands each time download again again again and expand this worked fine but it did have a couple of problems the first problem is the date is quite granular you know when you're dealing with tens of thousands of domains and most Google Tags will read across one or two domains that's that you're not going to see the visibility you want to see and the second issue is obviously it's quite slow because of the API rate limits and also if for whatever reason you pick up an unlucky start tag you might never end up with one of the tags that's used frequently for example this tag here which showed up like 10
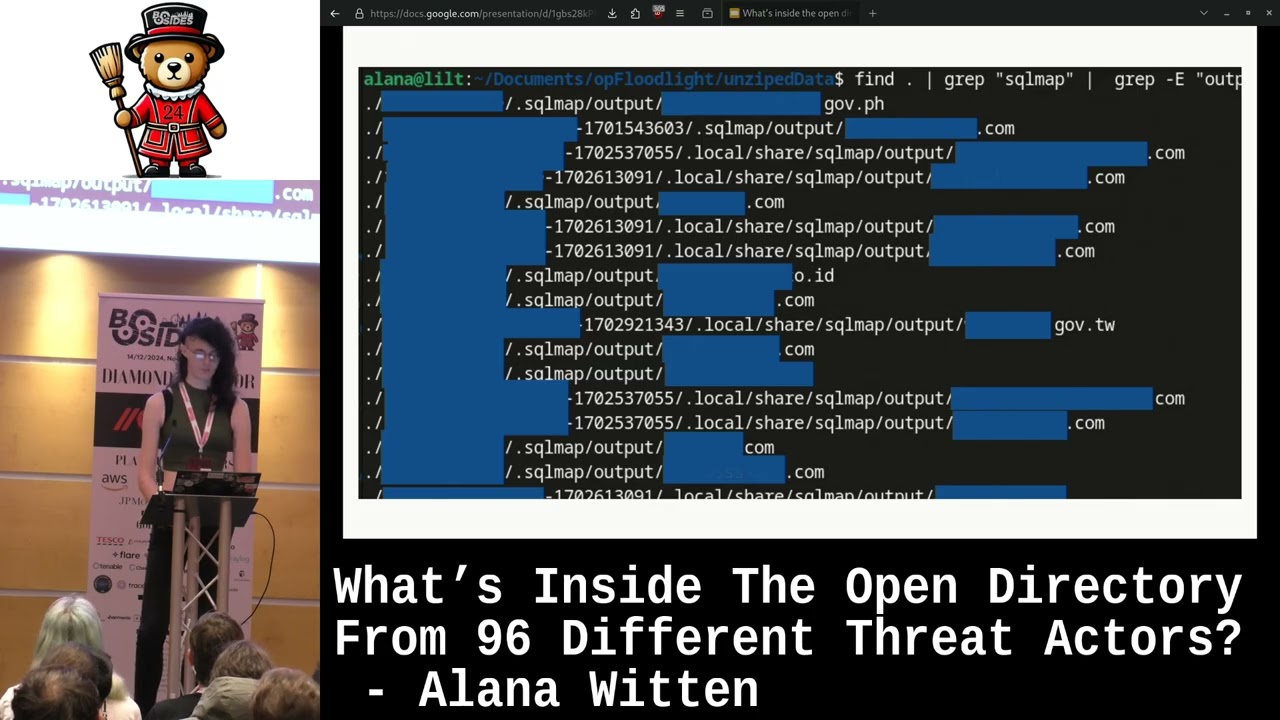
000 times for some reason um so this was good and we thought you're asking is a valuable source of data what else can we do here so this is uming.js that that file name I mentioned earlier that file I mentioned earlier and pretty much all the financial sites we found called out to uming.js and uming.js is a very unique name we couldn't find any other sites on the Internet or at least on euroscam we did a bunch of like open and search engine talking as well that called out to human dot share so if you just filter a map you could find pretty much everything shell site that had been you know that was already known
of so we we use this to find for example the first site uh the youtubing.js so this iteration of the campaign the uh the scam appeared in 2019 the structure changed over time for example they tried gamification you know they tried like having a fake slot machine you pull to get your reward and you always win eventually but you might lose once or twice to really you know want to get you like to get you hooked and so you remember those things that I was saying you will be tested on this later um you'll remember this they're important because we managed to find a bunch of links between the developer at the adware app um and the fake dating sites so get
price.club which redirects to that fake data uh not that data site the app uh the app is developed by locomind this is hosted on an IP address which shares which has these sites host on as well and as you can see I'll move out the ways you can actually see these sites on the same IPS local mind redirect to sites that getprize.club also redirects to so what we've got here is like shared redirects um historic redirects this is mainly archive data um basically showing there is a link between the app developer and the fake dating sites um again this isn't enough evidence to say for sure that I think child but it's really interesting to point out that you
know there is a link between at least two of the payloads okay so another form of essence an analysis we did is certificate ocean for those who aren't familiar with TLS certificates um they're obviously you know the thing that gives you a little green padlock in your bar and they have a bunch of metadata in them one of the most important bits is the not before thing this is basically stuff issuing time it's used that certificates are only valid for a few months so they can be revoked Etc um and usually this Maps up pretty neatly with when the certificate was issued so we scraped about 6 000 give or take certificates from known Bank child sites we put it into
like pandas data frame normalize the data um something interesting to note here is that you know it's obviously the just date time objects um let's encrypt back dates the issued by Time by an hour to avoid issues with clock skew or you know devices that are running a couple of minutes behind that would give you a terrifying like TLS issue otherwise you know the big red thing saying something is wrong here so if you're doing something like this look up your certificate issuer and look up what kind of back dating what kind of stuff they do to avoid that clock ski issue because it will affect your results um then what we did is we heat map the
registrations using sbone and some incredibly messy code that I will not be sharing here and you can see here inside the nice Red Box 9am to about 10 p.m China Standard Time so this is further Evidence again that you know okay you're likely dealing with a Chinese press actor here and it's interesting that especially you know throughout the night you've got almost no activity whatsoever again further evidence that this is China okay so one day I was like let's do a port scan and I tried to do that and then I ran into my best friend cloudflare um so the problem with I haven't told you is their entire infrastructure is behind Cloud but makes incredibly annoying
um so the question then becomes how do you bypass cloudflow and the answer to that one is you don't because it's cloudflare um but we don't really need to bypass the other we just need to bypass our implementation of cloudflare so fan share we're not this kind of Monolithic perfect entity that's always existed they've improved over time so all we need to do in theory is go back to the time when they weren't as good so then we looked for archiving in data for the internet which leads us to show them but then the second problem is if we're using domains to identify fan shell sites how do we find a raw IP which is within the
functional infrastructure but not tied to one of the domains and the way we do that is by looking for commonalities between the entire campaign set and the one thing that was common between everything was the kind of the thing that everyone forgets about is the fav icon at the top of the screen if you take the hash of that Fab icon you run it through showden um you'll get we actually got a few of our IPS if we went to Port 80 on the IP you saw campaigns being hosted so we knew it was in their infrastructure and then if you did a port scan we revealed quad 8 was open going to quad 8 revealed
this this is a internal admin login panel um if your back-end infrastructure which isn't meant to be seen by clients is written in Mandarin it could be indicative of where you're from um and that's kind of what we thought was it and we were very happy with the report we we published it we were lucky enough to give a talk at besides London and we thought that was kind of it we were keeping a rough eye on it but doing nothing major and then a couple of weeks later in Rapid succession uh things changed first of all that kind of the thing no one thinks about the Fab icon suddenly now every new um every new brand had its own unique
Fab icon which stopped us from pivoting off her next uh the uming.js file and the Google Tags which we mentioned earlier which in the overly both code that had been gone to um so replaced by this which is a little bit harder to do um and lastly we knew they were going to do this because we found some leaks but they then implemented more support for things like uh Facebook messenger and that we know they're going to well we assume they're going to implement soon some more um ways to spread the campaign cool so you know we thought we need to keep track of them we need to find some other ways to track them and
I don't know how many people here are infrastructure people have ever deployed like a large-scale set of websites but something you probably need to do that is a CDN and financial already do use cdns they use them a lot unfortunately they've gotten the key benefit of a CDN if you're a threat actor is blending in with the noise that's you know if if everyone's like loading stuff from I can't make a city down the top of my head right now but you know like a commonly used CDN great it just looks like any other idiot's web traffic unfortunately Fang Xiao used their own custom CDN domains so some of them are very cleverly named some you might be familiar with JS
deliver it's a JavaScript CDN and the official JS deliver site is js2liver.net so thank ciao seemed to control gsdeliver.cc which doesn't really do much Beyond serve a weird version of jQuery we haven't really been able to look into that much um some of the TDMs are not particularly cleverly um named so you remember the advertising Network at vertica which owns elix has ooh dot ooh which I didn't even know oh was it like a top level domain until I saw this obviously this isn't playing show controlled but from the data sets we hacks to this was a very strong indicator a thank-chao like stuff we could use this to filter down and then filter through that data set
so full list of all the cdns that we've tracked can be seen here first dates we found them can be seen here as well and yeah so as Alana mentioned you know we spoke about this stuff at besides London and there were changes and stuff was removed so I think this really comes down to an important thing to think about if you're doing threat intelligence if you're doing investigations if you're publishing is that you have to assume the threat actor will read what you're talking about you have to assume they will understand that you've effectively given them a free pen test that you've you've gone in and you've told them all their vulnerabilities and they will probably
change things so I know that everyone does you know cool research and stuff and they're like I want to publish this this is awesome but you do have to be careful about you know at what point is it diminishing returns at what point are you just helping the criminals um and so we are continuing to track Fang Chow in other ways but we're not going to talk about that now because there's no real benefit to it and we need to keep our visibility so let's wrap up with some key takeaways first of all they own over 42 000 different domains and that is rapidly growing that's actually quite now there's a number from besides London uh
it's much larger um secondly there's kind of evidence to suggest that from China thirdly uh they impersonate over 400 Global Brands something I've been working on for the last month or two is kind of tracking how quickly and when they add new brands and it's something they do that's kind of like their day job is to research Brands and like make new stuff campaigns and things and lastly they've spent over 72 000 on domains alone that isn't maintenance costs there's wages there's an hosting cost that is just a main cost so if you think about that's one aspect of course what do you think their revenue is like what do you think their profits are like
uh thank you so so much for listening and watching if you would like to read the full report and you would like all the iocs you can go to that link or you can scan the fancy QR code I have been Alana Whitton and I have been Emily Denison yeah please do give the report a read because you know we're very proud of it and I guess we finished up with about seven minutes to spare give or take so like questions
um we've spoken to Brands and stuff but in general stuff like cloudflare or I mean good luck getting anything from cloudflare you know it's a black box they they won't take down things like kiwi Farms or that massive Community pressure you know you're not going to get them to take down a fishing campaign unfortunately it we've definitely thought about it but not really a lot you can do
that's a good question to be honest no um I I would really struggle to make a guess because you know it depends how productive someone is it depends you know that work ethic I guess you know it depends how experienced they are you know so that's not something I feel confident sort of speculating about I don't know enough to be able to make that judgment I don't know yeah it is something we've thought about for a long time but at the end of the day like we don't have any kind of it but it would be so hard to make any sort of real judgment that it wouldn't be useful yeah oh yeah
uh it's reasonably quick to be honest they register and it's up you know they they burn through domains quite quickly especially with older domains they would they're not up like six months or a year later so um if I had to speculate I would guess they might be taking advantage of things like introductory offers or you know to get cheap domains but I can't say that for sure but it's certainly not that they're buying all of these domains and sitting on them for five years and then you know using them it's buying go you know Etc um just building on that we we saw because obviously we've tracked them over a long period of time we did see
the introductory office thing at the beginning but then they realized that as their they've been over on for a couple years now they realized that wasn't really like sustainable or profitable which is why they moved to the top top TLD which we didn't really talk about but that is the most uh used TLT and to my knowledge that's the cheapest you can buy domain it's 1.39 on Alibaba um so yeah I just I think that reflects like kind of like how when they were first starting up they they had this idea and then as they've grown and as they need to be sustainable in the long run they've switched models to kind of keep lost costs low
also it's worth pointing out in terms of registrars they mainly used like Chinese registers or like dodgy no name cheap ones um there are a couple of questions I can't remember who was first uh you I think that's not good
so almost trying to protect Ed
yeah well I mean I think uh obviously you know psyjects just provide threat intelligence services and we do provide like further stuff about Fang Xiao that we're not publishing publicly um but in terms of I think this sort of methodology can be used for hunting for a bunch of stuff not just hang chow and if your your blue team is mature enough to start working on like fret hunting stuff that's always a good idea to start looking into yeah uh there's someone over there I think yes
sorry I didn't quite catch the end of that
and that's that's a really good question you know I honestly don't know for what it's worth uh after the b-sized London talk and after it went quite popular we did see a lot of a few DNS like protection services and providers did take the entire list and block it which is it's quite nice to see like your research has actually kind of made an impact which is quite nice yeah I think one thing to point out is that because they they churn through new domains and stuff so quickly you know you can have you know like yeah yeah uh actually yeah two more questions
that is something we've considered doing it's just they have a very large uh word list and honestly we've been too busy to look into that yet a that b when I say dictionary I mean the English dictionary it's not like a word list it's the English dictionary so that you can yeah you can just grab them and find anything you want um and secondly I didn't mention it I said that's the predominant schema they do have other schemas I think you saw a few on the the data analytics slide um yeah so then there isn't like one hard thing there there set on they will change it if they need them time probably questions so do you and
then
sorry I couldn't quite hear
in terms of companies that rating when we do inform some companies and then you know um I think you're better place to talk about informing companies because you've been working some stuff relating to that and then in terms of getting to the media this white paper did get to the media but after that you know a lot of the stuff that is continuing is more internal to skyjacks unfortunately yeah I think it's a pretty good summer um I know I know I I'm not I died my last I passed the domains on someone else and they send them to the proper people but I know they do get like I think the single registered as a thing called yeah
everything everything from Aviation to to fast food to supermarkets um we're something in the works is potentially like a kind of a have I been poned but for brands that we're trying to work on um but yeah everything there is there it's they they're very kind of conscious and they read as much as they can for example a while ago there was like an unemployment crisis on Nigeria the next day there was a campaign to do with that um for the World Cup the next day there was World Cup covered that was covered it's just everything you know anything yeah definitely I think that's pretty much us done for time so thank you very much and any more
questions give us a shout