BSMaaS 2020 - The Art of bypassing endpoint protections for red teaming engagements
Show transcript [en]
welcome to beside munich uh 2020 you know i'll talk for um the art of bypassing endpoint production um in this in the store we're gonna be basically talking about uh a lot of stuff about um evading you know the the anti-virus revision techniques power show uh let's say the um the different aviation techniques or uh different os uh with the uh beloved one windows of course um so a bit of disclaimer before before before really starts and uh we're going to be showing him different techniques and that involves a bit of vendors uh so our all purpose right he's only you know for for research uh without any offense or violation to to these vendors just part of uh
from our research so who we are uh my name is jamin napo and i'm principal offensive security consultant in camp gemini uh basically handle around the decay with the with the breaking things legally um and yeah i have also uh my colleague islam right here i gotta be doing deal in in the store so giving you the floor hi everyone my name is an offensive security consultant at capgemini i'll be talking today with jamil we will try to give you an insight on how to evade antivirus and how to make your redeeming engagement more effective cool so uh moving forward uh there's end of this you know the upcoming uh 30 40 minute um gonna be talking basically about you
know the the issues of red team and engagement and why you need it uh you know we're not gonna be telling you roughly what is red teaming uh this is more advanced uh tool uh we're gonna be you know also displaying a bit of aviation techniques tools things about the manual development uh stuff about you know windows api powershell and shellcode and uh the cool things in dot net all right so um in order for us you know to start you know if if you're doing let's say a return engagement and let's say you're facing uh you know you're doing a little movement you're trying to you know break into the um domain control whatever
um so it's it's obvious sometimes that you're gonna be you know facing uh in the art solutions uh it's it's not you know sort of let's say oscp lab or something that they're gonna be removed so that means you're going to be facing firewalls going to be facing you know avs advanced avs perhaps uh that involves more than uh the let's say uh semantic analysis or signature based detection so it could be behavior analysis sometimes that depends really on on what you're doing um so let's throw it this way so when you start uh let's say you've got you've got you've got into an endpoint actually the lady right here uh you compromised that um
you know with the smb hash ps exec or whatever now on the other hand you would need to gain access to another endpoint in the system that in a direct connection with the domain controller but right here you got a bit of wall you got an adr on this on this endpoint so how you're going to be bypassing this and what kind of tools that you're going to be using mainly how you're going to be bypassing this this sometimes it may look like you know simple but sometimes it could really break your team and engagement so that's that's why you would really know need to be prepared um now i'm gonna be talking about the
the the evasion tools now you know a fuel company and i walk for small companies and not all of them really afford to pay club strike and you know uh cryptos or whatever because at the end it's it is not legal uh but on the other hand if you're going to be doing innovation if you're going to be you know creating new refugees for deductible uh you know payload whatever you're going to be using encoders so encoders is sort of it's not you know cryptos is mainly you know transferring let's say um you have an executable then you get uh you transfer that into perhaps base 64 and then you you know in the wrong time you you
switch it back or whatever now this kind of techniques uh could walk perhaps before five fees but uh in the 2020 i'm not sure if it's still encoder's walk uh we're gonna we're gonna see this in action you got packers packers you could use you know uh sort of packer like qpx that the most popular one but also get detected uh because of its resources and stuff so uh yeah signature-based tools like arrow tools uh your arrow rules can detect this very easily you're gonna be using also binders or interpreters now encrypters if you develop when you own uh that means uh you know yeah in business you don't have really time so it's really obvious yeah you're going
to be buying buying tools and stuff and on the other hand it's illegal so what you're going to be doing uh you're going to be perhaps taking the open source one and here you come into the problem uh right here you know you've got you know corbett's right you've got vo it's well known in the in the community for uh you know um krypton to create a battle i'm telling you if you're gonna be using it it's all detected you know it's all detected uh meta supply or whatever polish c2 um all of these open sources are detected the reason being the the the av companies is spain full times guys in order to you know
research and github and create create rules against uh you know uh these guys and play signatures and stuff so i'm telling you it is it's not the right choice um all payloads of course get detected um even if if you create any wireless you know their iot's again is is really popular now right here i'm gonna i'm gonna be jumping into you know when you run a malware what could be the ways in order in order you know to bypass the 80s uh it could be using you know uh you're going to be using you know let's say mootix or persistence i'm going to be talking this in in the upcoming slot uh but just as for
now think about it you want you know to run something and then keep it over there and make sure that it's um if there's another instance that running the target system uh so you're not getting uh multiple shield back um you're gonna be running in the memory now the modern uh you know uh avs uh are able to detect in the memory unless you're encrypted itself so that that that you make it difficult for them or it could be you know running executables and when you run executables uh you got to be facing you know the the uac i'm talking about windows uh user access control uh there are stuff to bypass it but sometimes you
fail bypassing these and then you run in the normal you know user mode and the user move can be let's say not allowing you to to do any kind of persistence and stuff so you need to overcome this uh i'm going to be talking about about about certain techniques and a process halloween if you don't know what's process how on just in simple terms it is simply injecting sort of uh you know uh payload into a process uh in order in order to evade you know the the the detection uh that could be you know if you have a process you simply just injecting that process and continue but that sometimes fail and sometimes the behavior analysis still
uh detect that the ln injections it's really simple you just put your dll if you find you know codes or something or whatever and the target application but this requires you to know beforehand uh what kind of applications or stuff that are running on the target host uh i'm not going to be diving into delivery techniques now for the matrix what are the mythics what does stand for what normally if you regardless you know the the programming language that you develop in it uh it could be job it could be c-sharp or whatever uh but anyway if you're gonna be you know uh first running your own stuff and care about the persistence so in this case
you would need you know to generate your own mistakes now the medics means like random value random sting think about it uh when you when you're generated you're going to be basically calling if you're walking in windows you're going to be calling in windows api when api create uh uh this this basically this this function can handle regardless the language that you create human um the the uh the music's creation now in this case you could also check if there are other running instances uh that the way you do it using the mythics it's not about the process name uh but some edr solutions could detect you when you're gonna be getting the md5 out of that medics
and you know basically uh eliminate you your privileges uh but the this is what the magic stand for um normally you know i've seen the red team and engagement not a lot of people really care about persistence or whatever there's more about remote access russians or tools that use a real wall attacks now the fun with the matrix is that you can run a file and on the other hand take a mutex value of another application so that means let's say you run your application a portable way you try to write and you know the registry or something supplies is that your application gonna you know take a bit of periods here run around once
whatever that what what kind of things that you can't access it uh that means you know if the use uac is enabled so it's it's kind of difficult but anyway it's basically you can also spawn uh another music so you basically take another application value the moody's value and then you you know with the application when the system asks for it your application runs so that that's that's different than the dll hijacking or something it's let's say i call it hijacking uh you can find it you know more information about about it in in in microsoft website the cool website all right so in terms of resistance now the obvious one you know you can see
it right here is the run run once and you know register the keys you basically you try first uh to check this out the you know a bit of uh advancement or their first check if they can write to the registry and then on the other hand uh if there's exception through or whatever they just forget about it or sometimes they they they try to write in order for them you know to keep to keep the persistence of of them you would sometimes really care about this in indirect team engagement not let's say like the ra but on the other hand you would need to care uh what if the machine crashes what if you know your paddle doesn't walk you
know there could be a lot of things involved and especially if you walk in production environment so you need to really be careful uh about running running new stuff if you're gonna be walking on the registry good you could be walking with the servers or whatever anyway so uh you got usernik explorer startup you can run on ring three mode or whatever that you can inject basically in the registry keys uh the mbr record the com object hijacking or perhaps you know in the in the the system32 you can kind of place it for the file that get um initiated or calls like the app any dlls so right now i think yeah michael you're gonna you're gonna start
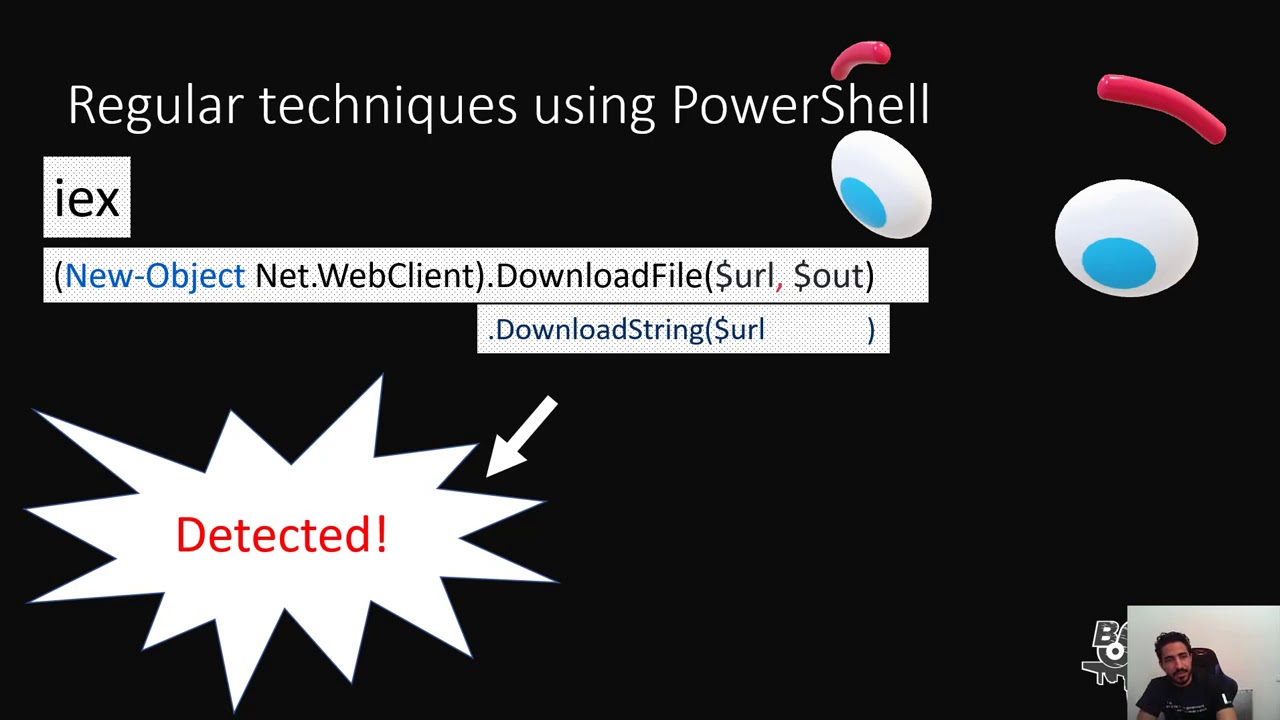
with a bit of power shelling um so take the floor again all right so we we now are going to talk about uh powershelling uh what we usually do is using these commands download file download string but we have been using this for a long time and it's already getting detected by antivirus so we we try to obfuscate our payload we we try to hide this from the detection of the antivirus using obfuscation but it's also getting detected so what's even better than dawn obfuscation is not using at all download file or download string here is an example of a script without using download file or download script we are using tcp sockets we start by defining uh
the client the stream and buffer and define our variables the client stores ib and the board for the tcp socket the stream gets the stream from the data that we already entered and we store our buffer in the buffer variable and we encode it using ascii encoding here we we we write to the buffer and we invoke bowshell and we start reading from the buffer and saving it in the variable bytes and then here we start decoding the buffer and storing the data in the data variable using the git string and then we go on in this if statement uh by invoking uh zakumon data and outputting in the terminal so uh it's a try catch block and
here's just some exceptions so we go on now to the powershell demo
we verify that kaspersky is running and we can see it's running and everything is working we start by scanning the scripts that we created and it's not detected and now we have our command ready to run the script we run the listener and run it and here we go we get that shell back home it will verify it and it's working and let's take a look so we know we are not cheating okay now we need to verify that after we got the shell it's already not detected and we are going to scan it using 36 different antivirus products so we upload it to clean scan and let's see
as we can see none of the antivirus products tell now detected our powershell script
let's wait for sofos and mcafee and it's still undetected
so as we can see with assembled technique we have bypassed the detection of almost every antivirus and we got zero detection rate from 36 antivirus products okay so uh for you who prefer to work with meter breather to use it as a payload so we are going to use another technique we are going to use a metal breather payload and included in a c container we are going to use msf venom to generate our payload and encode it using chicago and then take this shell and include it in our c container and execute it in a clean executable so how is it done in the beginning we will start by by creating an executable without our technique and see how will
the antivirus deal with that we are creating msf venom windows meter data reverse dcb and our local host and our local board
using the category encoder
here we are just creating an executable with an encoded payload which is which is the old way to create the payload and now let's copy it to our vector okay as soon as we copy it it's detected by the antivirus and let's verify it by scanning it and it's gone so with the normal encoding technique it's not working anymore so what we are going to do is we are going to create another payload and see we're just changing the extension here after we generate the payload node the size it's 557 and let's copy our shell code we will use that let's create a c plus plus project we name it clean
let's create our main file we will start by including the necessary libraries and that is studio.h that's for standard input and output and we will include windows which is uh the declaration for windows apis and then we define a constant with a payload array
and then here we add the size that we already noted during creation of the payload
and now we create our main function
okay here is our technique we will create an inject it's empty for now and we will create a statement here just to verify when the payload is working
here we start by virtual allocation so that we can allocate to inject in memory
so we do mem comment page execute read write
name copy and here we copy from the payload and to the inject with the size that we declared
and here we get our payload and do return to close gracefully
okay we are done what we can do now is just adding some dummy files you can create a resource bitmap and create another item here call it gui and just fill in any comment just confuse the yarau rules so getting network information and release and build now we have our clean executable we can copy it and let's see how the antivirus will deal with that
first let's set up a listener we are using metersploit because we used a meter better payload so exploit multi-handler we set our payload
so windows meter printer reverse dcb
we set our localhost
and our local board and start listening okay we go back paste it scan it and it's not detected so let's try and run it and here we go we get a meter breather shell and we are in let's verify it who am i and we are in okay now it's time to we have seen some techniques it's time to talk what is the use of this in the real world scenario well thanks thanks islam uh well i think yeah the mitsubishi is definitely not used in the uh and the rewards you know isn't it uh so uh now you know guys you've got red team and you got uh the the uh the the rats
uh what you're gonna be doing right here i'm gonna be really running around uh and it becomes really different uh but on the other hand there are some similarities um now in this this table if you're doing a red team in engagement you don't really care about resistance you're not scared about you know getting into that uh that lady machine and you know uh from from that popping that thing and then going into the um you don't mean control perhaps the yeah so it is basically like playing around now a rainbow persistence is really crucial and they we're touching upon some certain points right here um and also the red team and it's all over
when you when you are you know you take dominion admin uh and in the real world is it's never or you know over um you're gonna be updating and stuff uh so the the attackers really the criminals they really care about about maintaining their their their axes and also uh you know if you've got let's say um you're gonna believe in traces uh perhaps sometimes for the blue team sometimes this could be part of the deal and you know um in the in the real world they get uh really avoid detecting i'm talking about uh you know could be uh research institutions and stuff um doing these kind of crimes uh especially if they are
in a political way so they've got they've got money um in terms of investment now and the red team and you are not really doing the data breach don't you so it's mainly you know about simulating an attack for the real world what are you going to be doing you're going to be talking to the guys all right give me give him an idea about so it's it's not really uh it's not really the case so there's a bridge uh then then uh welcome to the club uh but uh right here i'm gonna be also uh you know talking about a bit uh about yeah rules so yara is you know been used uh for a lot of
by a lot of vendors uh without without naming them but let's say the 90 of the majority of the signature base detection already uh used in in europe so they kind of embed in yara into their engines and uh you know um development interfaces and stuff but at the end you've got the same for uh for you know uh signature-based detection so you basically um let's say you've got certain string it's the same in linux when you say string about certain file uh it could be asked it could be bonds it could be hex um so you basically you know say about the the meta description about that file the resources the url a bit of conditions uh signature
based now on the other hand uh by passing the signature base is not really difficult it is not really difficult at all uh but it just needs a bit of time about you know uh looking what's in there um so besides besides your rules you've got the behavior analysis malware detection now it's still in the learning curve uh because you also get a lot of false positives um i've done some engagement you know myself from my experience um on endpoints of network that contain you know twenty thousand in point two thousand point uh what what i'm telling you know it's it's a false positive so it's a time consuming all the on the other hand but
without digging into that much detail the behavior analysis it could be using you know machine learners the data set training set feeding it with the data uh published ioc uh tr sometimes they involve uh process names um and also an attempts perhaps you know to to gain access to certain uh you know certain ieps blacklisted ip you have listed ibs uh dynamic code you know uh analysis static analysis sometimes uh or perhaps you know if you let's say you're trying to create a project that gonna be let's say you make it an api call uh windows api call uh or linux or whatever you may use in in order to bypass the sandbox so if there's a call
for sets and processes that you know gonna publish the sandbox environment so that way it could be classified and the behavior analysis as the you know as uh revolution is gonna flag it as a malicious far uh you can also you know when you drop when you you spawn powershell uh you know download string download you know the these kind of data so that also the way that you you may get detected uh but of course there are different techniques to overcome this um you know because at the end it's uh it's a machine doesn't have the human intelligence uh but with that being said i'm going to be jumping into injirod so um this this guy you know uh has been used
over the past let's say six seven years um for you know about governments by intelligence but you know nations attacks and um basically started in the in the in the middle east um and then it spread over over the wall so hear what i'm calling in jira vs the ward so it's it's quite soup and the reason that we chosen in order to what up our poc is because this lady is you know um uh injury is i think famous uh as a detectable ioc uh more than pamela anderson uh so that's that's the reason that we we use it in order to show uh how in a simple techniques that you can basically clean it from all or
edr solutions so right here you know before six years or seven years there wasn't something called the cool now when donut core came to the table uh it's basically put in the capabilities that java has on the table in terms of you know across the platform and that brings available to for the criminals because you know the more they can reach systems uh in an easy way that you know um it takes you it could take you a couple of flights uh in order to money for you know you pay uh she'll cut boy whatever you may walk in uh walking with uh this guy's uh you know you can't you kind of better don't
get corner the cool thing about the call you don't really need dependencies you can't include all the dependencies in perhaps one file and then run it and and you know linux uh windows mac or whatever uh based on mono uh so in this case that that that's really cool but there's a disadvantages when the mellow developers uh you know uh fud there uh you know make the executable for the cable is basically the size uh because when you included a lot of stuff uh so that that way uh they're gonna be a lot a lot of things but rather than we make a really simple planet simple um we're gonna be starting with the uh with the demo uh for injury
and we're gonna see it both ways so let's let's get duty uh all right so this is the lady uh i'm starting it uh listening to normal port uh it's in a store that's basically a server so i'm building into my local host buying that same port and adding you know uh beside munich as the victim name uh without without you know including any process protection or whatever we can't do that ourselves uh but just care about creating the client so i i have already client and then replacing it with the new created file right here and then we we we we got it now what are we going to be doing is yeah take it take it this file let's
let's let's check it out uh first uh you know scanning it without any kind of you know specification or encryption or whatever so we're using right here at 31 um scanning you know adr um av right here and probably gonna come across all of them perhaps so uh right here you can see you know it's still you know uploading and and and you got 22 out of 31. surprisingly kaspersky sane undetected uh but we gotta move with that anyway um so yeah we've got uh other other ladies who are saying it's it's a clean um no offense but right here you can see you know it's it's all it's all got detected uh you know roughly we have 26
uh 26 out of 31 so basically all all of them and there are still ladies you know doing the pendant um and the scanning so that that that for obvious reason we just took the um the executable and then we we we just uploaded it uh out of out of generating it from ng right builder now uh let's check the the the file size it's 32 31 kilowatt 32 on the disk and and the next step that we're going to be creating all of this c sharp project console application and right here you know we have this is the program css starts in the starting place for our application we have basically the the the main method and we have a class
definition called util and util we use encrypt me and decrypt me and we're using right here you know a bit of threat um if we jump into utils right now you can see that what i'm doing is basically encrypting the string that i'm getting and the point um taking these bonds creating a key you can define the key that you want and the initialization vector the e v i'm using wide the the arundel algorithm uh which is really basic um normal cypher cbc move without padding uh you know for for for encrypting and returning this as a point array and the decryption is not the same basically uh but the the one thing that is different we just you know uh
trying to transform it so basically we encrypted with the key and then we decrypting with the key and right here we're just scoring uh the uh the the output the file that we generated from ngra already uh we output in it and to sr txt it doesn't matter the you know the uh the the extension right here a bit of threat and then we're using system the reflection though uh assembly law i think i can write a book about about this tool um but we're going to be moving forward so it's basically just loading uh you know the application um and the changing its entry point while the main application already starts so uh all right uh right here you can
see uh that the folder is empty and we we right now uh what we're gonna be doing is basically just you know copying this into our main workstation.3 for obvious reason you know because i don't want to define the path so it's easier right here so reading from the clients which is the server that was really using ng-run output into you know sr the txt you can't commit this line or whatever uh no i'm gonna i'm gonna be running in this demo uh you know i'm just putting a thread just to make sure that everything everything works alrighty i'm doing right now a build so please build a product for me so that the app
gonna be nice.exe as you can see right here in the output uh now if we go into the project directory we're gonna find in the bin directory and debug uh that that our file but you see it's uh the the txt is not created that for obvious reasons because we need um we need the compile time right here so we're gonna be now starting the application and going to read the points from the generator trojan encrypt it decrypt it load it into the main application that got started so sort of like you know doing jump so start the application encrypt decrypt and load the other application into the entry point that we loaded so it's like really simple techniques
now it's going to be a very slow you can see right here you know run as administrator even though without usc uh and getting the unification which means this machine got compromised and the we've got we've got the reverse uh reverse throttling back you can see that right here it's walking it's a bit i think slow at the moment because i'm using debugging right now but you can see the files um let's see if we're going to get the processes open to the connections all right so we are getting the connections rather you can see it's working even though it's in the sky time at one time all in all it's encrypted now closing this this error is
basically because i'm running debugging mill uh but let's now we verify it is walking uh what we're going to be doing at the moment is basically see what kind of endpoints edr solutions av can detect our noise file so right here you know you can see the the one let's see the new lady uh so browsing it
all right let's see uses jill sauce repo console application one bin file debug yeah that's it scattered see what we're going to come up with all right so all right so here we have 31 same as the old one uh we got a total of 40.5 kilobytes which is not even close to one megawatt and it's clean from all evs
0-31 you can see right here it's really hard for the signature based and also the the uh you know the behavior analysis tools to detect the encryption because obviously they have the key now someone may say that it's really easy because you can decompile the code really easily but i'm telling you that the method that you can't basically disallow your code to be decompiled so with that being said simple techniques created just to wrap up creating you know taking our output from injury the most famous right so it's detected from everything and then you know we we getting this boy we encrypted it using similar encryption run the algorithm uh create you know av we create in the
initialization vector and the key we're using the same key to decrypt and it's all coded even though it's clean so the conclusions if an av detects a signature that sadly means millions or thousands of people got hacked or compromised uh because the way that the signature based detection walks is basically when people you know get hacked let's say one thousand some one of them smart smart smart smart guy uploaded to virustotal uh you know uh unless they get it and then you know they they start you know deploying the update for it so uh um it is stolen avs is crucial of course uh but just the fact that if someone got detected that that means uh millions got hacked
bypass the signature base detection as you've been saying right here so we use the powershell we used you know uh we didn't even any kind of inspiration on the of the powershell itself uh we haven't done anything without just creating it socket and got by past um the the other thing that you've been saying uh the the metal project show which is also you know detected by a lot of people and also you know uh bypass with the simple technique just creating uh c file get that shield co and sometimes you know may every uh maybe although he's gonna detect that but on the other hand you can just split the shell code uh to base64 then you
need decoding and then you can continue the string so you make it really harder for them so it's not it's not something really difficult uh and when it comes you know uh we speak roughly on this and and red teaming and it's really crucial that you know what you're doing uh because sometimes you know i've seen some you know consultants um different different engagements um various companies that they're using you know just downloading rats and downloading you know uh shells and stuff excuse me without understanding so they what are they doing so at the end what they are ended up with is basically uh running and instead of securing a new client environment you basically
uh you understand what i'm gonna be saying so uh a few guys you know gonna be following us so you've got you've got islam right here um you know um my twitter and also a few questions about the materials the scripts uh all the powershell codes and stuff that we've written during this uh talk you can find them buffer overflow slash this this long layer you can just buffer overflow and gonna get there um just to not forget the references so these are the guys who using uh you know uh stuff content from the uh i developed our own content so thank you so much





