BSidesCharm 2022 - $how Me the Money! - Carlota Sage
Show transcript [en]
hi hello welcome to show me the money this is how you get business buy-in for a small organization to start your security program it is also known as are you sure you want to be a cesa i you know i'm not so sure you want to do that um i'm going to spend a few minutes talking about myself because i'm [ __ ] awesome and thank you and i like me a lot so this is my mug with my mug i'm carlita sage i am a virtual cso principal meaning i'm really good at being a vc so i guess i don't know with a company called fractional c sound fractional c so serves smaller small midsize organizations
usually sub 200 employee organizations they're small enough that they can't hire a full-time cso they're not ready for that step but they've also recognized oh hey that security stuff is kind of important especially to sales who knew so i'd say of our 30 clients 30-ish clients majority of our prospects come to us because their clients are going hey i'm interested in your product but like are you stock2 compliant like do you do anything about security and that is what drives them to us that's about 85 of them the other 15 the big majority of that is investors or board of directors say hey this is cool and all but i want to protect the money and uh you need cyber
security so why don't you go hire a virtual cso firm or something like that that that tiny little one i have exactly one customer out of 30 that came because they had an incident so the good news is that small and mid-sized businesses are looking at this earlier and they're taking it more seriously now before i was a virtual cso because at no point in my career did i go i want to be a virtual cso that seems like a great idea because nobody knew what a virtual cso is you probably in this room how many of you had actually heard of a virtual suitor before this weekend like yeah only because you knew me right so
like it's it's a growing niche because smaller and smaller organizations do need security and they need that strategic advisement we are purely strategic advisement we do not do any hands-on work if you want somebody to come in and do tacky-tappy stuff i either tell you i look at your job description and tell you yeah that looks like a good job description i'll interview top three candidates or i say you know my client over here is using this msp or this mssp whatever this consulting group i'll make an introduction but then i step out because i don't do that i'm purely advisory before i became a vcso though i spent a lot of time in silicon valley by attack
i mostly spent my time doing large scale content management systems help centers knowledge bases that sort of thing so if you go to support.netgear.com or health.netflix.com those were my babies back in 2010 2012. um from what i can tell netflix actually hasn't changed it so i guess i did a good job they got the money to spend uh and and for support websites it's really easy to prove roi um so it was great for me to say hey if you spend 140 000 setting this piece up or 240 000 whatever it cost i can save you x amount of money in call center operations so that is a direct here's the money you spend here's the
money i'm going to save you let's do it much easier kind of sell especially at scale that whole process is called knowledge strategy and that knowledge strategy boils down to people processes and technology you hear that a lot in cyber security because cyber security is a knowledge industry so i spent my time at netgear netflix i did a stint at facebook consulting to them and then i took a little six-week contract with a tiny company called fireeye back in 2013 and five years later when i quit i was like you know i didn't like the company so much but this industry is amazing so um so here i am i actually started out on their ip operations side
i hopped over to their support operations side because again i'm really good at metrics right and uh one day their community person came to me and said hey i can't find any product documentation for the ipmi product and i'm like you didn't even google that because ipm is a hardware studio bro it's not are you okay what's going on out there in those communities what's what questions are getting answered or asked and it turned out a lot of random questions were getting asked right security covers a lot of areas sometimes it's networking sometimes it's hardware sometimes it's product um but the community guy was neither technical or interested in security so we kind of pissed off everyone in the
company and support engineers sustaining engineers and they stopped answering customer questions so i spent my last three years at fit where was i fireeye um managing the communities and helping dozens and you can say hundreds of security teams solve problems so what do you do like not many companies are forward thinking enough to have that involvement in a community um so there was nowhere else for me to go it was hard for me to move around inside the company because nobody wanted to be the person that poached karluda out of the communities everyone felt like that would be a bad move so i was having a hard time getting a job inside the company um and i really
just didn't like my boss so i took off i started my own company started doing consulting was doing virtual cto work ended up fell into virtual seats at work so that's kind of the everything you need to know about how carluda got into cyber security and i give you that not just for contacts but because if you're early in your career i want you to understand that you can come to bc so or cesa work any different path there are a lot of paths in cyber security if you're a hiring manager in this room i want you to understand i'm a college dropout i dropped out of auburn university um i was a marine biology major uh took me 13
years to finally graduate from nc state i did community college in there at the same time eventually went back for my master's at columbia university the carlotta who graduated from auburn university and the carolina who graduated from columbia same amount of talent and skill i was just a lot more expensive on the other side so um i am a big proponent of not requiring certs not requiring degrees and i will die on that hill uh the other thing that i do um i am on the board of directors for the diana initiative which is an inclusivity and cyber security group we meet during that black cat def con come see us and i do a lot of [ __ ] posting on
twitter my meme game has gotten a lot better since i know this mick guy and you can also find me on linkedin where i actually post useful information for smaller mid-sized businesses so come on all right so that that gave you a lot of context i gotta give you a lot more context than you what you need um okay so this is more context part of the reason that i created this particular talk is because there are 5.6 million small businesses in the united states alone that's sub 500 employees um the majority of those have less than 100 employees they all need to get secure but we always hear from those vendors and the enterprises for those big scale
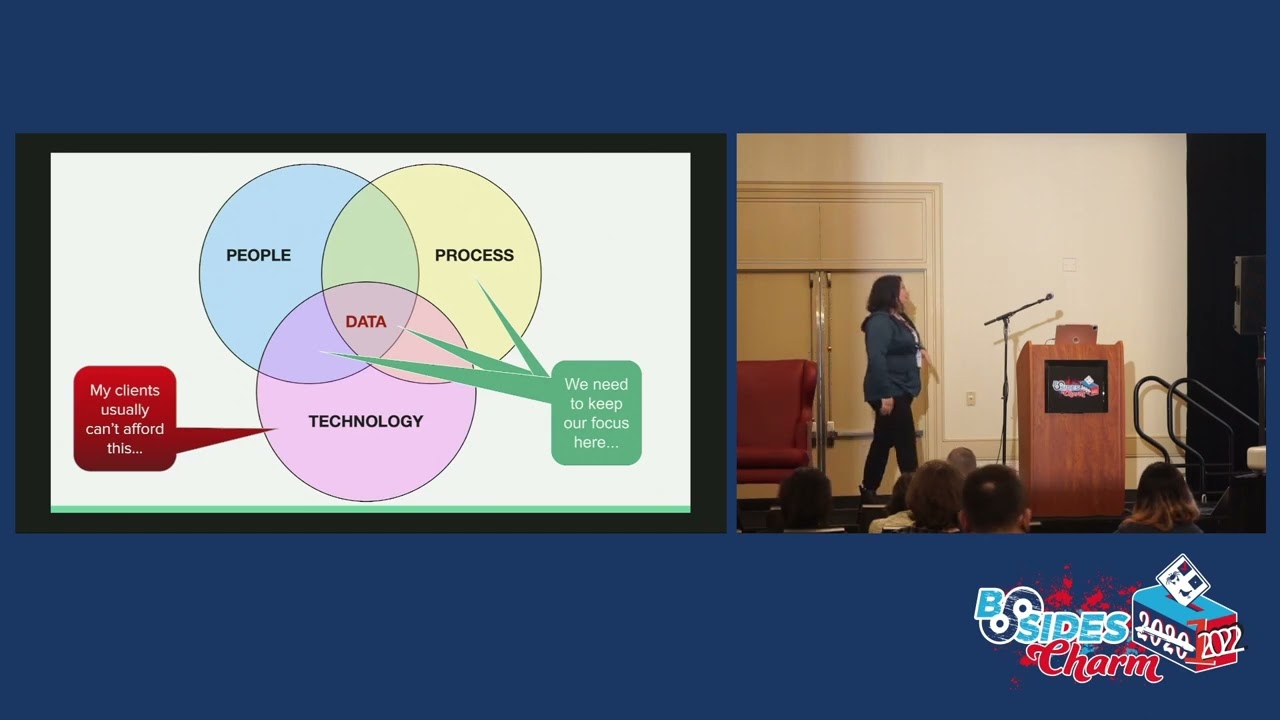
solutions where people are throwing money at the problem those clients that i'm serving i am their security budget that's it like i'm gonna have to justify every cost that i ask of them unless they are very well very well funded um and it's not a bad thing i'm not going to knock the vendors and the enterprises but you know there's only 500 fortune 500 companies how applicable is their model to yours if your sub 500 people probably not at all which brings us back to this knowledge strategy people process technology my clients can't afford that bottom line if you're in this room you are probably very familiar with that bottom line so we're not going to talk about that
bottom line we're going to focus on people processes and that data or if you're in a hospital situation the lives that you're trying to protect so if you're looking for a technical visual talk there's your time to escape um yes so i'm trying to decide how much kind of background i don't want this to be a sales pitch for my services but i think understanding what i do for small companies is helpful for people basically when you engage me you get me you get a cyber security analyst we do a gap analysis you are here i need you to be here for some basic level of cyber security all of our cyber security programs are
meant to be feed into compliance programs because we all know compliance does not equal security so we are very much about security first even if you want if you're coming to us saying i want to talk to your compliance i'm like right that's great we're going to get you secure and along the way we're going to get you compliant um we do a lot of stuff we look at your aws configurations we do all of that stuff so for our purposes though just from that people process technology perspective i want to focus on the people lens first there are a lot of concepts here um you are not your average customer if you are in cyber security you are
automatically not anything like the people you serve whether they're internal customers or external customers and i cannot stress this enough your job is to make them secure their job is to produce something you've got to find a way to set your expectations realistically like it's great if i could people to not teach people to not click on links awesome right they are doing what i need them to do i can't expect too much more a little more but it's important that we recognize that our customers don't think like us is very different you cannot succeed in cyber security with securing an organization if others in your organization are not invested in your success so you have to
be empathetic if you are thinking about being some kind of bcso role you have to be approachable you know as mick was talking earlier in his keynote he's like oh russia's gonna get you yeah i can't he's right you can't do that he's talking to 20 year olds i'm talking to business folks but i've got to make it seem like i really care about what they're doing and that i want to hear them and that's really important i you know there's we dandy around you know the average season 10 years like two and a half years and i think that burnout comes because they're approaching it from the security perspective and they're banging their head on this wall over and over again
and they're not stepping back and thinking this isn't working to try something else and that something else you try is shutting up listening for a little while giving more context on why this is a relay race i need you to take the baton and run with it hand me the baton and i'll run with it when you give people contacts they are more interested in helping you and my last mantra when it comes to people any friction that you create to a process is immediately an obstacle and they will do everything they can to work around that right so multi-factor authentication let's turn that on that's great how many people have been in an i.t
order in a small word i've seen this several times you turn on multi-factor authentication and everybody just enrages turn it on you did not communicate effectively why you're turning this on when you're turning it on why it's important to them why this will in the long run help them do their job better because then i can just bug out you don't have to call id as much you can just you know do this um any time you are altering somebody else's process you are potentially creating friction and that becomes an obstacle to be very aware about that that's where change management becomes really important so as we hear in doctor strange it's not about you and it's not about security it is
about making the people in your organization understand why they need to do what you're asking why i'm asking you not to click on links marketing why i'm asking you to turn multi-factor authentication on in linkedin and facebook i'm going to give you a great example a couple of months ago went through a client's marketing team made sure all of their social media platforms had multi-factor authentication turned on and of course somebody can turn that off you know you can only confirm once once a quarter that it's on um an attacker took over their facebook ads account and while that attack facebook was on it they they shut that down within 12 hours they cleared out all the bad guys that's
great but they didn't turn the account back over to my client for two i think eight days like the attackers got kicked out within 12 hours they're supposed to turn the account over within 24 hours in that eight days my client is losing because they are not running facebook ads two hundred thousand dollars a day right for a small business that's a lot of money scale that up right this is supply chain that you don't think about sometimes um advertising who would think that that's going to be a million-dollar head if i can't run facebook ads 1.4 million so think about that and as it turned out somebody in marketing went back and forth out of
multi-factor authentication and we were minus two marketing people that following week so um it really is about understanding and empathizing with your audience and and we're gonna get to stick with me here this is i'm laying the groundwork for where we get to the really good stuff you need to understand what business people care about because they're there to run a business as everyone points out security is a cost center until you can tie security to sales which i've done this with clients oh how many how many hundred thousand dollar deals are you losing because you're not stock two compliant oh why don't you put that in the crm now you have data awesome now you're
tying your cost center to actually generating revenue do a little things like this and it does help the business understand how making your job easier makes it easier to sell things so your executives care about operational costs these are costs the business know and can plan for um and risk and that is anything that's going to put pressure on the business that's going to spur spending above those known costs like if i know my cost that's great where are the costs that i don't know are coming from and if you can tie your stuff to any of those risks now you can actually has charlene had with her modeling if you didn't go next door
if you can put a dollar value to risk here's how much how likely a risk is how much it will cost you if that happens here's how much if we spend we spend 30 thousand dollars and can prevent 250 000 an unexpected spend that's really valuable to a ceo and cfo most of my clients i'm dealing with the cfo or the cto they don't have a cio they probably don't even have an icy person but about half of my clients the cfos sit in our weekly meetings because they consider this risk management and they feel it's very important so if you can talk about risk in terms of money you can really get a cfo on your side
and that's the person you want on the side because they control the money your internal customers what they care about is optimizing their work they want maximum return for minimal effort we all want to work smarter harder if you're making it harder for them to work smarter they're going to ignore you they want recognition shaming does not work it just doesn't stop doing it um one of the most effective things i've seen is small in a small company i don't know how this would scale but in a small company in the it channel every time somebody said hey i think this is a fish to the it team somebody would grab a screenshot post it into the it general
or the employee channel and say hey thanks so so you're 100 right this is a phishing email appreciate you catching that right so now they've faked someone publicly they've educated everyone else on the fact that hey this is a fake email don't click on this link please right and it generates a lot of goodwill you're also now making it awesome it gets a little competitive you're the first one to send that thing to the it group yeah and then if you throw in a couple of 25 amazon gift cards using gift cards that's actually a very effective security awareness training program i kid you not it is one of the most effective ones that i've seen
um but that all ties into success they need to know that you care that they are good at what they do and that you are enabling it that's a hard one to do that's a lot of social engineering i poured a lot of whiskey in my day like i always ran in my in-person backpack when i worked in an office i always ran the weekly whiskey for because it's like oh hey you've done really great this week come buy the weekly whiskey for i'll give you a shot of mcallen 18. right like i'll i'll give you something really good but it's really important that people feel like you're not holding them back in that success that's where you know that
whole department of no becomes a problem um it's easier to get people to feel like it's easier to get them invested in your success as a security person or as a citizen if they feel like you are invested in their success right it's just little tiny bits of psychology
okay so people process technology ignoring technology we've just done people process can be a little bit boring so i'm warning you um yeah run run um get the basics done like there's no way around that doesn't matter how much [ __ ] security building you have if you don't have your basics done you are not doing it right period um hardware digital asset inventories data flow architecture diagrams policies plans patch change vulnerability management cyber insurance cyber insurance is one of those things where i end up feeling really geeky because i actually like reading through insurance policies but it's also the nice thing about having a look across 30 different clients is that now when i talk to one
of my clients i'm like who is your broker because you're freaking cyber insurance you're getting twice what my other clients are getting for half the money like they're they're paying twenty thousand dollars a year for one million dollar cyber insurance sorry three million dollar cyber insurance policy with a ten thousand dollar retention and the retention is kind of like it's acceptable but it's per incident so if you have four incidents you're paying 10 000. you're not paying 10 000 for the year right um most of my clients are paying 40 000 for 3 million and 100 000 retention so if you have a 900 you know 99 000 sorry 99 000 incident you're paying for that entire incident and if
you get another one that's a hundred and two thousand dollars you're paying for the first hundred thousand and your insurance is giving you two grand so you've just paid two hundred thousand dollars for events right this is like i said it's really pretty but one of my favorite things um there is i realized that i came from cyber security at a different angle for my boss because i'm reading through this other insurance policy and i see that the phone number for the claims ends in one three three seven and they start laughing like oh one three three seven that's funny and my boss is like lie like it's league it's it's leaked so you don't know we'd speak i am in the wrong
place no yeah i'm in the right place um policies and plans seem like a real time save they are i won't lie it's pain in the ass to do them you write them for what you're doing today even if you're not doing stock compliance stock compliance will really enforce this write policies for what's going on now don't have some aspirational we should be doing it this way in your policy if it's not you've got it right to what you're doing it takes everything you want simpler um digital asset inventories hardware asset inventories are the easy part digital asset inventories are easier now that people are in the cloud you can just like hit aws and
work its magic data flow and architectural diagrams legit are the hardest thing i have to do with clients because they want you to do it for it for them and it's like i don't know you're a product man i don't know your systems i know the security you know your stuff that's how this works i need you to write this stuff down um i am amazed at how few people can legitimately do a data flow diagram it's like box starts here data goes from here to there it doesn't seem like it's that hard but i don't think i have very many clients that can do it without me actually talking them through the process so if you can do those diagrams
you've got a great potential to be a cso i'm just letting you know uh the biggest thing that i've done is a security health model and i was calling the security material at one point it's not accurate i don't like the word maturity um because it it indicates that we're growing and we get better or more sophisticated or more aged at least you know maturity has this connotation that you move in one one direction right so if you put the cnnc or the nist maternity model in front of a business person they have no idea what that means that is completely meaningless they're great maturity models for a security practitioner because we have the education that we can look at the model
and that's meaningful for us for ceo or cfo it is not meaningful stop using it don't throw that stuff stop copying security to non-security people this model is basically here's what's healthy here's what's not healthy most of my clients are starting somewhere between that left and middle space and so i've got this um piecemeal compliance driven risk base really it's ad hoc grassroots someone somewhere in an organization is trying to do security but they're kind of that one person who's doing it maybe they're not doing it well but they're they're putting that effort in there that's great i want to make that person feel really good that compliance driven can also be team driven once you've
gotten to a point where you've got one person focused and dedicated to security for my clients that person is me um and they're only getting me for three hours a week so how focused is it really um but once there is some kind of structure or program around that security you're moving towards that middle section that right hand section that's advanced that's where you're getting security when you're getting your sims and your you know whatever you're getting more advanced here i want my people to be in that middle column if we put this on a one to five scale that middle column's a three three means that it's documented repeatable and scalable that's what i need for my clients if i
can get them to that point that is very successful and the way that that you measure a security program before you have a security program is that you take this you put it on one to five scale and you literally ask questions about that i don't have that in the stack because it's a long kind of assessment i do have it in my github it is free it's under creative commons so if you are in a smaller organization or you have a friend who's in a smaller organization or you're just trying to talk about security the non-security people you're more than welcome to take that uh github.com show me the money uh no dollar sign but
literally really important that that and and in my contracts part of the reason the cfo or cta shows up after these and our contracts say the executive sponsor will be involved in this product in process right because we signed three-year contracts we want you to understand security is a process it's an ongoing need it is not a project it is not one and done um the biggest thing for my clients is just being able to say to their board here's where we are here is where we're moving oh here's where we were last quarter here is where we are now and if they can do that with little check marks on this chart that's fine whatever it takes to
start communicating security at a very simple level but meaningful like this is a lot of verbiage but it's helpful i've never seen a c-suite look at this and their eyes glaze over they look at this and go oh i see the green side that's where i really spend money right now i guess that is where you really spend money because that's where the real tooling comes in but it's also a lot less scary when i tell a client who's only got 50 employees i just need you to be yellow i just need you to be a three i just need you to write stuff down make it repeatable and make sure that it's going to scale as you grow because
a lot of my clients fractional has 30-ish clients i have eight that i serve most of mine are e-commerce or sas we have things like a private college we've got a medical device company i have a software uh a security vendor a security startup as a client why would a security startup need a fractional cso because they're 50 people and their money is spent on creating product but they also understand if we don't have a program we're not going to sell to the bigger clients right so we set up their program we're going to help them hire their first eso send them on their way it's a lot less scary for me to say to a
cfo i need you to be a three i don't need you to be a five i need you to be a three i need the security company to be a five because they're a security company i need the person who makes a physical security product for airports i need them to be a for me i need my i need my auction website to be at war but most clients i just need you to be a three you just got to take the fear out of security you've got to make it accessible once you take out the fear and you make it accessible you get them on board now once you have leadership on board it's a whole lot easier there's
there's a certain amount of trickle down and there's a certain amount of grassroots pushing up if you can get kind of both ends and work towards the middle you will be very similar
which brings me to the lens that isn't in our people process technology piece is the money right how do i get people to pay for security when i can't communicate security to them well now you can communicate security to them but more importantly in that same github i have a bunch of really simple excel sheets that you can download and start actually conversations and the first one is a really simple efficiency return on investment so if i'm saying i want to spend 30 000 on a piece of security tooling what is it what is it really getting us giving us more secure okay it's giving us back 15 hours a week you know of eight
employees 15 minutes a day of 80 employees it's giving us something and that's theoretical product productivity is a squishy number i've never had a cfo come back and go i just don't believe this i've had them adjust the numbers because to them time is money and they will make these numbers work in a way that's meaningful for them so if you can say i'm going to save people money at a time you can say i can save people or i can save you company money this is a really simple way this only works in an additive sense like if i'm trying to layer something in take a manual process and take that into something with digital more automated
this is a calculator that works really well if you're trying to justify hiring you can still do it with this calculator but if you've gotten if you're trying to do a riff this is not the calculator that you should be using so um it's really simplistic but it is valuable because again it starts that conversation with the cfo it says to the cfo i am trying to speak your language help me do that and they will but more valuable than that are risk and recovery estimates this is extremely simple much simpler than what charlene was saying but for 50 100 200 person organization being able to say hey if my internal applications are not available
this is what it costs us in productivity per hour per minute whatever here is our net productivity lost to a 60 minute 60 minute instant 3 250 bucks doesn't sound like a lot especially if we're talking about 100 000 person company but to a 50 non-profit that's a lot of money right um incident response costs i think adrian sinabria had originally posted his version of just what an incident cost your security team you can actually map that not just to that security team but to the entire organization or the affected organization and then your recovery costs your recovery costs become really important again because of those operating costs if i know my operating costs my risk or
the costs that put pressure on that and make me spend money i wasn't planning to spend your recovery cost if you know you have a system that needs to be changed maybe it's legacy software this is what the system is costing us here is the risk of you know it getting reached here's what it will cost us to move that system somewhere else now i can either plan for that cost for next year right this is how you solve some of that technical debt when they're small and it's easy to solve um here's what it's going to cost if we do it under pressure of an incident right so let's let's give people those tools uh
it also just sets that expectation on there is a cost to not doing security if you can get your cfo to buy into there is a cost associated to not doing security and you can say and if we do that here's what it's going to cost you can start building that security cost into your budget does that is that reasonable does that sound reasonable i've had one cso push back on this and go attackers don't care about your budget you're gonna burn out because your ceo cares about your budget a lot and yeah your attackers don't care about a budget or your roadmap or anything but if you're going to your ceo and saying well the attackers are going to do this
i need a hundred thousand dollars your ceo is probably you're probably frustrated because they're saying no if you can put some numbers to that this is what it's going to cost here as harleen was saying here's the likelihood of an attack here's what it's going to cost you if it happens here's what it's going to cost you to prevent it you get a lot easier volume that conversation becomes much more collaborative and much less combative right if you're a sufficiently small company if you're a 1500 company one of the things that sometimes there's still a hurdle they'll look at these and they're like this is helpful we'll plan it for next year one of the conversations i end up having
with people is how often do you change your laptops and most organizations now accept that technology moves fast enough that i need to give my internal employees a new laptop every three years because the technology has changed or it's just worn out so every three years we just built that into our operating cost and that's the important part operating costs is expected right if we just build that into our operating costs we're fine okay well are you a mac shop are you spending fifteen hundred dollars every three years how about we spend five hundred dollars per person per year on your most basic security tools that makes them stop because it's like i've just admitted that technology
changes and that i'm willing to do that are you willing to spend as much money as a laptop every three years to see you through your small organization that's a much basic much more basic and simpler conversation to have if you're not especially if they don't have a cfo if you're working with a client that's small enough that your coo is not from a cfo kind of background they don't have the economic background or the finance background [Music] you might have to change tactics there that conversation becomes very successful because once you can get them to say all right you're a small organization you're gonna spend 500 a year let's talk about what we can
get you for that now you've grown a little bit now you've gotten a little more you know more investors maybe um maybe you've got a little more revenue being reliably generated let's talk about upping upping that from my experience and this is purely anecdotal if you're a hundred person company you should be spending a thousand dollars per person per year on security as you get bigger that number drops because there's an economy of scale that's why enterprises can afford to do their own stuff but if you're a very small company i love to see spend a thousand dollars ahead just secure your organization and build that into your operating cost model if i can get you to
spend 500 ahead that's still a win um if you're trying to talk me down to 250 ahead maybe i don't need to be working for you anymore because there's not much you can do there yeah there's a lot of things that you can talk about here's how we're gonna spend our time for the first few months securing the pieces that you have now but once you've gotten the basics locked down now you do have to have those money conversations on no really i do need i do need i do need maybe you need for a small organization something of an article for expel security as a service knock center sock as a service that kind of thing
there's a lot of things that you can do by playing with numbers um oh my timer just okay um we're doing pretty good so are there any questions at this point has anyone had an experience where they're trying to set up a program do you want me to go more on the operational side of the health model are we good i know this is a lot of like really high level really boring information but i know this is interesting you like yeah yeah it's really simple sure have you seen one of those things i saw it one time that i just kind of lost that link so i never saw it again
um usually i haven't seen it as a how do i pet it uh free to the world here's what you do x y and z i'm sure there are guides out there usually an msp is trying to bake all of that in as part of their service offering so it becomes a sales pitch that's how i usually see it uh most of the clients yeah and it's interesting because we're not cheap i'll be really trying for 100 person company you're spending 80 to 100 000 for my company to help guide you through security can you get a vc so a solo practitioner cheaper sure they're 400 an hour um but if you only need five hours a
month that's great if you're willing to do the hands-on work and i think there are a lot of a lot of the ctos that i that i work with are willing to do the hands-on work they just don't know where to start or they don't have time to sift through all the information and figure out what's actually useful for them that's really what they're coming to us for because we don't like i said we're purely strategic or purely advisory we don't do any hands-on work and what they're trying to do is save that vp of engineering with that cto and that cm is time and learning security because they know that it's just gonna happen a lot faster
so there are lots of things and even we have blogs we write blogs every week on here's what you do small business here you know you want to understand the difference between sock 2 compliance vendors here's a white paper if you want to understand what's better gmail or what's better for security gmail or o365 and it's not microsoft gee um wonder why um yeah we have a lot of blogs we do put a lot of that information out there a lot of consulting agencies do because it's part of our brand but the amount of time that it takes someone to read through all of that and decide what's relevant to them it's cheaper for them to come to us or
somebody else right so does that does that answer the question yeah okay um but speaking of such things i do have some tools and suggestions actually if you i will come back to this if you download this there's actually several several uh tabs that have different loss recovery estimates depending on like if you're looking at infrastructure or if you are a service provider with a subscription model great but the last two tabs on the on this worksheet actually have links to useful information number one like the fbi and sofos reports yearly reports that kind of thing and summarize some of the kind of the numbers that i look at on a regular basis it also has links to a lot of open
source software um i'm a big fan of security onion i know those guys they worked with them at mandiak they're pretty awesome um security onions free it's not a sim but it's about as close as you're going to get to assume for free if you've got more time then you have money open source is a really good option i think the problem is that most teams don't they're so time constrained that they have to spend money right if you're in an organization that has enough more embodies like a university you see a lot more open source use if you're a developer or you have a large organization that has warm bodies it's cheaper for them to
take open source stuff and build out their own stuff that's great if you are a small or mid-sized company that's usually not an option unless you just have someone who's really passionate about it willing to do it outside of their regular work because at the end of the day the time that they spend doing this is not time they're spending on producing your product which is how you generate revenue and when you're sub 100 people that becomes super focused that is your focus you're trying to generate the revenue so that you can keep people
so there are lots of things out there fire eye well it's not fire anymore it's trellis i should go and check and see if they still have that they used to have a lot of freeware that was originally developed by mandiants before we purchased the indians um things like redline and that sort of thing really great resources free i don't know if they're maintaining it anymore i don't know if mandiant's taken that back i'll take a look nobody4.com has a list of free i.t security code tools i will admit i am not a no before training platform fan i don't like it but they do have some great links on there um osm os query from facebook i think um
there's a lot of stuff out there snipe it app that's a really good basic you know inventory system if you're just trying to get something so that you're out of a spreadsheet that's a good way of doing it so uh how much time have we got we've got a few minutes yeah all right i wrapped up six minutes early um if you want give me a second i can actually show you more of that spreadsheet or we just talk i can tell you about interesting experiences on the small business front not what i meant to do what would be useful for you do you guys need to run hit the bathroom before the keynote are
we done do you have questions have i answered all of the questions already some of the experience some experiences okay um i just i told you about my customer who was losing them uh two hundred thousand dollars a day because facebook ads weren't running um i have had some interest yeah i mean there's some really great people out there trying to do really great stuff but then you realize they're really built on uh gum and shoestrings right so had a customer last week come to me and say hey you know we're we need to migrate our aws accounts from uh somebody's you know from an email address to to another one do we need to use our
main domain or should we use some other domain so because if our domain gets compromised you know then they have access to our ews am i overthinking this and of course my first question is why are you moving your aws accounts from one account you know email address to another and it's because when they set those up uh they were set up on somebody's personal email address which right this was a friday afternoon at 4 30 questions so you know it's like well you know and when you're doing your gap assessment you're here i need you to be here that's not a question you asked where is your aws account owned who owns that what's the root account email
address there that's not something you think to ask yeah so they're really entertaining um i have had i i think prospect calls was fun for me because i actually got a talking to a prospective client and they had had an incident they called a forensics team they got everything cleaned up they were very confident that the people were out that they felt like it's clear we need a cyber security program and you cannot help you you know can you help us with that i'm like that's great how did they get into your website oh well they compromised uh uh what was it uh code fusion 2012 server that's where i've been in an ec2 instance i was decommissioning code
fusion 2010 like i didn't know there was even i laughed out loud i felt a little bad about it but but the guy's like yeah you can laugh i've only been here three months i'm the new cpa this is one of the things i need to clean up he did become a client and they were very entertaining my clients were using technology in ways i wasn't expecting um i had it when i first joined fractional css on my first client they're like it's a marketing services firm and i'm like oh that's going to be a nice easy client they are the most complicated client i have they have the most complex environment got 250 domains
they've got 60 aws accounts they have things in aws they have things in gcp we are not charging them frank they are really doing stuff that i was not expecting because what they're doing is they're basically doing online advertising for universities but they so they've got that kind of marketing model but where they're really making their money now is that they go okay if this student comes to us you know we're not going to charge you for the click we're going to take a percentage of their tuition right the entire time that they're enrolled but we're going to make it beneficial to the student they actually have basically a call center that is a whiteboard call center for any
of the students that are enrolled through having come through their marketing programs so if that student has a problem with getting their financial aid this company will actually call the bursar's office and go hey i want my money so we gotta get this student sorted out right this is not how i was expecting a marketing service services firm to be running their company i have a company that runs um online auctions for a lot of at auctions so like soft abuse is the one that everyone knows it's not necessarily their client but you know when soccer these cuisines whatever has an in-person live bidding option and then you'll hear so and so from online we have a bid from the online
auction this is one of the like four companies in the world that do that um they have taken with the pandemic they've taken their physical locations and now you can actually bring the artwork to them they will scan it and they will not only scan it to produce the online image for the auctions they will mention nfp as a part of the providence so if you have the art and you have the nft you own the art if you have the art but you don't have the nft maybe the art is stolen and that is like the first time i've actually heard of nft is used in a useful way but it's time confidence of a physical
object right um i have clients yeah like i said i've got a security client they are doing interesting things but if i talk about it and figure out who they are um what else have i got i've got a client that does you know if you go to a dealership website you can like spin the car on the dealership website like the 360 models of the car they do that that is the only thing they do for dealership websites that's their whole and they're like 60 70 people right that's that's great for them they're expanding in other areas but it wasn't they're actually they bought and just bought a company um out of eastern europe
who is a neighbor somewhere near ukraine so talking as i'm doing the the secure lifecycle development uh secure life yeah secure software life cycle assessment uh and i'm talking to this this team in the country of georgia just as the ukraine is starting and so like the first 10 minutes of our conversation are always you know the first actually the first 10 minutes of the first conversation is like how did you get into this business oh well in 2014 i was uh tracking russian misinformation campaigns that guy's cool talk to you nothing to do with our product but he's really cool to talk to you so getting to talk to somebody like that i was not expecting to like my
clients and enjoy actually talking about clients as much as i do yeah you know you don't get to pick your clients like it's whoever signs the contract and they're like you're up next you know so when you get that it it has really surprised and delighted me how lucky i've been with the clients that i've gotten they're all very cool they're doing something neat sometimes they're doing something they're doing interesting things with technology to do things that you weren't expecting like the client itself hair care products really not interesting to me as you can tell my hair's a mess i don't care about the hair care products but what you're doing to sell the hair care products on
their ecommerce site that's interesting e-commerce is a really different bag too from a security model because you know your end client your your consumer doesn't care if you're sought too compliant they really only kind of care if you're secure at all and that you know maybe their credit cards will get popped but if that happens that always happens no big deal we've kind of we've become consumers are important to that so they have actually a lower bar so if you're an e-commerce site coming to me actually wanting to do security i actually had to kind of go good job your cto actually seems to care um but you know when you you have to treat them
a little bit differently so we ran some fans and said hey you've got some open s3 buckets you know they should be public you know and they looked down no no i said no oh you don't care okay well here's a risk register here's what the problem is here's what we recommend um sign that you accept that risk i want you to put your name on that cto and then all of a sudden he cared like when i made him when i wanted him to sign off on this suddenly it's like give me two days to research so it's it's very interesting kind of the different personalities you get like i said i'm dealing with ctas cfos vps
the cfos are very much about the risk they get it they're on top of that risk the technology doesn't necessarily make sense to them but if you again if you can learn to talk and risk you can get a lot more done with securing a small organization so i think those are the most entertaining discussions i can have without ruining client confidentiality any other uh we've got five minutes left and i'm happy to call it there for no other questions good all right go get water before the keynote [Applause]





