Rogue One: A Wifi Story

Show transcript [en]
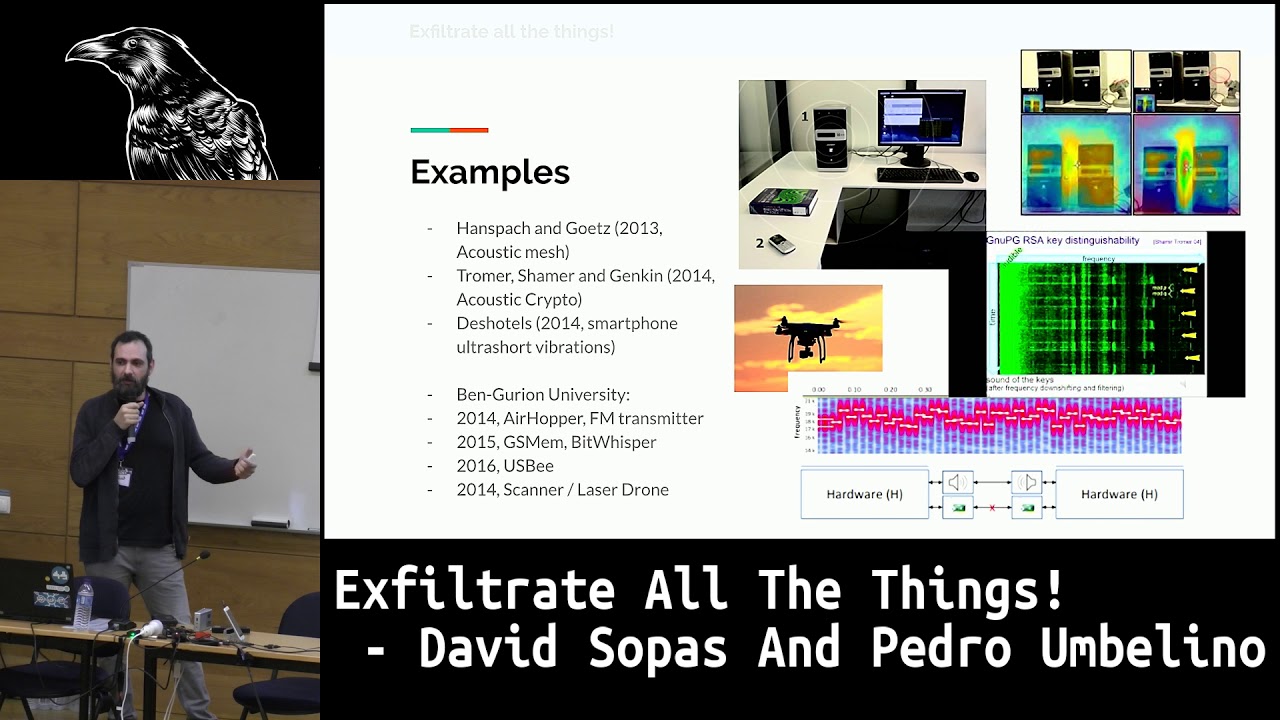
okay hello everybody my name is Ricardo consults and welcome to the road one a Wi-Fi story so this talk is going to be about a project that I developed during my master thesis at the beginning it was to detect rogue access points but then it expanded to a way to detect also Wi-Fi attacks so basically what we will look over this talk its contextualize the background that is needed to understand the tool that was developed and then we'll look to rogue access points what they are and Wi-Fi attacks that are sometimes needed and used together with rogue access points and the last part of this talk we will see the tool in action actually I record
some demos I don't trust doing some some live Wi-Fi attacks here so we also see a guide through over the detection process of this tool so the things that that drove me to embrace this project and to develop this tool was basically this the eye expansion and our our requirements were always being connected and everywhere so in order to this be possible we need to have these access points that will give us the internet that we want and so these need to be always connected and the easiness of performance and Wi-Fi text kind of drove me to try to create a tool that helps to detect these scenarios it's not the protection to its actual to detect this
has different things so sorry so the thing here is among all of these access points how can how can we trust that we are connecting to a trusted source and if you were for example a small company oh you can in a cost-effective way try to guarantee the wireless security and yeah basically it was all this kind of paranoia that made me create this detection tool so in order to start and understand the eristic used by this tool and how it is done the process of detection we need to understand a few a few concepts so basically when we talk about wireless we are talking about $82 level which are a set of rules on how to implement and
use the wireless networks inside this 802 dot 11 there's different operation modes we have the a dock where it's like peer-to-peer communication and we have this infrastructure mode which basically it's one that we care about it will be our environment and it's where the mobile units communicates through the access points that serve as a bridge to other networks and then we have these the the basic service set which is our environment which is the place where the things will happen basically it's when an access point is connect to the wire network that will receive the actual internet that will be send it to the to the stations and this wireless stations our laptops our smartphones and things
like that that are all together in this environment which is the BSS so we have the the environment ready so now you need to know all these entities all these environments communicate between each other so they communicate by sending some frame packets and these packets we have three different types the management ones the control and the data and most important and the ones that we will use in order to create the tensions are the management frames that are used to power management and emission controls and they will allow some devices to initiate and maintain communications they will send information like all of these subtypes of frames which is like the associations reassociation requests the broth the
beacons and other important subtypes that are going to take place between all these communication between these entities and for us we go we need to go deeper into the probe and the beacon frames so the beacon frames we have the the access points we have the clients and they need to talk between each other in order to understand them so the first thing comes from the beacon frame that needs to announce itself and say hey I hear and I have all these capabilities and this capabilities will be something like the name of the access point which is the service set identifier will be the basic service set identifier that it's like the the MAC address of the of the access point which
is unique and I didn't if you identified that access point and all the other other all the other subframe types like for example the time stamp that will be used to synchronize all the stations that are connected in that environment the basic service set so these beacon frames work in analysis the the access points and you as a client will listen to that beacon frame so you will do the things in the passive mode but if you want to be more efficient you can probe for that information so there's where the probe Procrit appropriate quests the probe frames will come into place so probe request is basically asking for the access point asking for the access point
information you do this probe request and then you will receive the response that will contain the other information that we saw previously in the beacon frame like the name the MAC address and stuff like that so having all these information together we can now see the process of authentication to an open access point so you will have the first case where the Authenticator which is the access point will announce itself by sending the beacon frame and then you can have in some places you asking for that information so basically sending the the probe request and then you will have the information back the probe responds and then will take place the authentication request the response and finally the
Association requests this is the representation for an open authentication if you will have an encrypted authentication the next step would be a four-way handshake so now we came to a point where we know what is an access point we know what the the clients the applicants are so basically your mobile phone your laptop all these entities and then comes to the point of what is a rogue access point so basically a road access point is an unauthorized or a false access point which is created with malicious intentions and sometimes it's used to support some Wi-Fi attacks LED strobe access points the most the most known one it's the evil twin type but there's different other types so for
example the unauthorized access point it's very much the case where for example a naive user or an attacker deploy an actual physical access point into a wireless network it will be there it will be an unauthorized access point and it is a rogue one so the next one is the improperly configure inside this type we can have for example access points that are configured with weak encryption like for example the web and they are vulnerable to some attacks and then they are again also a type of probe access point in space improperly inferior ones the compromised is the case that affects pre shared key WPA networks which in this case it happens when your pre shared key
is disclosed Simo so when attacker knows about this pre shared key it means that your access point is compromised and it is a type of rogue access point so the last one the evil twin which is the the most mainstream one it's like a clone of the exact believing at this point so in this case the an attacker will pretty much blown all the other identifiers that we saw in the beacon frame and it will create an exact clone which is the evil twin this one can exist in two types coexistence where pretty much exist side-by-side the authorized one and the replacement where pretty much you will be off the we will close the connections
to the authorized one and only exist your access point so these are the types Robles points so what what what you can do if you create an access point so basically you can perform an individual tax and to this you can say to me yeah I use a VPN I'm safe okay that's fine that's the way to go but there are other people that don't use VPNs and there is also the problem that if rogue access point is deployed in your network they can reach other nodes in the network and they can target them and perform another type of attacks like for example data exfiltration or maybe flood the network with some random data so at the next
point we have these Wi-Fi attacks this Wi-Fi text for example the rogue access point with strong a signal it's used in case like I said for example to evil to me where for example you have the real access point and the rogue access point and in this case by default be able to got 11 networks they will give you the connection to the access point that as a strong signal so if you have to choose between these two access points you'll pick the one with a strong signal but by default if you are connected to a rogue access point you will not be disconnected because you have a stable connection so you will not switch
immediately to the strong signal so what happens here basically the attackers use the second point which is the V authentication attacks they will send some specific way frames that sense this V of medication information and will make you disconnect from the from the real axis point and since you are now in this condition of choosing the access point you will switch to the one with the stronger signal and you will be inside the road one so the next one the route next the Wi-Fi attack is the Karma attacks so before I explain the car attacks I just want to give you a little context that these are not all of the Wi-Fi attacks that are available are the ones
that are in the scope of the detection of these two so yeah you might know about other types of Wi-Fi attacks like for example the crack and attacks to web network but they are not mentioned here because they are not in the scope of the detection of this tool so keeping on with the karma attacks so it is the case where he targets devices that actively probe for networks so my device for example can start saying if there's around the network or example a broom and it will also again ask if the network the Wi-Fi events for example is around and what the karma attacks is is basically responding yes I am headroom yes I am Wi-Fi event yes I'm other
network so basically the same device will say that it is different type of devices and this will target is this supplicant devices these these clients that actively probe for Vogue before for access points so then the fourth one the rogue access point with radius server is pretty much similar to do one describes but targets aro 2.11 enterprise networks and to these you can use for the tools for example like post a PD BB he that will create a fake radius server and you can pretty much explore the the victims targeting these networks and the last one is the pmcid attack which is a recent Wi-Fi attack was discovered I think August this year and it targets
again delegate to pre shared key networks and it will allow the attackers to obtain the preciate key that are using that in that particular SSID so it's it kind of give you the same as the the old Wi-Fi attacks where you would target a network the authenticate the client and try to crack the and shake but in this case the thing is that you don't need to actually have clients inside that that network you will just interact with the access point so the attackers will target the reassociation process in order to obtain a master key ID which is free maitus the pmcid and this is derivated from the access point to MAC address the clients like address
the PMT and the PMT name so these ones are are easy known by an attacker the one that it just needs and wants to know is the PM key which is the right from the pre shared key and if you do a dictionary attack you could basically crack the password of that access point the thing here is that maybe some of you already tried them you couldn't break your neighbors Network is that it only affects mostly affects wireless vendors that using roaming technologies so usually our home routers don't have this capability so yeah we kind of safe from this one so we now know about the Wi-Fi attacks that are in the scope of this
tool we know about the types of rogue access points we came to the point where we all look at the tool that was developed so basically this tool the techs different types of rogue access point and some Wi-Fi attacks it is a modular framework it was divided in different modules in order to make it easy to extend it for different things it is stationary one so basically yeah it could be improved but if I started this tool here it will just capture all what's going around in this room so it is limited to the scope and it can be used in Linux systems systems and it can fit all four different users if you are
a home consumer you will just figure with what you know about your network if you are a seasoned min straighter and you have a different network you can input some different some different specifications so basically we have this main tool which is the rogue access point detector and it will load a profile or not you up to you if you place this profile by the way you are saying informations about your network and these informations are in the name of your network your MAC address the amount of access points that you have the the channel where they are configured the the type of the encryption size that you are using the signal the signal strength
of your access point all this information will be stored in a profile that then will be used for a part of the detection process apart from this profile which is an optional one we left underneath a profile for free Wi-Fi networks it actually has just some free Wi-Fi from the Portuguese ISPs the north networks and and Mail networks and try some evil news and eristic that I was quite explained further on in order to give you some some authenticity about these free Wi-Fi so then once the profile is loaded we'll go to the modules where we have these scanners and detectors which are passive ones and we'll have the actuators which will do active approaches so basically the
scanners do the scanning process it does this scanning process with iawn lists from linux systems or it can use this KP framework and this will basically scan what's going around in the in the air and I'm doing this you will face a problem which is the you need to filter the access point because you just if you just keep listening you will have a lot of a lot of the same access point you have a lot of times so we need to do some threshold in order to to just keep once the adult the res access point and don't have a swath of that so basically the scanners will they'll give you all the information about what's going
around in the access point and then we'll place the the detection process detections at the to F the passive ones are the authorized list techniques which will depend from the profile that was configured if you don't configure profile it will be the no knowledge network there's no knowledge detection process that will basically use what it's known in the air and and try to do some no knowledge or it tips over these access points are announced so even if you don't configure the right list you can still have some results but from that we have a black mist technique which will make most of these Wi-Fi attacks happen for some some defaults brands like the pineapple a
piece of interfaces and if this is not immediately saying that this is a rather at this point but it will figure something and say oh it something is going wrong and we we have found an access point that has a brand from alpha cards that's not normal so if I take a look so the next one is the validate free Wi-Fi authenticity like I said not going to explain later the D authentication attacks detection karma attacks detection it works both in passive or active mode and the pmcid attack detection next one we have the actuators which will support the detections that are described in the previous section so this detected these actuators will pretty much do the the active active
process they will exert the access point and will retrieve these amounts of informations like the IP the the ISP information will calculate a trace route for example for a node in the network or for and a website that you know the amount of ops that you need to do to reach it and will also calculate the access point fingerprint actually this uses the N map framework and will do a scan over that node and will give you information about that that access point the last one is the countermeasure mechanism what where you can basically the authentic eight rogue access points so now we'll throw a tune to the heuristics in to detect the first one
they'll try to list attacking it's composed of four detection mechanism the white which one is the most easy one and known by everybody we pretty much see if the the announced SSID the announced name of the network if we have to announce main works with the same name and we have the different bssid which is unique or network we will alert the user about that something wrong of course that it's that this is available but that's why we have on top of that another heuristics the encryption orig eristic will look if the the encryption scheme used by the access point is different forum for the one that it's authorized so if it is different it will alert the user we also
have the multi-channel detection which will see if this slim access point it's an ass in a different channel which is also gives you another mystic about this this thing and the last one is the received signal strength indication eristic which will pretty much else will see if your access point the data point lost is inside of a baseline of the RSSI so in your profile you can figure this baseline because you know about your network and you know the the signal strength that you are of course that this is the air spectrum and we have interference that's why you have this baseline there that you need to fine-tune correctly and if you do this you will be it will not alert you but
will prompt you if you want to connect to that access point so if it's your authorized access point you will successfully authenticate and will do the wrist Xterra explained in the activators and you will see that information and Steve really match your access point if if it really matches that's ok you are good otherwise something is wrong maybe an attacker knows your appreciate key and create an access point similar to yours and you're kind of in trouble or not so so this I have a little video to show the process of detecting of using the auto authorized waste detection process so I hope this can be seen with good quality so basically in order to start the to
detection without right with we need to load this this profile with the flag waspy and this profile is basically what I said you will put the information about your access points and so we just start start the tool with bids and we will start looking what's going on around here it's just showing our access point in lab network because we are using the profile if we are not using a profile we will see a bunch of access point well I'll show you later on and now in this second window I will create an access point that will represent the first case where it is the one that it is a a bssid that is not authorized so I create this
access point using the tool it has a method which is the last H flag which is the ID mode where pretty much you can you can can configure a profile called road access points profile where you have pretty much set the config for your rogue access point this is mainly useful for testing purpose nothing else trust me so I started the world access point and you can see immediately that it's not readable enough but I can I can tell you that it says evil twin unauthorized DSS ID and on top of that you can also see that there's that information about recently created access point so and this is because of this tsf function which is the time synchronization
function that like I said it's the way that in inside the environment to be as DSS they will they will define the they will synchronize all the the entities inside that VSS I so basically since this access point is is created now by an attacker of course that you can use tools that can come you can have some specific time for the tsf but by default i am using the skeptic framework to create the rogue access points it will start by 0 and by 0 it's a recent access point I don't have any other access points in my my lab environment so it will be strange so the next one will go to the profile where we configure the
world at this point and we'll change it to target next next case which the encryption scheme so we changed to the open access point and we will see once we start the access point that will get rigorous the alert in this case these are two alerts the first one saying about the multi-channel thing because apart from you are deploying a rogue access point that is similar to the one that you have your network you are deploying an incorrect Channel so it says that it is a multi-channel access point and also give you the information that the authentic delta-t the encryption is different so this one is open and your is a double pa-choo so and
again it's recently created access point so this gives you some some information that something is going wrong so the the next one will be the received signal strength indication eristic so in this case you will have for example a scenario where the attacker will increase the signal of the road access point and in this case once you start the tool you will be prompted about you will be prompted you want to authenticate to that access point you can see here that yeah actually you can see what I'm telling you that it is say that strange receive signal strength indicator do you want to associate if you if you do okay it will ask you for
the informations about that network the interface that you want to use to authenticate the password of the access point and yeah it will try to associate after this association process if it works correctly it will perform the Mystics that I set internal IP information external ISP evaluation the traceroute actually is calculating it and then it will do the fingerprint with an map so with this since we were connecting to the authorized access point these informations are the correct ones but if we were in the case where we have an access point deployed for example with without encryption you will have different results or if it is one that it's the similar to mine because my
my pressure was leaked maybe it would be somehow difficult or maybe the attack will not be it is we think about it and something here will not be right so about these detections we are clear so the next one is the validate free Wi-Fi authenticity so in this case we notice the pattern that is that happens in in some networks basically the thing is that in the north and male free Wi-Fi is the the enough free Wi-Fi follows a specific pattern in the creation of the of the MAC address so because the this network is a nas from the same access point where you actually have your authorized your own network and since it's from the same
access point the MAC address is the write from it and what happens in the North free Wi-Fi is that the last byte from the bssid will increment one unit and if this happen we will give you some some heuristic that probably this north Wi-Fi it's an authorized one this is just probably because an attacker can think like we did and deploy this authorized network and create the right conditions to treat my tool so this is this is okay but this is a different different step and an extra layer that can give you some confidence that this access point is actually a trusted or not so the same happen for male free Wi-Fi the first byte is incremented to
units and the last five one unit this also happens for for for example it is also considered in the tool for for Wi-Fi advantage and university of war to access point because the the this VSS are these are the right from the ever new one and follow a similar pattern so we use that also to identify it someone is playing around so the demo to see this working it's pretty much we just you just need to run the tool any scales you don't pass any profile the thing that you pass is basically the interface and the scanning mode that you want here I'm using the I double missed and you will see that it will immediately say that are some
probably valid free white flies and if we look at the pattern they are the ones that I described before so yeah it is trying to do the same from this male or male this one failed but you can see over there that it actually found some problem well it's free Wi-Fi then I run the tool with skeptic foot escape Lee prema just to show that it also works with skeptic but the thing here it is a little slower with scape II because you need to do the extra weight channel open you need to code this channel open and because of this the tool becomes a little slower in this situation but you can see that it already detected a
problem with free Wi-Fi network so as for the sport the validate free Wi-Fi so that's it we could do other eristic but it's kind of a fair accurate to detect rogue access point in such conditions so the the karma attacks detections can be done in in different modes the active one or passive by default two runs in passive mode where we just listen for some probe responses that will fall into the condition that this progress pulses will will say that it is different SSIDs from the same access point so we spot a common attack if you want to be more active than you you have some some some speed results you will activate the active mode which will which will probe
from different SS IDs and since this attack is running it will just be spotted because it will answer to all these requests so to two detectives basically we just again run the tool in the normal mode you don't pass any more slugs except from the interface and the and the scanning process and then in this second window I will perform the comet X using the air base and z2 and once I started we will see that some some karma rogue access points will happen we have the first one which is the default access point which is created by the air base 2 and then you will see in a while yeah that it detected the karma attacks for this part
is not zero 157 Network so yeah basically we detect the karma attacks ok so the next one and I think yeah the last one flock for the videos is the PM k ID detection which in this case we will need to run the tool in a different way which is the we need to pass the different interface in this case it's the hi m interface which will need to put your interface in a monitor mode and then you'll pass the flag the white file the attacks detection once you started you will start looking for what's going on in the in the year and in this in this window I started the PM k ID attack
using the H hcx num2 which basically will try to do this p.m. key ID and how it works like i said it will use this rate will target to reassociation process and what it does it will try to do a bunch of authentication requests and association requests in order to see if it can leverage that p.m. key ID from the access point and so we will gather all these effectively authentication requests from a specific from a specific access point targeted a specific actions access point and you will alert the user that something is going wrong and is probably a pmcid attack so as long as we run the tool we will see this this buckets going around which is
not normal and they are told target all the same network or if they were done in broadcast they will talk different networks and we also see here these the authentication packets because the two also identifies the authentication and attacks but these ones are kind of legitimate because if it's reason 15 code which you pretty much it's the four way and shake timeout because once you are trying to do these associations request you will interact with the access point and you will fail doing it and the access point will send you the information about the authentication packet the forward four-way and shake went wrong so in the next step we configured this used every play to send
some the authentication attack to show that it also detects the authentication attacks like we already see it detects - the authentication packets but yeah just to be sure I change the channel of the interface to be in the same one of the target access point and we can see that it's flooding many the authentication packets and we can see that we rightly identified to the authentication attack so so basically these are the detections of the tool they are covered some of the of the detections process and in the next slide I'll show you a small case study that was done in the company where I work and it's pretty much we were doing a Wi-Fi assessment and the auditor
representing the attacker try to - - to validate the the Wi-Fi security of our networks and so basically he deployed a bunch of Wi-Fi attacks that were unknown to us and and we was running the - in the background just to see how it behaves and we can see that the we have three different types of detections this ones here are shortest to represent two one are not identified in the previous demo but the first one will identify Robeson's point with the same SSID and different the SSID the second one will identify rogue access points with actually everything exactly like the ones from our company but failing in a different region our SSI and the last
one it's pretty much identifying karma attacks and the one that I didn't show the black.we statistics so in the first case the auditor was just setting up the tool and didn't pay much attention and it just deployed the rogue access point not caring about the SSID so this diversity is not one of our authorized ones and we will immediately spot that rogue access point was going around so the next one challenge accepted from the from the attacker and it really go deep and configured an exact access point of our owns and in this case what failed here was that it configure it with a much higher our SSI which are much higher signal and it showed something strange
to us we try to authenticate to that and since this an enterprise network the the authentication process failed because the attacker didn't our our our process of authenticating to that network was not one of the attackers so it failed the Association process and basically in this kind of attacks the attacker just wants to steal your your credentials so it will just target the first phase of the authentication and will not actually authenticate you to the radius server so it failed so it spotted that there's a rogue access point around so the last one we look at this points from the pineapple AP tool and the karma attacks was spotted inside black base terrific because pineapple also called the
pineapple access points are are blacklisted by our two karma attacks we already saw the the auditor started a branch a bunch of karma attacks and we saw that something was going wrong and we successfully identified this rogue access point is Wi-Fi attacks a thing here is that apart from this the tool also has a lock mechanism where for example if you'd integrated with CM system and you could receive these alerts in real time and monitor them in your in your infrastructure but as the way it is configured we just run it in the terminal and that's great for us but see that this lock system you can actually connect it to to a to a cm so to
complete so we saw to that it's it's an open source module or framework actually if you are interesting you can you can look at that gita and then pretty much identify different types of rogue access points like even twins and authorize improperly configures ones that was described previously and also detects some Wi-Fi attacks like the karma the authentications p.m. key ID and i added here this limited crack detection because the way the crack attack starts basically one attack vector is to deploy an access point in a different channel so we have that nutritional detection that I don't say that it is specifically a comma attack that if something is tried as you should look on so basically
that's it if you have any question please go around and thank you all for it
any question yeah have you thought about implementing like Auto learning feature for a profile generation and stuff like that yeah that would be great yeah for example I think in a scenario for the free Wi-Fi that could be interesting because it's really hard to maintain all these profiles for free Wi-Fi so we have a couple of of detections but it will be interesting if you have this also learning feature but yeah it's something to think about in the future yeah also expand the tool from a stationary point to a way where it's deployed in different nodes will be great yeah any more questions that's it all right thank you