Controlling Your Neighbour's Lights: ZigBee Security Analysis and Smart Home Vulnerabilities
Show original YouTube description
Show transcript [en]
so welcome to controlling your neighborhood slides or maybe we should call it controlling your neighborhood's habits of course there is a big difference because between the habits in the end the lights because I'm not controlling the lights but he habits of the users you will understand that my name is Andrea Dido and this presentation is based on masterpieces of my master in information security in university of lisbon there there are four areas here in this presentation I have the motivation where where I explained the whys I have the the ZigBee and I will explain the ZigBee the standard because the the project is based on the CV and I explain some attacks that I did most of them without
success I must say other ones more interesting and you will you will say why did I choose this theme for me it was obvious from from day one that I need to choose something related with IOT when I arrived at the master from since the beginning I knew that I wanted to attack something that can can have some impact in our daily vices and I start searching for for what can i attack the first thing was smart goggles for skiing and my objective was to make a skier goes down a hill and probably kill himself but ok this is too much expensive and I can't do this way so I start looking for other projects
and I found some electrical plug system smart system that a user can turn on and off with the mobile or with a web portal and it's very simple I will explain a little bit more detail later but the thing about IOT is that as we know the most optimistic statistics say that there will be 20 billion devices connected to internet and this brings two major concerns two major problems is that first of all if we already have some problems with distributed denial-of-service nowadays when we have this kind of members of course we will have bought a lot more problems and will be very difficult to stop this and the other thing is that's Noah does most of the
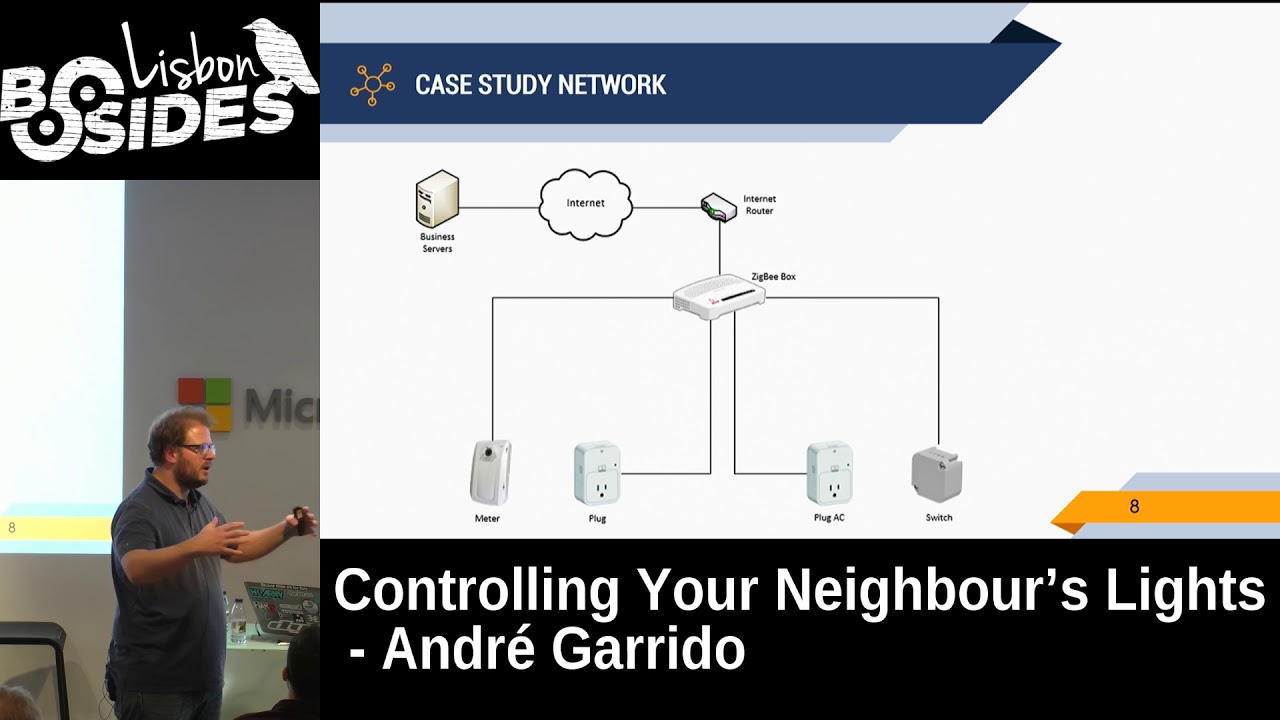
IOT gadgets F personal information and for me it was like a personal vendetta I think we need to save the personal information for example if you have a running bracelet it might save or saving some database remote database but it might save your your weight your height your age your running pace your art right and this could be somehow dangerous to to us in the future the case study was based on one on this on this let's say layer I call it Zig we layer it's it's normal plugs like the usual plugs that you buy on the Chinese stores the the main difference is that it has an on/off button that you can turn physically on or off the plug these
are the cases of these plugs the main difference between this one and this one is that you have infrared remote transmitter that sends sinus to air conditioners to turn it on or off you set it on the web portal and you say my air conditioner is the Samsung something blah blah blah and then you from your web from your mobile phone you say turn it on or off it's good in the web portal you can even schedule your tasks if for example if you arrive at 6:00 p.m. at at your house you can schedule for 5:00 p.m. and 2 your heater for example and you arrive and the house is warmer the the there are others - let's call plugs
on although they are not really plugs but we have the meter it's a programmable logical controller that is used for irrigation systems or water pumps and we have a switch that is used for boilers and heat pumps I only had access to these three and it was enough for for doing my research and for in this one this one is like it's it's it's called ZigBee box in reality it's a router a normal router and make an IP connection between internet router and ZigBee box of course there are some connections to the enterprise servers that control and send some actions to my plugs so this can work in in same way my objectives my objectives with this master thesis were
to for the front part it was the intrusion tests where where I can do some blackbox intrusion test the only aim for that I can gather it was from flyers from websites from technical information from books and manuals I can use any attack vector but I need to have courses with with ethics I can for me it wasn't it wasn't very good to attack some production server and gather some information from there and somehow exploit it so I decided I only will work on my sorry on my on my network on my ZigBee layer and I will focus on that the other thing is to gather much information about tools and different abilities about Ziggy since it's a
protocol it's not very very seen in Europe especially in the United States it's way bigger but in Europe is not very usual to see so what's the ZigBee some people say that Sigma is a protocol in reality in my opinion it's a protocol but some people say that it doesn't because it's it's based on 802 15 4 it's it's a specification used for wireless communication like Wi-Fi it's very similar to Wi-Fi and somehow there are three main characteristics it has low consumption you can have some some sensors or some ZigBee equipments that last for five years in a warehouse because mainly because the there are there are a low bandwidth that transfers all the data very very very slowly but
very few data and of course this goes to the low consumption it's a characteristic low cost the the ships usually from Texas Instruments are very very cheap and this of course brings the device is cheaper than others there are there are some persons to that say that ZigBee do create personal area networks in my opinion and this is my and some other people opinions is that it's area networks because I will just go to three slides this kind of plugs for example our routers they can can route data to other to other plugs and so you can have a way bigger network than a personal area network there usually a personal narrow area network is the the Bluetooth
so I think we should make some difference between and we can use dedicated profiles for home automation smart energy else care green power there are a lot more you have special profiles if for example you use gadgets for IOT devices from medical stuff you will lose the healthcare dedicated profile this makes sense because it's a lot smaller and the ships doesn't have too much memory and it makes some sense the other thing is that ZigBee and this could be a problem for me and during the other work is that it works in regional frequencies for example in the United States not United States in North America and north and south of America there are 10
different channels 4zv strangely in Europe there is only one that channels zero in in China there is there are four and in Japan and Australia there are one there are others but these are the most important but luckily there is also international frequency that is like Wi-Fi it's the same as Wi-Fi 2.4 gigahertz in the in the vendors perspective this is very useful because if you can sell worldwide is way better than selling only to United sides only to Brazil for example only to Europe Japan and so on and this was my first problem is to no not not my first problem that it was one of my problems is if this if my project doesn't work in
international frequency would be a problem because I don't have tools to regional frequencies so one thing is that ZigBee since since the beginning and it's written all over all over places as if we bet on security they say we don't want to commit the same errors from the past and we want to use some kind of security to protect the communications and they decided to use some cryptographic keys we have we have the link key it's used for unicast communication basically it's a communication between two peers it's shared by transport for installation or establishment the only purpose of the link key is to encrypt then the network key that is used for broadcast communication anyone who has the network
he can communicate so can translate the ZigBee packets and understand what's going on there as you imagine now this is my purpose break something here the network is a road key for broadcast communication can be shared by transport or pre-installation there is another key that is the master key it's more I don't know how many of you know diffie-hellman but it's more or less like the film and we have some variables we exchange it and you then derive with an algorithm the link key then you encrypt the networking can be shared by transport pre-installation or user input it's mandatory in one more recent standards of ZigBee Pro but in my case it wasn't mandatory and it was faster to know that
but in my case it wasn't about key sharing we talked a little bit before but in transport the keys are passed in clear at the time of the network assess approval the first contact between a plug in my case a plug and a router the the keys would be passed in clear so I can get the that key the pre-installation comes pre-configured from factory and the main problem is that if it's can print reconfigured from factory if you want to change the key it's more difficult because you'll need to go back to the factory to change it at least for most of the mortals and then you have establishment is is the same as the the master key the
allows two equipments to determine one key from from a master key about the tools the there are there are two men two three mind tools let's have it in this light - it's the r0s mystic are the and FP mode both of them are for the same purposes it's to translate the packets and to gather information from ZigBee it's more or less like Wi-Fi pan that you connect to your laptop the main differences between them is that RZ is older you need to install yourself the firmware and with with the one from the right with a GTA programmer and you have then the EPI mode that is newer it comes already with with the firmware installed
which is great but the great problem is that FP mode FP modes you can't export it outside of the United States because there's some proprietary and you can't you can receive it so I I used in the beginning this one I I will explain a little bit more later but I use GTECH to program it and then there are some other tools the killer bee killer is the framework is is software to analyze ZigBee and then you have good fat for me it's the most interesting ones especially because you need physical access to to the to the devices but you can extract the file system from from the ships and from the plugs and devices so my case study as
you understand is some kind of plugs I open the plugs and I have access to to it and I need to study everything and I need to start doing something with it the during the the first phase was studying all the vulnerabilities all the tools it took some some time to understand the things and the what I would think that would be very very easy I'm not very good with it but if I think okay I have the rzv West mystic I need to soldier some wires here to connect to G tech programmer I don't know how to do it I must be honest but I thought someone can do it this very easily so so
I decided ok I will try to to find someone and this is almost my reaction I spent an entire weekend to find someone who can do it because some people said okay this is easy that's right the the soldier doesn't stick to the world that the wires are too small I can do it and I passed the whole weekend to find someone who can do it until I found one guy that's did it and I can start doing some some work and when I start doing my first my first problem as I told you before I want to grab some packets to understand if it works in regional or international frequency and I use Ziva Stambler it's one of the
scripts in a CV killer killer B and this gives me some information already giving some information telling it selling me okay this is international frequency you can use it and you can start doing some more interaction with it it gives me an address this address is is volatile when you disconnect the plug when you connect it again it's another one you have extensible address it's the MAC address and you have the stacked version this is not what I have seen it's always the same for everyone so I don't believe this is real so it is what it is and it works on channel 11 from a bunch of channels like Wi-Fi my other step was
okay let's let's start gathering some some other information from the plug that I have and I gather all the addresses from the plugs the ZigBee router as this address four zeros and in every network ZigBee network it the router as is always four zeros so we can identify every time the router then there is another tool I must be honest it wasn't very useful for me but I think I might it's good to show it to you it's zippy finds if we find it's like a radar you can grab your laptop with your your board connected to the laptop and you start walking through a hair walls or to a factory and see where are the sensors
and grab them or do something with them it's it's kind of useful then my next step was there aren't much more that I can do in an information gathering phase and I decided I need to start doing some packet analysis and I start grabbing some packets and this is more or less my reaction when I start getting the packets I became looking at it and what's happening here I couldn't understand because all the packets start freezing after 10 packets 20 packets I think the higher number that I got it was when Android then something which is not normal and I can study it very well because it's very short I can get 100 packets in one
minute probably so it's it was strange my my decision was try to talk with some people in the ZigBee community understand what I was possible to do no one knows about this error I put some some errors in in their github they start some talking's and nothing can happen and my time is passing I don't really know what to do I try to contact one person that is the the brain nowadays behind Ziggy is Ryan Spears and I said Ryan I'm having this problem please help me and sell me an app remote and it told me it's impossible because I can't export it outside of the United States and I told but why don't you come
to Europe I'll go there and fetch one of those words it all it's impossible I can't do it and so one of my friends in New York got one for him and lend me for a good time so I can study I receive it and I put it on on plug it on my laptop and my reaction I was very very happy because everything was already on the on the on the board with the new firmware with everything set up and my reaction was immediately this because all the packets that I got as errors and so I have when rzv West mystic that doesn't do anything i as epi mode that come with full of
errors and I don't have any other options what can I do now I start contacting with Ryan I start contacting the other people meanwhile there was some guy that spent some time looking at the errors that I sent and found the error in the firmware core system and decided okay I need to correct this he corrected he sent it to me to do some better testers in the in the firmware and it was perfectly and I started doing the analysis as I expected the first the first the first packets were encrypted I was expecting this it was not not a surprise I confirm it with will by the way this is DB dump ZB dump
is the same as TCP dump but for Wireshark for sorry for Ziggy's and then we have CV Wireshark is it's really the same thing as Wireshark with some advanced let's say but you need to to start it with with GB Wireshark and I confirm it that it was encrypted payload and I can do anything I I know what what would be my why I start doing some tests and trying to connect and disconnect the plugs trying to reset the plugs trying a bunch of things and nothing happens on my logs everything was there were no key there is even a script I don't remember the name but there is a script in killer be that find the keys automatically if
you gather for example I I gather for we entire week of vlogs I put it there and he said there is no Nokia so the only option was to get some pre-installation key so the the key is already on the plug comes from factory it's in the file system of the plug and this is my only option so I I went to good fat it's that small board that I showed you it's made by trivias good speed and the what you need to do is wire for soldier for wires one year what another year another we're and one in one of those and connect to good fat on those pins and then you connect to the your laptop I must say
that it was very very funny of course it wasn't me soldier again but I asked I asked some professional themes on polymer Center that I knew between those those times and they did it this job they said okay I can do on switch do you remember the the network layer you have the switch on the right but the others I can't do it because the you have a component above the this spins and we don't have space they did it I was happy with it I connected but the board was burned i I couldn't have access to to any information it didn't connect so at this moment I was more or less like this because I don't have nothing if you
believe I'm doing master thesis and I don't have anything to show I know I knew that this was a problem for me because I already asked the teacher if that was very ending me and if I don't have nothing what what will be the solution and she told me we will arrange something and don't worry about so I decided ok I need to I need to relax I need to sit down and think about this I decided to sit on on the floor of my of my living room together all the books all the papers everything that I have and start reading again and again everything to find if after those months of studying if I found anything new and
suddenly I found something in the standard that is this they say a device will not intentionally or no dependently transmitted sking material to other devices unless the king material is protected and as Schwarzenegger says this is very cool because your king material should never go and protect it anywhere the problem is that's some after some paragraphs after this you have this a default global tourist center link e must be supported by the device if no other link is specified by the application so in one way and we you say that you can you can share your your keys and you can share your king material without protection but the other end you say if you don't have a
link e defined by yourself you have this one that you can use and it's written on the standard so I was I don't know what to say so this one it's written on the standard the most amazing part is this one was signed by contract and no one can reveal it and of course someone reveal it on Twitter as always so so this this was this was strange for me why did I choose this method it's it's it's very strange for me and of course I inserted in on Wireshark is this key and I start and I get the the network II by the way the way that I got the network II was resetting the plug
totally resetting connected putting out of the network come again and the first time they connect the router sends to the plug the key the the network II I then I fetch this Network II I put it on a Wi-Fi on TV Wireshark and I can start reading all the information that's passing in the Ziggy network and if you can see remember that we are talking about plugs you can see that this the router send an action to this plug to turn it on okay this is nothing special right but how about if you studied the the abbot's of that user if I gather for example one week one year 10 years or of the abbot's of a person I can understand
everything that she is doing and what are the habits and what are what we will do in the future because probably there is a probabilistic that you'll do the same in the future what will go there next then I start doing some some other attacks none of them which is sorry I I did a distributed denial-of-service denial of service attack I don't really know why that's the strange part after after I putting the two keys the network key and the link key or the default link II the network starts running very very slowly I didn't know why I don't have two devices that can read and send packets at the same time so I'm a little limited
here but what happens is that the the network instruct and for a while it is didn't answer to the user and I reset again I take off the the world and everything start working again then I did some replay attacks with different frame counters with the same frame counters different frame counters did some forgery trying to to send different actions but nothing happened and this was the end of the study in Ziggy but tired I had other areas that I can that I can study for example I added the IP network and the website I need to be honest the website was already studied by a pen testing company of course there weren't many things that I could get especially
because I was in a staging environment so I found some errors but they weren't available in in production so I didn't feel very very very well using my time for a thing that is not the production so I let it go and I decided to focus on my EP network the first thing that I did was of course some an maps and some information gathering stuff and I found that the ZigBee box disagree router has the port 22 open I tried to find what was happening there the version of the of the SSH server that was there and I didn't found anything interesting so I moved on and I decided to go to something that is called an tap is a
man-in-the-middle in a raspberry more or less I connect the I connect the ZigBee router to the to the raspberry I connect the raspberry to the IP router and I start getting all the information that pass there and one thing that's that clearly got attention to me it was that the first packet was this one I got some basic stuff and then I asked some JSON file with push Commons remote SSH IP remote @sh login and remote SSH port I try to understand what's behind this but once again it was a production server I didn't want to mess a lot with it but you have the login you have the port you have the IP the only thing is missing is
the password probably because it uses a key but well you have some critical information passing in clear in your network okay what why I wasn't expecting this is probably something that some of you expect to see what what I wasn't expecting is that I can gather the same information that I got in the ZigBee Network in the IP network in clear when you send a comment an action through your phone discount this action passes to the IP network and then goes to the ZigBee network and turn on or off the plug the thing is in this one you have switched on the plug and this is the address the MAC address of the plug and you know it once again if you
studied you have you understand the habits of that person in conclusion I would like to know to talk about the past and the future of this work I think that the ZigBee community it's it lacks a lot of maturity many of the tools doesn't work there are there aren't too much information too much documentation it's very difficult to have something working I would not say another percent but I would say 80% and I think there is a big gap from the point that you need to study this very very well I show that it was possible to steal some keys I truly believe I saw that it was possible with default link but I truly believe
that if I add spice to thousand more wires in the plugs I could do it with with a good fat and physical extraction because if you think about the default link and already with with the stuff so you can gather from there so for me it's obvious and then we come to the to the best part of it is the capture of personal information I did it in ZigBee Network in the IP network and let's stop here for for a while and understand the dangers of this if you have this kind of information most of you say who cares if someone knows if I plugged in or plug out something remember this one this one
wasn't clear so you need to have physical access to it but this one I can be outside of your house and capturing all the packets because it's not necessary anything and if we stop here we start understanding that is possible for example and I did this study if you arrived at 5 p.m. and you watch television at 11:00 but for example if you have an electric oven I can understand that you cook between 8:00 and 8:30 and then you wait until 9:00 and at 11:00 you go to bed and you turn on your lamp and read until midnight after that you go to bed you sleep and you wake up at 7 a.m. and you'll do your
beer because your saver is electrical and you take your best and you have a boiler where that hits your water and I understand all your efforts in the weekend you have other stuff so for me this is very very critical because if you study someone not not for one day not for two days but if you studies someone for one year you can have you can predict the future of that person and this could be very critical in terms of future work I have 3 3 topics that I would love to study is the silver n moon is attack it's to Portuguese that found that ZigBee have a problem with frame counter if you if you rise the the frame counter
to the limit the the network stop okay I couldn't do it sorry I couldn't do it because I don't I need to to pans to do it and I don't have it I would love to do some packets for during in a way that I can change the infrared codes instead of connecting air-conditioner for example turning on a television or something like that or something more dangerous and he's already talking with the company to study PLC the one of the other plugs because they didn't have the time to install it I didn't take the time to study too so we are doing this in the future there are two additional contributions to this work honestly in
my point of view and being humble it wasn't very big but they asked me to do some testings to the firmware to see if there were any problem after that they corrected I was with them doing that and one thing that I found very funny is that they asked me at the description of a new firmware installed using the GTA programmer because the ones that they use it was a very I would not say amateur but something more poor and and this one is more professional let's say like this and they decided to put I think it's already on github of them on the killer wave framework so you can you can see what's this that's all I think
the hope do you like it if you have any questions please do so [Applause]