Pwning For Plaintext: A Hashcat 2.0 Adventure
Show transcript [en]
awesome thank you very much welcome everyone hope you enjoyed lunch chil wasn't too bad at least I don't think so and of course I hope you're enjoying the weather too the token slide I'm will online Twitter Discord anywhere steal flit um co-founded a Cambridge based cyber security company so when I saw bsides CS pop up I had to represent quite literally and figuratively um so yeah I'm a pentester red te a hacker by trade used to be in digital forensics but then I turned massively defensive and I also do some pentesting on the side I've been lucky and humbled enough to have been training and speaking at a number of different places and this year I managed to
socially engineer myself into helping out password vage at Defcon which was fantastic um yeah I've got another job as well and I I help out in various advisory um sort of capacities but that's pretty much all there is for me okay the agenda so first of all who here is either a pentest a red team or generally someone offend iive brilliant who here has password cracked for is cracked of hash even better who here really Geeks out and loves like loves like obsessive this is like it porn for me who really loves cracking hashes like really loves it fantastic subtract that number and I know how many people I need to convert by the end of this talk so that's where
we're going to start we're not going to be doing anything intro 101 stuff I apologize this is going to assume some knowledge um we're going to be get into some weird and wonderful attack chains talk about pass phrases specifically delimited pass phrases as time goes on promoting length over complexity we need to make sure our secrets of the incap secure we're own some deep stuff around hash cat internals and Rule buffers and position buffers I'm a massive hash cat Fanboy anyone use John the Ripper okay you can all exit now fantastic great having you in the room um but it's good what it is but hash cat is is quicker um I don't get commission but I I'm a huge
hashcat Fanboy my emoji see look this is what happens when I don't run on my own laptop that should have been the ow and Emoji quite clearly um we're going to look at emojis uni code and cracking hashes with hashes if that emojis move there are going to be a couple of other things that are out of place unfortunately because I didn't have time to vet this before we started the only primer we're going to drop straight into those is masks kind of 101 because we need to understand what masks do in terms of cracking hashes so that we can understand some of the more complex attack chains that we look at soon so a
mask is effectively one of these inbuilt hashcat character sets we have l u d s and a you can see we have a few more over here we're not going to touch on what these are um L for lower Alpha U for upper Alpha D for decimal and S for those elusive 33 special characters we also have a and when we see a mask with a a question mark a it says test all lower upper decimal and special which accounts for the 95 printable a characters typically work with so if we had an example passw of P 1 two three we can see a mask that would absolutely match that part clearly an attacker wouldn't know the mask to use but this
is just so we can get a start to get a grasp of what masks do so we can build this into attack chains using Attack Mode three Brute Force mode to do either that we can pass standard in when we want to test per position character sets that contain either ler upper or lower for example or more than one character set we can also Define up to four custom character sets using -1 2-4 in this instance we can see that we're saying custom character set number one will only test for upper and low upper and low Alpha Characters so when hashcat sees three instances of question mark one in The Mask it's not going to test
decimals and special characters reducing the key space and therefore massively increasing our chances of attack with the primer out of the way though let's get into some fun so I sometimes get asked how do I do this anyone who's cracked passwords might have done masks you might have done word rules yada yada we'll get to that later but what if I know the start character what if I know the end character but I don't know how many characters in the middle this is what I there's probably a better way for it but I call this Midway incrementing mask so we don't know how many is there but we know the start and end hashcat can't like natively do that
but luckily for us and as we'll see as we go through this presentation hashcat is fully pipel lineable and we can chain all manner of things to hashcat and here are two examples of what we could do to do just that in this example we can see the password of crack starts with a number so what we could do is we create a word list containing 0 through 9 okay easy job done we could then use that mass in- A6 which is a hybrid attack mode so hybrid Attack Mode is take a word list and then add a mass to it we could then increment this mask which means it'll start at um here and then
build up and up and up until it keeps going but instead of trying to crack a hatch with it if we write standard out that's just going to print our candidates to the screen we can then PPE this back into hashcat and then we can append our last known character or known character set as a rule now if we want to go deeply technical on this there are actually some really important caveats to this the number of L's you could do here is finite and this is because when hashcat uses masks in this sense in A6 Attack Mode we're storing that value as an nign 32bit integer so 32-bit integers can have store of course store a lot
less than a 64-bit integer can in A3 mode so you're going to get you're going to get an integer overflow very quickly if you try and test above seven in this instance but the testing may vary and I can of course go into more detail offline if people are interested okay separating the week from the shaft so expander and print who's used expander Don't Be Afraid who's heard of expander oh okay I know I need to Target this who's heard of print's processor anyone okay so these are very very cool tools um very token high level intro on this first of all if you're not you've not got the hashcat utils download hashcat utils it has a ton of really really
useful tools that you can use to enhance and aent your attacks one of these tools is called expander I've got a couple of screenshots in the bottom right that shows you what expander does if we were to give expander a word for example hashcat expand it always unique the output because it does produce dupes we can see what it does it's taking our word hashcat and it's chunking this up up to a maximum length of four because that's what s uses by default but all the letters will always be contiguous in how they appeared in the original candidate I highly recommend you recompile expander at eight or 10 depending what you're after and you can
see you get a bit more mileage but visually seeing what expander does will go a long way into showing you how weird and wonderful these candidates can be produced so this is a a candidate generator okay fantastic that's expander out the way prints processor has its own repo prints again is a candidate generator but this is more targeted towards building past phrases chains of elements together and you're going to hear me using elements a lot because when we talk about a p phrase there are a number of elements in the pass phrase so quiry 1 2 3 4 5 six would be a two element pass raise okay you could refer to them as passwords but as you can
imagine that's going to get very confusing going to talk about passwords so taken straight from the wiki here if I was to tell Prince processor here's Rock utx it's a very common wellknown and very tiny dictionary that most people are aware of if I say read through Rock you and print me every possible four character passwords these are the only ways you can generate a four character password so prints will go through Rock you or your word is to choice and generate every one two three or four and mix and match them together until it produces a four character candidate now that might seem pretty basic but when you get into bigger lengths it becomes absolutely crazy and
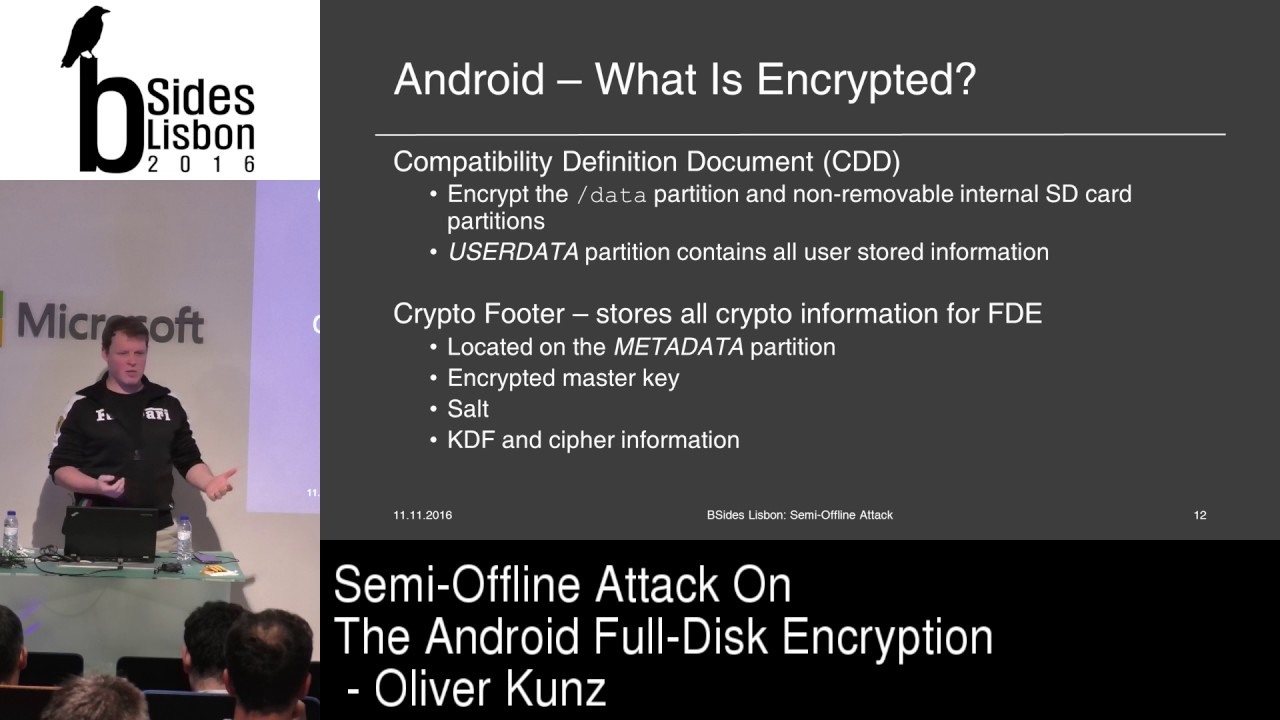
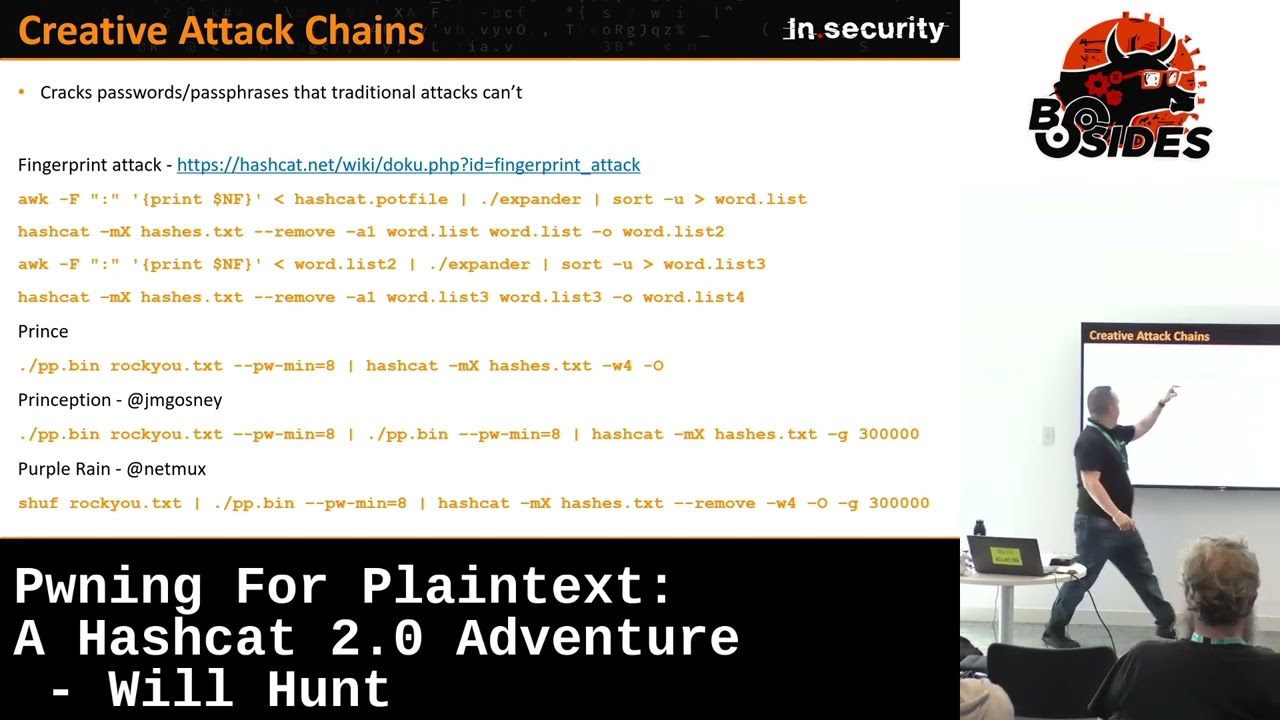
you can tell Prince guess a minimum of three and a maximum of four elements and you can build this up to fulfill the requirements that you're after we'll have a look at this in context very shortly okay one of my favorite slides is just a c of hash caps intact and stuff these are really cool attacks so what we're talking about here is I speak to a lot of pen testers my company does AD audits know every pen tester sees hashes people tend to run Rock You they'll run at rules they'll do a few things they might do a bit of a mask attack or brute force a small key space then it's like what of you tracked job
done move on to the next there is an absolute untapped Gold Mine of resources out there and if I knew what I knew today years ago I Dre to think how many extra passwords I could have cracked I appreciate that Stu same as anything in life um fingerprint attack is the first been around for since the dinosaurs since hash started but it's really underloved and not very much talked about for a thing attack you don't even need a dictionary for this attack what you do is you take your pop file your pop file is a a list of files of all the previously cracked password is very cranked it's your it's your gold mine if
I'm reformatting my box I don't care about my personal data I take I back up my pot file okay this is this is gold duster password cracker so you go through all the passwords you cracked previously so they're real life passwords for a start this is just taking the clear text and that not the hash you expand it you sort it and you create a word list for the output now that's a very very important part because you you can see what we're doing next we're running Flash in combinator mode which is- A1 combinator mode takes two input lists and it will mix and match every option in word list one with every option in word list two but again
we haven't started from rock you we are expanding so we've taken every part you've ever cracked done this kind of crazy Jazz to it and now we're running that in combination with itself and it creates really really weird and wonderful candidates that normal sort of traditional worthless rule attacks can't do but the fund doesn't stop there when you crack as a result of that combinator mode you save the output and then you repeat and rinse you re-expand your newly cracked passwords get back into a word after you expand and unique and then you same again and what you'll find is this technique excels on big big big password lists like huge password lists especially if you're doing like analysis
on data bleach type Stu millions of hashes and you'll find you'll very quickly crack load it'll plateau and you'll get diminishing returns hard until you get none either your patients or alcohol will will drain first it's it's you know it's hit or misses to which which it goes a prince pipeline the most basic Prince pipeline you can do call Prince give it a word list we can tell Prince set a minimum password length this is generally almost a staple in any testing you do because in pen testing or reding or just general password cracking gpus are fast enough that we could exhaust the key space of seven guaranteed eight quite so if there are any gamers in the
house you buy the latest and greatest Nvidia RTX cards and Nvidia RTX 490 can guess NM hashes at 288 billion guesses per second okay so phenomenal stack a few of those together and you can exhaust every eight character the Windows password in under an hour very very easily these days so we won't tell quins don't guess four character passwords I've already cracked all them get everything eight then give it to hashcat and append your any options as you normally would it creates really really cool passwords Prince setion so Jeremy gosy part of Team hash um invented this on the Fly a few years ago and he thought hey why not take prce output and pipe it
back into prce because why not so PR setion felt like a very good name at the time um and again when he was doing it some of the candidates that came out on the screen were absolutely crazy you couldn't even imagine them up and yes you are able to crack some passw of this I'm not going to sit here and say if you use these attacks you're going to crack every hash of course I'd be stupid to say that but you will get hashes falling otherwise contested for anyone who's unaware the Das g at the end invokes hash cats r rule generation so rather than dash off your own rule set say hey hash give me 300,000 completely random
rules so for this attack and the next we've moved on to what's called non-deterministic attacks that often go for infinite runtime we are now no longer in control of the candidates we are generating because they're being augumented by hashcat netm who is the author of hash crack if anyone hasn't bought hash crack version three from Amazon it's about5 please do it it is the gospel for password cracking what net Mark found was if you take rock you give it to Prince and just head the first 10 outputs you'll get the same 10 candidates each time every time you run it but if you shuffle your input list you get completely random passwords every single time so we thought well s
it why not let's just Shuffle it press go walk away and these are the types of attacks that you kind of run when you've got days and days you you fired up an Amazon instance and you're just going to let it run these won't ever end okay but they will generate especially this one will generate completely random candidates each time okay on to delimited pass phas generation oh but we You' been talking about pass raises but I'm super Le and I put spaces I'm writing a sentence and you know what that's good you should any delimiter is better than no delimiter how do we address that Prince we have already discussed but Quin only accepts
a single list there is another option called combinator X again hash utils what combinator x does it can take up to eight word lists and you can see here we've got three files containing two candidat in each one we can tell combinator take that file that file that file and you can quickly see what it's doing to generate those candidates but a limitation of combinator X that prints overcomes is that only the candidates that are in password one will ever appear in the first element so you won't ever have let me in or querty appearing in this position obviously because you're feeding it specific files now if you copy and paste the same file eight
times clearly you you'll address that but for different files that is a that is a limitation so it depends on what you're after combinator is quite some quick wins because you can in insert custom separators and different ones let's say I want a space between the first two elements and I want a colon then I want a comma you can mix and match very very easily with combinator pipe to Hash capap business as usual there's an example of that in an up slide embedded videos because you know live demos are the devil's work um so you can see here just an example combinator X sprints on the left we've got three word lists pping that hashcat
and you can see that the word the is always the first element now it would eventually change if the video was of course left hours but you can quickly see how that varies with prints where it's randomly picking any elements it can from anywhere prints most of the time is the better option okay most of the time not all but most of the time um and in print we can also Define the elements so we've got three wordless here we can say elementum count minimum and maximum of three to tell print exactly how many elements in our Pathways we're after one very very important thing um with prints though if with prints we have to have a pre-
delimited word list so you can see here I've got a combined word list of these three but with a space at the end um and I need to do that because prints can't insert spaces but in doing so we're going to have a trailing space at the end of your word list on every candidate and we need to delete that last we need to truncate that last space that's what we're doing here at DJ so DJ is a single this in this place is applying a single rule and a closed bracket is delete the last character that last space is always mov okay case toggling cyber security is not a technical problem never has been never
will be it's a people problem passwords are absolutely no exception we I'm not going to sit here and say humans are terrible no we we're generally pretty good but we are unfortunately the vulnerability when it comes to password sory because humans generate passwords and when people like to create path phrases if you're going to capitalize a letter you're going to capitalize the first letter if you doing something like this a lot of people like to capitalize the first letter of each element because we're humans and that's what we do why would we go case or or anything else why would we possibly do that we are creatures of habit and unfortunately that is our problem hash can address
this for us very very nicely okay so um I'll go in reverse so toxic three so um Janis who is one of the team hash members has got an awesome rule called toxic three rule which has been in hashcat again since the dinosaurs but people don't tend to use it um and what this does is this goes through and starts capitalizing different elements depending on how many you go through inside your word lists you can extend that even further by using things like capital E which in this botted example here with rule two will take any pass phrase Del limited and automatically just uppercase the first letter so for a single for a single rule you've wiped
out lots of very painful manual rules you would otherwise had to have created absolutely fantastic use it Nest it by nested we means run- R rule set dasr rule set you can use more than one rule in hashcat uh or use it with PRS as well have some fun like I said these are all things you should be doing when your usual attacks are fail okay so here is the the syntax slide there lot of syntax but we are talking about password tracking so there's going to be some some takeaways from this um these two options are more or less what you saw on the slide with the video a minute ago in this first
example we're taking Prince we're saying Prince I want to crack a Four Element pass race denoted by our minimum maximum here we want to have an overall total minimum password length of eight and I'm going to give it a word called 20K space now this that the Google top 20,000 words for a tiny word list just for testing it's fantastic I pre- appended the space at the end of every single line in that word list okay that's what this demotes we then pipe that to hashcat DJ locks off the truncates the final space to give us a nice clean pass race and then business as usual dashr and we can go on and do what we need
Clint itself comes with an optimized rule set optimized for prints I highly encourage you to use that as well as other rule sets of course your mileage may vary with conator X we don't have that requirement of having to pre-create our hardcoded word list with our own delimiters we can just pass yeah the word we want and manually insert our separators either static or mixed now how we see fit P that to hashcat and then business as usual run it with whatever you want the examples here are for a hashcat vary just because you're in your you're in your own kind of safe space now you can do what you want aftering this kind of
Z prints sorry pre- delimited lists with prints is the most painful because it does require pre- delimited lists from the start so for example you would have to create a word list with one element manually insert a space run like combinator bin to combine that with a second password list and then add a spacing at the end just to create your first word list bit of a pain but this does work too second word list is just t with a single delimiter you can see here I've tried to hopefully make the wording like logical our first word has a mid and an end space our second word just has a mid space part back to Hash cat go
nuts who's heard of one rule to rule them all oh a couple of you who R me still oh dedication okay so that is my own chain plug slide so I made one the mall in 2017 um I did have some people sort of say is this going to updated I said no because I'm too lazy um it went on a bit longer and this year I fun got around to doing it the point of the update was not for it to crack more password there are fewer rules it's got 5% less rules which shaved a few thousand off what it does do is it cracks the same amount in a quicker time this is an optimized rule
set do not use on bcrypt scrypt anything painful use it for NT md4 md5 anything in the sh one and two family fast hashes absolutely fine okay when you are testing your rules always always debug not just to show the effectiveness of what you're testing but also because it shows human behavioral traits and characteristics again password is not a technical problem like Cy it's a people's problem and it's more of a psychological study of how we're generating our secrets when you're running debug mode one get that out to a file and you wouldn't see this live you just C file normally sort unique and reverse it but I'm just doing a live kind of cat on this and you can
see how your cracked passwords the the the effective rules are kind of bubbling to the top so in rules a colon is a vanilla pass through just take the plain candidate we can then see we are in this in this example comma is a bit weird that's replace the replace the character at position seven with position six um and it gets a bit crazy here's some more familiar stuff dollar one do two do three we saw that append one two3 send your password okay statistically speaking and I'm not going to ask for names and hands but when you've been kind of conditioned and nurtured into choosing your passwords um unse secure because I've got a you know a number of
special characters one statistically is the highest performing 1 2 3 closely second for special characters at least someone in this room uses an exclamation mark most people have not just cuz we love to exclaim our password as humans no because we're lazy the exclamation mark is on the same physical key as one so one shift one saves me moving my heavy hand all the way across the keyboard to press brackets or Asters no I'm a lazy human so yeah one bang one two three bang these are all very very common things okay that do not make your password stronger please stop doing them okay on to the next section rules and buffer limits so for this
we're going a little bit deeper into hash cats internals here how the ru engine works we have maximum par par lengths for a start there are algorithm imposed ones LM hashes maximum seven bcrypt 72 by input we do have fixed limitations when we cracking passwords we also have other things that are imposed on us I say imposed but this is actually hashcat really helping us out there optimizing things to make them as fast as possible for us in terms of the trade-off for computation in attack mode zero which is a standard attack and using optimized kernels d o that most people use and that's fine is 31 okay hard liit if you have a 32 Ash you're running in
dictionary mode with optimized for n um not for n for nd5 for example if you had the 32 character password in your word list it would not crack categorically if you running Dash because we have the sliit okay so what can we do knowing this if you've got rule sets especially rule sets you yourself have created and I highly encourage you to do your own testing there are things that we can optimize out that are redundant rules that result in no operations or no Ops for sure if we assume we've broken everything below seven characters anyway because the key space is just so small we can do it we're talking eight characters plus anything P3 P3 P4 P5 some through to p z
can immediately get removed same for Z O through to Z Z okay let's let's deconstruct P rules P will append the duplicate append the word an additional number of times R vanilla word is password okay password and P1 will result in password password append it once P2 password password password 83 24 P3 48 32 we're now over our 31 limit that's an operation hasht will only process the vill candidate okay similarly a um P2 z7 append the last character seven times results in 31 duplicate twice and append the last character eight times results in 32 that doesn't execute but we don't just get password we still get our P2 so each operation inside they're called Rule
operations and you can have a finite limit of these two generally speaking ask extreme edge cases but generally speaking the last op in your chain will execute cleanly if for example this one the p8 doesn't generally more often than not similarly D rules duplicate it duplicate it once append one two three we can see what's doing here easily this one gets a bit weird though because it says duplicate one two three 1 two three duplicate B but what duplicate here will do in the second instance is it doesn't duplicate the original candidate it duplicates the current buffer and the current buffer is duplicated 1 two three so we've got duplicate with one two three and then it will duplicate the
entire buffer again and this instance our final bang everyone okay with that one that's the one where people just start scratching their heads and looking at me like I'm very drunk uh there is methods to mad this though I promise okay and again just to just to kick we bang on to show that doesn't execute but it does execute the buffers differently okay oh and also um some people ask why pz so you can only index up to um 36 positions in hash from the start have 0 through 9 and a through z you cannot and we're going to touch on this very much in a second for this reason um that's why we have letters and numbers in there
another interesting one when the final length of your candidate is less than the intermediate length Okay so we've got no Ops here that we can optimize out make our rule sets cleaner here we have a rule which is prepend 123 okay and we have to do this in reverse order because we're prepending the carrot symbol in this case is prepend so we have to prepend in reverse order prender three then prender two then prender one okay so we can run that fantastic we have the password of super secure one bang prepended the actual final rule is here I'm just showing you in stages by the way if we then add a P4 to that a P4
doesn't execute okay so that's absolutely not going to execute that's a long pass already we're above 31 on our limit because we're running optimized Kels however if we prend 3 2 1 go out of bounds but then truncate the ninth character we can truncate the ninth character and that will still execute therefore rendering this P4 move redundant useless we can optimize that P4 out okay and finally I should probably give a shout out to these um uh rules at the bottom see these rules these tools at the bottom that can help you do automate a lot of the heavy lifting for this um juk rule has been around for ages um rule processor is made byaldi
one of the guys from the hash mob cre and it's a bit more modern a bit more optimized so highly encourage you to do these on large Ru set that you may have in terms of your own testing and um see how much you can optimize out okay position buffer workarounds now we're going to get a little bit more crazy but no one's walked out yet I am both grateful and amazed um we do have some hard limits 31 rule Ops so okay so we're talking about each of these operations you can't have more than 31 operations in a single rule first hard limit second of all that position buffer of 30 6 I said you can't index outside
of Zed position 36 from the start we can't index from the right if we don't know where the password ends but from position zero we always can we need to bear this in mind for this absolute gibberish here on the screen um again the last rule is actually the ultimate rule but I'm just stepping through it for clarity we have a password here um well it's a past phrase sorry it's a p clearly it's a pass raise with uh six elements in it okay that's good just to show where our index bounds are I inserted in position 36 an exclamation mark we can see where that hits so once we've got rules that can delete the last
character and that's all fine what I can't do is for example insert let me in in that position I can't because I can't I can't extend outside of my 36 buffer but we can if we kind of flip the script a bit what we could do is we could say okay I can't get anything past this exclamation mark so why don't I reverse the reverse the candidate and you can see the whole thing's been reversed then I'm going to insert in reverse order let me in and it's a bit awkward now I've put Let Me In with an exclamation Mar I probably should have done one for clarity you can see it's got let me in
in Reverse starting l l l e t m e exclamation mark n in position 6 7 8 9 10 11 and 12 inserting that in in reverse order as you can see will insert let me in in Reverse so why not do that and then finally throw another AR so reverse operate reverse again and you can see the result in C we're getting into positions where as time goes on and passwords get longer this could be more of a thing what's unlikely to be a thing in password cracking but is definitely applicable elsewhere is stuff like this so passwords aren't the only thing that's hashed okay uh domains get hashed Els get hashed and game reverse
engineering internal file names and file paths get hashed so whilst I've got a ridiculously long 97 character password Here I fully admit I've been lying to myself I said I was trying to crack 97 character passwords so uh bear with me for this example but we can sludge the left and sludge the right Chris Coss okay sorry sorry I tried to resist the chaa slide okay we have first 36 characters here just to Clarity we want to operates on the word this quite clearly we can't do that that's outside of our 36th buffer just to show where that buffer is again I've done an IED bang to show you where that exists okay let's slide to the left a number of
times is that 13 12 I don't know either way you can see the password has been slid to the left and then effectively appended on to the end and starts in now the word you want to operate on is within positional bounds I can insert a position 35 sorry not insert a place replace the character at position 35 with the number one to change this into this with a one and then slide to the right and here we are back again like I said less applicable in passwords granted but definitely applicable in other areas Markov chains who's heard of marov oh look at the hands Okay who wants to get up and teach it then that's
that's okay awesome um tldr um statistic probability of output of a character based on the preceding character it's kind of like the if you've got a q with the starting letter there's a high chance the next letter might be a u for example um through years of past where breaches and stud we can see the types of characters people choose and the types of characters that people choose afterwards and after that and we can build these up these are called marov chains Now hashcat by default a little lesser known fact uses marov based on Rocky by default so hashcat will never unless you tell it to do a completely naive unintelligent Brute Force as in a through Zed AA a a
that will never ever happen because hashcat like John the Ripper and other tools will actually help and do this for you but what if you want something something more targeted than rocky mean Rocky is great but it is a breach in 2007 and it's there are better lists out there which I can talk offline about but it's the one everyone knows so we have to tip the Box let's say I've got in possession a Minecraft breach and actually the Minecraft breach the life boat community in 2016 was one of the corpuses I used to develop one rule to R the more fly enough so this was a breach but if you've got a Minecraft breach and
you're an attacker I reckon that loads of the passwords like Minecraft breach might have passwords that are Minecraft related that would be reasonable to assume right yeah surely there those of kids making passwords about Minecraft stuff obviously okay so maybe running hash with this inbuilt default Markov table is actually going to limit us some okay we can work around this you'll never know if this is good until you of course but what we can do is we can say right what I did because the the stacks I show you in a minute are real I went online to a Minecraft Wiki and I downloaded a list of every Minecraft object monster like my kids love
Minecraft I should pay more attention really um every Minecraft object in the game I could find I know probably a few 5 600 maybe I then mangled that with my rule fantastic to get a really tens of thousands a really mangled list of passwords that are all based on real Minecraft thing shall we say created created a list out it stage one next hash utils again HC stat to gen this is a tool a binary for generating custom mark on tables I gave my resulting passw file to HC Gen 2 and generated a file H St 2 which then just du to Hash Cap's um support requirements needs to be compressed and when that's in a format
that you've got ready to go you can then pass that to Hash cap with the D- Markov HC snap 2 switch so now hashcat is not going to use statistical analysis B rock you to do its per position Markov modeling and you can see here we're doing a brw force in this case we're doing seven characters because I have a Lenovo ThinkPad and when I'm cracking properly I do not use that but this example it's on that with a with a real GPU and what we found was if you ran if I ran it this is 60 Minutes run time just an hour in an hour using just um just um Rocky just hashcat I cracked
12,000 less passwords than when I supplied my own custom Rule and all I did was scrape scrape a couple of wikis and then tell flash cat look at all these passwords and do some analysis based on the probability of the sequence of characters and use that to do your intelligent boo forcing for me and in 60 minutes you crack 12,000 more passwords okay so for targeted bleaches for targeted attacks so you got big custom word don't take a look custom Mar okay uni code oh the fun of uni code and emojis wooo we all love emojis um shout out to Y you did a talk um uh death come this year I I literally as
soon as the talk was over I found him and I applauded him it was brilliant um just a one liner to print out various UN code code page um code points so now we're talking about outside that nice comfortable asy area there have been times not many where I've needed to crack an Arabic password or a Greek or the hardest ones are always the Asian based languages like variance of Chinese and things it's absolutely horrible but all of these things fall outside of ASI they're all what we call utf8 so what we can do is go to ucfa table millions of them out there in this example we've got we can see the code points for Arabic
are 06 to 06 FF and hex okay so 06 to6 FF which I think is this second example here and it will just print out all the Arabic characters to fine easy do that for your language of choice for emojis emojis are a bit more painful because emojis use up to four UTF bites per character which is a pain you can see in this example Arabic uses two so the Arabic number sign whatever that is uses d 8 Z okay so for asky we've got one for UTF we have up to four bites of encoding depending on what we're targeting Greek and Arabic use two OT use four and there's many others either way we need
to show how we can create these symbols to set the scene for further attacks like this so hashcat again our Savor does accept unod characters to standard in in the top example I've literally quoted all the Arabic characters and then created a mask from my custom character set that I've created here and say attack two 468 character Arabic password please do bear in mind in this instance for Arabic it takes two botes to represent a single character so that's only going to be four Arabic characters because two of those you two of those bites is going to be a single character and you can get absolutely crack Arab passwords why the hell not um Windows has had utf8 support in beta for
approximately 700 years give or take one or two if you go into your Regional language settings and go to advance you can do enable UTF support beta um and it's it's quite useful for this kind of stuff or we can crack in HEX as well and if we're doing it in HEX we need to give hash CRA the hex charet switch so it actually processes these hexadecimal and if you were to go to this site or any site and look for emo emojis and look at all the um all the examples of four by combinations for emojis only the first bite is always F0 the second bite is always 9f the third bite could be one of
these four there and the fourth B could be any of that so again reduce our key space make sure we're only testing combinations of things that do actually exist L and in this example here we've got 1 2 3 four four times that would crack a password that contains four emojis in this instance we can also use um Unicode in rules uh we have to escape the X with a backlash prepend append do whatever you want prepend that append you are going to run into limits as to how much you can do before you get various errors that are all there due to how many values we can store in 32 and 64 bit integers um but it is fun it is good and
people really do use them I'm not joking yes I'm not going to see this on a pentest if I've dumped at I'm not going to be seeing this stuff because people aren't going to be typing this on their keyboards but you do see it even on outside of um active Direction environments people like to copy emojis on their desktop computers let alone people generating accounts on their mobiles of course Wi-Fi ssids with Emojis pop upy people love emojis now things on mobile so this stuff does happen this is real data I've not forged this okay these are these are these are passwords okay I need to calm myself down I'm getting a little bit too
excited I apologize I really love password um okay tesis um so tesis is an insertion rule generator again hash utils um thanks to Royce Williams who goes by TI hnus I DM him a few months back and he actually put in a poll request and then well he made the addition for me to allow Tois to support utf8 characters before that he didn't um but it's fantastic and what this does it generates this okay it doesn't generate that that's the crap it generates this so you give it a word list and it can it can splice one word list in with another to generate candidates like this you can see the word password Here For example is being
shifted through one through five there are limits to that unless you want to muck around with the Pearl you know go only goes up to 15 positions and there's other kind of limitations um but this which I'm not allowed to give you the code for but yanis promised me um it's going to be either in hashcat or hash utils very soon um for just single list insertion so you give you give it two word lists I mean I mean you could write your own I mean don't get me wrong this isn't black magic not to discredit Y she's done a fantastic job um but yeah give it a word and it supports Unicode and you can just see what it does and
then when you've got passwords like that give that to expander give that to Prince give that to expander and then expand it again honestly you go so far down the rabbit hole you will never see the light of day again it's absolutely phenomenal nothing gets me happier 2: in the morning when I'm high on coffee than watching some of these random password candidates come out with all manner of crazy passwords and if and those lucky elusive times what actually cracks yes my kids get woken up at 3 in the morning because I can't suppress the screens um but yeah use your imagination for those of you who haven't heard of expander and prints before today please please start
using them and if not any you need help with them please DM me I mean everyone's everyone's got my Twitter shout outs here I am more available on Discord um if you want help happy to help you right I like this one that looks like a pretty good password right everyone's smiling at me because they're they're seeing a bear shot being L and you're damn right hands up if you think you could crack this password of course you're not going to fit your hands up I've just set the Trap no one's going to actually admit to be able to crack that for all intents and purposes you've probably counted the number of characters in there that's not a
terrible password societally speaking based on we have we choose our password like right now summer 23 bang is being used Autumn 2023 bang you know seriously I kid you not for anyone who's seen the film snatch Vinnie Jones never underestimate the predictability of stupidity honestly I'm not going to tarnish humans with a brush but there are times where I'm sorry we should not be using the season and the year R over that would look like a pretty good password for all intents and purposes but would it surprise you to know that if you took the nty hash of that that asky string there I want to tell you that it appeared in 249 data breaches in
have I been homes pone password list that's a large inly High number of data breaches for that string to be inputed right yeah yeah no one's got their hand up now have they that's because that is actually the transliterated password for my password when typed into a zuin keyboard loud which is very popular in Taiwan so tyane users who are typing Myspace password will type in those characters and if you go to an online um zoin um keyo L you type in ji and it like present with 27 different tones that one letter honestly it was absolutely mindblowing but yeah it spells it out but this is actually a big big deal because it's the transliterated
password that's hash not the UN Cod character so yeah you see this and you just think oh yeah I ain't cracking that but this is actually a really really important thing especially if you're targeting passwords outside of printer baski and it also raises the very very important question and one I often get asked of but hang on password entropy is everything if it's got good entropy well yes okay blanket Cav I am not debunking entropy entropy is good okay really no seriously it's scientifically good for computer generated passwords that are absolutely 100% completely random completely random okay the fact is a lot of the time passwords aren't random and and for people who know about prngs and
CS prngs with a distinguish between that as well you know unless it's a reputable ratified CR csprng password managers whatever you want to Target it's not actually good let's take the entropy of this entropy is log base two of the key space 36 characters set there um we've got lower Alpha and numbers only 36 possible characters raised to the power of 12 the length that gives us with the log two 62 bits of entropy I've seen worse we've all seen worse that's not terrible but whilst that's fine mathematically societally for us entp is Quantified by how password looks you look at that and you think yeah that's got good entropy look at 62 bits yeah
cing that but this is kind of counter to that because you know that that actually isn't the best password I'm for reasons we've just shown okay so again not debunking entropy but entropy assumes that is a completely computer generated random attack which yeah give or take zero people do because no one goes a a a a a a a b a a a c no one attacks like that because all the tools you use use marov they're helping you whether you know it or not your are actually giving you the college triy they're giving you the Fighting Chance to really get those passwords where possible no one uses marov disabled test it for yourself hash
cat- A3 question mark D for a number run it by itself and it will print like 0219 it won't go 0 through N Run the same command with Markov disable and hash will print 0 1 2 3 4 5 6 7 8 nine hashcat is doing a lot of the heavy lifting for you okay so I'm not here debunking entropy but we have to make sure we're addressing and talking about entropy in the right context next when we are talking about completely random passwords which are actually RAR rarer than you might think okay because when you get into areas like this this isn't actually a crazy password okay I realized I probably opened up P
door's box now about cracking emojis Chinese characters and everything else um so I'll mentally prepare myself for whatever weird and wonderful questions you're hopefully not going to ask but let's move on to the last part of this hash upgrades okay you're responsible for an app you've developed an app you've been using md5 since forever because you're 72 years old and md5 was probably just around us fine you want to upgrade the security what do you do do you reset do you reset all your user passwords okay do you update your passwords and upgrade to bcrypt for example on the next login requiring you to store both hashes do you rehash the hash okay so see I told you I told you
this is my laptop that arrow is of course in in the Gap there on my laptop okay here's an example and absolute token shout out here to Sam Crowley who goes by chicken man want2 on Twitter but on Discord is just chicken man one of the core hash developers who did a fantastic talk in deathcon a couple years ago called what the shock we're building up to something called hash shocking which we're now kind of setting the setting the tone for here so you've got an nd5 let's say you want to upgrade your database by b crypting or md5 in this example we're taking in security MD filing it we're then B ing the md5 value
and here we have a result hash supports bcrypt of md5 no issues there and we can still crack that to get the play at the end no problems at all but let's speak about this adversarially in a real world and how a threat actor might go to use this against you we have a user here a happy go-lucky user who's who's created a pretty good absolutely not not uncrackable not at all uncrackable but a pretty good password there user because we're humans has Reus that password on S A and S B I'm seeing some nods in the audience already you know where this is going site one hashes Bob's password it's always Bob and Alice Bob's password
with SH 256 of the string fantastic site two BCPS a sh 256 of it okay these two SS get popped okay attack out has both of these if an attacker is able to go through an uncracked list of sh 25 sixes for example they might have bcrypt each of those values and generate the resulting hash they don't know the clear text password but they do now know the sh25 uh the sh 256 of the password that was used in the bcrypt process oh I'm seeing some like oh okay I'm seeing some n okay awesome which means this is brilliant news because we don't have to worry about running like a dog with three legs on bit we can
actually get out of bed in the morning and actually crack some hashes because sh 256 cracks a lot faster that's based off an RTX 3090 for anyone interested in the the benchmarks there yeah for anyone who's ever cracked be anyone no one gets out of bed for hashes when you've got when you've got the shadow file yeah great fantastic but bcrypt is really really really hard to crack it's very very GPU resilient we'll touch on this again later okay that's even with the default work factor of 10 you can increase that is Curr RFC to increase the defa iteration count work count of bcrypt from 10 to either 11 or 12 so this is very very powerful because
people are in possession of lots of data breaches can do this they don't need to know your clear text password they are mass enough uncracked ashes of a typ able to identify there's 100 ways could identify that they could look at how pone they could read a Blog that said oh yeah XY Z they got hacked you bcrypt the md5 fantastic I know how that was generated let's find every md5 I've never cracked and bcrypt it to see what there is there's aund ways this could go but if the inner hash okay this case sh 256 is very fast because you want speed increases and it's unsalted very important because the attack wouldn't have knowledge of the internal assult
that was used to generate um we can Shu off the bcrypt in this instance Shu it off and then there we go we've got now got the the inner hash the sh 256 or the md5 or whatever it might be but will I'm not a bad guy I don't do this I'm the pentester and I rinse ad day and day out that's good luckily we've got you covered there I say we I take zero credit you're clever team at hashcat I've done it um this was in uh this was a a bet version I used this has now been pushed to Main Branch so don't run the binary if you're compiling hash Source you now have all of these modes
in uh the main cash credentials were recently added so you would have this um commonly for pentesters in the room who all love to go in like me in the morning you've got a man in the middle six you've got responder the only two commands you've ever used while you go to get your first coffee you come back and it's rain hatches on your screen or you've relayed off to a 20 service and it's Happy Days da in an hour okay great but what about those hashes you don't relay those n m2s you don't crack well when you peel back all the layers in Windows World everything's an NT hash everything's n the Hood okay NT is used
to encrypt service accounts curb authentication ntlm challenge response the NT hash is used to encrypt the challenge NT is everywhere whether you like it or not so what I'm saying here is that when you are dumping ntds when you are running your ad Ram sacks whatever you don't crack never delete it and I'm hoping everyone's go oh no all the millions of N hashes I haven't cracked that I've got rid of when you're done dash dash left and output those you haven't cracked to a file treat that like your pop file don't delete it every nty hash you don't crack you could use to crack an NT mv2 in the future now in Windows world this is actually brilliant
because even if you don't know the clear Tex password of whatever this is that's fine but once you know the NT hash you can pass the hash business as usual a hash is as good as a password for so this is actually really powerful and again not an attack I'm saying it's going to allow you to crack every NT NL mv2 straight away of course it's not you to amass a file of uncracked enties first but this is literally cracking hashes with hashes you don't know the plain text but you can attack the underlying hash that was used to construct in this case n mb2 or the cach domain credentials okay hopefully that was a
bit of fun for everyone so we're going to wrap up uh on something that actually isn't password cracking but it's kind of like the whole Al so what should I use yeah okay go to oos that's fine that's great OS recommends in order Aron to ID with some memory requirements iterations single thread great scit really memory hard algorithm there and bit with a minimum of 10 that's good now B is an unintentionally cash hard algorithm okay if anyone who's done password cracking like in a bit more depth you might have heard things like script being memory hard okay it's a memory hard algorithm B is unintentionally cash hard now what that means is if we can keep the hash in
level one through three CPU cach before it spills over into RAM which is where GPU acceleration comes into its own because we we need memory to do GPU stuff but if we can keep the hash on the CPU before it spills over this is this is pretty getting we're talking defensively now this is like good protections honestly this is really good it's unintentionally cash hard now it's better than memory hard algorithms and there's good examples of this but only for Real Time authentication now real time authentication is generally denoted to be a second or less under a second is considered acceptable for Real Time author so in the examples of scpt Aron 2 for run times of less than a second only
yet bcrypt is better of course it's going to be a point where there's a me and a change over granted which is why these two algorithms which are very memory hard are good for General key derivation function work good for k yes but not for real- time authentication but then for those of you who might have looked into this a bit further and said well hang on there's loads of cash hard algorithm there's BS cpts there's puffer fish there's really good cash hard algorithms out there you're absolutely right but they are newer they're less studied bcrypt is bcrypt is bcrypt we know about bcrypt B cryts ratified tried tested and it's good and it's probably one of the
reasons I haven't asked him maybe I should why Jeremy Gosney kind of coined hmac bit um just over a year ago which I'm really hoping is going to get the uptake soon it deserves so this pre and post hases using H Max sh 512 and it uses it's an optional pepper but people are generally using a pepper pepper instantly means it can't be shared brilliant fantastic job done that's then base 64s it's then decrypted and then it's posted again using the same process this overcomes broken implementations this overcomes the 72 byte length limit that bcrypt natively enforces unfortunately for us yet our tools don't support HB bcrypt but hashcat does support script and John the Ripper does
support escrip and argon we'll get there soon okay I've got this in because it's free if this was commercial I would never be plugging it at all um we used to have a commercial training course called password cracking r one that we ran with black hills information security um we decided June last year to make this free um it's got a VM to download pre-built with 15 Hands-On challenges and answers 15 YouTube videos of my dlet tones over about 4 hours maybe enough alcohol will get you through to the end again it does cover not everything we've covered in this talk but it certainly goes into UTF custom masks combinator prints and other things as well so if you haven't you
know if you've not been enough G for punishment already and you're feeling a bit more sadistic please go do to the free site go to our website here like I said there's loads of free training on there and you can go nuts I think everyone might be a bit too scared now but um if you want to win a coveted insecurity challenge coin that glows in the dark you heard it here folks um only a hacking one I'm afraid because we're currently house offending ones um if you can crack that hash and the only hint I'm going to give you is if anyone's heard of checklists Daniel mea's top 100 but you need to think
creative if you can crack that hash and I would say tweet me but quite honestly follow me on Discord because I'm more likely to see it um you can win yourself a coveted Priceless insecurity challenge coin but on that note always be cracking okay um thank you very much and for anyone who still wants more we had a password CTF I released in 2018 the cryptocurrency prize is gone don't think you're going to eat any crypto it took someone four hours to swipe it you put a $100 of ethereum into a wallet but all the details are there if you want to keep the fun going and the coffee drinking um but yeah apart from that do
anyone have any questions yeah don't know who was first but go sir so with um people using pass phrases maybe they would select a pass phrase from a book um so assing you had the text of a book what be a good way to turn that into a CRA so for for for a targeted attack if you need to kind of have an idea of the book that someone's used there are alternative methods like one time grid there's also diceware diceware has been popular for a while and still is so for those of you who aren't familiar with dice wear you've got a choice of 7,776 words you literally roll dice and you choose five random passwords the key
space of which is computationally secure in terms of exhausting a key space with a book um again if you have knowledge of what that might be if I was targeting you and I saw on your Facebook linked in Twitter and insta that you loved water ship down maybe I index water ship down and you that adversar in terms of real life um I've seen it a lot in competitions um but you'd have to have pretty good knowledge of what the original forus was you knew the book I'm thinking like a sliding window but it would be variable length because you know how long pass phas is I was just wondering if there was a b already yeah
so you would do for that is if if you were if you thought it was a pass phras from a book you would use an example from an earlier slide you would probably use this one near the very beginning You' probably use this um but you'd need to augment it a little bit you wouldn't be starting with a mask you would in fact in fact there's probably a better way of doing this uh let's take this one forget the the rest of it you would index your book create a word start of it you give it to Clint you'd say element counts minimum Two element maximum count five six whatever you want to and then it would concatenate and
create two to six element pass rases you only terms in your book if you use Quint to do that and then pipes to Hash you could then run rules to aend that even further which possibly people have done o to zero you know L to one usual crap we all use but that's that's definely do it you canly define how many elements in your past arays based on your your Books Corpus yeah so emojis yeah of course um basically I noticed that in the a real that's only because that's only because and I've got no email addresses in this or anything actual personal OB I've looked at the passwords themselves that's only because the examples I've
used I made a prend list only and a pend list only and this case uh prepend append so it put an emoj at the start and end of each one so in the one cracked here they were only ever going to crack if there was a single Emoji at the end just in terms of the demo you could argument that out further and use multiple emojis so the question is is there any research or any kind of um data on how actually are used oh um quite possibly but I wouldn't okay that's more the actually more the human study of how they're used selected I would almost certainly say so but I wouldn't know I'm afraid I haven't seen
anything myself yeah oh I've got two minutes I'll do had two questions I'm getting all excited oh get out how you can't that's why youing I'm not a real P got real I could use v no no no yes so if I use ke pass to generate a phras six words that's probably good enough okay that's probably good enough now when you say use key pass generates it or you put six words into key pass oh key pass is it oh sufficiently entropic password yeah you're probably good you're probably good however um ke pass XC still has a current issue the clear pass dat the clear pass master password is in Ram not ke pass ke pass XC you might
even see the Tweet yeah is from Snow Crash yeah it was a couple months ago but it's still there I tested it on the most recent release key pass itself though good it uses decent algorithms it what's the is the default iteration count 30,000 or has it gone up I can't even remember it's it's painfully slow you're not going to get out of bed for a key pass Ash you're safe no good anyone else yes you recomended a book early on I did WR down hash crack uh it's current version is version three um it's on Amazon uh it's I think his name is Joshua Piccola I think his name is he goes by netm online really
really good it covers loads and loads of stuff like lots more than I've course course well worth it yes's the Special character set includes a dollar sign but on my UK keyboard I have a pound pound sterling oh yeah so is that going to be cated for ah so it can be cated for but it's a very valid point so um a UK pound selling sign a little bit of a it's like a bit of a Holy Grail because um the UK pound sign isn't part of the 95 principal Asing characters a dollar is but a pound isn't you have to spill over into extended Asing for that so you do you can attack it 100% but by doing a
question mark a for example or question mark s when signing masks you are not going to cover that keyspace no you'd have to augment the attack and then include that yeah yeah so you mentioned Thea model has users are models out there based on like Chinese characters oh um that's a fantastic question um I'm willing to say yes but quite honestly Janis is the person I would ask about that he's literally just done a talk covering that so um that there are but if you download hash Legacy hash Legacy has lookup tables simple tables off the elepant and you can use it to lookups of UT it's matched up to get that transliterated output so in the example we had down
here um you can do that kind of thing there where you can actually work out what that might be based on a zoo in or Mandarin or whatever it is your you're looking at on that kind of thing but I'm not aware of this Resort as a fantastic Mark for AG they love numbers they love numbers Chinese people on the whole one through six like repeated numbers for some reason again psychological study based on Asian culture who knows they L numbers which in itself is fantastic when attacking a really how yeah yeah well that stuff fascinates me too um probably more so from how to attack it point of view but yeah it's really really interesting culturally how
we select our passwords differently I'm prop yeah I'm I'm over time everyone that's enough thank you but please find me afterwards and I'll happily lead your ears more than I already have