Plundering and Pillaging Password and Passphrase Plains for Profit

Show transcript [en]
Thank you very much. Welcome everyone. Thank you for choosing to be with me because there's almost certainly a better talk in the other track. I'm not going to say what this title is, but try saying it 10 times quickly and I'll give you a sticker. Um the token, this is me. Um Will Stealth um I run a cyber security company called insecurity. Started off in digital forensics after my masters uh doing criminal forensics. So crime scene, bagging and tagging, analyzing evidence, going to court, putting bad people in prison, defected to dark side, pentesting and all the good fun offensive stuff in 2014 and have never looked back since. Um, lucky enough to have been a black hat trainer
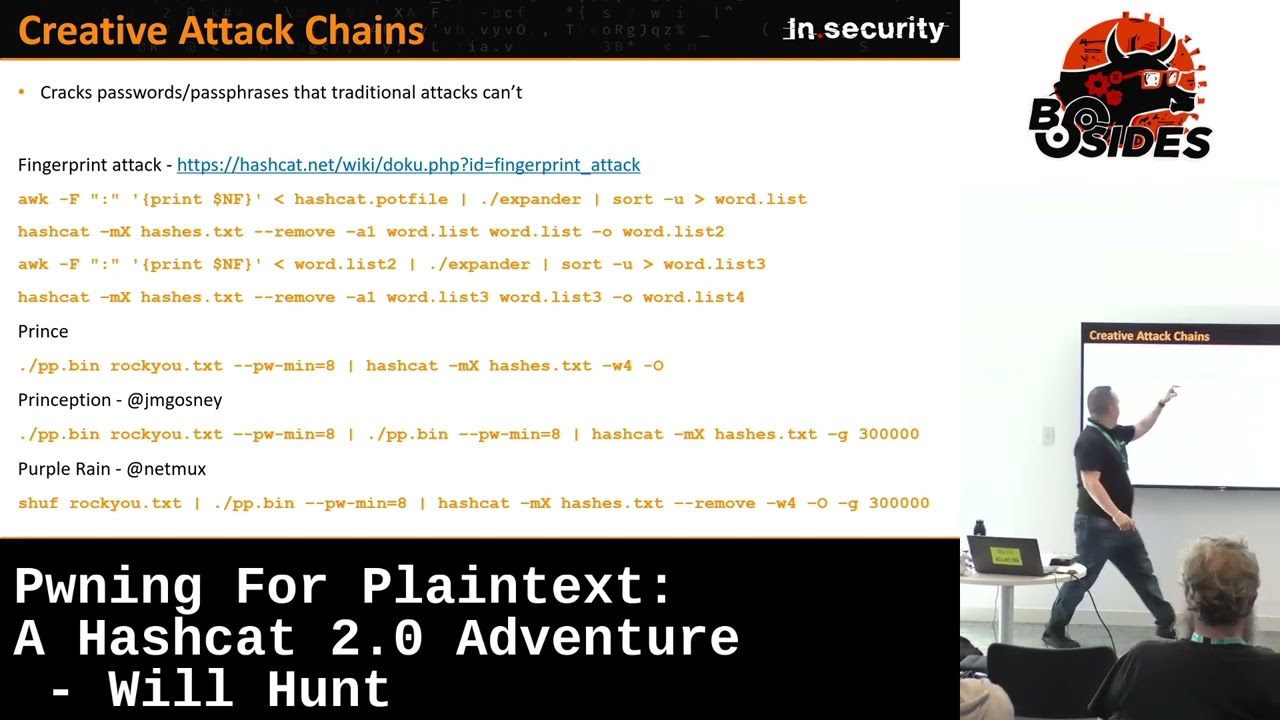
for the last seven years and I've been lucky to have spoken and trained other places as well. Nice to be at home for once. Uh, by that I mean in England. Um, the talked about passwords. So the second to last bullet point shouldn't be too much of a surprise. Big big password cracking fan. helped run password village at Defconom for the last few years. And yeah, let's let's move on. Okay, so we've got a bit of a journey. Um, lots of different things we're going to look at today. Um, we're going to start off with some unorthodox, creative, slightly non-traditional password and passphrase attacking techniques, things to really consider doing when your traditional kind of
wordless rule attacks fail you. We're then going to go on to some foreign language stuff and some fun. Look at some optimizations and wrap up with a little tool to help automate some of your non-distributed workflows. Right. You'll also notice this this symbol might be unfamiliar to some people. I'm a big hashcat fan boy. It's not the only tool that will be in the slide, but hashcat will be uh we'll be following this around. Right. Two element passphrases. Let's just get started. This is as kind of as simple as it gets. So when we talk about elements in a passphrase, we're going beyond the word password or secure or let me in. So 1 2 3 4 5 6y would be a
two elements passphrase. For example, hashcat in this case A1 is combinator mode. Take two word lists, match them together, and it will it'll mix and match all the uh words, all the candidates in list one with all the candidates in list two. Nothing untoward there, right? Let's start adding delimiters because you know what? Adding delimiters helps. Lots of people use spaces. It's the main one people use, but commas, colons, and things aren't uncommon. Also, we can just adopt the same command adding a dash j. So, hash allows you two single um rule um sort of entries here, dash j and dash k for your left and right dictionaries. And the dollar space is append space. So, what
we're just doing is take the top 100, insert a space, and then add again top 100. Pipe that hashgap business as usual. But we can also add rules to this like traditional rule sets that people use. So again, we can still insert our space, but this time we can just tack on a rule. Um I've got one rule to rule all still in here because I finally after a bit of nagging from other people revamped that in 2023. Some of you might have heard of one rule to rule them all. Um that's one I I made in 2017, but um there was a lot of performance updates. So it's the same performance, but basically a few thousand rules less. So
a little bit quicker. Um good for fast hashes. Don't use on things like bcrypt, script, anything slow, it'll never finish in your lifetime. Right, then that's two. Let's move on to three element passphrases. Okay, print processor. Another tool um doesn't come with hashgap standalone GitHub repository. It's a nice candidate generator. It takes a single word list as an input and then chains together n numbers of elements together and mixes and matches them. So if you gave it rock for example and said I want a minimum of three elements and a maximum of four it would pick three and four words in every possible combination it could your input list and chain them together. Rocku is
quite even though rocku is itself a very small dictionary. It would take a very long time to perform this kind of attack with it. So sometimes better for smaller more targeted target specific word lists. You can set a minimum or a maximum password length. You can set a minimum or a maximum element length and in either way pipe that to hashcat business as usual. We can make it work with our delimited list like before. In this example, we do have to pre-create our word list. So what we've done here is taken our top 100 dictionary and we've then created it with a space. We've inserted a space to the end of that dictionary. So every
line ends in a trailing space. Very important here because when we send that to hashcat-j with the closed square bracket, we'll delete the trailing character. So you're not ending up with a trailing space. Hopefully that makes sense. It will give you something akin to what you can see here. But again, without that trailing space at the end, I should be using my pointer. Look at that. Um to delete it with the dash j. But there are more ways we can do this. And there is another tool that comes with hashcat utils called combinator x. not probably as as well known as as combinator which itself is a binary that you can use to to take two words
together. There are pros and cons to using combinator X with prints. One of the flex one of the really good pros about combinator X is its flexibility with regards as you can see here um with variable delimiters. So if we take three files we've got file one, two and three over here. We can forcefully insert a space in separator one and separator 2. You could do a colon and a space or a space and a comma or whatever you want. So it allows for a greater degree of flexibility when creating multimited passphrase attacks. Uh prints unfortunately is a little bit more a little bit more rigid and you would have to have pre-limited word lists in order
to kind of achieve this. So if we bring combinator X back into our chat chains, this is how we might emulate a three or a four or however many you're going for um element passphrase specifying your first, second, and third lists. One thing to note with combinator X only allows you to use the same dictionary twice, the same word list. So if you want to combine the word list five times, that's fine. Just copy paste and rename the file because it won't let you do it otherwise. But you can still emulate this activity. Okay. What about case toggling? We're humans, okay? And password tracking, just like cyber security is a human problem, not a technical one. It's a
psychological study. And when we choose our passwords, historically we love to put a capital letter for the first letter of our our password. When we create passphrases, not uncommon, you might have three words, three elements separated by a space, but the first letter gets capitalized. Well, that's going to be tricky to do unless you you're using rules. And um guy called toxic, part team hashat, his real name is Janice. Um he's got the toxic 3 rule as he's dubbed it, which is shipped with hashtag and can can really help automate doing this kind of thing. The descriptions of the hashcat wiki are shown here. But as you can see on the top here, the three will allow you to
toggle the case of the start of each letter within a specific element after a given delimiter. So in this time, you see we've got spaces and the letters being capitalized as you go along. And similarly, we've got the e rule which will just capitalize everything down the bottom. So a single rule can then emulate that and you can of course attack a much much larger candidate in this process. So let's bring it all back again. In the full command, you can use your combinator X or your prints tack on a rule and then you can start to see different uh different case capitalizations. So I think in this one we've just got that Jose 123 where
there's a capital J you can see there. Um all of these excerpts by the way are done from data breaches or have been home stuff. So these these are synthetic. It's all kind of real life data um been using for testing. Okay. Engrams. Engrams are great. We should all be using engrams. There's your token Wikipedia entry. As you can see here, if you take a string of words, an engram is a sequence of these defined by a number of our choosing. So, if we take that string, B size leads is an awesome kind. We can look at it in two and in three gram variants, and it's quite obvious to see what you're doing here. Now, this is fantastic. Um, and
you'd be amazed at the mileage you can get by generating words based on engrams to attack your hashes. There great tooling out there that can also do it for characters and character sets. So you can slice up on a given number of characters and increment as you go along. If you've got password phrases that are quarterly in capitals, lowerase password, uppercase secure, for example, you can do character sets. These are called C and K gs and allow to splice an individual on individual um kind of boundaries of your choosing. So it's really really powerful. There's a couple of options there, but I would highly recommend going for grammar. Um it's much much more modern. It's very
flexible and it's it's really useful for generating these kinds of um these kinds of word lists. Now, as we started off giving a sentence as a demonstration, it's unsurprising that this kind of attack is great or large texts, things like the Bible, just as an example, the Quran. So, what I did was I took down have I been poems, which is these numbers are probably a little bit lower than they will be now because it's it's like a month or two old in terms of the number of hashes. But you can see just by looking through the hab and pone database in two through six gram with and without the toxic three walls to show about that case modification how
many passwords were found in their respective in their respective brackets there. And we've also done you know the in native Arabic as well. So you can see how far it can actually go just by generating these name ground word lists. So they're really quick they're really easy to do. You just need to of course source a list. So if you're doing a targeted attack or you know you're trying to you're maybe it's a maybe it's a password CTF and there's a theme of like films and movies download loads of films and movie scripts fine run your engrams on it you'd be amazed at the mileage you can get right then so again this this attack's kind of been
around for a while but I think it's been quite kind of underlooked and people aren't aren't using as much. Let's say you you taken a fast run and a load of hashes. By definition of a fast run, everyone loves rockyouut txt. There are so much better dictionaries out there, but we all love rock. So, let's stick to rock. Um, I ran rock with one rule and still generated a word list. Fine. Let's take the fs from that cracking session I got. Uh, in this case, it's against the game ego data breach, which I think was from 2016, 2017. It was a gaming forum kind of website thing. Um, and then you can separate the alpha and the non-alpha
characters, smash them both together in a combinator attack. People tend to use the same patterns repetitively. So, we're all humans here. Statistically speaking, when we've been conditioned into adding a number and a special character into our passwords, you're going to use one or 1 2 3. When we use a symbol, again, conditioned over time, these things that we've been told believe make our passwords stronger and don't. You're most likely to use an exclamation mark. And that's not even because we love to exclaim our passwords. That's cuz we're lazy creatures of habit. And the exclamation mark is on the same key as one. So one shift one is so much easier than dragging my hand across the keyboard to
find a bracket or something else. So this is why 1 2 3 bang and all this kind of stuff works. And this attack will allow you to extract all of the non-alpha kind of um punch of data with non-alpha data there. Smash them against all of your alpha characters and you'd be amazed at the things you can find. Okay, intermediate scaling masks. I quite like this one. Um interesting kind of use case. This isn't necessarily applicable to everyone all the time. Absolutely not. You need to know something about the password. So this isn't necessarily if you've done ting on a pen test and you you know doing your usual your usual workflow. But let's say
you have some idea about the password. You know it starts with a number in this case. You know it ends in a special character and let's say you know it's got some lowerase characters in the middle but you don't know how many. And actually natively that's kind of quite hard to emulate a hash cap. Um, but you can do it and there's a couple of ways with actually a very important but subtle difference. Um, what you can do is you can take your your first known I mean in this case we're using numbers. Take your first known uh put it into a word list with course first char.ext. You can then apply your mask. In this
case we're just doing lower alpha characters. The dash I is increment. That's very very important because it will start at one and scale up. Otherwise hash would just attack the number of L's you put there. standard out Pyth standard out feed that back into hashtapat and then apply your last known in this case a symbol with a rule. So this is in hybrid mode A6 is hybrid wordless plus mask you can get exactly the same functionality in A3 which is traditional brute force mode by specifying your number to begin with starting incrementing to a minimum of two only and doing the same thing. However, how many of these characters or how many L's you'll get will be more generally in
A3 mode rather than A6. And that's because in hybrid mode, you've only got a 32-bit integer as the buffer to store. So, you can hold a much smaller number. Your key space is going to be a lot smaller. Whereas in A3 mode, you've got a 64-bit integer. So, you can store a lot more in there and you'll get much more mileage before you overflow. And cash will cause error and tell you that. Okay. Marco changed. Anyone come across markoff before? Anyone done markup attacks before? Oh, okay. Right. I'm talking to you then, sir. Um, let's say you're doing something very targeted. Okay. Um, marker modeling is about statistical probability of a character based on its
position in the preceding character. Very high level example. If the first letter of a password is a Q, the next letter is more than likely going to be a U. Not necessarily, but could be. Um and you can do lots of statistical analysis on passwords to see the frequency and distribution of of characters and this is what it's all about. So it's again it's just that likelihood increasing that probability. Now by default hashcat uses rock as it internal markoff table. Okay fine again rock. Yes it's been around for a long time. Uh and that's fine but let's say you want something more targeted. Let's say you've got a data breach that's related to Minecraft. Um, and I use that example because there
was a live um, a Minecraft community called Lifeboat Greek. Um, I did some research on that when I was originally creating um, one to them all. Actually, um, it's reasonable to assume that if you've got millions of hashes from a Minecraft database that the passwords are more likely going to be Minecraft related. Fairly fair to assume. And the distribution of letters in said Minecraft passwords, it could well differ from how people have created their passwords in the database. So, let's generate a Markoff table. Um, I went online, found a few Minecraft wikis, um, downloaded every object, skin, mon, and I'm not a Minecraft player, so shoot me if I'm butchering terminology here. Um, as much as I
could, downloaded a Minecraft word list, ran it through one rule, created a nice big obfiscated password list. Cool. Fine. The next two steps are just to get it ready for hashcat. Um, hash us has that second um, second binary there. That's just to generate the markoff table and it needs to be compressed in a format that hashcat is ready to accept in fine but ultimately I then attacked the uh the hashes which were unsorted MD5 hashes so perfect test fed for this kind of research eight character brute force fairly standard but I assigned my markoff table instead of being hashcat use its own and after letting it run for just an hour the Minecraft markoff um
cracked over 10,000 more hashes. Now, ultimately, if you were to let both attacks exhaust get to the very end, of course, they would have cracked the same amount. Absolutely. This is about getting the best getting getting more cracks from your password list quicker because there's plenty of times where you'll run a session and you'll see in it and it says 27 days. I'm not waiting for that. I mean, actually, let's be honest, if people see anything over 10 minutes, they usually control C these days. It's amazing how impatient we are. People need to get better. Um, but yeah, this is about getting the most bang for your buck in a smaller time frame by using Marov. You can and you can
actually alter that. You can go deeper and say use the top X characters of a Markoff table based on a full 95 character principal aski set. Okay, cracking hashes with hashes sounds like fun, doesn't it? Um, let's say, let's take a step out of our password cracking adversarial hat. Let's say you're upgrading security for your users as an application and let's say you're using unsorted MD5 smack your wrists or SH 256 something else like that and you want to upgrade your security to something solid robust secure something like brypt which is a very well-known very resilient uh um algorithm to attack what do you do for automatic password resets do you get your users to uh
upgrade their hash on next login do you rehash the hash I'm see I'm seeing some smiles I'm seeing some shaky heads there's some good and bad ways to do this. Um, this builds up to attack which, um, Sam Crowley, who goes by Chicken Man, one of the team hashgat guys, did a great talk a few years back called What the Shuck? um, in Defcon. And this is about attacking underlying inner hashes. As you can see in this example, if you take an MD5, fine. But if you decrypt the MD5, let's say you use using MD5 and you just decrypt over the top of it, we can attack that. That's fine. In this case, hash cap's
got a motor 25600. And you can crack the underlying plain text. Fine. But this does actually present a vulnerability and issue for us. So, let's put this into context. We've got a user, very happy user, because they've got a what they think is a great password. It's not a terrible password, but absolutely by no means uncrackable. Uh hard to crack, but not impossible. And that user reuses that password on two sites. Fine. Unfortunately, people reuse passwords. It shouldn't be, but we do. Okay. Site number one uses a vanilla SH 256. Fine. Site two uses a brypt of a SH 256. Both those both those sides get popped. See hash caps popped up now just to see
see what's going on. Um now at this point the attackers got two breaches. They able to identify what the algorithms these breaches are. Now if they've got list of users email addresses they can almost certainly if they've cracked a faster hash and they have cracked it, they can of course test that password again. But that's not always the case. And lots of the time, most of the time, you end up with big, big lists of uncracked caches, N5s or in this case, SH 256s. So what you can try and do then is brypt those uncracked SH 256s to see if you get a hit. And if you get a hit because the B-rypt matches, you don't have a password, but you know
the inner hash. You know the the SH 256 that you can't crack. But even though you can't crack that and haven't got the password, it doesn't matter because now you can attack SH 256 speeds instead of B-crypt speeds. And let's be honest, if your password isn't really really simple, no one's getting out of bed to crack Brypts. At least they shouldn't be. No one's got enough patience for that. But SH 256 is is reasonable. But the inner hash has to be fast obviously or at least faster than the outer hash that you're trying to shock off. And it has to be unsorted. If the inner hash is sorted, you can't do this. Hopefully that would make make sense as to why.
But it's about moving into a place where you can attack um weaker algorithms that are thieves if the unintent pentest world which nine times out of 10 is where I'm doing this kind of stuff. Um and you can do it with empty hashes too. And I'm not condone you save client hashes by the way and make lists. They wouldn't be happy. Do not do that. Um but this this functionality everything under the hood in Windows Kus hash creds you made it empty. Everything is empty under the hood. And for those of you up on NT, you'll have heard finally after server 2025 and then 24H too much. They're finally deprecating NLM after years of waiting. They're only replacing
it with Kerus, which again has been around since the dinosaurs and has its own problems, but let's you know, it's a small baby step. But in in Windows, if you've got a load of uncracked NT hashes and let's say you've caught some NVD2s using respondent or six, whatever it is you're doing, you can then take those NT hashes to try and crack the ND2. Now in this case you wouldn't know the password. This is Windows. You got you got the NT hash paste is usually um I do know that the modes for Kerbras are have been worked on by chicken man and some of the other guys in the team but they're pretty low priority. So I'm not
going to say they're going to make it in task anytime soon. Okay. Uni code and transliteration. Anyone done this type of cracking before? Oh, okay. Right. So uni code lots of fun. Everyone just homes on the emoji straight away. And I get it. I do too. Um, we've got our 95 principal asky characters. Okay, that's that's that's fine. There's many many more characters out there than ASKI as I'm sure you're all aware. Um, in this example, we've just gone to a lookup table here and we can see we've got um 66F code points Arabic, which is the exert here shown in the middle. 600 6 FF just to print out the Arabic characters. Similarly, you
know, you've got 101 um Asian um character sets and when when you go into more Asia, some of them get really complex because UTF8 can store up to four bytes per character. Principal asks nice is one bite per character. But emojis, for example, they take four hex bytes, four UTF8 bytes per character. So, the ability to crack a pure emoji password, you won't be able to crack like 20 emojis because you have to attack four bytes per character. You're going to run out of key space and overflow very very quickly. Um just a one liner there from uh Yanis which I told him I totally stole from his uh from his great talk at Defcon just to
show you how he can bring this out. You'll notice down the bottom here for example Arabic D8 H0 is the Arabic number sign. So we've got two hex bytes per Arabic character which is pertinent for the um bottom example here for emojis in a second. Now whilst hasht can take native uni code characters in via standard in for example in the top it's not designed for that. It's designed to crack in hex, which I've got an example here. So, in this emoji example, we've got four custom character sets because if you go back to a lookup table, find the emoticons, emoji emojis, how they're referred to, and look down the list, you'll see they've all got four hex
bytes. And in the case of emojis, the first bite is always f0. The second bite is always 9F. The third bite could be 98, 99, A9, 9, or 9B. And the fourth bite could be any of them. So what you can do is you can paste the hex into hashcat. Make sure you specify hex charet. So hash knows it's attacking hex and then apply your mask. In the case of emojis, you'll see we've got 1 2 3 four four times. So even though there's 16 character masks there, that's only four emojis. That's cracking because each emoji requires those four parts. So again, your mileage may vary, but people can do it. People use it. We'll see in
the next slide. And you can use it in rules. So rules is a nice way of getting emojis in. Hashtag accepts it. You do need to um escape the uh X in the rules of the hex here. You can prepend, you can append, you can prepend or app end. These rules can get very very big as you might imagine. So uh try not to uh try not to go too far, but people use them in real life. Um especially, you know, people creating accounts on mobile phones, they I'm sure people have seen like Wi-Fi SSRDs that follow and stuff. Um yeah, they are a real thing. People do use them and and you tend to see
people love the love emojis. It's all about hearts and kisses when you're using emotion. I don't maybe I need to be a 16-year-old child to to kind of get that. Who knows? But um these are these are things you can do to help increase your chance of attacking you code. Um and if you if you were to look down uh if you were to look down this list for example, there are better sites for it and grab every single code you've got and create a big list of them. You can run it over your existing word lists. You can run it over things that you practically asked and you can create lots of different word lists that
contain these different unic codes and foreign character sets and all this kind of stuff. And then you can use that you can you can use literally assets. You can wild card a folder containing all of your stuff and try a few times. Mangle that because why not? And you can get some crazy stuff out of it. Again, all real passwords. Um, you know, I mean, some of these even like just dots for example, I don't know half of what these characters and languages are, but you can crack them. They do exist. And these are things that you're not necessarily going to find unless you're looking for them. Okay. Transliteration. I won't ask. Maybe I will ask. Who
thinks that's a strong password? By virtue of me asking you that, I appreciate no one's probably going to put their hand up, but if anyone if anyone doesn't want to be a liar and and own up, who thinks that's a strong password? We've got one. We've got two. Okay. Okay. It's good. It's good. I admire your courage and honesty. Um, right. Okay. Yes. It doesn't look like a terrible password. It uses lower alpha. It uses numbers. Okay. So, we've got a pool of 36 characters there to choose from. Okay. What if I was to tell you though that that password's been found in at the time I downloaded 890 data breaches. Um, taking the NC hash of
that. That see that's not that's very strange now. That's Yeah, that's very strange. And that's because those pass those those characters the actual transliterated password of my password entitled to Brazilian keyboard layout which is almost wholly Taiwan and potentially other um surrounding countries as well. Um now the translate password might be hashed. It's not always hashed. It might be. It depends on the keyboard, the h you're using how that's passed to the operating system. Um but again that looks weird as hell but it's actually a terrible password. And there's not some good reading on this. This is it's not new. It's really underlooked and under known about because we look at that and we think
solid password manage generated but it's terrible. It's a terrible terrible password. So what you can do is you can create lookup tables. We've got an example in a second where you can then attack translate passwords. Again if you're some if you're searching you've got data breaches and I use data breaches in my search and stuff. You'd be amazed at how many times you can find where the translate password's been hashed not the native text. Okay. So um old school method of doing this was hashtag legacy. So I mean you can still do it using hashtag legacy. It's called a table lookup attack. Um but uh a friend of mine who actually speaking to me about translate passwords and I was
moaning to him about hashtag legacy ended up uh creating this um lookup tool he uh wrote it and it's very quick. It's very nice and if you give it lookup tables it can then do this kind of attack for you in this kind of way. So let's take our base word list. Russian cerillic is fantastic for this. Really, really useful. Um, again, the quality of the source of your word may vary. There could be dodgy characters in here. Of course, you're not really going to know. Create a lookup table. Plenty of ways you can do that. Some exist online. You can install the Russian keyboard layout and start typing. Just press ABC D and see what comes out. Create your lookup
table. Get the translate of that. Okay, now we've got a load of gibberish. You'll invariably find non after characters in there, too. And for cleanliness, I just got rid of them. So all I wanted to do was get asky characters. So this was I can't remember how big my Russian word list was. Um but I got lots I got lots of transliterated uh passwords. I then threw that against that was other than it was I can't remember which one. And that cracked and yeah um I was like what the hell because you're not going to get those candidates in dictionaries. Of course you're not cuz they're transliterated passwords. And then just for fun because why not you can reverse
translate that lookup and then translate it if you wanted to. So in the first example here you can bounce that back to it as code and then convert it if you wanted to translate it sorry if you wanted to. But yeah it it's it's really really weird um but it is there and people aren't doing it. So this goes back to my rant about why it's a terrible password and again I admire the courage and honesty of the people who put their hands up because the entropy of that password 62 bits okay which isn't terrible. It isn't terrible. It's not where we should be at a minimum, but it isn't terrible. However, entropy, which does work, is a thing and is
great, only applies to machine generated passwords. No exceptions. By that, I traditionally mean password managers. But, you know, there are there are lots of ways to generate passwords with secure amount of entry. But human generated passwords, entry does not apply to because all it does for us is society quantify it. When I asked you who thought that was a good password, you looked at it and thought looks pretty random. So no, it's not. It's it's a terrible password. Um so we're not unintelligently brute forcing this. We're not no one runs marov disabled which um in hash would actually start a b c d a ab a b a ac. No one does that when you're brute forcing in hash and
your other tools. By default you're getting a leg up. You're getting a helping hand. You're you're being you're attacking with marker which gives you statistically speaking based on that table the highest likelihood of guessing those letters. So yeah, like I said, entry only applies to machine generated passwords, but it's it's good as an example. Rule optimizations. Okay, let's move away from attacks now. The maximum password length for um fast hashes in dictionary mode is 31 with optimized kernels, specifically optimized kernels. Um so there are some rules that we can remove because if you're guessing passwords at speed, you're going to generate candidates that are above 31 characters. Um and they're going to, you know, that could result in operations.
So in this example here, we're using the P and the D, which is the duplicate and append the duplicated buffer a number of times. You can see here on the left, we've just taken the right password. And if we run P1, P2, and P3, it's going to duplicate it once. It's going to duplicate twice, but 8 * 4 here is 32. That's above 31. So it's only the original word. Okay. Similarly, duplicate twice, add the last letter seven times. That fits into the 31 buffer. An eighth adding a D doesn't. So in the stop ration will occur there. Now if you're assuming you're attacking passwords that are bigger than eight characters things like PC upwards and Z0
upwards can be removed from rules because each of those is compute cycle. It's an operation. Similarly there's interesting cases where the final length of your candidate is less than the intermediate length. So the bottom rule is actually the real one. But I'll step through this to try and hopefully make it make it clearer. Let's say we've got the password of of super secure uh super seccure one bang here. If we were to prepend uh 1 2 3 to that, we could do it in the first rule and you can see how it comes up. In the second rule, we're then going to do P4, duplicate the whole thing four times. That's going to be bigger than 31
characters. It's not going to operate. But then we truncate at the ninth character in the last rule. That does drop us back under, but that P4 now becomes redundant. Optimize it out. There's no need for it. Uh again, two more tools. And I know it's the same guy, but he's done a lot of fantastic work. He's part of the Hashmob team. UV rule processor Y could really really help you do this and it actually helped me optimize one rule to rule and still further after I released it. So yeah kudos right then iterative hashing and case sensitivity. Now I don't have a lot of answers for these because there's weird stuff you find in data breaches.
Sometimes systems will store iterative hashes like a char one of a sh one of a pass for example. Yeah, if they natively store that, that's fine. But sometimes like hashes and weird things finds their way into passwords. Maybe stupidity quite often is sometimes there's an insecure generator where unbeknown to the user it's doing something very weak and insecure and for most of the time I just have no idea. Um like literally nearly all the time I have no idea. So a couple of examples of past data breaches here, all of which are vanilla MD5, single unsalted MD5. Um, and this is where I'm using a tool called MDX find. CPUbased cracker, but fantastic for big
big hash lists like in the tens of millions. Really, really good for unknown hash testing as well. Um, and you can see in each examples, we've got a cracker at the top, this L04, but when you look down here, you can see we've iterated it twice. The MD4 the first iteration is that, and then hashing the MD5 the second time gives you the resulting hash that cracks. So, there were only five in the first one. Yeah. Okay. Maybe there were five clever people who thought, you know what, I'm going to MD5 my password and then paste that in as the password. Five. Okay, reasonable 40 to this uh second one here. Already 700,000 uh users and that
slightly higher numbers. Yoku breach was a very big breach. 48 million MD5 hashes 692. Okay, more hashes granted, but that's not necessarily the most trivial number of nested hashes to find in there. Um, but when you look you look at the data, you can see the plain text is a hash. It's like, so now why is the plain text a hash? Is that real? Did someone was the data kind of polluted or dirty before it got ingested? You It's hard to tell and I don't really have an answer for you, but seeing hashes there, of course, you have to take that one step further. And they did in fact crack. So technically, that's a third nest if you want to think
about it that way. Really deep inside the rabbit hole. Uh, and there were actually nearly 11,000 triple neck double nested MD5s as well where you can see it's gone through the loop three times. So, they do exist. Uh, and don't just assume that you're working on an MD5 breach that every hash in there is necessarily going to be MD5. But NDX finds a great tool that can help you identify some of this stuff. Okay, even intermediate case sensitivity. Let's take the password of password. Cool. We all know that. No one in here has ever used that password. I have no doubt. Let's let's hash it. Uh let's use is the SH1 hash we're using but in this case
we're going to take the lower and the uppercase of the SH1 hash which is very very important. Now hash by default uses lower most of the time you see lower there are places actually uppercase hashes. Now if you then hash that a second time the final hash of course is going to be completely different because whilst the intermediate hash was the same the case sensitivity does matter because we're now hashing that again. So now I've got two completely different hashes for the lower and upper of password. And this one 353 E here you can actually see in the fourth row here. So that's the lower lower um hash here and the upper hash for the top 20
passwords of rockq double nested. Okay. So these are char one of char one. But just as an example, it's the lower and the upper. And you can see as you go around, hashtag is very pleased to hop around the screen and show you that both the lower and the upper were found this number of times um in have I been poned again at the time of a month or two ago. So it does happen where intermediate case sensitivity can affect the resulting hash. Okay. Password placeos, right? Um chicken man said, "What should you be using?" Yeah, Bitcoin addresses. I thought that's got to be rubbish. People wouldn't do that. Yeah. Yeah, they did. And I had a bit of a run. 172 Bitcoin
addresses I found. So these are the career tax passwords because, you know, we're need secure people who think that if I use my Bitcoin password, that is going to be uh good. So I thought, why not? Let's move onwards and upwards. I downloaded the 33 richest well populated Ethereum wallets and sure enough, a load of Ethereum uh passwords were cracked. But watch this. The observers of you might have noticed that not only have people use their Ethereum wallets, they've actually put one two three and exclamation mark at the end. Again, all these things that we're conditioned into believe make our password stronger. Wow. I mean, I was lucky. I mean, I literally just hand wrote a couple of quick rules
to add one 23 exclamation mark. All the usual kind of rubbish that we do. And yeah, I was amazed to find them. And of course, there's going to be more, but yeah. Um, so I thought, okay, what's next? We've done crypto. Let's move on to personal identification numbers. So I started researching the format and structure of not necessarily knowing like passports or anything like that. The respective national IDs for the countries. Uh and I'm also not saying that there's no awesome chance someone could have that format by themselves anyway. Yes, I completely can see that might be the case. Um but social security people do use social security numbers their passwords. I shouldn't. Um, but again, you can, you know, have
be interested, be inquisitive, think what's weird, crazy, and random, you should never be used as a password. Try it. Guaranteed if you throw enough, you know, throw enough water stick. So then I found this one. If you Google, and this is 2020, how's it going to rescue your password? Take the Unix epoch time stamp of the current date, shy 56 it, B 64 that, and then just take the first 32 characters. So truncate the resulting value if necessary. Wow. Okay, let's try it. Now I didn't generate from the 1st of January 1970. I went back to 2015 and I decided why not? Let's just try one shot in process. Take the first 32 characters and within seconds I got a
hit. I stopped it for the benefit of just the slide. You can see here this was the crack working back into my um my my generated word that I did to do it. and see where that was truncated from, what the resulting hash was, and converted it back into a into a date. So, someone probably at that time generated a password using a very insecure password generator. But I wasn't stopping there. I was stopping there. I'd only open my second beer. I was going strong. Science, why not download a list of chemical formulas, compounds, whatever. put that through prints. Uh, minimum element counter two and I went for a minimum password length of 10 just to weed out
some of the the lower stuff where there's a higher chance of it occurring naturally. Ran that through MDX find um just for SH one and yeah, science. We got I mean I killed it at 12 hours cuz I was never going to finish. But I got 121 cracks in that 12 hours. Um and as you can see I got some cool stuff. So if anyone wants to nominate me for a chemistry Nobel Prize for like you know compound discovery I will accept nominations. But some of these I mean it's up to you whether you think that these are passwords that could legitimately done. Yeah, of course there's a chance but there were there were you know there were more than what
I show on the screen and some of them were some crazy crazy compounds. So yeah, a lot of scientists out there taking their work home and then you keep on googling and you find the invariable stack overflow things where someone said oh I create memorable pseudo passwords with high level of entropy by starting off with a capital um vowel or constant whatever it is and then alternating yeah random random consonants and vowels. Right, let's just get into that. It's not the worst, but it's it's not high. It doesn't apply. Um, that's just rubbish. Sure. You know, it's not um but it's not rubbish. It's not susceptible to traditional dictionary attacks, but it's susceptible to very very simple
ones as we're going to find out. This is completely rubbish. Sure, passwords can't be can't be can't be good. So, yeah, just scripts generate positive combinations and again mixing matching off capital constant vow constant vow. Again, I'm not saying that all of these were a result of that stack overflow post, but you can find out random things and people will do it. Right on to the last bit. I think I'm still just about out of time. Automating non-destructive hash workflow. So, a few weeks ago, um I released hash catalyst because we don't all have massive GPU files. We don't all have hash top list. We don't all can't afford to farm out money for AWS and the rest of it. Um,
and there have been plenty of times where I've had stuff running on my local GPU at home, um, and I' want to go to bed at night, but I know the attack I'm currently running will exhaust in like an hour or two, and there's all that dead wasted time. And that happened enough that I got really annoyed. Um, I wanted something that could just automate and chain things together. So, there's a uh, bashcript Windows batch file variants. Um, you plug in a number of file paths, which I'll show in a second. Um, and then you can, these are these are the kind of taxs I've gone with. You can chain them together. And then some extra stuff because people
aren't generating good word list enough. Got some like some word list augmentation where you can use things like expander and cut B from the hash util suite to splice up and mutate both your word lists and the passwords you cracked to generate new word lists. Um so select 16 which is custom attack. I'll do a demo in a sec. Pick your chosen attacks and then wait possibly forever depending on how adventurous you're feeling. um inside the respective files. These are the file paths there set. So point it to your uh folders you want for rules. If you want a specific folder for nested rules, we've got it all out individually. Just make sure all your word lists are txt, all your rules
are rule. Um I've also included the lights binary from sinos prime which is fantastic for sorting and dduping. Whilst Linux does have and whilst Windows does have an undocumented switch for sort by it's garbage and you move outside of ASI and it just falls over. Whereas our light sorts and dupes beautifully. So it's included in there and it's by attack logging. So when an attack starts, it logs it. So it's quite nice to see the things you've gone through, especially if you've got like six word list 700 rules and you can see what started the start. Uh oh, and at that point I'll quickly live demo. Let's go for it. Oh, there you go. Let's
uh in fact, let's start this without just to show you. I'm going to delete my pop file. Okay. Okay. Pop file not yet created. Have I? Let's delete that. And attack log not yet created. Backup list. Right. So hopefully you can all see this. Right. Again, number of options here. You can always type 28 to show your current path, which I'll do just to show you that I'm using very very basic top 100 best 64. Really, it's a demo. All right. We don't need to worry about horse tower here. But let's say I want to do a custom attack and I want to do nested rules number seven, with a hybrid attack, three character incrementing mask with a full asky
character set. And then let's say I want to go yolo, why not word list with 250,000 random rules. So you run that and you'll see that when the start tracking they'll appear on the right up here. Up here you've got the attacks being logged down here. So you can see it's [ __ ] iterating through. Um three character mask here incrementing it will actually it'll log it. Now it it will log at the start of the attack. So you can't really do much in terms of what logging it completes. But if you've got like a huge world as a rule set and the time stamp is like 20 seconds apart. So it means a long hash
cap skipped over it. Maybe you've given it in helping your attack. Um and because all these all the rule based attacks with loop back as well. So loop back takes the cracks from your current session and feeds it back in to reapply the rules over the top of it. People, you should, if you're using any rule, always d- loop back. It's I don't It baffles me why not many more people are using this. And that will just keep going and going invariably until eventually loop back can't crack anymore. Oh, look at that. It's cracked one more on that loop. Two more. So now it's going to take those two cracks and feed them back in
for another 250,000 random rules. So with random rule generation, this could go in indefinitely. But of course, we're using very, very small words. Eventually, it's going to stop. But either way, we're still on this attack. I've only given it 72, which is as far as we're going to get. Needless to say, is that going to finish. Oh, it's looking promising.
I think we're on to a winner. >> If not, I'll squit it. >> It doesn't Well, it's because it's random rule generation. This is the beauty of it. Nothing like an on nothing like an on the fly on the fly demo. Oh, critics. All right. Either way, look, let's uh go back and have a look. You can type 29, show your cracked passwords. So, now it'll span out everything you've got. But now let's say you want to use those cracked passwords, those founds inside a word list. We can do that. Option 21, create a found list from your pop file. So if I type 21 now, it'll generate in the word list folder that I've specified, lists folder, pop
file.txt. So I can now go in and find that. And that's now got a word list that I've just done for my cracks. And I can go further because now I can do something that lets expand that word list. Uh expand the files that I've just done. 22. I've now got expanded pop file text in the same folder. Expanded pop file.ext and it's now spliced up using expander which by default has a length and len max of four. I've recompiled that for 10 I think in this instance. Eight's pretty good for mileage. And you can see how it's mutating a word list. Apologies about the profanity. This is the top 100 word list. Um and you can see how it's
splicing it out. So then you can take that word list, run that by itself or in combination with other things. We've got free training. Uh, we used to have commercial, we open sourced it a few years ago. If you're not sick and tired of the sound of my voice already, and you should, you can have four more hours of it on YouTube. There's a VM download virtual box OVA format pre-built with 15 hands-on questions and answers, challenges to really get your teeth into and get the practice. It covers foreign language unic code. We have an old CTF in 2018 where there is no cryptocurrency prize left either. So, have a go at that. And if you're feeling
daring, if you're feeling daring and can find me, you can win a coveted priceless insecurity glow-in-the-dark challenge coin if you find me. Um, it's not the simplest of things and it does use attacks that we've seen in this talk. All you'll need is the top 100 word list from Sepus if you're interested. So, take a take a picture if you do want to have a go at it. But I encourage you to enjoy the conference of course while you're here. But with that, that wraps it up. I think I'm just about done for time. And I'll answer your first question for you. Where's hasht? Don't worry, hashtag was not forgotten. But thanks very much for
listening. I hope you've enjoyed it. And obviously we've got time for questions. Great. We don't