BSidesCharm 2024 - Cloud IAM Strategy for Multicloud and Hybrid Environments: Risks and Gaps
Show transcript [en]
[Music] hey good afternoon everyone thank you for showing up it's a little late in the afternoon on this lovely Saturday um so you're probably still in your lunch coma you know or maybe you kind of want to go nibble on something I don't know just a thought um so thanks for for coming we're going to talk about Cloud IM strategy for multicloud hybrid environments which is a very long title uh but it's going to be a pretty long talk so buckle up it's gon to be fun so just for some introductions uh I'm Cassandra young my handle is muteki um I'm over the Internet I've been done a bunch of um different talks all around
Cloud I love Cloud it's my favorite thing um I'm currently a senior consultant at crowd strike in our services kind of Consulting Division I do Cloud security assessments which means I basically get to jump into someone's Cloud environment poke around find a bunch of holes and then yell at Executives about it which is really fun um so I used to also be a CIS adman so I have also suffered alongside um you folks as well who are out there as practitioners and that was my inro to Cloud um I also suffer through a master's degree in computer science which I'm very happy to be done with uh nine of 10 recommend except for the lack
of sleep uh and lastly I'm also a director at Blue Team Village at Defcon um where I help kind of put on some free content uh give trainings and talks for uh folks that come to Defcon and stop by The Village so that's me in a nutshell I am going to hand it over to my wonderful co-speaker Cosmos to introduce themselves thank you uh my name is Cosmos I go by Guardian Cosmos that's my full handle you could also call me Christian I go by both I'm the owner and operator over at indelible it's a security company that we founded as a holistic company I'm also a Sans instructor part-time um and I also do a
lot of community advocation and I advise a number of different startup um companies uh like my counterpart here I also volunteer at multiple conferences so you've probably seen my face in a various different shades of hair color because it's never the same this is probably the longest I've had a natural hair color uh in in memorable history uh so jumping right into it we like to start all of our talks with some topics and definitions about what we're going to be talking about today as well as just some baselining definitions here that we think are really important the first and one probably the most important for this talk because we're talking about multicloud is defining
what is cloud as you can see by our lovely Morpheus meme over here um it's really just someone else's computer right at the end of the day whenever you're using Cloud you're just Outsourcing uh hosting of that device to someone else and with it hopefully you're Outsourcing some of the risk um now as we're going to talk about later in this talk you don't get to Outsource all of it and you have different challenges that you have to overcome instead we're also going to talk about the differences between traditional or what we refer to typically as now as on-prem infrastructure how that interacts in a hybrid environment that's an environment where you're dealing with both cloud and on premise devices we're
not going to dive too much into this we really wanted this to be more of an intro to intermediate talk um we will probably be doing some follow-up talks where we get more in depth on each of our various topics later on um we also uh Shameless plug Maybe rele a book under no starch press um in the next couple of years as well on the same topic um we're next going to talk about multicloud so in the context of this talk multic cloud is really going to be referring to usage of any of the major Cloud providers in concert with another major cloud provider so in this case you might be using either Azure AWS or gcp
or a combination of all three or one or two of those and we'll talk a little bit about the different reasons why you might select each for example if you're looking for someone as a cloud provider who's got a little bit of everything is going to have the most diverse and integrated products said you're probably going to go to AWS if you're primarily hosting kubernetes apps and nothing else you're probably going to want to go to gcp uh and if you are primarily a Microsoft shop you're probably going to do something with Azure just because it's going to be the most integrated environment for the purpose of today's talk we're also going to talk a lot
about identity and access management as well as identity Federation for the context of this talk assume that identity and access management is going to be referring to management of the identity and access control systems and the different Federation ideas that go along with that same thing for Federation how do we handle getting separate disperate environments to handle the similar set of shared credentials and what are the best practices around that lastly we're going to try to tie all these things together and we'll talk very very briefly about some Automation and orchestration and how to deal with some of these issues um as we go through the
talk can I get this one on thank you just realize I'm like don't want to just stand here the whole time um so while we're on the topic of of uh definitions I think you know we're all kind of familiar with the the major three Cloud providers that's going to be AWS Azure gcp they're ranked in order of kind of what their market share is um you know we have a number of um of companies that we've worked with that have presence in one or more of these uh different um these different platforms and you know part of the um the draw for any of these is well probably budget that's probably going to be high on people's list um but
folks in in AWS tend to be focused more on development you know they're hosting workload applications um they were kind of the leader in this space they have the widest range of services uh offerings you know uh worldwide regions that you can deploy applications in so that's one of the draws for using AWS it's very developer friendly I personally like it for writing applications um I use a lot of like serverless microservices Lambda things like that which are more interesting to me than spinning up VMS so that's my preference um Azure you know we see a lot of folks uh using entra ID which is you know forly Azure after directory a show of hands for who
how many people in this room hate entra ID as a name I don't I don't get it seriously it's really really weird um but then a lot of these you know companies as well you'll have that like M365 your Office 365 email integration so it has a huge market share mostly related to that and also has the ability within Azure itself to host you know workloads uh virtual machines things like that um so you kind of get that like you know everything's Under One Roof it's almost like Microsoft's kind of developing this this Walled Garden that you can use if you stick with Microsoft products gcp is the Wild Wild West as I like to call it it's a lot
more fun and it might be also fun to exploit for there any red teamers who've ever dealt with gcp there are some really really bad defaults but it's also really fun really flexible um I I personally kind of like that it's a little bit rough around the edges like it's a lot fun to work with um and it's a great space if you're working with containers kubernetes um you know any of those like any anything that's um that's going to be more on the serverless side gcp actually does really well it's also a lot more budget friendly so a lot of orgs move to it for that reason and then I'm going to hand it back over to Cosmos
to talk about your own cloud all right so we've talked about all the major commercial Cloud providers obviously we didn't name all of the majoral commercial Cloud providers there are some other clouds out there Nvidia has theirs now for a lot of the GPU intensive workloads as we've seen the of llms yes I very specifically chose that terminology I refuse to use the other one for various reasons feel free to ask me about that later I have a whole rant on it um we're also going to talk about some of the other options available to you so what if you don't want to side with the major Cloud providers well you do have some other options available to
you first of all you can go with the commercial Cloud stack so all three of the major Cloud providers being gcp Amazon and Azure all offer varying flavors of methods where you can actually virtualize all their services in a hybrid or Standalone format on your own devices so Azure for example has Azure HCI um gcp and AWS also have their own proprietary solutions for those for the purpose of this talk we're probably going to talk a lot about Azure just because that's already going to be in almost everyone here's environment show hands really quick how many people have Azure or Office 365 in their environments okay so for the purpose of this talk we're going to focus a lot
around some of the Azure stuff um and entra IDs as your primary source of identity um you know in later talks we'll talk a little bit more about using things like OCTA um or other identity providers you might be using AWS Cognito for certain things in your applications um but that's a little bit beyond the scope of this particular talk um the other options you have are things like owncloud or nextcloud so these are really great if you're only really looking to um commercialize on your existing email and calendar and contact syncing or file syncing they're not really great for if you want to have like a managed SQL server or something like that so your last option in the set
in the category of running your own cloud is actually to use some of these Gateway orchestrators now that is not a term you're going to find everywhere it's just the best term that I found to describe uh the series of things that you would do here so there are a couple different utilities there's a popular one on GitHub right now called print tunnle spelled p r i t u NL again it's a little bit too advanced for the scope of this particular talk but if you want to look it up for extra homework feel free it's a solution that's B based around a VPN into your Walled Garden being your private Cloud infrastructure as well as
allowing you to manage via a unified portal like you might be familiar with with any of the major Cloud platforms your actual underlying infrastructure it grants you some user access control it's not the only one there are a couple of other good options out there um feel free to search on GitHub for building your own cloud you'll find tons of different things you'll find open tofu or terraform formulas to actually build those environments on some of the existing clouds if you just want to play around with them or if you happen to have a home lab with a proxmox server or you know a VMware array or any of the other virtualization Solutions please do
feel free to try that at home as well it'll work on all of those um so that covers off on Gateway orchestrators I'm going to turn it back over to Cassandra for our next topic thank you very much and honestly I hadn't even really looked into this the idea of like your you know your own cloud and all this stuff before we talked about doing this talk and like hang on what what is that and if you don't know what it is so don't feel bad it'll it's it's like the the Next Generation thing we're you know eventually going to know all know about yeah definitely less common so I mean I work in Consulting so I usually work
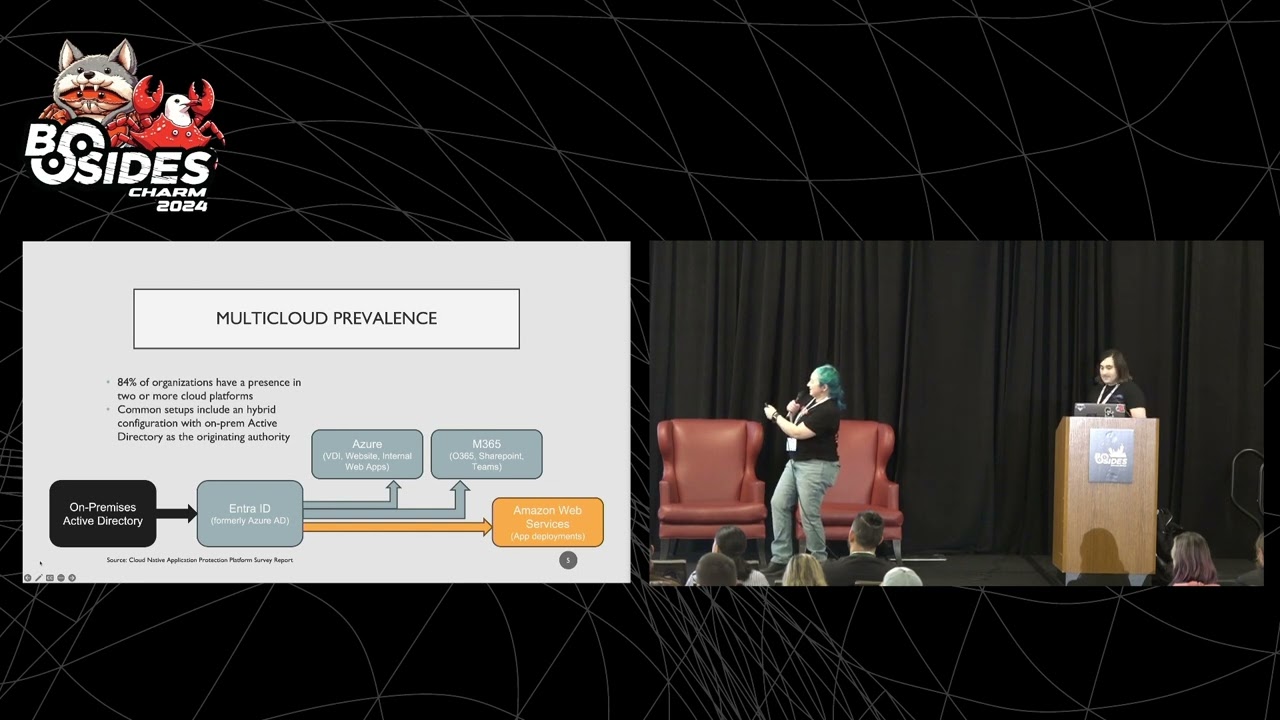
with bigger organizations or some some small to mediumsized businesses say and they usually have like a common set of of patterns that they follow in terms of their maturity in terms of their multic Cloud environments so um pulled some fun statistics 84% of organizations have a presence in two or more Cloud platforms um I extrapolated from this based on my own experience and folks I've talked to as well probably the most common thing that you can actually see and I realize that white text on blue background is terrible I'm gonna fix that later um I'll just side note we'll be posting the slides on GitHub afterwards so I'll just tweak that and then you'll be able to have all this content you can
just download it and fill in the blanks a little bit um so the most common architecture that I personally see in my day-to-day covering Azure and and gcpa on the side as well is uh my you know my client has an on- premises active directory infrastructure so you know users groups um you know uh computer objects complex OU infrastructure all that fun stuff um that's you know active directory and they probably have some other backing systems workflow to get users kind of provision from workday for example into that act active directory environment and then they're using something like um I want to say a connect and I don't think that actually is the term anymore forgive me I usually
look at the cloud only side um and that is going to flow into uh the the very nebulous uh box that The Black Arrow points to which says entra ID formerly Azure ad um and you'll see that out from there we have three arrows so a common kind of uh setup for an organization would be one of those errors points up to that first box which says Azure so Azure is platform uh infrastructure is a service hosted VMS cloud storage you know managed server instances uh or SQL Server instances things like that um that's the platform side that would flow out from entra ID uh and use it uses entra ID as the identity Source the
other arrow is going to point to M365 which is kind of like on the other side of that like set on the other side of of azure is going to be uh where M365 is going to be your Office 365 you have SharePoint online teams which is really honestly just dropped hot dropped on top of SharePoint anyways but you know it's a separate service so I'll call it out um so those are all of your Microsoft hosted services and then on the other side you'll see we have AWS so we're in this case a lot of organizations are going to use that entra ID as an identity source to flow into um Amazon web services to have that Federated um
integration so this is a very common example of use you know a multicloud organization that you know is kind of federating everything through Entre ID and behind that act of directory so uh just to briefly again I'll be posting a slide so I'm not going to get too into depth but um there are some really interesting statistics that show a really high increase in the amount of cloud-based intrusions uh so 75% increase is pretty significant this is just 2023 I'm sure it'll be even more this year there are there has been an explosion of cloud Savvy threat actors um you know one example like on the bottom here we have 29% are cloud of are
of cloud conscious cases where the in where the Intruder knew that they were going into a cloud environment 29% of those are attributed to scattered spider AKA whatever UNCC 3944 or octo Tempest if you like Microsoft's really weird naming convention I don't it's fine I also work for crowd strike so I might have a slight bias there um but you know another one like I think it's pretty obvious to say like this 84% Cloud conscious intrusions attributed to e- Crime actors that means they're after money they're they're not politically motivated they're not nation states and I mean in I I don't have any statistics to back this up but I can look at it and say like if an
organization has the kind of money to invest in Cloud infrastructure they might have you know a decent amount of money that can be extorted and that's kind of a common pattern you see in these intrusions so when we look at the threat landscape when we look at what's actually occurring with these intrusions kind of one common theme that we see is that they're really primarily going to be from exploiting valid credentials so your social engineering attacks you know your uh leaked credentials your lack of MFA you should all have MFA please my God please um and so some of these vectors going to include fishing um stolen compromised credentials business email compromise also a big contributor
and like that section alone probably adds up to like like in do math like 40% of of compromises and I call out Cloud uh like these Cloud misconfigurations at 11% it's that's actually lower than you might expect like the cloud is not insecure by default it's insecure because humans go in and like make things easier for themselves I think we can all agree with that um and then malicious Insider at 6% I think contributes too because when you have IM am like designed in a way that that has excess credentials and excess privilege you can kind of if if you get someone smart enough they can go in and find out a lot about the environment just using
you know all the access that they might have that they don't that the user doesn't actually need so I would almost say that Insider really is a kind of an important thing to think about not just because of the people behind the attack but what they can do once they're in the environment and then uh it's also worth noting that um IM am and the ability to privilege escalate extends the lifetime of an attack so that's kind of an important factor too and then the last thing I I'll say about this particular topic is multicloud adds complexity shocking right completely shocking multiple clouds clouds complicated multiple clouds yeah I know pretty obvious um but I think it's kind of interesting um you
know I I was looking for some more like hardcore CR some hardcore like um statistics around this I didn't have an easy time with that but I think um you know seeing that like the average time to identify contain data breach is a little bit higher for these uh use of multiple environments I think that makes sense intuitively um cost of breaches is also higher I think that again correlates pretty well so I think it's worth saying that like you know when you take the combination of presence in multiple clouds and identity and access management you've got the perfect kind of boiling pot of uh of stew for for something going completely wrong if you
don't have the right controls in place so yeah so so now we're going to get into it and uh I'll just say you know we've got there there are gaps and there are recommendations around all these strategic uh recommendations or strategic kind of angles on these different topics so decentralized identity source of Truth is that really does not flow as a sentence I don't know where my brain was at when I was saying that um but it's you know I'll go into a client environment and oftentimes what I'll wind up seeing is they might have something where they have like active directory entra Ed Azure and it's like it's pretty clean it's documented maybe not completely accurately but there was
an attempt um and then on the side they've got like gcp and Google workspace and it's like nothing but ad hoc users like they don't know half of who's in it they have no idea why that person is a super admin wait that one doesn't even work here anymore it's not a good look guys it's really not so that that kind of comes up as a as a huge strategic Gap when we have these conversations um you know accounts manually provisioned like you're also asking users to if they're you know you're feder you're you're not federating individual users you're asking people to have to memorize another set of credentials and like they can't even get MFA right like you really
expect a memorized passwords I don't think so um and then we have some you know inconsistent application of privileges again why is this person super admin they don't even work here anymore why is insights going to a Gmail address I have no idea so you know recommendations around that are like basically sit down and and actually architect what this should look like and I can't really tell you there's one exact way to do it there just isn't it's it's not going to ever work like that um but having a process of figuring out like what are your edge cases you know what kind of users you have what other service principles you know are in the
environment that should be probably Cloud only like you know having these discussions at a high level before you get too deep in the weeds of implementation and aren't able to actually you know roll it back if it's not done in a way that's making sense for your organization um you know defining and documenting everything I almost put that on every single line because it is so important like when I have conversations with organizations it's like do you have a defined process for you how you provision users usually they do usually they do sometimes they don't but like is the documentation accurate a little biger room there um you know and the same thing with privileges we want to make sure that you
that you're defining what users need what permissions which admins really need Global admin in ENT ID hint hint pretty much none of them and then lastly ensure that your security controls are baked into the processes for provisioning uh next I just want to call out service account sync from on Prem you almost never need to do this you really don't and I see it pretty much constantly there are very few use cases for this um so while you're architecting around you know wanting your users to come from a centralized identity source and flow into the environment you don't need every single user you should actually actually limit what accounts get synced over what devices get synced
over and really kind of like map that out what that's supposed to look like based on what you're actually using oops um and then some edge cases you know you've got like contractors's role changes I asked the question of organization like tell me about what happens when you provision a user someone starts they're going to be you know a Dev or something like that they get onboarded in workday there's a couple processes you know a service now ticket gets generated they get put into an active directory group that group syncs to Entre ID blah blah blah blah blah they get provisioned into Azure great they get some some roles assigned they leave the company and they're like
you know the companies usually say well the account gets deactivated in workday and the whole process works backwards what happens when someone changes roles does anyone does anyone here think that their org might have a little bit of a gap in that yeah see some enthusiastic nodding this is almost always like the pause in the conversation when it comes up because you know if you have an A Dev working on one project and they get moved to another project if you don't have a clear process for how that that privilege moves then they might wind up being overprivileged if they just get manually granted additional roles instead of their existing roles being reevaluated so you kind of always want
to look out for those edge cases um so you know enforcing your uh cloudon service accounts with you know as much as possible um defining and documenting yet again I'll say it a million times uh your processes for contractors you know you can align them with your normal users if possible if not create a standard process that um that encapsulates their needs and then uh implementing regular entitlement reviews uh that'll help with the uh like the kind of role changes and other like odd edges um you know reevaluating permissions things like that and then weeding out stale or unnecessary privilege accounts using tooling and entitlement reviews we'll hold for questions at the end and we're actually gonna have a
little more discussion too hopefully if I if I don't talk too long yeah I'm like oh look at the time um so just another quick thing to call out um you know I see a lot lot of cases of minimum like not really enough logging and monitoring this one's always going to be tough who here is concerned about the volume of logs in your Cloud environment yeah yeah it is not cheap so there are strategies to work through that so some of them would include you know uh pre-filtering um a lot of cloud environments will will have you know stream logs to either like a pub sub thing in gcp or um other technology and
you can basically like filter out the ones you actually need and just export those cuz the costs are going to hit you on the the um export from the environment so there are some ways around that but logging and monitoring and actually customizing your alerts because that's another thing that we don't really see enough of uh will help you kind of catch any abnormal behavior or you know egregiously obvious intrusions a little bit earlier so we definitely see that as a kind of a common thing that comes up um yeah and I think we just have you know there's never going to be enough visibility into Mis configured I am permissions and that's something where I can't really
advise people because I don't know exactly what the use case is so you have to kind of take a little extra time to really evaluate that and um I I mean honestly I would say like use tools that exist out there like cspm are really you know great at having some even even out of the box capabilities to like look at the roles that you have assigned and say like this is very privileged does it really need to be over like disprivileged so um you know that you know make make that cloud security a joint effort between existing tools and Cloud native capabilities uh and then one one last thing I'll I'll call out I think before
I I'm gonna hand it back over or maybe not I don't know have I got one more there yeah keep charging along um particularly about this so um I think the one of the the main issues I see is like when talking organizations they still have this on-prem mentality like the the amount of times I've heard lift and shift I I hate that term so much it's just it's it it like makes my skin crawl it's really bad um but there's kind of this this mentality of like well we have this way that we do things and now we're just using a different technology to do the same thing if you get stuck in that
mentality it's really hard to adapt to the unique challenges that cloud are going to throw is going to throw you away and even worse if you're in a multicloud environment where you just have this excessive complexity that you know and each cloud has its own unique issues and its own quirks so it's really difficult to to bring an nonpr mentality to that something that is just so completely incompatible um you know human knowledge I yeah it's it's incredibly difficult to have to get Cloud resources to get people that really know cloud and then you find for one Cloud well technically sometimes those skills are transferable I like to think that they are on a conceptual
level but when it comes down to implementation they're very different um yeah and then you know just documented processes having Cloud specific cific processes is often an issue as well and uh did you have anything you wanted to add that I haven't covered no I think you did a really good job both everything just for people who are wondering we do have a reference on the slide to where all the statistics came from but if you are interested in those statistics you can find those in a combination of the crow strike threat report as well as the panamon Institute report um which is the cost of data preach report it's put out every year in conjunction with IBM and
their red team yeah there's some really awesome reports that I I was like I'm reading this report and I actually like it this is weird wait a report that's not fluff what shocking and then please I love diagrams so brownie points for thorough upto-date diagrams please give me all your diagrams so before we move into the next section I really had to put a little Barney Sanders in there we had to ask you at least one more time you know at least one more time all right I will hand it back over awesome thank you so uh we did mention that this is a more intro intermediate level talk so although this is a more technical
session um of this talk uh it's not going to go as deep uh as some of you may expect we're not going to go through any examples today um we will try to post some of those uh later on uh along with the talk slides so the first thing you got to do is pick your poison so how many people here by show of hands would prefer to do role-based provisioning with groups how many of you would prefer to do it with arbac and direct role assignments less of you okay so uh there's a really good reason why there's a difference in that dichotomy and um I'm not going to say that any one group is right or one group
is wrong because you're both right um so there are advantages and disadvantages from both approaches uh with group-based provisioning I generally like to advise customers that if you are having a group of consistent and when I say consistent I mean always reliably consistent I.E I have a tier one help Des person they always get the same exact roles that's a really good use case if you have a large to use a group for your access provisioning if it's less than 10 people that role is probably a privileged role or it's a role that's less commonly used or more specific to a particular workstream you may be better off using a direct assignment with role-based provisioning why in terms of management
at scale you learn run less of a risk of one confusing the group or reusing the group and two especially in modern identity providers which have abandoned um the hierarchy so to speak that many people were used to with ous and duus inside of classic on active directory those Concepts don't really translate well to Identity providers based on cloud systems for example the stack for your directory inside of entra ID is actually much flatter in nature then even though you can Nest groups it's still flatter and it's not hierarchical right so there's a big difference there and that can impact the way that you want to provision roles and lead to things like over-provisioning which
we'll talk a little bit more about on some of the extra slides the other reason that you might want to use role-based provisioning over group based provisioning is it definitely is more granular like I said if you're using a privilege role or depending on what identity provider and Cloud combination you're using there are various advantages great example as I mentioned we're going to talk a lot about Azure um and entra because that's what most people in this room are probably using as their primary identity Source um in entra we now have the ability to provision roles in Azure to specific resources from within our identity portal inside of the entra portal right so not only can I provision
administrative roles for Office 365 Administration but we can now start to provision things in Azure and that uniformity removes a lot of ambiguity that you have with other identity providers when it comes to things like assessing claims so whether or not you get a token in a ooth or a saml type response you are always going to have some form of claims that tells you what roles and groups you have now there's some downfalls to that um one being if you have a very large organization and you have users that have a lot of claims you may run out of space um and you may have to combine some of those claims um you also may need to transform some of
those on the fly in your uh requests for compatibility with various systems so there are reasons why you might go both directions and your biggest choice is really going to come down to what cloud am I using and what identity providers am I using and what is going to be my ultimate source of Truth do you want to add anything to that yeah a great uh choice for arbac is your Global admins please do not provision those by group and please don't provision more than five it's bad don't do it also please don't don't give service principles Global admin and also in addition to that if you have money and you know who you are when you have
money please please use privileged identity access management controls and Pam Solutions especially for your admins and also make sure that all your admins are named please do not share admin accounts unless you have another method of tracking them I cannot tell you the number of breaches that we've both encountered in our roles where there is just an account and we can't figure out who did what went on it because there was no attribution ability so let's talk about some of the inconsistencies that tend to exist when you are doing provisioning and assignments inconsistency is a big problem why depending on what cloud providers you're using in a multicloud scenario right the role and the permissions granted by each role are
going to vary they're not always the same what is true for AWS may not be true for Azure or gcp and vice versa now there are a couple roles that do match that and are the same across all platforms but some of them don't exist a really good example of that we mentioned earlier one of the best use cases to use gcp for is if you're looking for an autoscaling kubernetes cluster uh they have a service called autopilot it is much more cost- effective than using say ECS or eks on AWS where you're provisioning a pool of traditional VMS as opposed to a autoscaling array where you're only paying for what you're using instead of paying a fixed price for your
pool size right so that's a really good example so if you have an autopilot administrator role on gcp that role will never exist in AWS it will never exist in Azure there isn't a comparable compatible technology on those platforms so how do we deal with that um in many cases people don't so instead of using a single source of Truth being your IDP of choice right many people will choose to actually manage and provision each of these accounts and roles individually across each of their clouds and identity providers this leads to our inconsistency problem here because you can't map it up it's hard to find one single list you lack visibility I'm going to use the buzzword that everyone
hates so cross it off on your bingo card you know single paint of glass that doesn't exist um in fact up until recently um recently being defined as the last year AWS had no way for you to view all resources across all regions they only introduced the global dashboard last year now I just want you to think about the fact that it is 2024 they introduced this in 2023 how long has AWS been around right um and a huge problem that we see in cloud is a form of attack Vector is if I compromise a cloud account for you what do I have access to everything I have a whole Cloud environment I don't need to
leverage and hide in your existing resource when I can spin up any resource of my choosing and the only way anyone's going to notice is when the bill changes and if I'm really clever and I use containers and I use the always free tiers you are never going to find those assets why you probably don't have a good asset report for your Cloud you know I'm just going to ignore the fact that you probably don't have one for on Prem either for the sake of this talk at least so we've talked about inconsistency in terminology we've talked about inconsistency in technical application um we also got to talk about the role and functions of scope as I
mentioned it in my autopilot example right your scope of what permissions are granted and what those permissions can do is going to vary between your different clouds do you want to add anything on there just 100% accurate so now that we've talked about some of those challenges let's talk about the Big Bear in the room how many of you have had to deal with Federation I hear the yays the size and I can tell you how many of you are actual practitioners who have used the cloud based on how many groans I heard and where I heard them from so when you're doing Federation Federation is the idea that I'm going to take one set
of identity from one service set and I'm going to try to reuse that in some Fashion on another parallel set of items now the problem is these are not the same controls so during the process of federation in many cases you're going to use some kind of Transformer a Transformer is essentially an on thefly method to say you are a member of this group which translates to this group over here it's basically just a big case statement right many times that'll be governed by your IDP and in some cases it'll be governed by the product that you're integrating with because it'll be part of the role mapping so that leads to a lot of very interesting
complications in Federation for one going back to our prior slide inconsistencies in naming conventions in scopes of permissions lead to a lot of federation problems because if I am a person who's trained specifically on AWS and I walk into a gcp shop and I think that I'm going to use the same set of accounts and roles to grant that access I am I am in for a rude awakening because it's not going to match up there's a couple other problems here as well collisions what happens when there's a name Collision what happens when there's a reserve name there are a number of reserved names not many of which are actually published um so the only way that you'll find out that you
have a collision problem with your role claims is one of two things will happen something will break or you'll get popped because it's overly Broad in a very very rare third case you may get an error message but unfortunately uh if you are fortunate enough to get set error message you're probably not going to understand what it means we also have a problem with over-provisioning what happens when an account has a different footprint on each different service again let's say I have a very large AWS footprint but a very small Azure footprint I may find that the group that I'm using to provision that set of roles does not make sense to use on Azure because those
roles will never be used so now I've over-provisioned access for an account that'll never be used the other problem is what happen if I Federate an entire identity directory is Joo and accounting ever going to log into an ec2 instance probably not if he does there's something wrong right maybe like an avd streaming workspace app or other virtual desktop but definitely not just sshing into a Linux ec2 box I think that's probably Beyond most anyone in many accounting departments apologies if I have accountants in the room so we have over provisioning right I've now created a stub account via Federation for users that will never log into that cloud provider so that comes back to trimming down how you Federate
your data and making sure that you're only federating accounts that will actually be actively used it also creates a lot of noise when you're trying to do incident response attribution or detection because you have so many accounts to Now sort through that are inactive that it's hard to figure out what might make sense or what might be relevant for your active use case we also have over abstraction so over abstraction is a proxy of trying to solve some of the other problems on the slide right so let's say and again it's a little beyond the scope to into the details of using a orchestrator platform like terraform or open tofu also feel free to come talk to me about
the difference between the two later on um I have a whole other slide deck just for that um but that also leads to some visibility issues right so visibility go back to my ec2 dashboard instance right now if I have that much trouble with Assets in a singular cloud provider what happens when now I have a single cloud provider and then I have a second cloud provider and then maybe a third cloud provider I've gotten a directory provider I've got an IDP and I've also got my on-prem am I ever going to have a clear asset inventory probably not can I get close maybe how do we solve the visibility issue we're going to talk
more about that so we've talked about some of the technical gaps we've talked about the provisioning so let's talk a little bit more about arbac arbac is hard arpac plus lease privilege on disperate systems it's harder right why why is it hard well we talked about a number of the issues right we have different roles across different platforms they have different names they have different Scopes they have different claims they have visibility issues it's hard to have a single source of truth right so one of the best things you can do is pick a single source of Truth for identity if you're an Azure shop it's Pro in an Office 365 shop it's probably entra ID
if you are using OCTA it might be OCTA right and from there you can then decide do I have a big enough use case on my multicloud environment to manage that particular very very small scope again going back to the kubernetes example if I'm using gcp and the only thing I use it for is autopilot in a kubernetes cluster I might be able to manage the roles locally without requirement for Federation in just gcp because that team is very strictly scoped and no one else should ever go in there and I can set up an alerting rule to detect that someone that's not on the authorized team tried to use that access right and then I can
triage that appropriately so that's starting to get into the how do we solve so we start with exraction layers we start with normalization we consolidate dashboards we for for lack of a better term we get a cspm right we we need to do some Cloud security posture management that'll help us with managing our configurations that'll help us with consistency across different providers and it allows us to create uniformity and you might say to me I can't afford a cspm I bet you you can there's so many great free ones we're going to get to some on the last slide we have a resource slide um where I've listed a couple links to a couple uh waza which is a great great
implementation of osc for HIDs and nids if you're not familiar with it has recently added some Cloud provision capabilities and there's also a new tool that's being co-sponsored by oosp that will be released as an open- Source cspm this year at black hat so it's another great thing to follow uh full disclosure I'm not involved with that project I just know about it um and if you Google that you will find some of the initial slide decks already available online so the other thing we can do is we can create common lexicons and custom roles now custom rols are scary right custom roles mean that I'm going to develop a role I'm going to give it my own naming
convention and I'm going to assign a series of permissions to it and it's a lot of work and a lot of people tend to do it wrong but if you do it right once it'll solve a lot of problems going forward and again going back to something muteki said earlier documentation please document your stuff processes for everything you define the process please and make sure that you are going to use that and that it matches reality please do not be one of those orgs that writes some beautiful documentation and then I look at your org chart and nothing makes sense it doesn't add up if something changes in prod make sure you change it in your
documentation we're looking at you every one of the major Cloud providers out there right now whose documentations are all wrong and lastly as I mentioned create additional tooling so when it comes to this right to put it bluntly if you want to be take the honors there design and Doc doent please design and document your implementation thoroughly and accurately if you take nothing from this talk walk away with better documentation please it'll save you and every consultant you ever hire a lot of headache and a lot of work and it'll save your org a lot of money um so to close out we did want to put a couple resources up here um and we
did want to leave a couple minutes at the end for any questions uh that you guys might have so I'm going to go very quickly over the resources on this slide what each of them is uh again we will be making this available later on on uh M's GitHub uh so please feel free uh to go ahead and look for that later um so the first thing we have on our tool list over there pick your strain uh depending on who your uh AV provider or identity provider of choices you may have access included in your existing subscriptions to a commercial cspm for example if you are a crow TR customer you have access to Horizon if you are an Azure customer
and 365 customer and you have an E5 license you have access to Cloud Defender which does a hell of a lot for you and Defender uh for those of you who have been in the AV game for a very long time uh you will remember the days where a Defender had really bad rule sets that were very not useful um that's not the case anymore they've gotten a lot better over the years um now you might look at open source tools things like Prowler uh Scout Suite cloud sploit and scuba gear these are all some really good open source utilities you can find all of those on GitHub and use them for free to assess your accounts
today each of them has a different format of reporting um Prowler and Scouts are probably I would say and you know feel free to chime in probably the top two that we see used most often and get the best results from they also do have some advantages uh both Prowler and Scout Suite will let you write your own custom checks and rules so you can uniify that to your organization and then in terms of orchestration uh open tofu and terraform I'll will be really brief because we are we are running out of time here and I can talk about the difference between those two for a very long time the most important thing to know is open tofu and
terraform are the same thing Hashi Corp just decided to be not very nice and change their business license agreement uh for using terraform so some very nice people uh decided that they were going to Fork the last open source version very similar to the elastic search debacle um and created open tofu so they are intercompatibility
um but open tofu is now sponsored by the Apache and Linux foundations uh so they are committed to remaining permanently free and open source under a consumer friendly license um in terms of some links that we have over here we do have some links to Some Cloud utility repos um awesome cloudsec Labs we'll give you a lot of different Labs uh and some plans to deploy those labs if you want to play around with Cloud we also have the Cs Suite up there we have a link to the prowler GitHub repository and we also have a link to the awesome Cloud native repository again again it's another great resource with a bunch of different Cloud resources included there
and lastly we do have um our reports there I have a link to waza I have a mention of Magpie we don't have a link for that yet because it's not live um until black hat this year uh so definitely keep an eye out for that and last but not least we have the two links to the reports that we've used so with that I'm going to turn it over back to mki and we can um answer any questions thank you very much um yeah absolutely I I personally don't like Scout Suite um I think they're little like interface have to load that's not programmatic is it's not that great but I am a huge supporter of
Prowler I love it um so I think we we had some discussion points we wanted to talk through but I think we only have about like five minutes in so I just want to go ahead and just take some general questions I think you had one earlier go ahead useres way what we do is what I've seen done is deprovision them completely reprovision them completely correctly is that over or is that actually the best way to do it it's it's better than not touching it at all way to do it or good enough I think that's it probably has something to do with like it depends a lot it depends on who your cloud provider is what level of
orchestration you're using and who your identity access provider is and what the skill set of your team is in some cases if you've got a lower skill set team and you've had some Consultants come in and orchestrate everything for you you may find it easier to just deprovision and Vision um but that's not always the best because that can have some very vicious side effects depending on any other automations or processes that are around it could also be time consuming and impact you know work time um and consistency in that transition uh in the back wait way over there yep you
for anyone that didn't hear that so um one like if if there's a workday integration then having workday a workday change trigger the the process to actually reevaluate permissions or to reassign them that's a good work around for that I think it really depends like how much integration do you have is it going to get to the point where it hits like the identity provider but it doesn't like reprovision once it passes from like active directory over ad connect entra and into Azure for example so it's really a matter of like how technically mature your your organization is and how like locked down those processes are but yeah I'd be worried about like if you have enough
integration where like you know you deprovision reprovision user like is there something else in the chain that might like get a little a little messed up there uh over here yep thank you documentation in the room give it up documentation for the win every time living documentation documentation of code um recipes my favorite thing ever entitlement management and recipes please use them infrastructure of code is one of the best ways to make sure your documentation always stays up to date anytime you make a change
sure uh so so one of the more complex use cases that we were actually talking about last night is when you leverage something like an orchestration platform
um and then fine grain that based on the different resources you want to provision into so for example using either terraform or tofu example I might Define a resources file that just defines all of my users and how my users are going to be loaded in from an existing database connection or a spreadsheet which will have a different field which will flag you know what provisioning should happen that in turn can also be used to generate live documentation either a notion page a Confluence page if you like Monday and Monday docs I mean there are Integrations for all these tools you can do that as part of your change control so if you have automations in J or if
you're using git based work Flows In GitHub uh you have lots of options with workers to help automate that and that's why I say you know infrastructure as code as your friend because that's going to help take a lot of that burden away from you it also can address some of the provisioning issues we were talking about because if you're using entitlements management you can use that to manually Trigger or I'm sorry automatically trigger periodic access reviews um that'll be performed by managers based on how you have done the organizational chart inside of your identity provider and just to walk it back like take a little bit more abstract from the Strategic perspective or like looking at it from a process
perspective like you know um putting a a lot more thought into like designing how roles are supposed to look like what what these processes look like and taking time to actually like socialize that process between you know your despar teams it's always the question of like how closely does the security team work with the cloud team you know is it like a war every time they they want to do some kind of change well the more process and strategy you incorporate early on in that in that in that life cycle then the easier it is to to make small changes and to actually U have them be properly implemented and like that would tie in really well to having
like let's design how these roles are supposed to look and then we're going to write terraform code or open tofu code to actually like create them for us and then they'll kind of be there and it'll ease everyone ease everyone's job um I think I can take like one last question real quick anyone else uh over there
that's a really good question um right now honestly if if you're dealing with blockchain because of the CPU intensity that you're looking for your best bet is probably to look at either uh making your own uh with your own infrastructure so again a little beyond the scope of this talk um getting into that that one slide we had where we talked about building your own cloud and your own orchestration layers that's definitely one option if you want to run your own data centers or if you're okay to use your own orchestration portal and you just want that higher level of Automation and control and customizability for your own users you know you may write something or adapt
something open source custom um in house to manage the resources existing on another Cloud um alternatively you may explore other more gov Cloud friendly options that might be better for that but specific to blockchain you're probably going to want to try nvidia's new Cloud offering today because they just have the most access to you know their own gpus at the better rates uh so particular to blockchain if you're looking to build your own private wallet Garden that's probably one of your best spots to look outside of building your own data center well thank you all thank you very
much so as as mentioned slides will be up on uh my GitHub uh probably within the next couple days so check it out I'm on the Twitter I refuse to call it X just like ID it's a terrible name um and then we're both on LinkedIn on the various you know Medias and all that fun stuff thank you very much thanks so much stay tuned we'll be releasing additional follow-up talks and books at later conferences





