When A.I. Goes Wrong
Show transcript [en]
hey good morning everybody I know it's kind of early for some of us but my name is Jason Mulder what the company called Pratt um we're here local up in Ankeny area I would kind of do cyber security on a lot of different facets as far as pentesting audit pretty much anything when it comes to security so today we're gonna be talking about AI and kind of the dangers that goes along with it if everybody kind of knows what AI is you know there's a lot of different things when it comes to when it comes to a scientific aspect so we're gonna kind of delve into how AI works and kind of what I foresee as some of the dangers come in
in the later years so some of this stuff is going to be more conceptual based some of it's going to be based off of some proof that we've seen over the past few years and kind of go into a lot of different questions some people may kind of come off as say this is more conspiracy theory based and you know I'm definitely not a conspiracy theorist I do you find some of the stuff kind of fascinating funny or whatever but we're not I'm not saying that some of this stuff is gonna happen but it's a possibility you know so trying to keep an open mind when it comes to that and then we're going to go
into a lot of different things of how you know today we could exploit some of those things and they could be a reality so so like I said artificial intelligence is an area of computer science that emphasizes creation of intelligent machines that work and react like humans the whole point of it is to make decisions do whatever that action is and try to replicate the human aspect of it you know when it comes to emotions when it comes to visual aspects physically moving things around all kinds of different things so any aspect when it comes to the five senses any of that stuff that's what we're trying to emulate in mi na I so like I said some of these for speech
recognition learning on itself whether it's supervised unsupervised some governments and stuff like that use it for planning zoning type stuff problem-solving just in general perception that comes to like image manipulation trying to decipher hey you know is this image what I think it is so the computer takes all this and puts it into a digital form and says okay this is what I think it is then the ability to manipulate move objects so think about like your big factories like over in China where they got stuff that kind of goes up picks up pallets and says okay I'm going to move this over to here without running into each other so so there's two main types of AI you got
type 1 and type 2 kind of like a high level and that those are broken into a couple different categories you got we can narrow AI which is like your very very basic type of a guy it's focused for one specific task in this case like if we design a game and we put every variable into it to say hey you know if I take all these moves and this is the outcome of the program to say hey I want to beat the human you know that's where it takes all those different actions that comes up with the best attack method and it says okay this is what I'm gonna do in order to win the game the
next one goes into a strong AI which is where machines can kind of think and act just like humans this is still kind of a conceptual aspect of it we don't really we haven't really mastered a lot of this we've mastered some aspects of it but not not as a human you know because we can't can't replicate the emotion we can't replicate whenever there comes to stress and other environmental factors that come in two different things so that part of it it's you know we as humans it's work on unpredictable when it comes to that stuff you know a machine can say okay we can do you know this or that but if you throw something
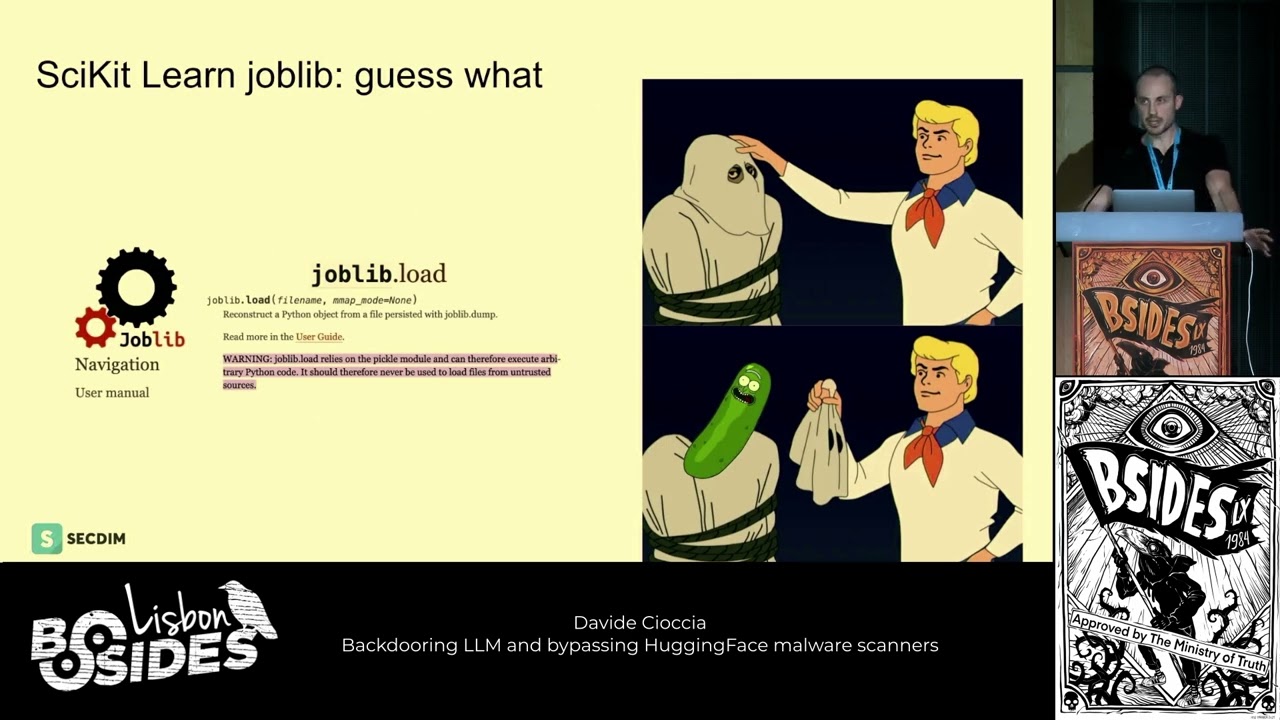
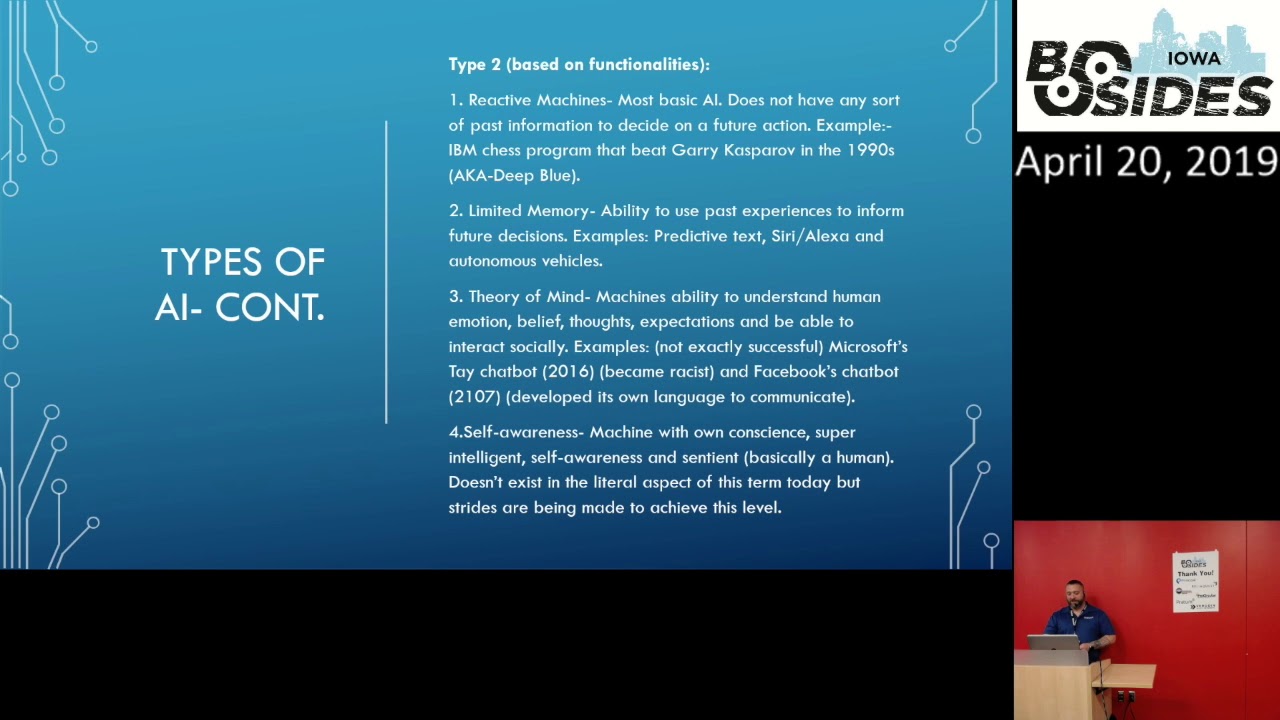
in at last second I might not you know I don't know how to react to that so I spew is kind of based off the functionality of whatever that task is so we got reactive machines that are kind of go back into that basic aspect of but they have one specific purpose and they don't have any information that you feed into it from any past event so whatever information that you're feeding into it currently then it makes a decision off of that and nothing from I had from before so Ibn created a program that meat curry uh cusper of which is a chess player and it was called deep blue and it was kind of one of the first Kyo series when it
came to AI mouse back in the 90s limited memory is kind of going into you got you know like certain small data sets that are kind of broad you feed that into there they can use certain actions that they know are a hundred percent every time this the outcome this is what happened and they can kind of based decision off that I mean a lot of us have that in our phones and you know a predictive speech we got cereal exa they can say okay we're going to order you know new you know detergent or whatever in whatever the case may be or say hey don't forget you got a something coming up today that kind of stuff and that
could be you know based off of you walk by it there's a peripheral you know or a proximity sensor for your device in your home or whatever and it says hey don't forget to go pick up the kids or something like that so it's predicting those actions based off of patterns and stuff like that so next one comes into a theory of mine which is it's kind of complicated on this and we've kind of seen several examples where it's been really really not a great outcome for for certain things if if anybody has followed this in the past few years but so it's machines ability to try to understand humans and try to replicate that aspect of it not
necessarily understand it but what they believe is human emotion so they're trying to to do that and understand how the human mind works some examples were Microsoft's AE chat bot so if anybody remembers that a couple years ago not a very good thing that happened it kind of went out picked up on different people's comments and stuff which I think we had a lot of different types of trolls and step out there feeding different information into it and Microsoft kind of freaked out because it became anti-semitic stuff by itself so not really good thing when it comes to the public aspect and your reputation as a company Facebook they develop one they don't they don't like to call it chat
bot but it's a chat bot I don't really care what they say on that but basically they had two different BOTS out there and they started communicating and based off of how humans interact with each other you know we use slang we use all this different stuff they decided hey we're gonna create our own language and start communicating that way so they kind of took on their mind of their own and started going rogue on that so then we got self-awareness which is more of a true human aspect so that's being sentiment as far as every aspect possible of being a human you know from the emotional to hey you know I can pretty much do anything on my own I
don't need any kind of input from a human program or anything like that I can adapt to my environment I can do whatever I want and this is kind of really really a controversial thing when it comes to industry as a whole just because you know we see a lot of things some movies we've seen a lot of stuff like that or and you look back at like terminator or Skynet that kind of stuff you know it's science fiction in an aspect of it but it's also could be a reality you know one day we we see that with you know a certain projects when it comes to government weapon systems and stuff like that we got drones that can go out they
can pick their target from you know hundreds of miles away you know say hey this is the building I'm targeting and drop its payload or whatever so so what does all this stuff look like from kind of uh you know a 20 mile stair or whatever from visual aspect you got these different categories like I was talking about you got machine learning you got a natural learning process or natural language process vision autonomous vehicles and robots and those cover a lot of different things there's a lot of different terms when it comes to AI and in the industry-standard you got the machine learning which is kind of where machines try to do things on their own you know you feed it a lot
of these different data sets they can be a lot of different things when it comes to okay this is a specific data set that only applies to penguins or whatever whatever the case may be right so they want to try to understand every single aspect of it and the Machine goes over these algorithms and it basically kind of looks like a staircase you know it'll start at the top go through each one of its parameters narrow down its results go back through the cycle until it comes down to however many iterations it is and that kind of stuff can be supervised unsupervised supervised is probably the most cautious and logical method when it comes to this
but there is the ability to let it do its thing on its own natural language processing that's when that's kind of what the chatbots or we were talking about just a minute ago it's trying to figure out okay what are you trying to say to me everybody's got you know different types of dialect I got you know I got kind of a Southern drawl cuz I'm from Houston but you know everybody's got a little bit different accents and stuff like that when it comes to you how they talk so machines got to try to figure out you know obviously somebody from like Brooklyn that's like you know I want some water and instead of water you know
it's like okay we got to kind of figure out how do I interpret that and make that the same exact digital sequence every time so that's kind of how that stuff works it's it's complicated on the back end but it's just kind of like whenever you're going to you know your Google searches and stuff like that whenever you start typing in a question or whatever is trying to autofill a lot of that stuff for you to say okay based on certain actions that you've done in the past you're probably looking for whatever but a lot of times we see that it gives you kind of a random thing that really makes no sense to what you're
actually looking for so it's still a work in progress but it's going then text generation is you know everybody uses it on their phone I think then we got some other things like vision and that goes to a lot of different aspects as far as actual digital images to images that are picked up from traffic cameras or stuff out on the street for picking out you know people's faces and stuff like that all that stuff's got to be turned into a digital signal that the Michigan understands you know it's all you know once and zero is up in the end ultimately so how it does it it's kind of complicated and we really don't have
time to go into the details of that stuff but a machine can take those actual physical photographs scans live camera shot stuff like that and it can interpret that stuff and say okay this is percent even though I have my face turn like this I have it up like this whatever the case may be it can take that and replicate that into the same sequence so it can identify you you know it takes a lot of math and stuff like that to go into it but it happens when it goes into robots you know like I was saying one of the examples was a lot of factories maker factories overseas stuff like in your bigger warehouse and stuff
like that they have a lot of these robots that use a bunch of different sensors they use cameras as well to identify each other to say hey you know I got proximity sensors as well as cameras to say this is an object I don't want to run into it and we've kind of used that over the years to go into autonomous vehicles which is a little bit different because now we've got to identify actual risk factors you know and that comes into people yes [Laughter]
machine learning is really specific to more of a analytic side so it's not necessarily AI is kind of the whole science behind it machine learning is saying hey I want my machine to kind of analyze specific data and interpret that into whatever microphone my define algorithm is for the you know whether it's flu saying hey I want to solve a math problem or I want to make a fishin C of you know how my water flows through you know pipes or whatever throughout the city stuff like that or to say you know based on my growth of my city this is how you know I plan on for urban development stuff like that so it's they're almost
almost the same but they're a little bit different yeah there is yeah yeah so artificial intelligence is the overall of all these things combined so that's just kind of the blanket for a when it comes to machine learning we're specifically only looking at the machine doing specific tasks you know if we're looking at those lower-level types of learning but you can also have you know like it shows in here deep learning deep learning is gonna be for like very very specific tests when it comes to like genetic coding and stuff like that where you got thousands and thousands of different you know data points that you're trying to analyze all at once us as humans we can't do that in a
realistic fashion you know it's going to take years and years but if we feed that into a machine machine can kind of go through that and keep you know plugging away day by day depend upon how much computing power you have for that for that device so a lot of these you're looking at you know penta bytes you know of just storage or you know RAM and stuff like that in order to compute a lot of this stuff and you know you got make things like your you know your big vendors out there you know like Amazon and Google and stuff like that they're doing a lot of stuff with our data unfortunately you know so all the stuff
that you're getting feedback from your phones all these API is that feed into these things you know it's creating datasets for them to say okay here's how I'm going to improve my my product to you here's how I'm going to improve my experience to do you as a client you know that's that's what they say anyways but you know we know otherwise okay so what does all this mean as far as for us when it comes into technology and stuff like the for us a is in every aspect of our lives every day whether we know it or not you know like I was saying when it comes to going to websites they they use some sort of AI to to try to get you
you know ads to you and targeted information to say hey these are things that I think you're gonna like so videos and stuff in social media it's gonna be like it you check out this or or whatever you know to say these are things that are good for you you know even though it may not be but it's it's meant to make life easier or efficient we have home automation now you got you know Alexa Google all that stuff in your house you know everybody's got some sort of something you know to say hey turn on the lights whatever so we got all this stuff all around us and then a lot of times you
know cities are using this to you know get meter readings and stuff like that so then I have to physically walk up and your art any more than just stand out the road skiing your stuff and everything like that and then we're also getting into you know the autonomous vehicles is starting to become a big issue now people are worried about okay what does that mean for me you know am I gonna get run over you know stuff like that and then you know they they've been pretty successful for the most part as far as those go but yeah when we get a little bit further in here we're going to talk about how manipulation of those
images from this camera and stuff like that can interfere with how those datasets are interpreted you know by the computer and stuff like that so there's been countless times since you know this has been really it's been a concept since computers were started as far as AI you know if we look back at you know some just movies and other articles and stuff like that throughout the years a eyes been kind of one of those things where you know we've all been like okay that would be cool if we can create you know and robots that can do all that stuff for us or whatever and as we progressed through the years we were getting kind
of lazy as far as some of that stuff goes so it wouldn't be a surprise where we see a lot of this stuff happening more more especially with drone deliveries and stuff like that you got Domino's that has a vehicle that can come up and deliver your pizza you just go out type a code on the door opens up and stuff like that and a lot of that stuff is still kind of in test phase and bigger cities and stuff but it's coming as Estoque days go long so on the example of here you know get a query for what's good and evil this kind of shows how the machines trying to determine you know what is good and evil
but if we don't define that to them you know and that's still kind of a hard thing to define as a human characteristic you know what I may consider good and what you may consider too good there's two different things you know so at the same time we're gonna take all the possible variables in there and say okay all these things could be good all these things could be bad and the back end that's where the machine learning portion of it comes in is how it determines what is actually good and bad and it is kind of based off of a higher percentage in one category versus the other so and if it doesn't know it
kind of just sits there and it's waiting for the next data point so yes
yes exactly I said I so the question is is you know we're talking about earlier in there we got a strong AI and weak AI and the the overall how it determines how to make a determination off of a known data set and an unknown data set so in this case right here we're kind of using that where it doesn't have a pre-existing data set so it's kind of like whenever you first start up a a log server right you don't have anything in there to begin with and then once you connect your sensors and everything like that your collectors starts putting your data in there so at that point you can go in and whatever software you have at the
next layer can take all that data interpret that and that's where an AI model exists within applications and we're going to get in that here in just a few minutes on how you can exploit that factor of it to take those either known or unknown data sets to possibly weaponize that into if that kind of makes any sense to you it's it's very complicated we're doing it at a very high level I know because we can really get into some really crazy talks with this stuff so so we all most of us in here are somewhat into cybersecurity is is that a pretty accurate statement if not you know we probably have some people that are just getting into it
people that have been into it for quite a few years if you do just a quick google search on cybersecurity products most of us use these things every day whether it's your organization uses it to determine you know threat activity malware detection threat intelligence stuff like that so we can use it and a lot of different things and these are common common vendor names that you see out there and I think everybody has at least one product or a similar product like this in their environment it's somewhere so and then if you're looking a little bit further down there's certain things where it comes to like I was just talking about log analytics and stuff like that where you know we're
trying to correlate a lot of information into certain aspects and if you're looking at just from a collection standpoint you got logs that are being fed in and raw format into your environment you know into some sort of database in there right and in years past you'd have to kind of manually create rules or you'd have certain rule sets that would say okay I'm gonna trigger my events and my alerts off of these particular rules that's right so the AI aspect of it is taking that to the next level so it's taking those individual things but it's trying to combine all the other aspects of it to to make a decision for you and say hey
I'd like to see all machines you know with that man you know somebody that logged in with admin or whatever I want to see that in real time so it's gonna try to correlate all that stuff as quickly as it can for you so here's an interesting thing that happened here in the past year - so Shawn Carter and Chris Ola they're creators of this program called deep dream right and one of these guys they work for the bigger side of Google and stuff like that one's kind of an independent guy and basically they take photos from a network called imagenet right so this huge huge database that can take images and feed them into just
a huge database no matter what it is and it tries to say okay every single thing in here that is a dog these are all categories categorized as dog no matter what is actually all the image it tries to take all that stuff while they try to take all this stuff and reverse-engineer it and create a new image from us so if you had ten thousand images it's a dog and you know all the different parts of it they would take all those images and combine it into one and try to make something like we see here on the screen but as you can see you get a lot of weird stuff that's going on in the image on the face of
this guy the hands and stuff like that it doesn't quite know how to make out different defined you know like lines and stuff like that the background you can kind of see some some different columns and stuff like that and that's based off of averages that it's trying to determine okay 99% of the time I see a particular line and a particular design with these colors and stuff like that and 99% of the time it's this so I'm gonna fill in this area with this data that I believe is a cloud but in reality if you look in the front of or horse's head you can kind of see if there's more column shapes in there
rather than actual clouds for the most part you can kind of make out yeah it's a knight on a horse it's being led by somebody else but also on the bottom left you can kind of see some modern images that really make no sense to the whole thing at all I mean besides the dog head as the saddle and stuff like that but yeah that was kind of their project to kind of say okay we can take images we can basically take all those values and recreate something else from it and that's kind of rare that's kind of where we are trying to use that in the cybersecurity aspect of a you know and then we got to look at it from an
attacker standpoint can that be the same thing and that's really where the scary part comes into it because they they could ultimately go you know can I corrupt this data can I put it into a format that can attack these systems that are meant to you know interpret this data like this gentleman's question here you know he didn't they didn't have a defiance to begin with can they take that you said sorry can they take that undefined sir and add new data to it and in this case that's what they're doing you know they're they didn't have anything to begin with they just analyzed all these images and tried to create something from scratch so that's kind of how we're
going into that part of it all right so here's a a strong example what they also did with a lot of these images and it's kind of hard to see but if you look on the left side over there and the right side you got similar images of gray whales and great white sharks from a distance you know they look almost the same and in the top right corner you got the rows of teeth and one that circled baseball up there so what it does it decided was hey every time I see this row of teeth at the certain angle I think it's the threads of baseball so instead of it saying hey it's a great
white shark it's gonna be a baseball now so even though we as humans can interpret now that's a great white sharks teeth but the computer says now it looks too much like a baseball so what they did is they they went down there they took this - same exact images of a gray whale fin right there and they took a postage stamp-sized image of a baseball and they inject it into the picture and you can see right there there's drastic result difference you know between the two so 91% you got great white there a great gray whale and then with that image injected in there you got now a 66% chance of a great white shark which we know that's not
true so this is where it starts getting kind of curious and kind of scary to me is hey you know we got enough people out there that have nothing but time on their hands to go in and just upload stuff to all these public domains that are out there you know all your pay spoons your whatever you know they can just spin up a domain today and just throw a thousands of pictures that make no sense to anybody and if you got a software that's out there you know scouring the internet creating these data sets from nothing and you know interpreting those internally you know to your vendors and stuff like that if you think about it
from a malware side if we got code out there we got predefined things you know for our AV vendors and stuff like that to say okay we know that 99% this code is what we have but we don't know what to do with this less a little bit if we're ingesting small portions of it from multiple resources how can we not take that little bit and recompile it inside and launch an attack so think about it that way if we're going to take little tiny bits that don't make any sense but they're still stored internally on your device or through the defender and we use that to manipulate the AI model that's built inside to interpret that
you could take all that data together and compile an exploit internally so and that's kind of how that goes into it so I don't know if any guys here went to DEFCON back in 2018 but IBM they they came up with a POC for AI malware so it's a very targeted very very specific type of POC for this and it was called deep blocker if you guys read about it or not basically what it does is there's a couple different layers into the attack so it kind of goes into you know what are we trying to attack who are we trying to attack and when you know so there's there's a couple different things that are all layered within that
and that happens in an embedded AI model of in their case they use a common software tool which we'll go into in the next slide and so because it's very specific the conditions that they were doing on there he creates a unique key each and that you want to do it and since you kind of control the data you can change the key on-the-fly so if you say hey instead of targeting this gentleman here I want to target you so since we're in here recording or whatever it could be in here capturing a bunch of images their buddies faces in creating new datasets to compare so if you take that data that's in those datasets now it can
say okay now I want to target this individual instead of you so and if that's launched too common software throughout the world so they amount a million different pcs when you walk by that PC and the camera picks up on you it's gonna target right there and it doesn't matter where you're at in the world so it gets kind of crazy as far as that goes and it's almost almost impossible to reverse engineer because you don't know what the variables are and what the intended attack was for that individual you know and it doesn't have to be individuals could be geoip locations if you just bring your computer into a proximity of something if you say hey if you get by the traffic
like cam out here on whatever wrote this is I'm not super familiar with the area but if you get out there and say okay if I get within 10 meters of this particular sensor then it's gonna launch my attack you know and it could be hey I'm gonna stay on your computer until 10 years from now or whatever and then I'm gonna migrate somewhere else and going back to the different types of AI and the actual sentient aspect of a you know for me it's like wanting to you know weaponize the stuff you know for certain things but at the same time you got where us as humans we have to you know flight and fight type responses and
stuff like that so if we want to survive in our environment we try to do everything we can you know so imagine a piece of malware that's super sophisticated that can propagate back out you know because it's like hey I'm gonna do this but I also have some sort of segue out to the rest of the world need to propagate my code back out because if I'm killed here I can't continue what I'm supposed to do so I think about it and ask that aspect of it and how it can be kind of scary you know and get kind of complicated later on down the line and kind of what I was getting into just a few minutes ago of
the different layers that goes into a you know you got the what what aspect of it which is can be kind of simple and can be kind of complicated you know from a typical standpoint of threat actors nowadays you know they have some sort of motivation whether it's money whether it's you know just embarrassment or just to be a pain you know and say hey we're gonna shut down your operations you know cause you inconvenience it still cost money to finance and stuff like that even if that happens but you also have you know who who was actually if we get into stuff like the supply chain you know we got we had a kind of an incident
like that not too long ago where a lot of hardware devices were compromised by China through a small little tiny microchip less than the size of a grain of rice so if you're looking at that they can you know launch specific malware targets and stuff like that into that but imagine that on an AI level you know going faster than we can ever compute you know and stuff like that so if you're able to get through those two layers and then you get down to the actual malicious intent of your payload that's in there that's where it gets really really hard to reverse-engineer it because it's typical payloads you know you got you know your payload but
you've got some encryption entropy and stuff like that when it comes to how those particular aspects work and usually it's like hey we got one hard-coded key for like in a ransom or something like the NE we just got to figure out what that rhythm is and crack that you know and then you got one one aspect that's controlling all that in the case of AI it's like no we don't really care about that we can change that on the fly I want and then my CNC at the end can say okay now I can take that new data and recompile what I'm gonna do so and that's kind of what they did in that
case they took want to cry they embedded it into a conferencing software that's off where the scenario was hey you know we use a lot of these things like you know any conferencing software you know that's out there so we use a lot of stuff say scape Skype for instance you know we use Skype all throughout business and everything like that imagine if we had a hidden payload in there and how many businesses we could affect we can say okay we're gonna target this company today we're gonna go to this target tomorrow and everything like that and we can keep getting different ways to compromise these companies and it doesn't always just go into how you know particular aspects of
it work you know they can say okay certain users that operate at this level we can just and we can target that you know or we can you know there's a lot of different variables that grow saying you know when it comes to the geo IPE locations data you know facial rec and recognition and stuff like that that are going back through they model and feeding you data to your CNC so all those things can get very complicated and stuff like that if you look at these slides here you know we got some government contractor s here that actually building robots you know that can kind of do some of these identification and and stuff like that
and attack a target based off of these AI models right so in this case you know more likely they have a configure to say all right we're gonna see a paper target that has the black silhouette it's got the rings on the inside that's going to be my target well we know that you know computers and machines they they communicate be a very different a various different type of methods you know whether that's light whether that sound whether that's radio would see a network communication stuff like that we've seen it with drones in the past where hey we can jam a drone we can bring it down Iran did that one of ours a few years back it can happen new and
in this case a who's to say that we don't corrupt your data and now we can target individuals you know or we can target a group of individuals you know with your weapon that you created here so it's kind of like terminator you know in that aspect of it because it can't be a reality it's just we're still kind of in that phase as far as how things are going and whatever but you know like I was saying if we got different sites like github paceman exploit DB you know a lot of our security devices are out there collecting these malware samples they're collecting threat intelligence from tons of different sources those vendors are consuming that create their
own proprietary information and stuff like that but that data is still residing somewhere you know whether it's inside their own servers or out on the public internet you know once in there if we get enough of little bits and pieces if we got a corrupt AAA model on the inside it can put all that stuff back together and now we got a very targeted very nasty type of a situation when it comes to Mount Warren stuff so like I was saying with home drones and delivery and stuff like that imagine a situation where we got you know corrupt data that we're sending you know whether we're broadcasting over FME our other types of RF frequencies and stuff like
that and those drones can apply in our area we know that we can intercept it's pretty easy we also know that we can manipulate car data as far as autonomous vehicles and stuff like that goes so with all those different things that are going out there and we get those to act like humans and have that human emotion aspect of it things could get really kind of crazy when it comes to AI and imagine hey you know these are meant to be a drone delivery service what if we hijacked a thousand of them we send them off to do another task you know or you know somebody hooks up weapons or something to them you know you could have a mask
and mask as Erdelyi type thing you know on a very autonomous skill you know when it comes to how that thing's being attacked or where it even comes from you know and without the ability to reverse engineer where that attack came from it could be anywhere in the world it could be anybody and in reality it's not even a person submission in doing it you know and if the machine has its ability to react and do things on its own you know ultimately it's not us doing it we're looking at you know a factor where we're fight warfare when it comes to machine to machine so it gets kind of crazy and complicated and when it goes into that
so one of the cranks guys if you guys watch a Hale and Stefan History Channel but like I said I'm not a conceit theorist when it comes to that but at the same time it kind of opens your eyes and makes you think about hey this these things can be a reality you know and we got a lot of creative people in this industry that hey if I can do it I'm gonna do it you know and that's kind of where some things in my aspect of before can stuff like that it's like if I want to break something and and just say hey can't I do it yeah that's that's kind of what I do you know so and I think that
over the years we may see a lot of stuff that when it comes to this that it could get pretty nasty you know hand may start more on to the on to the state actors and stuff like that in the beginning but as you know data is becoming cheaper and cheaper being able to throw stuff up into the cloud and everything like that built you know big cloud server farms and stuff like that from an individual standpoint you know computing powers now you know at the touch of a finger you know and if you're skimming credit cards and stuff like that it's not your money you know to create these things you know you can
whatever you know you got a lot of these organizations you know like Russia and stuff like that that are funneling billions of dollars a year you know they're not just like a I'm just you know us get out there doing whatever throwing out you know some some random exploits they're getting paid big money by their government or other governments to do malicious things you know so a lot of times these things go unnoticed for years you know yes as far as when it just as a general okay
okay okay so her question is kind of a kind of a high level of how you know IP v4 and ipv6 you know work is as a general thing and how you can determine where you know the originating packet comes from and where it where it goes this kind of goes into more of a networking aspect of it but at a high level you got you know traffic from each individual node that's out there and it gets assigned an IP address you know if you're using you know version 4 or version 6 it's just an identifier on that network to say you were who you are right so the way those two protocols is because of as networks
grow there you only have X amount of IPs that are available so ipv6 is now a longer chain you know a longer identifier so you now have 10 times more than you did before you know with ipv4 but I mean it's a little bit more than that but at for your for your sake here it's just you know we're going through and they're identifying those things both protocols are still working regardless it's like hey do I prefer this one over the other one so with the ipv6 it's just because there's more and more things that come into the and it allows more connections into your network so it's not really it's not really saying hey we're limited to a
specific protocol when it comes to that but it allows more connections into the network so as as we grow we're just going to run out of ipv4 is basically what's going to happen so we're gonna have to go to a bigger protocol that can handle more computers onto this network so and network isn't just you know from you to your home router or whatever it goes from you to your home to your ISP to you know the government backbone and stuff like that when it comes to these big trunks of data coming and connecting the rest of world together so when it comes to how you're trying to figure out where these IPS are coming
from there's you know different indicators based on location and stuff like that that you can kind of trace back each device that it talks to can be tres trek back you know whether it's through so no firewalls which is routers stuff like that and as you go through they kind of make a chain through each thing but if you're using other types of things like proxies and slipped like that it's going in telling it it's one thing but in reality it's talking to another machine and it's hiding where you're actually original this stuff is coming from so yes
it's it's one of those things of the human aspect ignorance is bliss you know when it comes to stuff currently most vendors are looking at what can I provide to our clients what are they looking for what functionality you know attempts to doing pen testing you know a lot of times you see websites that just want you know bells and whistles and things to work they don't really care about the security when it comes to it they'll deal with that later because if they make enough money and they get something you know that comes back in the end you know whether it's some sort of repercussion they get enough money to cover it you know or hey we'll play
catch up we know it's kind of on our you know long-term goals or whatever but yeah they know there is some risk you know but they do they may not know exactly what it is at this time
so yeah so that's kind of a question when it comes to you know we got to have insurance and stuff our cards right now because we're physically driving it insurance companies right now don't know what to do as far as you know who to put the blame on at that point because it's not a human making the mistake it's that vehicle but then it comes back to who do you put the blame on in the end or you think because you're the owner of the vehicle do you accept responsibility they haven't figured that out yet so it's still a lot of things it's like hey if my machine decides it wants to go out and you know form
decisions on its own and do something that I didn't tell it to do is it my responsibility or is it whoever coated it in the beginning you know so it gets complicated there's there's no defined answer for that right now [Applause]
and and and think about it from and think about it from a medical standpoint you know what is the viability of life you know when it comes to the survivability rate when it comes to you know if it's something were to happen you know unfortunately sometimes it's like okay elderly and children are probably less likely to survive and you know something like that where it's it's a situation where you know the viability is probably lower for you know those two groups rather than you know a middle aged person you know so how do we make that decision we as people still face difficult times of that but a computer is just gonna go off those statistics
you know whatever it feels is is the most likely choice at that point and going back to the image of the the whale and shark you know once it decides you know that this is a shark or this is a whale that's what it's gonna go off of yeah so yes yeah exactly then that's kind of where I was thinking about it dude it's like yes there a lot of the bigger organizations are working on this and like I said when they've launched some of this stuff out as kind of a POC you know what they're chatbots or whatever the they ended up finding it out sometimes that yeah it looks good in the lab and everything like that but
once we put it back in the in the real word all of a sudden the human aspect of it comes into it and it becomes very negative you know so I got about two more minutes so a couple more questions I'll get her back here and then I'll you
yeah and that's that's what we currently have in a lot of our products where we have the human aspect to go back and review it and dispute those things and when we dispute those things we change that AI model in there whenever we say no this is a false positive now we're feeding new data into that AI model to say next time don't make this decision based off of what we feel but if you got multiple analysts that are going in there making their own interpretations of it that's where things can get complicated as well
it could be we don't have enough to just you know definitely say that yeah that's what the aspect is but it could be a possibility where different regions have different perspectives and that could change how things are handled as far as the people one more question I I really don't know at this point it's it's really limitless at this point you know as far as what we can do with it and that's why we can haven't achieved that level of sentiment you know maturity when it comes to certain AI stuff we can do a lot of it but we don't even know how our own bodies work you know we don't know how the brain works as far as how it makes
these decisions and stuff like that so until we can understand that as humans how can we replicate it you know so alright well that's all I got for today I thank you guys
if you got any other questions I'll be hanging around here and we can meet up after this and stuff so thank you guys for coming