DFIR in 2022: The Wild Wild East - Jack Rutherford & Richard Grainger
Show transcript [en]
[Music] yeah so good morning everyone um as mentioned the title of our talk today is DFI on 2022 digital forensics and incident response the wild wild East we've entitled it this way because the vast majority of incidents that we've seen this year have come from Eastern Europe I have to say certainly a trend look I'm sure there's threat actors in the other parts of the world that are just as active but generally their motivations are more along the lines of political or perhaps Espionage and they're certainly not as loud as Eastern European thread actors which are very much financially motivated at this point in time we want you to know that they've been in your
network because you need to be able to read The Ransom note so you can pay the ransom essentially quick introductions my name is Jack I'm a chief technology officer at Drisco Labs we've got rich here as well he leads our dfir team a bit of background on triska Labs quickly we run three major branches of our business advisory defensive and offensive which is basically GRC 24x7 security operations center and the offensive team for pen testing and red teaming under the defensive team we have a digital forensics and incident response team as well which we'll be talking about today quick overview of the agenda so we'll have a look at the high level overview of the attacks that we've seen over the
course of this year the major two types of attacks being ransomware and business email compromise um these are the attacks where a businesses in Australia really have felt the effects and experienced subsequent Financial loss at least very much in the short term we'll do a deep dive in a case study on a particularly effective ransomware incident that we responded to by a ruthless factor and then we'll look at the top takeaways as well for how organizations can protect themselves before we dive in I want to reiterate some of the takeaways things to remember while we talk today look nothing we're talking about today is particularly sophisticated uh as I'm sure many of you know it's the low
hanging fruit that get targeted and those are what we're responding to so it's pretty simple things that organizations can do to protect themselves things like multi-factor authentication being in place poor backups or sometimes good backups but they're not segregated so they're really poor backups a lot of organizations don't really have the it resources needed to implement the right security controls or maybe they have an MSP whose focus is not security and threat actors particularly in the ransomware space they're becoming more and more efficient and quick and effective at privilege escalation lateral movement and subsequent execution of ransomware so we'll have a quick look at the types of engagements in the industry verticals that we've conducted 34 business email compromise
as we can see the majority is ransomware and extortion few incidents where it's only around somewhere and a few where it's only extortion but the vast majority is certainly these two things being combined so the threat actor will get in they'll steal the sensitive information first and then they'll encrypt the business critical data they'll perform a double extortion attack try to get the organization to pay for both the decryption keys and to prevent the data being released on the web the industry verticals that we've responded to varied certainly varied Healthcare is the biggest one but I think the major takeaway from this slide is to understand that no one industry is really being targeted here it's more
about the low hanging fruit particularly financially motivated threat actors are opportunistic they want to make as much money as possible as fast as possible so they'll just Target the weakness weak organizations rather than targeting specific verticals with that I'll hand over to Rich quickly who's going to talk about ransomware give a bit of an introduction thanks Jack so when we're talking about ransomware we're essentially talking about a threat actor running encryption um software or ransomware binary on one or more systems within a network and what that binary will do is go through the file system and encrypt files on it make them inaccessible to users so the only way you can get that data back is
either pay through a decryption key or have really good backups a lot of the time the Rants and notes will be built into the ransomware binary as well and that's listed across the drives where it's encrypted and that will include information about the threat actor that most of them maintain websites on the dark web where they will list their victim organization so there'll be links to that instructions on how to download Tor so you can actually visit the site and also often a unique Company ID for the victim organization so if they choose to engage with the threat actor they'll be able to identify who that organization is as Jack mentioned double extortion is something we see a lot so threat actors
stealing data prior to encrypting it and the reason for this is that it puts additional pressure on that organization to pay the ransom so they may have really good backups and they can simply restore from backups they might be down for a couple of weeks they might have some business interruptions but they're they're able to get back up and running however if the threat Act is stolen potentially pii data Phi data IP data for how that company operates they may not want that to be made publicly available and that may entice them to negotiate with the threat actor the screen we've got a screenshot here of blackbusters blog that they maintained so it'll list the the victim
organizations here a bit about the company and then the published percentage they will release Excel traded data in stages if the rants is not paid and they also track the number of people that have clicked on the site as well two more examples here so on the left we've got Hive leaks this is the The Hive ransomware group uh they will include information about when they actually encrypted uh that victim organization and when they posted it on their website and on the right is lockbit uh probably one of the more well-known ransomware groups at the moment they operate a very effective ransomware as a service operation where they will let Fred actors utilize their ransomware tools they'll let them use
their back end and they get a cut of any successful Ransom so they've got the big red countdown timer at the top where essentially that hitch reaches zero then the data becomes available
so as part of the investigations that we do we like to track um the time between the initial access when they first got into the environment and when they deploy their ransomware this is also also often known as dwell time so essentially the key takeaway here is about 20 days on average across the threat Act of the web scene the most extreme one here on the left is unknown so that's where we we're dealing with threat actors that weren't affiliated with any major groups and that's about 80 days then we can see Conti lock bit 2.0 before they rebranded and phosphorus is all sort of around the 45 to 35 day Mark and then we start getting to sort
of sub five days with um things like lock bit three dive all black bike Cuba and black Basta which will do the Deep dive on and also Dharma
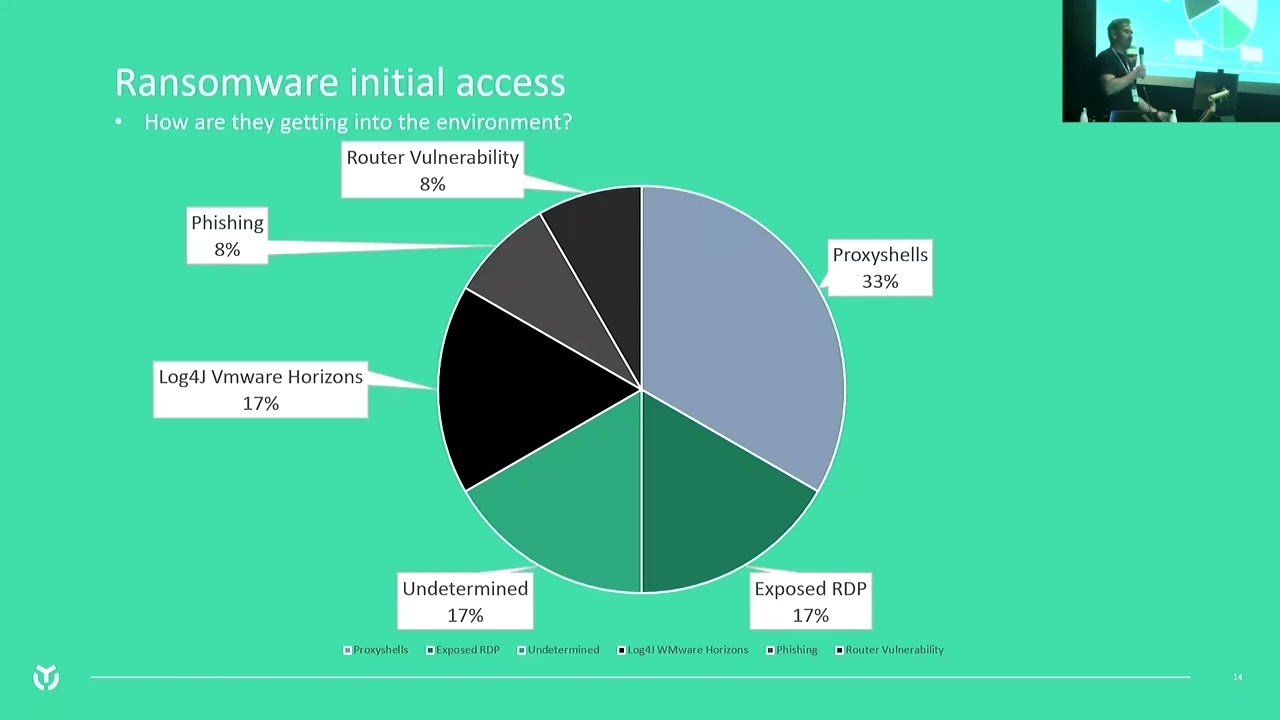
so we also like to get an understanding of how thread access got into the environment that way we can provide guidance that organization to stop it from happening again unfortunately the largest initial access Vector is proxy shells so if you're not familiar with proxy shells it was a group of vulnerabilities in Microsoft Exchange particularly on-premise hosted servers and this came out in August last year but unfortunately it's still being exploited today this year with organizations essentially exploring that vulnerability gives a threat actor system level access on that machine so very useful initial access point into the environment exposed RDP so that's the remote desktop protocol proprietary Windows protocol and it allows you to connect a machine
using nuts and keyboard as if you were sitting in front of it unfortunately exposing RDP to The Wider internet is not a great idea users can thread actors will try and Brute Force accounts particularly the administrator accounts which by default doesn't lock out so they can just keep on hammering it but also if they're able to get valid user credentials through phishing or some other method they can just log straight in because by default the traditional RDP doesn't have MFA so it makes it very easy undetermined so this is where we will group um initial access where we believe we know the way that we don't have the actual evidence to prove it or the
environment has been wiped before we are brought into the investigation which does happen um and also if the threat actors have just encrypted absolutely everything um specifically when they target hypervisors and the virtual hard drives or bmdk files are encrypted we can't even access those to get an understanding of what happens on those machines log4j specifically vanway Horizons The Log 4J is a Java logging Library very very popular it's open source used by a lot of software and in December last year was identified that there was quite a big vulnerability within that and it had a very widespread effect on the IT industry in particular we've got the VMware Horizons there so that's an external facing
server okay to the internet and by exploiting that particular vulnerability threat Act is going to again get system level access on that machine interestingly with all the uh log for Jay VMware Horizon engagement we've had there's been evidence of crypto mining occurring on these servers from January January February um until the ransomware group gets in and then essentially ransoms the network fishing so the delivery of malicious files through email and router vulnerabilities as well so we actually had a recent engagement where the organization had a draytech router and vulnerabilities were available for that which they exploited and essentially set up port forwarding in the router and then they could access RDP from externally in brute force one
of the machines on the network
Jacks talk about business email compromise yeah so we won't spend too much time on this as the majority of things we've seen have been ransomware but it is important to talk about this type of attack it's quite a simple one it should be said but it can be quiet effective even though it only involves a threat actor gaining access to a single account often usually in a low privileged user we see this often resulting in the transaction of you know hundreds of thousands of dollars that can be lost so quick slide on what this is essentially when a threat actor gains access to a mailbox ideally the mailbox of some kind of financial administrative position within an organization someone
who handles invoices and they'll sit there undetected their Land wait sometimes for a few weeks and they'll wait for an invoice to come through they'll intercept the invoice unbeknownst to the owner of mailbox and they'll change the bank account details on that invoice so that the legitimate party paying the invoice actually pays a threat actor bank account instead of the legitimate bank account a few stats here on the screen from the a Triple C in 2021 um they reckon that two billion dollars in 2021 was lost to scams and 227 million of that was payment redirection scams which includes business email compromise so how the thread Act is actually getting access to the mailbox nothing
groundbreaking but particularly effective techniques the first one being fishing pretty obvious uh generally this is when they'll send a malicious link to a user that points to a phishing page to collect credentials such as this page on the screen right looks like a Microsoft Office 365 login but they use it to collect a username and password instead worth noting that tools certainly do exist that can collect two-factor authentication tokens and codes as well one of the most popular is probably evil gen X2 very effective tool that man in the middles the connection somewhat and then passes the creds to the legitimate service so that the session token can be intercepted as well they can get access
to accounts protected by 2fa worth mentioning as well the other major techniques that actors are using to gain access to mailboxes credential stuffing for those of you that aren't familiar this is where a third-party organization completely unrelated to the business or to Office 365 will be compromised the data will be posted online the credentials from that bridge and because of user Tendencies to share passwords across multiple Services the passwords for the third party site will be valid for Office 365 as well and subsequently provide access to a mailbox this next page is simply what it looks like when a password is entered into such a phishing page right you can see the password testing there sent in
Blaine text to the thread actor um a quick few notes as well as to how the threat actor achieves not being noticed within the mailbox they'll generally set up forwarding rules email forwarding rules so everyone has a folder called RSS feeds for example that no one really uses so common technique is to set up a rule so that when certain emails come in with invoices it gets marked as read it gets put in that folder when the thread actor logs in and checks in they can see these emails that have come through and they can either forward them to the legitimate parties or they can intercept them change the bank account details on this slide here
we can see an example of one such threadactor email where they've intercepted an invoice and they've forwarded the email onto the legitimate party to try and get the invoice paid with the fake Bank Account Details in this particular instance the third actor had actually successfully pre-authorized two different payments using this method totaling about three hundred thousand dollars but luckily a third party organization who was about to pay this picked up the phone called the victim and confirmed whether or not it was legitimate I just buy a phone call Save themselves 300 Grand I mean that's not too bad you can see the importance of having these processes in place
so I'll hand back over to Rich he's going to Deep dive into a ransomware investigation we performed the threat actor group in this case was blackbuster Blockbuster they formed in about April this year when they sort of established themselves they posted on English and russian-speaking forums essentially looking for initial access into organizations based in Australia Canada New Zealand United States United Kingdom so essentially five ice countries and didn't their Inception they've been estimated to have encrypted about 80 victim networks that's based on numbers of organizations that have been posted on their blog so if an organization pays they're not going to be listed so that number could actually be much higher on the screen we've got a quick high
level overview of um the this particular incident uh it only took them 14 hours from that initial phishing email being sent out to escalating their privileges getting domain admin and disabling tools finding out how backups work and finally deploying the ransomware encrypting the organization and we'll talk a little bit more about these steps in detail so this is the phishing email that was sent to them it was essentially a link to a Google drive file and the password for that file was contained within the email and the reason that threat actors do this is because Google will inspect files that are hosts on Google Drive so if it sees it's malicious it's going to scan it and remove it so by password
protecting it Google can't see into it that fall was a zip fault items 6811.zip and that contained one file in it which is a link file so a link file is essentially a shortcut file you'll have links um and shortcuts on your desktop so Outlook Google Chrome but link files can also be used in a malicious manner which is what we've got down the bottom here that's the command that this particular link file would execute and essentially what this would do would execute command prompts to create a folder reach out online and download a dll file and then execute that dll file which was identified to be Martin Booker's initial access malware so we got the patient zero machine and
did a forensic acquisition of it and analyzed that and from that we're able to confirm that the user did reach out to that particular URL they downloaded that file which was saved in their downloads and we also saw a subsequent execution of the command prompt ping and curl which we all saw in the the link command there as well to show that it did execute the command and control uh the threat actors use Cobalt strike um they deployed that on the first machine so Cobalt strike is a an adversary simulation tool it essentially provides command and control with a whole bunch of other functionality like dumping passwords and password hashes and you can exfiltrate data but
essentially you're you're issuing commands to the workstation where the Cobalt strike is being deployed and you're getting the responses back
so when they've got that initial foothold on the machine they were just a low privileged user and we saw them escalating their privileges to a local administrator and they did this by using an Event Viewer UAC bypass they actually use a proof of concept code that was just on GitHub and then just around the Powershell script and they got it but essentially once there were local administrator they could do a bit more on that machine they're able to dump password hashes and in this particular case they're able to dump a domain admin password hash we got that hash and gave that to the red team they cracked it within a couple of seconds using a
popular word list and we're all set to show that it wasn't a very strong password so essentially once they had that they had their keys to the kingdom they're able to move throughout the network so they move to servers with the environments uh they put Cobalt strike on those as well to get Hands-On people on those and started to understand what defenses were in this environment so they were using Windows Defender some other early tooling as well they just disabled that they had their privileges to do that and got an understanding of how backups were being done by this organization so they were using veeam backup replication they just used vmshell to delete all of the
feedbackups they also deleted the schedule backups as well in case anything was backed up before they got a chance to deploy their ransomware
finally you've got impact so this was them actually deploying that ransomware in the environment so they use PS exec to push it out to all powered on servers and workstations Network that ransomware binary executed went through the file system and essentially made a large subset of files inaccessible for users they also identified that the organization using esxi for hypervisors for their servers and they had an esxi variants as well which they deployed on those hypervisors and that encrypted the vmdks or the virtual hard drives of those machines which makes it very difficult to perform an analysis on because we're not able to even see into those disks when the ransomware was run on those machines as well we changed all the
backgrounds that's all we got the screenshot of here essentially saying that they're being encrypted and to look at the ransom note for next instruction
for Jack to talk about how organizations can protect themselves in these kind of attacks yeah so look there's nothing groundbreaking here um a lot of the time it's simple stuff that organizations can do but I'll break it down a bit into a few different categories here so how we like to break it down to trisco Labs is into three major categories for where protections should be implemented this is across people process and Technology but it's important to note too a strong defense in-depth approach to Security will also include implementing protections at each stage as each stage of the attack uh chain that we've just talked about that Richard just went through right this is to say that you need mitigations in
place at the initial access boundary of your network but then you have to assume that a thread actor might gain access to the network too you need mitigations in place to prevent lateral movement to prevent privilege escalation you need to make sure things are segregated your sensitive data is segregated backups are segregated right and you need to make sure turns in place so that you can see if anything happens essentially it's all just to slow the threat actor down here because as a lot of people I'm sure know most protections can be bypassed in one way or another but by making yourself not the low-hanging fruit and by giving yourself time particularly if monitoring is in place you can heavily reduce the
impact that can happen here uh if you have holes if your networks like swiss cheese right then they're able to do it within 24 hours could be before you even wake up the next day that you find your network has been ransomed so some of the major takeaways as a result of this talk and as a result of the data that we've collected the first one's pretty easy you know multi-factor authentication you can understand why this is important for the business email compromise attacks we talked about even though it can be bypassed it can certainly reduce the risks associated with it it's one layer of what should be a defense in-depth approach but if we
talk about ransomware then you know we mentioned RDP for example um you can also get initial access to legitimate credentials and credential stuffings so multi-factor authentication on the VPN is also critical that can also prevent you know persistence techniques that an attacker might set up in the network ensuring you have a tested and segregated backup procedure so segregation is obviously important if you have great backups but they're not segregated the ransomware will simply encrypt them however more and more these days we're seeing threat actors actually actively looking for the backups and becoming quite effective at it we had an example recently where there were two sources of backups for the network there was some hosted on a Nas and then some
completely segregated within the cloud unfortunately the credentials for that cloud account were stored in textile on a share right so it's not the best procedure I've ever seen you need to test this too right so you need to make sure that your backups can actually be used to restore your data you need to ensure there's a procedure in place restricting and monitoring your external footprint it's really important to understand what you have exposed to the Internet so that you can continuously test this monitor it um footprint monitoring is important because eventually you might expose something that you don't mean to this is monitoring of the external attack surface it should go without saying that insecure services such as RDP for
example shouldn't be exposed in the first place use a VPN instead patching is critical uh people in this room might have seen recently the Australian cyber security annual threat report for the previous year one of the major Trends coming out of the report that they've seen is threat actors are becoming faster and faster at weaponizing the exploitation of publicly disclosed vulnerabilities so a vulnerability like log4j example will be dropped and made public and threat actors are quickly weaponizing this to gain access to as many networks as possible in as shorter time as possible to make as much money as possible so prioritizing external is important but don't ignore the internal when you're patching as well
um because like I said defense in depth is crucial penetration testing same endpoint detection and response these all form part of a good security program but I think the main takeaway from that dot point is that you kind of need someone monitoring these alerts 24x7 right partially because of the times that time difference Russians operate while we're asleep right that's just their business day um and also because in a lot of cases we actually saw even when it was you know not your top of the line AV alerts would still be popped when these networks were compromised but no one was really looking at them so you know sometimes it's days before it's actually been
noticed and by that point it's too late so if you are deploying tools that pop alerts you need someone in place to respond to those alerts and to notice those alerts to take action quickly user awareness training is critical um ensuring staff know the risks of cyber security right pretty simple stuff making them aware of the different kinds of phishing attacks and how it can impact them but also encouraging staff to just practice good Security in their everyday lives there's been examples recently where a lot of personal devices have been compromised Redline malware if anyone's heard of that right it steals browser credentials and a lot of the time users will store VPN credits work related creds within
the browser and this has been the initial access Vector for a lot of high profile breaches recently and finally having a good security roadmap no one's really going to get security perfect it's almost impossible to do right but it's so critical to be ahead of the curve to not be that low hanging fruit and by continuously improving and continuously implementing the right things in place for cyber security right you can get ahead of the curve and heavily reduce risk ensuring you have an instant response plan and actually testing this plan War Games Etc things of that nature so you know how Executives and Boards will respond in these situations is crucial as well so with that that brings us to the
conclusion of the talk thank you very much [Music] [Applause] thank you





