What's Running In There
Show original YouTube description
Show transcript [en]
Okay, cool. Uh, I think I'll get started. Um, thanks everybody for showing up to this afternoon session. I know it can be quite hard and it's a long day. So, um, I appreciate you all coming along. So, a bit about me. Hi, I'm Fen Kelly. I'm a senior engineering manager at Rapid 7. I've 10 plus years um, tech industry experience and started out as a QA. um pivoted very quickly to dev to cloud then to security and have been working in rapid 7 for the last number of years focused on uh cloud security. I'm also a cyber first ambassador for the first time this year and so shout out to Sarah and all the folks on the booth in upstairs room. So
if anybody else is uh interested like me in mentoring young people in Northern Ireland um and showcasing what the pathway in tech actually looks like and how many roles and jobs there are and please give Sharah or me a shout um we could use more ambassadors and um it's really good to see um I know I'm especially passionate about paving the way for young girls in our schooling at school age and um making sure that they know that there's many different types of people that make up the tech industry today. So, um, okay. So, I'll try and slow down and I'll try and talk not my usual fast pace, but why I'm here today. Um, so recently I've been working on a
runtime security project within Rabbit 7. Um, and a lot of people always come up to you, what are you doing? Even in within Rabbit 7, I've had to explain runtime security and you know a lot of people overlook all the nuances that come with that and actually the the differences between other cloud security principles that we already talk about and get loads of our time. So we're talking about all the shift left and we're talking about CI/CD security, static analysis and infrastructure hardening, but what actually happens at runtime is is equally important and is a huge threat. into real world environment. So um this talk is aimed at a very foundational level um and give
you kind of an inkling into some tools and that you could dip your toe into. So um diving straight into a definition, I love um to have a definition to start us off. So what is runtime security? Um this is the observation and defense of workloads while they're actively running. H so what that means in a cloudnative environment. So think about your big names, Docker, Kubernetes, containers. Um these are often dynamic, ephemeral, spin up, spin down, um constantly. So that's so runtime means having the visibility into what's actually running in those environments while they're executing. For me um as a security individual and in my current role I have the responsibility to think about the whole ecosystem um and what we
deliver to customers and how they can succeed in security. So not just showing them what's happening. So if you give them visibility that's great but what do they actually do with it. Um, we need to give them the tools to detect threats quickly, respond effectively, and then take those right remediation steps and guide them on that path because a lot of people don't know what they're doing and they don't know where they're exposed and these are the most vulnerable people like we see a lot of universities that come up against runtime threats um and they don't know how to handle this. Uh um so again we're trying to empower that action back to the customer and the end
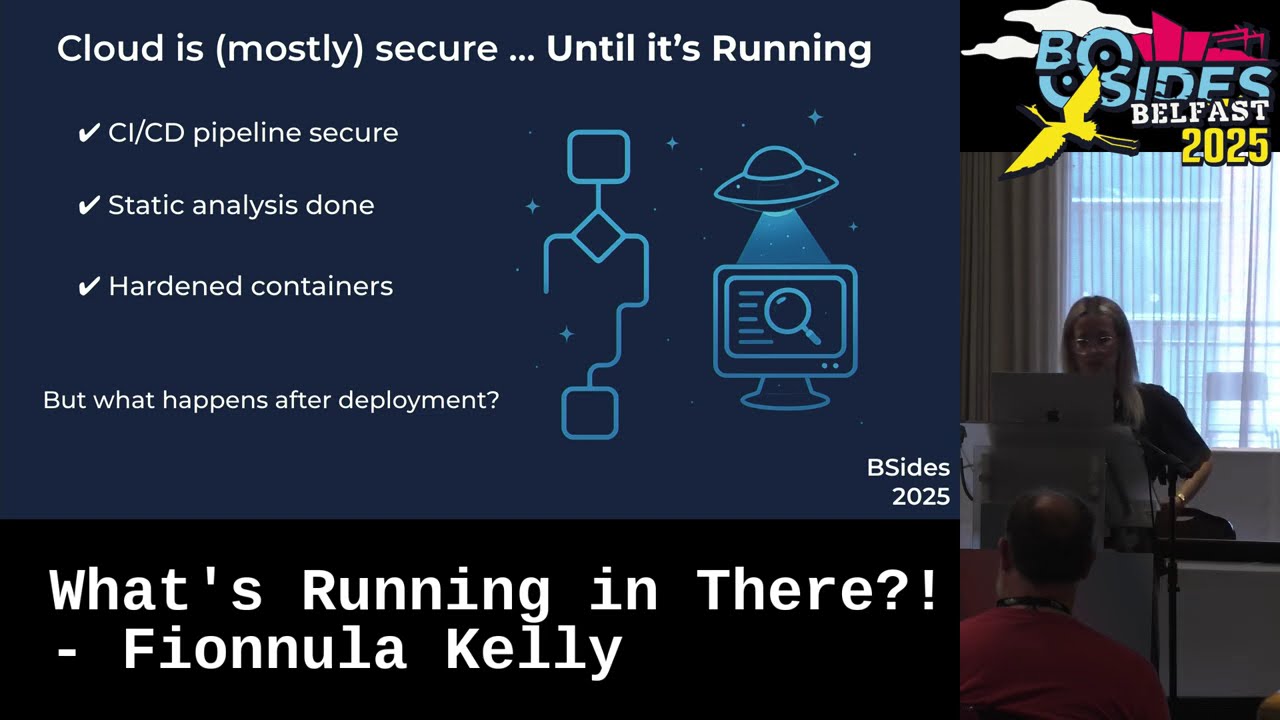
user. So as a team we are all familiar with with these processes. We've done all the really hard work which is setting up a CI/CD pipeline. We know how long that takes and how much time we haven't built into our dev cycle to actually set that up. Um, and then as a team we've argued about which static tool analysis we want to go with and you know we've we've spent hours that complaining about this one and the pros and cons and right okay we've agreed we've set it up and yeah these things are running they're running in our environment and we're happy and our teams dev teams are following all the company's basic security principles and we're confident
in the security of our system But one of the key questions is here what do you as a team have in place to effectively monitor the execution exploits happen after deployment and you know it's not just the vulnerability in that static code that you have scanned. Um so that does not give you the level of protection that you need. Um so this isn't just about like monitoring the health of your system for up times and downtime and having those pager duty alarms go off and get you out of bed. This is actually the the execution items that are happening and logging those for any deviations outside of the norm or the the mean. So going back to simple
terms, trying to keep this as foundational as possible. If you think about an analogy, build time security is like a blueprint of a house. So you're thinking about, you know, where are your foundations going to be set? Are your walls all straight? And are your materials safe? And then if you think about runtime security, putting the cameras, motion sensors in place, um watching what's happening in real time as people move move around, why does that matter? And if you look at the blue blueprint, can it tell you who broke in last night? No. That's where you need those monitors and sensors to go off and really protect you. And that's where your cloud protection comes in. You need
that visibility into what's happening live in your environment. So that brings me on to the next part, real world threats and how they actually operate at at runtime. So all of these are very commonly known runtime threats. We've heard of heard about them. They're on the news. Um and just to even walk through a simple example and a very well-known CVE and it was talked about even here this afternoon at one of the sessions log for shell December 21 hugely disruptive just before Christmas. um and took out a lot of organizations and we all spent a lot of time digging around and trying to remediate that vulnerability. But what actually was that? Um you know we talk
about this and does does everybody actually understand what went on? What happened? Um so log forj is a Java based logging library. It's most commonly used frameworks in the world and that's why it was so disruptive. It's built into thousands of applications and frameworks. Um, and what actually happened is attackers tricked log forj into executing arbitrary code just by sending it specially crafted log messages. That meant attackers could gain remote code execution and have full control of a system with minimal effort. Attackers used it from crypto mining to data theft. Um, and the impact of that was crosscutting. uh big tech giants faced government and why the runtime coming back to why it really matters. We've talked about an
organization can have that perfectly clean code base, everything well configured in your environment, but at the time there was an unknown vulnerability in log forj and and nobody knew that if somebody had some runtime level of monitoring, they would have seen that malicious activity starting to kick off in their environment. [clears throat] So that brings us on to runtime telemetry. This is the live signals and data that tell us what's happening and running inside a workload. It's a foundation for being able to detect and respond to threats just like the one I've talked about. So this is your SIS calls, process trees, network flows, and file um access events. So here I've listed out some of the
commonly known runtime tools. And a big buzzword around runtime is ebpf. So tools like Tetragonon or Tracy here they hook into the Linux kernel by leveraging ebpf technology. They place probes and trace points at various uh points in the kernel functions sis calls file operations and provide that deep visibility allowing for real time realtime security observation and runtime enforcement. Um there are another there are a number of commercial agents as well available from various different security providers um and use this to surface and respond uh to threats. Falco here um I've listed is a great entry point. It detects unexpected behavior in containerized environments based on SIS calls. So, Falco, just as an example of
one of these tools, super simple to set up and you can actually configure it through GCP um through the Google Cloud Marketplace. Um it can be deployed on an existing GKA cluster or a new one. So, if you have a free environment or anything or feel like um playing around with this, super super simple. Um this so even just to test Falco, it's it's a couple of command lines. Um, it gives you immediate visible proof of runtime detection. One of the default rules in Falco uh will fire an alert if somebody shells into a running container. So, if you can see here on the left, if you start up the the container and have it sleep, so it's
running, you execute a shell um and then check the logs. You can see here on on the right hand side that a notice that's um Falco's notion of an alert will tell you that a shell has been spawn spawned. Um and that's that's the kind of events and alerts you should be monitoring for. And then there's the commercial agents and tools that will help you decipher that deviation outside of the norm and really alert alert you to to those threat actors in your environment. Um yeah, thank you all for your time today. Quickly, [applause]
so find me after if you have any questions. I don't feel confident enough to stand up here. [laughter] Thank you.





