Operational Technology Cyber Security In Railways
Show transcript [en]
hello everyone yep I'm Dan Basher uh and I'm going to be talking as I said about OT cber Security in the railway uh quick overview we're going to be talking about quick introduction about the railway and how side is managed talk about sort of the projects that we've been working on the three strands of said projects current progress and a bit about what we want to do in the future so who are we I work for digital Transit limited we're a small company we were based in Lancaster and Huddersfield with a whole range of things from software safety assessment training in uh safety engineering we developed condition monitoring tools and in the last sort of year or so we've
been moving into the cyber security space so a bit of background about the project it's an innovate UK project it's going to be running over the next 3 years we started about four months ago so you're really getting to see uh the the intro into this project where we've got to so far and what our big plans are for the next 3 years so why is this important important not going to mince words here s Security in the railway is poor currently uh they've done surveys about people's awareness of cyber security they get very poor results back uh there are lots of companies who are talking about what they're doing I'm not going to name
names here we've discussed with operators and we say what you doing they say oh you won't believe that we're doing this that and the other we've uh started putting some policies in place right okay that's not where you need to be we're in 2023 now 2024 even you need to be a lot further ahead of that why else because in the railway industry the uh governing um laws in place other than his regulations which are basically placed against operators so think uh aello greater Anglia Northern trans penine um a anti West Coast people who are running the services they are given the responsibility for cyber security which means that the supply chain are much less interested so for them it's
it's important we can make it as easy for them as possible to do as much cyber as possible now what is it we want to do we want to develop a compliance tool now we've been um giving training courses on a technical specification ts50 701 I apologize if I start listenting a lot of numbers in this presentation essentially it's about how to apply OT cyber security to the railway industry it's based off the IEC 62443 Suite of standards so what we want to do is we want to make it as easy as possible for people to start developing cyber security Management Systems to start considering how they want to do risk assessments for their assets and
basically to bring up the competency of the industry and how are we going to do it well I'm sure you're going to hear the word AI a lot today we want to make the most of AI we want to look at natural language processing uh we want to look at using um databases to help manage things automatically produce documents uh work people through how to do risk assessments all that good stuff so again product description what do we want to do we want to create a tool now we're looking at creating a plugin for Enterprise architect which is a tool that can be used for all sorts of project management requirements management developing models that can
then be used again to do things like produce documentation to keep your projects on track in this case we wanted to use it to keep your cyber security on track so I mentioned three strands what are the three strands of this project we want to do standards modeling so this is going back to the IEC 62443 I mentioned before we want to look at that from the perspective of two different groups of people we're considering the operators as I mentioned before but also system integrators so this is your likes of Itachi Seamans Stadler people who are building trains they might be building um large infrastructure for the railway and that's important because the two different groups are doing different
things it's not going to be a one-sized fits all tool there are going to have to be different things available for different groups and so the way we man way we model the standards and the parts of the standard we model have to be different for those different groups next we want to get our large language model these things are incredible in the last two years what can be done because of these large language models is massive before if you had hundreds and hundreds of documents you've got to have someone either read them or scan them or use some other technology now you load them all into a large language model and it'll automatically find everything you
want from it it's fantastic I'll get into that a bit more in a while and the third strand case studies there's not a lot of best practice in the railway industry for cyber security there's no great uh examples of what's being done so we want to use this to do that and to give people an idea of this is what good looks like this is where you need to be so I mentioned Enterprise Architects and standard modeling what sort of things are we going to do with that so let's say you're working through your process in the um Railway industry there's a standard called 50126 that's a v life cycle model if you think about
your systems engineering you go through from your concept uh to requirements architecture design up the other side validation verification and then putting your um asset into service and we want to help guide people through that but specifically on the cyber security activities now in the railway there is a massive emphasis on safety the UK has the safest Railway in the world bar it's incredible and B Bas no accidents happen ever so safety is really high however integrating that safety with cyber security is where you start having a problem because teams don't talk to each other you end up with little silos everyone sort of trying to get their little bit in so the idea is by using
this you can say right we're at this stage of the life cycle here's what safety should be doing here's what design should be doing here's what cyber should be doing and here's where they need to be crossing over here's the artifacts that are going to have to be passed backwards and forwards so as you go through that we're doing things like storing the requir security requirements and then automatically because we're modeling this within sort of a database structure it should be as point out right well here's where you missing something here you've got an asset but there's nothing attributed to it in terms of risk or in terms of requirements for it uh you've got um a
connection here between something that is a safety system let's say a signaling system and you've stuck a nice little iot device on it because you wanted to monitor it all of a sudden you've got connection between the internet and one of your safety critical systems it's a bad idea and as part of that we want to consider a massive number of Standards we don't just want to say uh think about your OT only like I said there needs to be uh working together between these different areas so we want to be considering the safety organizational standards like equality management system and we want to be considering in not just at your operational level but also your
corporate um so so this is my favorite now the large language model so we are currently just using an existing large language model we're using llama B llama 27b currently which is a mediumsized chat model and what we've been using is something called retrieval augmented generation rag as far as I'm concerned this is like cheating they these things are incredible you basically take your query you have your question and before it gets to your model you send it through this retrieval this I call it rag you send it through your Rag and it looks for all the documents that you've put in there for example we've currently put standards best practice and C security for in there and it looks through it and
it says right that's relevant that's relevant that's relevant that's relevant throws it all into your query before then sending it onto the chat B we don't have to train it to do this we don't have to we can put weights on um different documents to say how much it should be taking from each of them but for the most part it all works automatically and it gives us back an answer which contains all of the relevant information we want and the main thing that we're changing and varying at the moment is again the waiting on the different documents and also which documents we choose to include because the worst thing you can do for any sort of AI is give it bad
data the moment you give it bad data you're going to start getting bad results now one of the things we want to do with this tool is uh most companies will have some sort of existing documentation or perhaps they'll be producing documentation that we then want to assess so the question was how do we feed this large amount of information that people have already got into our large language model now you can train models but that's incredibly energy and time intensive so we thought what if we use a rag for this as well so you use an initial rag to load in all of your documentation that you have you send your query into that well in this
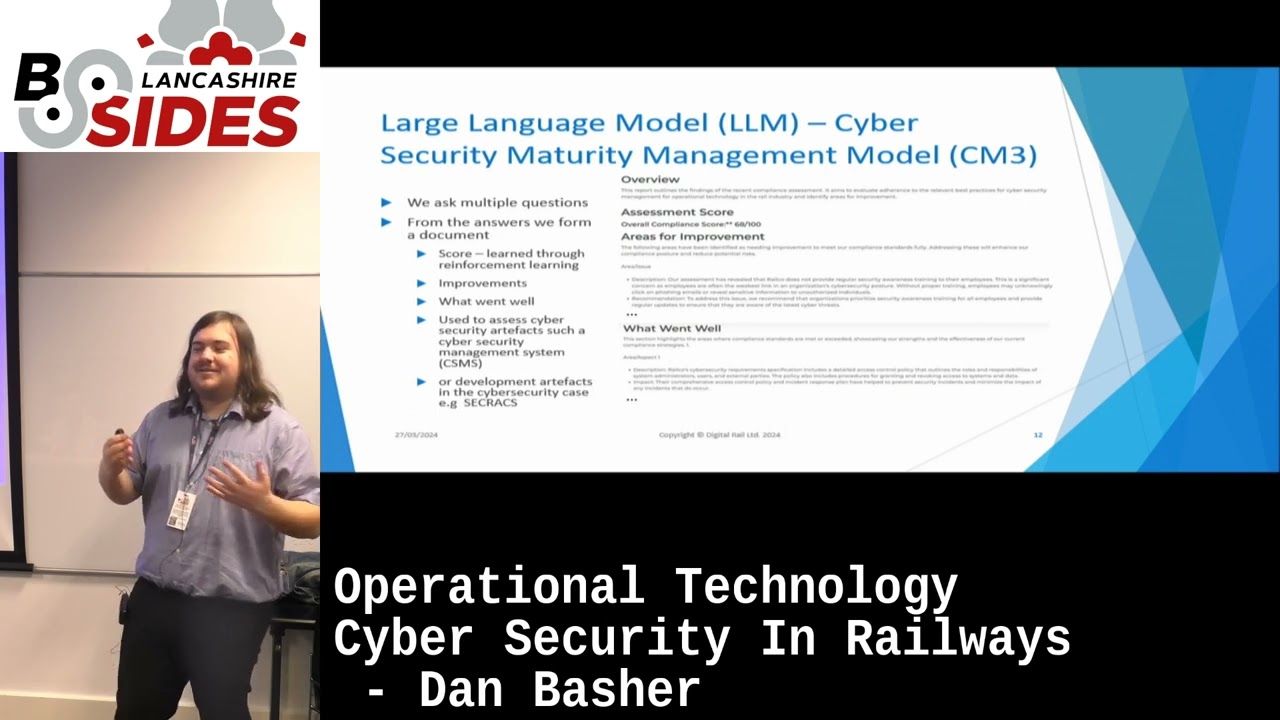
case it be our query that we send into that saying okay where is your policy on passwords keep it nice and simple it goes it looks in that documentation finds everything relevant then takes it through through to the next stage to the next rag where we have the um uh standards and things that we mentioned before it checks it against that and finally we get our answer so we're using a two-stage system here again just to extract all the information we need automatically there's no sitting there checking everything bit by bit and this is how we imagine it will look at the end so you're going to get things like a score which we think we
could do through reinforcement learning I.E we uh through case studies through doing example we get lots of examples of these um of your SL Security Management Systems different policies and procedures we can rank them on a score which ones are good which ones are bad and then use that as an as to then get an output of the score want to do things like a gap analysis what's good what's bad what's missing and then provide people um useful areas for improvement and again because we're using llms we can use generative AI to produce a lot of that automatically with big red squares around it saying this has been generated by AI please check this and review this
before you uh submit this to your line manager and we're also going to include a connection to these realtime uh threat databases if you have a cyber security management system it's it's um sorry you have a cyber security case so as a systems integrator you have collected together all of your Assurance information to pass on to the operator to say this train that I have built is safe it's cyber secure for usage now a safety case changes very rarely hardly ever once you've made that except for quite you know unrealistic circumstances it's going to stay the same but cyber security case is changing constantly there's always new threat there's always new technology out there that's going to be a problem and so
therefore we want to connect it up to these threat databases now these are I know these are more it related databases there are some OT databases in existence we've talked to train operators systems integrators where do you get your threat information from who do you report to we get lots of different interesting answers I've talked to uh people before who say well we just sort of uh call Our IT people and tell them there's a problem there's no proper reporting going on so this is sort of an initial list that we're looking into that's going to have to expand over time and with access with the LM having access to this realtime threat information we should be able to
always keep the information and the advice that we're giving people up toate and relevant and because we're then going to have all this data stored within this database structure it's going be quite easy for us to do things like this to generate diagrams to generate documents for people now a long-term goal is that we'd like to be able to read in not just text but also diagrams themselves using a model for example like daring that's this is very much a research project and that's the most researchy of the research projects As It Gets this is not easy and you can imagine there's an awful lot of uh confusion when you read in a diagram and
somebody's used completely different symbols can me completely different things so this is an aspiration that we have though for the project over the next three years and finally as I say case studies want to produce case studies because there aren't very many in existence I always like to put this one up because CU this is a fantastic example of going through that left hand side of the V that was produced uh from conference a few years ago and it's one of the only ones in existence and I understand it's cyber security people have to keep things close to the chest you can't go around explaining every detail of your system mad however if this best practice
doesn't exist out there for people to see no one knows where to start especially in OT this is a big issue now we want to do several case studies the main focus of this is of course rail but we're also looking to other sectors such as energy and this is a joint project with a company in Singapore so we'd like to do ones both in the UK and in Singapore and sort of compare how that is different terms of the project timeline we we're looking to having Alpha Ready uh sort of May next year sort of time um sorry may this year so I keep forgetting it's 2024 may this year um and we're can start releasing that to
select a few people um mostly operators and assist integrators to get their feedback find out what's helping find out what's useless then we can get rid of um and have a final release around April 2025 this is our my if any of you are in the railway industry you are operators systems integrators or interested in this toour you're interested in testing it or giving feedback about what you need in your day-to-day job please talk to us you can contact me you can find me I'll be around we're really interested you can go to our website to contact us as well we want this to be useful for people we don't want to be produced something over the next 3 years and get
to the end of it and find that actually it's no use to anyone so we're always looking for feedback and to find out what people are interested in thank you very much for listening cheers thank
you guys everybody know about IX
so where says absolutely yeah so
I'm aware the contradictions between cyber need to fix things as soon as possible safety need to do it the right way which can be slow and that is an
issue yeah man yeah
so is this currently being designed as a like modular solution where you could use different regulatory standards so outside of the ra sector so for example like Aerospace a software could it be I know you mentioned looking for case studies in different operational environments is that the kind of thing that would be possible absolutely so one of the great things about the rag I mentioned earlier is you can swap out in and out whatever you want if we're talking about a different industry energy manufacturing you can swap in the relevant um standards and regulation and it will respond from that instead and yes we are absolutely the focus of the project is for Rail and so a lot of the
deliverables that we have planned are specifically for ra however we're absolutely looking especially towards the end of it to look for other Industries and to test how well how interchangeable it is between them we understand there's a few unique things about the railway industry for example the fact it has a massive premises you think about the amount of land that Network ra owns it's unbelievable you know Bridges uh they own various fields that they don't do anything with own lakes and reservoirs you know it's just a huge business premises in the railway U and it's International as well you think about like the Eurostar that travels between UK and France and you've got to try and consider how to manage
the cyber security of like a international railway it's very complex however a lot of the same um principles apply in terms of operational technology you got to think about availability before you think about your security sometimes which can be quite difficult to balance so sorry yeah anyway thank you would you bring this in like it's a lify life cycle model so that you're also doing like replacement like servicing so it comes in for 20 years or whatever and if any parts need to be replaced for example like this AB security is considered availability things like that yeah so the idea is that this does cover your whole life cycle this isn't what the focus at the
moment is definitely on the left hand side building up your requirements but when we're talking about having the databas is integrated that is very much thinking about the whole life cycle and once you have all this data in one place it makes perfect sense to keep using it it pulls all the different exactly and then you can use that for ongoing maintenance and patching and new vulnerabilities appearing how you deal with them EXC thank you very much