Crit Get Hit
Show transcript [en]
um I would like to present Nick Dorner who's going to talk about uh crit get hit and give you some insights into uh automated scanners for pen tusting please give him a round of [Applause] applause great thank you so my talk is talk Cricket hit I examining vulnerability scanners for penetration testing so this talk is mainly aimed towards um anyone who's interested in ation testing but you can also use it quite a bit on the defensive side so there should be some value here for both offense and defense out of range there we go uh so who am I I'm a uh security consultant over at trusted SEC currently I have about 5 years experience in the field I
also work as a red team member for the NCA cyber games and also am an adjunct at various colleges in my area um right now I'm mostly focused on penetration testing and social engineering for my work uh this includes internal external um a little bit of web application and fishing fishing all that fun stuff uh today we're going to do a little bit of picking on a few mostly one vulnerability scanner uh you'll see quite a bit of it it's nothing against them specifically um it's nothing that I really hate them or I'm have any animosity towards them it's just it's the most common one so you'll see we we're picking on them for a reason um
and it's really just a lot of it's not full-on complaining but a little bit of old manuals at Clouds so who are we picking on um I think this this was expected uh just based off the name of the talk um there's a lot of reasons why but specifically in my line of work of what I do now as well as what I was doing before is I see nessus just about everywhere um I see nessus at my own clients I've seen nus used at organizations I worked for in the past uh organizations I work for in general um it's something that we just it's it's out there it's something that's used all the time and a lot of organizations will
really rely on it and I get some really interesting questions um from my own clients during uh you know readout reviews things along those lines um asking hey we use nessus we have it in our toolkit we're remediating the crits the highs uh even some of the mediums we're just trying to keep up with this stuff why are we still uh losing in a penetration test uh why are you still getting d why are we still having all these issues why are we still getting rated you know at these high levels of uh compromise so really uh there's there's a few reasons to it but we'll kind of jump into some of my some of my
excitement when I first started uh working in the field this got me really excited this was awesome I was like oh man we're we're GNA have shells everywhere everything's going to be awesome um I'm going to get da real quick um that's that's not really the case when you actually dig into these a little bit though um one of the things with Nessa specifically is a lot of this is aimed towards more um compliance factors and compliancy uh so you'll see a lot of these vulnerabilities are more SSL TLS is out of date what are you really going to do with that on an internal penetration test um things that you looking for are more along the lines
of something that's going to get you a shell so uh your Eternal Blues Blue keep you know all the all the good ones that we have our modules for and tools and this is this is where the excitement kind of dies down because you start to look at it and uh just a side note kind of tangent I really hated when nessus decided to make everything nested under mixed you can fix that now which is great but that that's really annoying um you can go in and you can see you know we have uh different different things here that you know are rated as a high and a critical but they're not necessarily things that are actionable
for a penetration tester they're ones that you can report on and they're great from a compliance standpoint um but when you're looking at a attack path or any type of vulner ability that you're trying to go in and use or chain together with others you can't necessarily take that and use it to to either get da or get your uh standard user and then either pivot and try to escalate privileges or try to get your your highle users so the these are some of the common attack pads I use I'm really sorry that this is an awful looking uh flowchart but this is these are the ones I I get most common uh just to get to Da
in a really quick and a fast time frame uh we we start off we just have a device on the network so you know whether the client provides a VM uh you have a DropBox something along those lines um and then my my first step is responder and ANM relay um it's really common aack path is to use those in conjunction together you look for areas where SMB signings not required you can then pass that that information along get your your initial access your foothold um if the account's got local admin that you've got then you can start using like proxy chains with secret stump getting that really good information um you can also take uh while you're doing your
responder onum relay you're capturing hashes actively also take those offline try to recover a password um once you have your foothold your initial foothold whether it's credentials um or getting local admin and dumping credentials that way um you can use things like cdpy that gets you straight to Da a lot of the time right now um you can use things like secret stump and then passing the hash and and just going through reiterating through systems until you find you know that that da account that golden account that you really want and then using that again the domain controller and just getting getting da that way um there's also password spring that gets you an initial foothold um you know what what
are we right now March 2023 explanation point that's going to get you a lot of places spring 2023 winter 2022 um those those are great passwords great ways to start um Cisco smart installs one that I've seen quite a bit lately um usually it's on internal the internal side you're going to see that um Cisco has said that that is a feature not a vulnerability um because of that you can actually go in you can get some really good information out of that there have been a few times I've even gotten da just because I've seen Cisco smart install is enabled you go in get the get the hash out of there reverse it and your da um now how this relates to
like nessus for example is we have a small key right here so blue the blues are in nessus what most of the most of what these uh revolve around are either going to be informational or not in nessus in the scan from an unauthenticated scan against your systems um same thing for the yellow that's going to be something that's going to be a medium and red is going to be high so the only one that that comes directly to mind when you're using responder and ANM relay there are a few vulnerabilities that NS will pick up with this um but SMB signing and that's rated a medium so SMB signing not enabled that's going to be generally
rated to medium by nessus itself um you're not really going to be thinking wow I'm going to get so much access off of this but it's something that really good and is really uh useful for trying to get that access uh spread across a network and then be able to elevate your privileges um password stored and shares so this one's a little bit uh tricky there's uh the reason I put it here and have added as a high is there's a lot of times you're going to see open Shares are rated as a high or even a critical depending on uh how your scan is set up with nesses um but this I generally use
with authentication usually when you're already authenticated and you can get access to shares or you can read some shares you can use uh your spider module for crap ex uh exec for example uh that's going to get you a lot further than just going in unauthenticated but this is still something I want to include because it it is still a point that they make to make sure that if they are unauthenticated and they can see get into those shares they're they word uh World readable that they they notify you about so so really um these are these are the ones that we came out with um SMB signing uh not required Cisco smart install enabled is informational and shares a
world readable High um one more note just on Cisco smart install uh there are vulnerabilities for rce that came out a few years ago that nessus will pick up on but since um that time and they came out with that being an informational now uh so if it if it's uh patched up to the latest version after that disclosure it'll still appear as an informational but you can still get in and actually uh go through that config file
maybe there it goes so so what does work um right now the these are the things I kind of want to talk about as far as nesus goes and vulnerability scanning in general um what what do you want to use it for um there's there's a few reasons not only as a pentester but also as a Defender so offensive and defensive uh it's really great for cves uh finding those CVS finding your systems that are vulnerable to to Blue keepy finding your systems that are vulnerable to Eternal blue um whatever the next new great exploit is that you know comes out and then you update nessus all the plugins are updated and it's detecting you know the
new RC that weekend uh it's really great at that um it's also good at compliance uh a lot of people you know roll their eyes and hate compliance but it is something that's out there it's something that a lot of organizations have to adhere to whether it's you know PCI compliance or uh anything that has to do with medical industry or anything has to do with pii so going in and making sure that that you're compliant is something that's important to lot of organizations but in my view that's only one step and that's only the first step on compliance isn't just a checkbox it's just the first step into making sure that you're properly secured and making
sure that your organization can properly defend whether it's uh your own information or the information of your clients and customers um it's also great for checking what's on your network um I've seen a lot of organizations that that don't have nessus a lot of really small small ones and we'll go through and we'll take a look at the entire network we'll use you know our admap nessus all all that good stuff and when you come back to them and say hey what's what's the system doing it's really vulnerable it's really out they're like we thought we you know threw that in the trash in a dumpster somewhere three years ago but it's just still hanging out on the
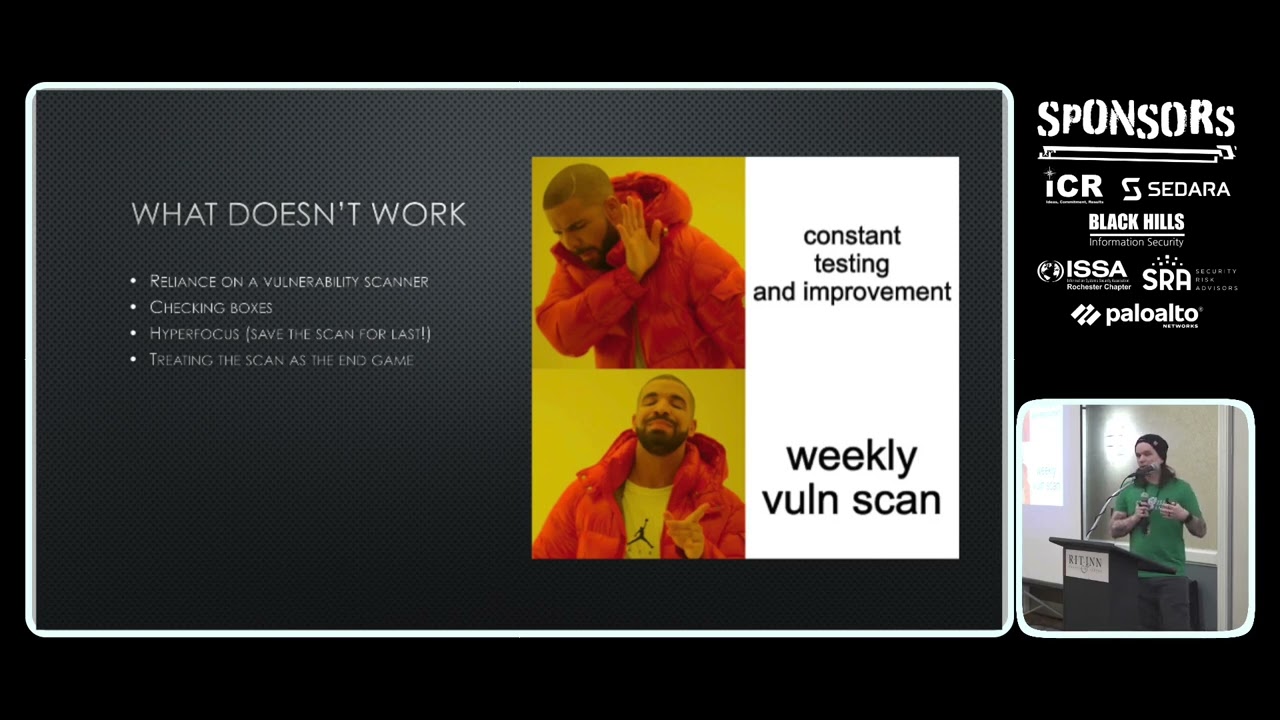
network uh responding to everything letting you know and letting you get in uh and and in my personal view scanners um I've kind of been paring this a little bit but they're they're very much a supplement um they're just another tool in your toolbox and they're just something that both from the offensive side and the defensive side are going going to help you better secure the organization and your and your clients so so what doesn't work and these are the ones that drive me a little little crazy especially because they're ones I wish that I knew about very early in my career um I I took a lot of a lot of losses just trying to
figure a lot of this out on my own but um Reliance and vulnerability scanners is generally something that's going to to be a real big negative for you um because of this I really like to run nessus at the end of an engagement so do all of your manual testing for example you have an internal from a Monday through a Friday so you have a full week for it um instead of starting off with nessus don't don't just fire it away try to stay a little stealthy try to see if uh monitoring detection is working things along those lines but also go in and do your Nessa scan on the Thursday or Friday and then verify if you don't
have da or you don't have your your goal or the goal set forth by the client by the time that you are reaching those last two days then go for it that that means that they're doing really well and that they're doing what they need to do and that you should go and do a double check with nessus if you can get any further using that information great if not you you did your job from a very high level um by manual testing in a very good way and you're going to do really well uh hyperfocus is another one um this kind of stems also from using nesus and vulnerability scanners first a lot of people will kind of hone in on those
issues and that they see in there they won't look for other issues things like cerp uh certificate Authority misconfigurations those aren't going to be really picked up by nessus um things like different ways that you can do poisoning and and tampering with the network and try to capture traffic again not going to really be picked up and that hyperfocus when you're just kind of zoning in on those vulnerabilities that you see from a scanner uh that's that's where you're really kind of setting yourself up to have some
issues so what what can we do better really a lot of it is um foundational knowledge in my personal opinion I come from Academia I went to school for my my associates bachelor's Masters and partway through a doctorate um so the foundational knowledge that we're giving to students and not just saying hey here's a vulnerability scanner you should just use this going through the actual techniques and pathing and how to either utilize them or how to defend against them is really a lot a lot more beneficial I think to students and making sure that they're able to take that information then apply it in their careers further on um also constant education um just making sure that
you're going to you know things like bsize Rochester things like all kinds of conferences uh educating yourself either through conferences free talks uh online news articles things along those lines and seeing the new techniques that are coming out that may not be picked up by a vulnerability scanner that may not be something that your company already has um preparations for so that you can you can better defend against new uh new and exciting vulnerabilities and uh I've already I Saw the Sign so we're running low on time any questions from anybody more than happy to answer any yes so how much do you coordinate
resp absolutely so so how much do we coordinate with the defensive teams to to go through our proper response when we're seeing these vulnerabilities um for for where I Work It really depends on where you're working what I like to do personally though is go in and talk to that defensive team now a lot of it depends on if the defensive team is one that that is a pure defensive team sometimes it's just you know Ed from it and and he's you know got the security budget here's your point of contact but a lot of the time what I like to do is notify the client at the start of the engagement listen we're going to go low
and slow we're going to start really quiet if you see anything from us if you start getting alerts from from any type of uh monitoring and detection if you're seeing things that are saying hey we're blocking all this uh stuff because it's doing really really poorly uh let us know send us an email we'll verify it was us and then from there we can work on was that a detection was it a proper detection maybe we don't hear from them either because they didn't get that notification directly or they just didn't send it on so that's another thing at the end of the engagement is say hey did you detect XYZ did you detect that we were running you know
default versions of responder did you did you detect that we were you know throwing Eternal blue did you detect that we attempted to log into 600 systems at once with one user um things along those lines and then try to refine down and see how can we enhance that monitoring and detection for them um in the future yes like yesol beginning absolutely yeah so so some of the tool what kind of tools am I using outside of nessus at the start of the engagement uh first thing I do every single time I go in I throw responder up an analyze mode and I just see what what's going across um it's not something that's generally
going to pop anything on me and it's something that I can go through and get some really good ideas of what I'm working with what kind of client I'm seeing um I also like to go through and do some small sweeps I'll do some things with um very small like light sweeps with CRA crack map EXA CME um that's a really good one to kind of get an idea of what you that's outward facing um what what you have to work with as far as SMB signing goes so if you do decide to go the path of a responder and Anum relay you have that list already compiled and ready to go um very light
uh end map scans uh end map and going through we use I like to use a tool called spoon map that's uh that we use and it combines n map with a with another tool and allows you to go through and uh pull out a lot of information and specify ports things along those lines okay yes um anything else
yes that's a loaded question um that that's one I can speak to you after about a little bit that's just um I know we're kind of running low on time and I've seen the sign already once um any any other questions feel free to come to me outside of the event I'm for the event the whole day um but we do have other speakers coming up so I'm excited to to see them and thank you so much for coming out