BSides Rochester 2016: Nitin Jami: Exploring SecAccessControl Obj in iOS 9 Keychain
Show original YouTube description
Show transcript [en]
hello everybody animus let them I'm going to talk a little bit about is each ate some improvements on the kitchen itself and how as a dentist or security researcher it will be useful for you to know some of the kitchen i'm a senior security consultant with the SEC group just work from Arkansas yeah I both of our mobile security I specialize in is I think I specialized my ass this lack of work to do I love to understand although predators for maintenance my current research improves my poking around OS X is a lot but i do work on Windows and Linux as well time comes I'm author of each a redditor tool that I we
should be missing you as well as each at you and if you are it is a movie app and this is my first time speaking the conference thank you so the basic outline is very simple so a little bit introduction about is teaching why am I doing this for evocation of my ski jet since its inception after is fine and then something the Christian has changed for my essay and that is the axis controller object will be looking at it and then finally showcasing both the rules so um assistant teaching is basically of a secure storage puddin pie OS operating system even think of it as a password management tool or where it would store all your secrets
certificates and anything I device I think it has a gap of foreign me but having said that a lot of secrets will be stored in a speech at hand it should be floating them oh it's a single teacher for all apps or however we'll talk a bit about practice groups and that is how the isolation fragments and each app each at this is only able to access its own item or or if of fits like a glove elephant access group then you have a set of applications from the same developer team safe house urban blacks is that I hope it's maintained as a simple I database and that's basically the path DJ Clue database that's over
them and the different classes for random as a generic password Oh Internet passwords for Safari and stuff and then search includes anything like so those are all battery but spring move along to the important stuff that is the rate of production and if you have been out here at the debit should stop it's pretty similar on how of the progression from under me and all the tea bags that allow or when I think amount of time so I'm not going too deep into the kitchen is already being taken care of so what I am going to focus is just the the user layer just the surface and it's very analogous to a file system production
you have like when unlock after us unlock accessible always which means when are no updates only that this item is available when the devices universe is unlocked and after personal mark is when the item is not available under sorry that I'm is available after first half review so always is the nice prediction and it's never in prepared so but think about some considerations oh the night's dinner prediction the latest stability sequence your apps so let them love this the default right now which is like a little bit contrary to the anise fire protection wear ananas fire protection its after question awkward Jennings phenomena but that means that if you're a piston some backtracking work you wouldn't be able
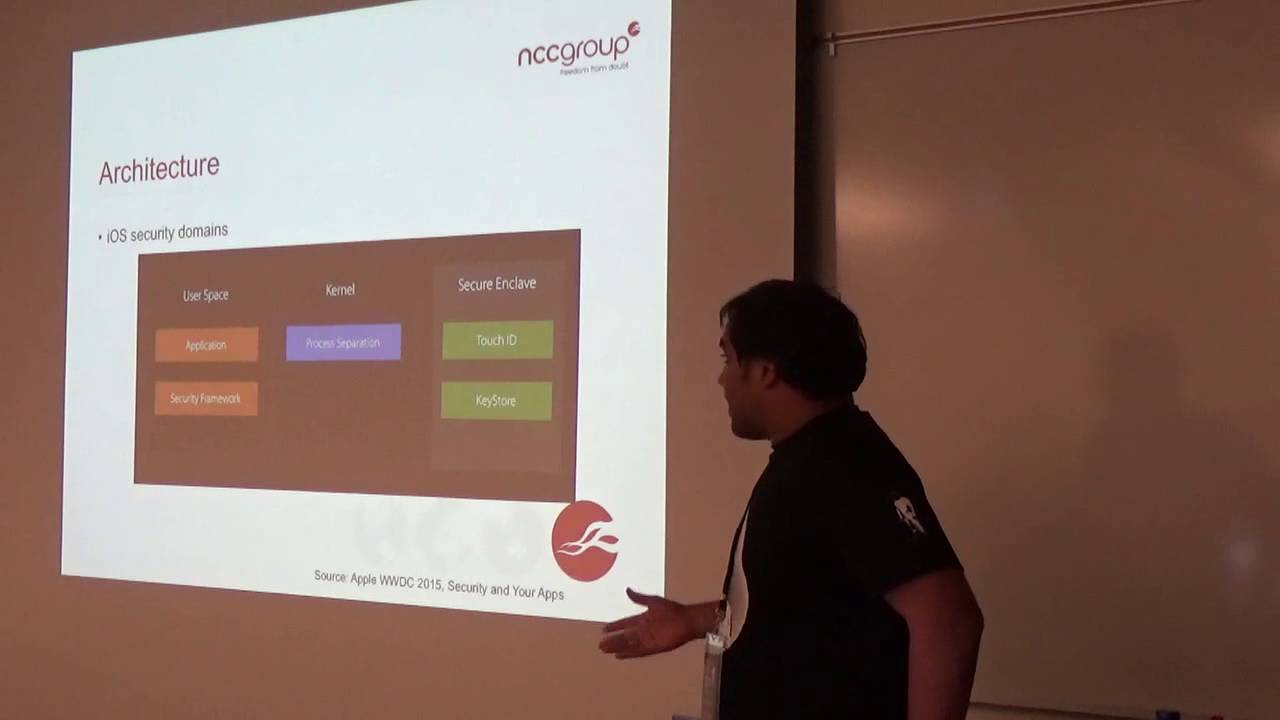
to use it so you want after first look for bad when the gaps and the most important thing is that accessible always would be deprecated in iOS 9 but if you still see the iOS 9 API lives are you see that changed from from about to let a constant so that means access below resistant is so this is just to give some perspective on how how an item gets stored inside the secure and clear using the kitchen so the application of security from the current user space and your application put Adam would use one of those security networks aps like second side we do better to add an idol inside the kitchen the security framework runs our
demon as well of that demon takes care with our our problem with the colonel on adding that item however if you see that Keystone prior to iphone 5 i have 25 or free based devices they do not have secured and kept secure and Claire was introduced in icon fires and the keystore was stood in the kernel so that means and all the cryptographic keys that are useful for for the kitchen items are very much accessible it's only from our pious you see that the keystore is safe in the second round clip and if you have been litigated stuff he basically talks a little bit about secondhand try on how security at present so you could use a touch ID or
device bus code to further access one of those items and we talked a little bit more or how that goes above so like I said using the kitchen definitely clears our pilots wears a very small set of a ps1 compared to present for ad copy matching is basically like extracting the keys out of the kitchen and then there is a degree however in order to get some more reserved useful features there are underfunded same functions i get prediction on credit and strength so here is a reminder so you would want to know like what kind of protection this item must have a hand if you want to flag it or not so these are the functions that lick you know
so these are some important attributes as far as the kitchen Stinson account Magnus of anything that your app tries to store we can think of it as like a continent inside your application or just use the name of stuff like that so account names can be mainly for a single application service no man is basically like a number of us were to an app itself you can have more of these things as well but there are movements like Oh within the service name and then Isis group that is what I was talking about right here access company finds like defines the bonding for each each an item so if you do not want to share an
item with any other apps then your access group will be only for your particular option for your application but so but if you have more than one application you could use this access group to to give that I don't do more number of apps but it still needs to come from the same developer intimate it needs to be sent from the same developer and protections that is what we are interested so accessibility which I talk to you those are always worth looking at
so of research books and that is why I'm here today so one of the main motivations behind as it is that we all know we all recommend as a security and serpents that drunk kitchen is the recommended storage area and stuff but but it needs to be noted that not all that refers use the keygen and city of me so most of the times you see that all these items are are like use the least amount of protection like accessible always and this happens because and when we talk to developers we understand that as the app for spring they do not understand which application needs to be used with the full protection like monaural of garbage application needs
which i can sorry which I can needs to be used a while back running so if that does not work for some reason they just switch on this just switch to access a book always for all the items so that's the application just works for them and it's still to this day that we see more and more applications use accessible always so it it is a good area for a century tea vendors to look at it and come from that ledge if if an application using an on the kitchen it should be secured problem however they are most previous work but since I have said a lot of tools have been stacking great and this
is because a lot of restructuring of Boston within the file system within the operating system as itself from I I say and as I brought a lot of changes Iceland even brought more changes so all this previous tools uh no longer supported right now and keychain is sensitive so we would want to hack it in case so the previous work you guys have already heard about jackie chan kin-por a keygen newer which was which was really working well kill is 6 and ayah samish but after that it wouldn't work and the way for a kitchen where these up these tools for moment will go to focus only on a jailbroken device because of Jake Brooklyn a jailbroken device but
would disable all the integrity checks or write code signing or entitlements check so I did now have an application with an entitlement as star so this is so like I said a real kitchen access group would define life what applications put your food item have access to but if you just give a while silently that means your application will have access to all that the kitchen now this books because there is a demon world Anthony which runs and most of the jailbreakers in order for them to run their unfettered court lady they disable equity this that's the first thing that they do open the jailbreak so I am feed is the Apple in mobile file integrity
demon and that demon is responsible to to validate this and ask them in fact with that of the apple key and since that I'm feeling you know who works properly now we could have an attacker and run flag with about anything and we would like to have a star which means that we can have access to all that I'm said we could dump it so the main motivation behind we're doing the research on teaching and then writing tools is that like I said existing tools it work on your eyes movements I'm pretty sure I aside and I assign those tools would not work and we talked a bit about the evolution of the kitchen we'll see that pious 8 as a lot of
changes and therefore there is no support absolutely no support and one of the things that if you if you run if you manage to run the previous loops you will see that instead of these long I hyperx is about one block you see those sharp homes anc IDK which are basically the same thing as this but those are the internal representations of that and those tools would just display a casing getting in which gives a lot of problem that we point to any standard and the doctor is the number be you really huge if if you're you are dealing with a lot of applications that the dump would be really big because applets of source a
lot of fun times in his kitchen and on top of that there are many applications on the phone so there is no big church through out of that place sure you would regret but it would be nice to have something in Whitman's at the pool itself and then Eddie editing and deleting kitchen on the flyer yes but most of the times what happens is that you invest a particular application but then but then you want to edit or ticketed sure you could delete the application but anything the application does not ensure that the item is related so you'll have all the settings in the kitchen asses but you want to delete those items so now we would use the key
generator whether tis the item or if you want to edit it on the fly and see if the application behaves differently adjusted it so let's talk about evolution of our sha also one of the important things that was introduced and that was introduced in iOS 8 is the multi-factor authentication so up until now we know that all the items are so when you use like one unlocked items only accessible when the device is unlocked that means that you enter your passcode your device's unlock now all the key is related to those particular items are available right now so that's why you get those items decrypted however so they introduce multi-factor authentication that means that you need
to have another layer of another layer of our guarantee that you need to learn the system that hey this item can be decrypted and that is by either giving the device password or a touch ID so if you see them how if you open your banking applications and everything it asks for on another another authentication to later keep your budget itself is you fall back to the best possible so that is basically multipacks of information and it's used by both the teacher no BS in the local occasionally and I'm not going to talk about local a complication again this stuff because that is it is only likely related but it's still a good good topic
to explore but that is not what I'm good so n is 8 apart from those accessibility constants of a very welcome change is variation of when passport said and what this basically means is that an item can only be stored in the kitchen if a user has set a passcode on the device so we have said users who do not use device password they do not set wave as password so if you have like super sensitive application like a banking application on if the bank really wants to make sure that their application of their customers let I secured they could use like 1password said that means that it forces the end user to actually use a
device password if if the application from sure if the if the device parts Corp is room or after the application is installed on its mission then that I can get my directed by default oh so that's the new accessibility constant and then there is this new attribute for access control and I just control is basically what the multi-factor authentication is so I gives more fine-grained control over each item like when we decrypted so vitamins no longer decrypted as soon as our devices on rock you need to give a secondary or authentication to it and for I said there was only one policy that was available at that time that's the user presence so user presences
basically that means that they the device password opportunity to further decrypt that pitch an actor however in I a snide more policies were added also in relation to user presence you now have touch ID any or touch ID parents it a what touch ID in your concept mean is that so on an iOS device currently you can have more than one set of fingerprints android so i think the maximum it is fine right now so if you have hid any that means that you could enroll or tea n roll the fingerprints and it's still a valid of valid said but if you use touch ID current self so let's say you have three fingerprints enrolled at the time of the application
installation and if there is a fourth finger print and roll after the application is installed then that item gets in violated because the parent said would not is not matching with the previous set so the way it does is that it takes a hash of all the fingerprints of the three from difference oh and it checks for each time whenever that item is being accessed and if that hash does not much like if our finger dress be enrolled or enter then that item gets invalidated so that is useful and lastly the device passcode oh so that means that if the if the phone is if the device is not supporting Pacioretty then you could just be fort lee pretty wise
passport on an hour and are just the logical operators and then two important additions are also the private key usage and application password now private key usage means that a particular item that is being stored inside each attack will be used to basically sign a sign you need anything you want to have some side later between the device and the server between occupation on the server you could specify there's an item that data can be used as a as a sign in here you specify that by saying that private key usage application Palace one means that in order for for that item to be decrypted it's not just your it's not just your device passcode
of touch ID it also requires another password that's that comes from your application so that means that in order for an item to decrypt you need now you need to have two passwords one comes from the application that could be like hard buried within the application are like a good fetch from the server on the slide and then your device password that's ready so yeah so that's a basically all the changes that we have and so let's let's see what basically all those access controls is and why is it useful so as if I'm tester you know that there is an item over there and if you figure out that it's being used as an application passport then you want to
go further investigate how that secondary password is coming a bit comes from a if it's hardwired into the application of minor itself so that's bad that's the final process the good way to do is to fetch it on the fly from the server keep it in memory and then discredit as soon as it's used also for things like that would you really want to know like how the developers actually actually set the permissions to that particular item and in order to able to do that we need to we need to understand what is a access control object so currently there is no atl to to see that what so there there is an idea to get the protections
of like if what kind of protection it's being used but there is no api to know what kind of access control that item has over it so for that you have to do a little bit of reversing and then understand like how this this access control object is paying it so if you see over here this is a simple query to add an item to set a time i takes an inquiry the prayer is a dictionary with class set will generate password I found that one hand service service name and if you see over there that's the access control with a ACL is a is if it is a constant over on the top of which is a
written value of seconds is control create with flags so created flats takes two operations or one is the one is the protection accessibility constant it is and the next is actually return strength or the policies that we see I've seen earlier that's the user presence over here so when all these gets into it gets gets it gets built into the wedding oh and then it's being added into the keychain so let's see oh whatever what such are being taken when this dictionary spill is being built so the first thing we need to know is what actually like constant acrs so the written value of this create with flags is an option say access control so it's
something you insert the options and I really likes with for this only reason that it gives you optional where it means that a variable can have a value or if for some reason that value fails then the variable is by default set to live and if you see that if flip is a is like a unwrapping of that optional so oh the code path is only followed if there is a value in the ACA if there is not a value then you could just go into that is blocking on print or further but anyway so the Sexus control is an option value and what basically sec access control is internally it's a structure but sassy structure with to various one
is the runtime based and the other one is the dictionary so randomness is something something that we do not the thing that we really care about is the lectionary because that is where all the transitions are being set so the first call of when that API is for a user level intimately the first ball is going is being made to the SEC access control create where it creates that dictionary it creates memories intentionally and the second call is immediately went to the set protection the set protection is just at the one is the accessible by my blog so now when you access the is the structure that it's rated side it you will see that the protection over here
is set to AK which is when Allah and then the next step is that to create a a sub dictionary within that the bigger dictionary and this sub dictionary is actually the ACL value you can see over here from there only be if you dump that particular memory address for that big smelly you see that ACL is a second secondary dictionary inside every dictionary and for that ASEAN I college main again two beautiful constraints or double constraints of his friends friends are whatever the flags that we human at the user level whether it's a user presence for now so now we have addiction inside a dictionary that and we'll see how the page ACR gets
better and so like I sell flags determine the overall structure of that ACL dictionary and if knows of policy is not specified that is like if you just fasten mill instead of the user presence of the top then the default ACL is set so the default ACL means that there is no access control on that particular vector so you see Vinny Mac's is the dictionary you will see that the the ACL dictionary will have a de sel which is the default access control list and set to boolean value 1 that means that no access control policies are set on it however if a user user presence policy is specified then we get free built in
operation set for the side and the new items are the OD hotel and OD OD what cody is this that is so we'll take a step back and actually understand what these operations are basically an operation is is basically like what kind of an action can be performed performed on that particular vector so that means that you see Bodie is off decrypt so that means that an item can be decrypted odense an item can be deleted also that is the operation that can be performed on that item and OE means that an item can be encrypted as well and then for privately you said you see oxide and op sink is for op Singh is used for iCloud
sharing i clogged kitchen which is not used at present yet so now if you see over here in our dictionary will see that there is Goldie Odin OE hotel and olya by default set to true because like every item is encrypted by default right so whenever the device gets unlocked by default it just encrypted so that is that the true and any anthem should be able to be deleted so again the operation on that item is like totally is settled but the important thing over here is that when an item gets decrypted so it means to me only decrypted by based on a set of constraints that were specified and the constraint over here is that the CEO is
basically the user presence constraint which is set to devise owner authentication so that means that you can either specify device password or you could specify hid your you will be prompted with any of one of those um instead of user presence if you have like HIV current or touch ID any you will have a different different set of constraint mentioned over here in order to decrypt that item and similarly you will see for private key usage as well so that means that there is the mapping between these operations and the constraints that are being set oh and that mapping is basically like when you mention an item when you give an access ACL to an icon as like a user presence
device password natural energetic current set my default you will have these three operations on a particular item these three operations are set on that item so that means that as a security researcher if you see these three items you would be sure that this item is being is not being used for an private key usage but it is being used for one of those four above-mentioned things and going further if we go further the the dictionary will know for sure that which of the constraint that is being set on that device so if it's a CP ER than you know that it's a user presence so as an appendix where you will know that yes we have we have used
as a presence at as an easier for this um luckily for me I I was going through some documentation of and luckily there were some undocumented apx for me so which from swifty but just call them are what you need to do some sort of casting and if you do like cell access control gate constraints and then you cast a CL OS x axis controller object take the unwritten value and then again cast it as a dictionary then you the the constraint over this a variable you have addiction to be like this so now I could use the Swift dictionary to manipulate this dictionary and access the key value thing oh so just started to understand what this lineman line is
over here is that a CL by default comes and as a sec access control reference also that's still an object but the ! over this is that there is a valuing a sealed so since its site access control gates constraints is a see as a c function we cannot pass into it and for that reason we need to say it but we need to tell Swift that there is a value you can go all this with the c function and they unwritten values anything to do with the art of the memory management stuff so what this means is that so the object the asean object is being accessed over here but once this operation completes then the pointer so
this is how the memory management works right so you have if you have a number of pointers then you have a power for it so if you have the five pointers you have a 55 home to it and once the once you go through the free function then those found get dick and those down get decreased 20 once it gets to zero then that memory allocation is free forever so what they come reading value does is that even though there is a point to remove to it it does not decrease the count of that knocked out yet this is important because when this function the it's written inside a function in this fence or when that function exists
automatically Lee differences but for their ACL object so if if I need to tell if I depend on Swift to take care of freeing the object I need to do and take unwritten value if I want to free an object myself than I just take retain value which automatically freeze the object over here and finally a casters as a swift dictionary so that I will be able to book it by just doing like a key value so so that's basically about psychiatrist moonful object now we know that we have a dictionary and based on that dictionary we can map out what constraints that that the item was originally safe as and key generator I'm technically not introducing because this
has already been released and it's it some- page also have a blog post once but the main features are that this would provide you too you know dump the riveter edit delete a each an item and supports very well is a tangible and it integrates with ID be so I db's at all if you guys not already know it's a static analysis tool written by my colleague for basically doing I'm expand testing also the usage is that you have a detailed of health and I were to use and I'll just show a quick demo later on but some important functions are over here is that the action will will either take like min de combate de some minimum notes of when I
used to dependence thing I always I most of the times I do not from the I found him on the surface name of a particular item that I was looking for so in order for that I need to dump the whole agent but if i turn the whole kitchen it's basically like this with a lot of stuff and I need to go through each one of them but instead of that what I did is that I just display that on hand surg listening so that's like a meaning it up and this will be a short list and you would quickly go through what application you want to look at it and you get the you get the full reverse
reverse name of it so something like comrade face after their faces if you're looking at some application you'll have calmed or convenient or application oh so that's min done and the other feature that I was talking about is the search functionality within the term so search is basically contains operator on hmmm service name access group and access to the constants so that means that you can specify action and stuff and then you say you only let's say only want to find a list of women block diagrams and you just do find when Allah you get items that use when I'm locked as I accessibility constant so here's only just three 3i times so likewise you
could just search for i hope you my service name and you'll just get a short list of that no need for everything and I got a pull request saying that I need to support x vampires but I'm planning for that to do that something also this teacher named Victor is like 6am months old and already wrote this one I said was amazing at that point of man so that I only use a presence was only only policy or constraint that was available so i just use a boolean value whether that item has access that will trick on accessibility so the access control or not but i just say no aureus and it it as again like i said earlier if you want
to edit a particular kitchen item then you use the Edit action however this whole thing to note that since it's a database and item needs to be identified unique and the way that an item is being identified is using a 3 pupil of a condom service name and access group so these are using this three pieces of information you guarantee that an item is unique however access group is not required all the times it is only required when let's say you are dealing with ND stuff and then some names are complicated um so what that means is that when you are dealing with MDM you will have a duplicate period of service and that one
I'm confident services so one instance that I'm at her face was so the RSA is a by default gives you an RSA library but there was this MDM solution where it would also install its own RSA library it's the same piece of RSA library but MDM uses that is a library compile statically so it gets installed and that RSA library stores in kitchen item again onto the kitchen but since the lamb diems access group is different from that of the ious operating system you need to have like a three people do I get a differentiated version of it which item you're actually poking at if you know for sure that you're not dealing with MDM stuff then you you're just
parented with that found remnants are listening that your second will be unique and right now I only accept basics before infrared data because I don't want to lose any form of information when entering because there are a lot of physical to enter that might create the pool work just break the encoding format when it's inserted into the room oh and then finally to relate the same uniqueness to ad infinitum uniquely the same thing applies over here it's just that the argument you're passing is one less of it you don't pass any data argument you just us and this is the ideal tool that i am showing us so this gives like a sweet honey GUI interface and the kitchen is
integrated with the itbs work so if we put it on your computer and if you just hit done kitchen it will call my tool it dumps the kitchen and then you have like delete or really buttons as well and today i would like to also introduced each anyway it's just the same tool but i just wanted to learn Swift and i wanted to write the GUI f for it I just heard a small UI application I also know we have used one of my close friends to help bread that you I us stuff that really don't care about when he was trying to mock me he had a pink tab at the top word so it's again a similar set
of things that it does liquid search for a condom serviceman and then dumped or if you don't give any of it than absolute list of things would it just done so something like the u.s. not pretty and just getting there but so this is since this is stephen am I think these creatures are from bias emulator so all the are so there are only three items for this purpose and when you click on one of the economy service in America then you will get a full list of items and so you see their protection the only problem and then there is a degree but not about and that you have an edit button at bottom but it'd be nice Oh the
only problem for me right now is that I couldn't integrate the access control into into the release version is because there is a slight problem with the house with so I lights web Swift works really fast it's easy to write but it's not complete yet and it brings a lot of problems when you eat with the bridging headers so if you have since I'm dealing with like undocumented see functions it it's giving me a few errors here in there and that it's not really stable right hand side I want to understand how swift works how the Swift's memory management works like I was telling earlier that a convenient value was one thing that helped me helped me stop that
free or double free I need to identify simpler cases elsewhere in the board and then and then I'll just have access controller than humans a new here which will tell like Mitch constraint that item has on so yeah those are the dunes obviously the front of the future because that obviously a lot of work remains from 40 stores and I try I will try to keep update with new versions of iOS and hopefully it would be helpful for everyone and less but of course internet password and certificate so not support elliot up I haven't had a case where I had to dump these of these items yet but if there are enough pull request then I would think about being
and unite passwords and certificates as 40 again our I estate onwards there is I club Egypt so the web sharing where the kitchen items get synchronized across all your devices that is well that is something that I have to work on on my 20 and in general I would want to go deep in the I ask each and stack itself those are like badly and I showed you the architecture of how the how the kitchen works and something to workers towards securing them how the whole code path goes into secure Enclave cover each and hundreds of sword so one thing so if you were in David should stock so David was telling that it's not totally clear
like weather and an actual item Dixon cryptid or the metadata for that item gets encrypted from my experience I think it's the manner that gets encrypted because this is only for each and said so remember that I said that when when passcode said you didn't win password said if you use that particular accessibility constant and if you remove the device password later after the application will store then the then that item gets invalidated by default it gets deleted but that's what document says but in practice if you still also if you dump that item the item would not show fine but if you use the command line tool and if you try to delete that
written than that I can gets deleted that is that is the point when that item gets delayed so when I beg a little bit of understood that since a lot of properties are added to form a hfs+ file system that is what happened uses there is a there is a new attribute not some new attribute it's been there for a while the attribute basically specifies that whether an item is accessible to the user of month so when the key gets gets thrown away then that particular item is like you know I said to unavailable so you never present it with that I can but it's still there in that memory it's going to date in the
and when I force it to delete it then that particular item gets deleted that is one it is really so interesting stuff like this so I want to dig deeper in debt if you're interested in me and if you ever use the tool and if you if you encounter is these file issues on guitar and happy understand I'll take any questions you took any work on Wi-Fi or keychain of realizing for the tune or in general just in general so it does it just sync the file is the yes my dear is it does addressing the file across all your devices the only exception is that if you see
the only exception is one that left our accessibility constant is said to this device only that it would not sing across devices or it would not get back up back up so each accessibility constant will have its own set of keys cryptographic keys for it and this device only a banking is only still within that device so for some reason of that but he is less than that I can ask us forever so yeah
all right thank you guys thanks for