OWASP Won't Save You Here Tale Of A Modern Web App Challenge by Tas Tondang
Show transcript [en]
uh hi everyone good morning uh thank you so much for being here a bit early in the morning Saturday morning so I really appreciate it uh yeah so as been introduced we'll be talking about olafs and also Tech of probably framework that most of you use in this uh room uh like how it won't save you here we'll be talking about like a real life uh case this is a combination of like web application uh detection engineering like social engineering everything in one and how like everything is not working all together so start with disclaimer uh this is actually my own personal research this is not related to my current work at Microsoft uh and I'm
trying to fit like two presentation in one presentation so like 4 hours of content in 25 minutes so we'll see how it how that works out uh not here to name m shame uh not here to sponsor uh any product or anything it's just like something that I want to share with the people and I'm not a threat Intel person so I'm I'm trying threat Intelligence on my side on the side uh with the group called created Intel uh so you might feel like something is a bit off it's probably off so yeah so let's start uh Little B introduction I'm Tas U manga Tas task manager on socials you can find me on LinkedIn also uh I'm a security
researcher at Microsoft uh curated Intel member and also DFI report uh contributor I I Love A Long Walk uh on the beach of security locks so yeah so that's my passion say to say uh today again because of time limitation we will only be talking about three topics uh I've done presentation uh related to this it takes like 1 hour so it's going to be like really compact version uh feel free to reach out to me I can share the previous contents and then we can talk more about it if you want to yeah so we'll talk about the problem uh the the real world example that I personally F victim for and then recommendation
when Olaf's plus M attch doesn't even uh suffice to tackle this problem so first thing first the problem there are a gap between Security operation and also application security so we're talking death Cyclops when you're developing applications when you're doing sasy Dy all those stuff they are gaap and uh the the two framework that we uh people are using in the corporation there oaps and there's attack so I think there's a lot of students here uh so just a brief introduction to ol it's literally one of the best framework for to safeguard a web applications so we are talking about anything in your mobile phone it can be protected with o so it will be used mostly with absc
people de psycho people and then on the on the other side attack it's a framework being used by Security operation people sock uh defensive you name it blue team uh so they'll be using that so it's a list of known attacks known uh mitigation non detection so it's like a really it's almost like a Bible for defensive mechanisms so let me ask you a question uh fishing uh so we get OAS upsc on one one side we get uh detection uh blue team on the on the other side so who is responsible for fishing uh who say oaps can you ask your hand sorry raise your hand when you say my attack or like blue team anybody
agree Okay so we see it's more like in the attack so yeah so which Tech crime workk I guess it's going to be attack uh that's fairly simple if the victim is your corporate user right but what what happened here uh and this is a real work examples we'll go de deeper about it so the first thing is so you have an application you are you are a platform that let a seller selling stuff to buyers so your your Merchant received a fishing email with malicious attachment uh the Second Step the malicious attachment it's an info stealer so the thre actor stole their password token Keys all the nhi everything that was presented earlier today and then they
use it to log in to the merchant uh account so they have access to the merchant account so they can see all the transaction they can see all the information about the customers etc etc and then they have all the information and then they send a fishing email so there are two fishing happen the first one and then the second one uh and then through through your very own chat function so your application have a function for the seller to chat to the buyer so it happens all in your ecosystem and then eventually you lose uh customer trust because they felt victim for it both of them so the question here like who's responsible here so I guess that's that's the
question here like where do we draw the attack surface line so from there we see some gaps already so the two team that I've mentioned they have different budget they have different personnels they they know different things they are mainly working on The Silo kind of like systems so they don't really talk all the time you probably talk to them once a year or something like that during like a general security meeting like big meeting with everyone in there uh they have different priorities so if you tell absc to protect the fishing they're probably like oh that's like a matter type stuff why would I do that it's not in o or something like that and even
even The Blue Team like if you ask them to protect the the customers of the app and they're like that's application it's not our business this is not in the realm of the corporate world and then they have different languages as we know there's two framework uh I will not because my my main framework is probably matter I will not have much knowledge of the oaps so it's probably the cases in most of organizations to so we'll go deeper on the real world case uh so yeah so the first the very first thing the merchant received an email from with malicious attachment so it's a so this is a hotel booking system uh or let's
just call it booking.com because it is booking.com uh so yeah so you probably see it on the news yes uh so yeah so they they fish the merchant so they they actually book the hotel and they message them hey I have a booking and there's some problem with my booking can you open this file this is my passwort in the Google Drive here's the password for you to see it well that they know that it's actually uh you know like infos dealer so secure Works actually posted this research earlier last year uh so so they get they get brid pretty much uh a lot of hotel we are talking I think it's like thousands I've from last year till like few like
yesterday I booked I think like more than six hotel in booking.com I Reed five fishing chat all the time that that's how really bad yesterday was even worse because they chat me in Spanish I book a hotel in Japan like it's just like super weird and I'm I'm English speaker so so yeah if only they have information where I live you know uh yeah so so yeah the go to the Second Step It is an info stealer so it is again confirmed by secure Works they do like all the uh need stuff mod analysis and all those stuff and it is actually a fedar info stealer it's a really Market Common Marketplace info stealer and the worst part when there's
demand there is always like people trying to fulfill the demand so there are people looking to buy Hotel admin uh you know like credentials in the dark web so people will be like more keen and Keen exploiting the hotel uh hotelier to say so yeah the full TTP is pretty like I will say straightforward but not really uh so so they do the initial booking and then they they ask uh they they perform a reply hey I have a problem with my booking and then can you see this they they send the attach file they use password to in order to protect from uh you know like email uh malware analysis automated analysis so that's
bypass that and then yeah the and then they they get they launch the info stealer by accident and then they they get all the credentials and then they start doing the second phase of thing which is uh using the stolen credentials they'll logged in so booking come when you are a user they have different login and then when you are the the hotel year you have different login so for example here uh that's the login for the hotel owner so the question here Hotel owner when we talk about it of course we have Marriott with you know their own security team and then we get some nice lady in the you know like little town in
Italy like I don't think they have security team if they have like well good good for them uh so yeah so they're able to log into the merchant profile and then gather all the information information related to booking so uh the problem with that they are you they are smart they use the tools uh I've I've did more research on the platform itself I have I have a copy of the source code of the platform uh there will be not enough time to talk about it here unfortunately uh we can chat about it later so yeah so the the fishing is really bad because first thing first they have all the information needed so they have my
literally booking number uh they have my hotel name my hotel uh location and they have everything pretty much and then for example they send a link and they put the reservation ID in it although the link is a little bit you know like there's some typo and stuff but uh the reservation idea I probably thinking like oh there's no way fishing can get those information but I guess I'm wrong uh and then they they actually send the fish so that window over there those are actually the official uh booking.com chat if if someone sent you a message from official booking.com chat you will not ask second question I didn't I clicked the link anyway uh so so that that's even the problem
I'm a security researcher and I click the link thankfully the link is not like stole the credentials right away so it's actually asked for credit card information so for example here you see this hotel uh the booking.com the web page is literally the same uh with booking.com why because they use literally booking.com code to to write the fishing if you compare the class if you compare all the element of that it's literally the same the only difference they have a lot of JavaScript in the in the back uh processing for processing the data and validation uh so for example yeah if you don't put the right phone number they will tell you oh this is wrong phone number this is not an
Canadian phone number or something uh so they have the hotel name the hotel address the picture of the hotel uh from the legitimate side they have the correct checkin checkout date and they have similar price when I say similar here they don't really know which currency that I'm paying to I think it's because it's probably protected in the credit card uh area uh so they don't have that information but the rough uh currency after you know like uh currency exchange it's almost the same so that kind of uh interesting for me and I once you enter all the information of course I enter all the information not with my information don't worry about it uh and then we get the the price again
and then they ask for credit card number uh oh my bad my bad who did that uh so yeah so the interesting about this credit card number for example you have MFA these days right for protection you have I think they have 3DS something like that in the Europe so they they keep that in mind they actually have a mechanism in the backand when when it asks for MFA they actually have a telegram bot that will send like a message to the user like hey uh this you need to send MFA and then they will put they will reply to the telegram board and they send the MFA code that they received so pretty much the user already
breached again like how would a normal user know because I would say half of the people who probably fell for it uh when it happens to you uh so yeah so that's that's really bad because it's all happening in the application security area and nobody is taking responsibity for that and then what happened next uh so yeah everybody fell victim for it so previously it's in booking.com now it's an Expedia Airbnb aoda in Asia there's a lot of other platform uh this this framework called telecopier which is uh uh ESET just recently released like a full uh paper on that so you can check on that so for example in Australia Australia is the smallest area
being targeted so they have 900% increase I think the loss is about like $200,000,000 of people something like that that's the smallest area the biggest area is Europe Poland like Romania Etc they get targeted more and we don't have the number we'll probably talking Millions hundreds of millions we never know and then even worse when uh Taylor Swift Philippines forum is talking about how there's a fishing in your website it's really Niche and yeah it's not good for your uh company so what what we can do better right uh here are some recommendation that I would say so again we get the three problem that we identify or the gaps we call it uh so
there like uh lacking of cross team collaboration so it's important to connect the different team sure we do like oh red team blue team purple team uh you know just mix the color but what about absc do you mix it together do you include it in your uh you know like end to end kind of detection uh or protection mechanism so it's always good to include because when you're pushing out application it's becoming your own responsibility to protect like who who going to protect them it's it's not going to be like some random government agency or like some you know like Microsoft Google or anything like that it will be your your priorities and if
you lose trust on your platform that's it that's that's your bread and butter that's your business right and then yeah you need to align priorities uh you you have to mix everyone together create an end to endend from the application development all the way to the end for example when you're building application you need to infall for example the Security operation because they know for example how to detect malicious users because they've been doing it in the active directory in the cloud Etc so you can learn a little bit from them for the upset fults and then common language uh you can create your own in a sense but you can always uh kind of like teach
each other like the lingual that you been using so that's more like high levels let's talk about uh Hands-On recommendation that you can Implement so protecting the merchants or like the seller uh so they get uh just a reminder they get breach because of the uh stolen credentials so we need to treat them as a corporate so you protect your user when they're when their credentials being stolen you know that it's not them when they're not logging from their usual ISP when they're not logging from the same country when they're logging from two different area so we can use that also here sure it's much it's much more money to spend but comparing to to the loose of business uh
yeah so it's it's something that uh you need to reconsider uh secure practice of course uh teach them to utilize security best practice such as MFA uh how to identify fing and such intelligence when you receive you probably receive all this information as a corporation before the user uh so it's always good to share that in the form of email you put it on your uh web page on the first page of things so it's always good to do that and activity monitors suspicious activity uh for the merchant account for example when they suddenly send thousand of chats to uh multiple user at the same time when they send uh suspicious links in the chat messages so all the
activities uh in there like you have to kind of Monitor and you ask like oh we didn't log uh the chat I mean like it's your application you can log it if you want it right so you can you can you have the capability to do that this is not like teams this is not like slack that you don't have access to it's your application whatever you want to put in the lock you can put it in the lock don't lie to yourself um and then protecting user pretty much the same most of the time time uh identity is the same secure practice is also the same uh intelligence it's probably a bit more different you might want to use your
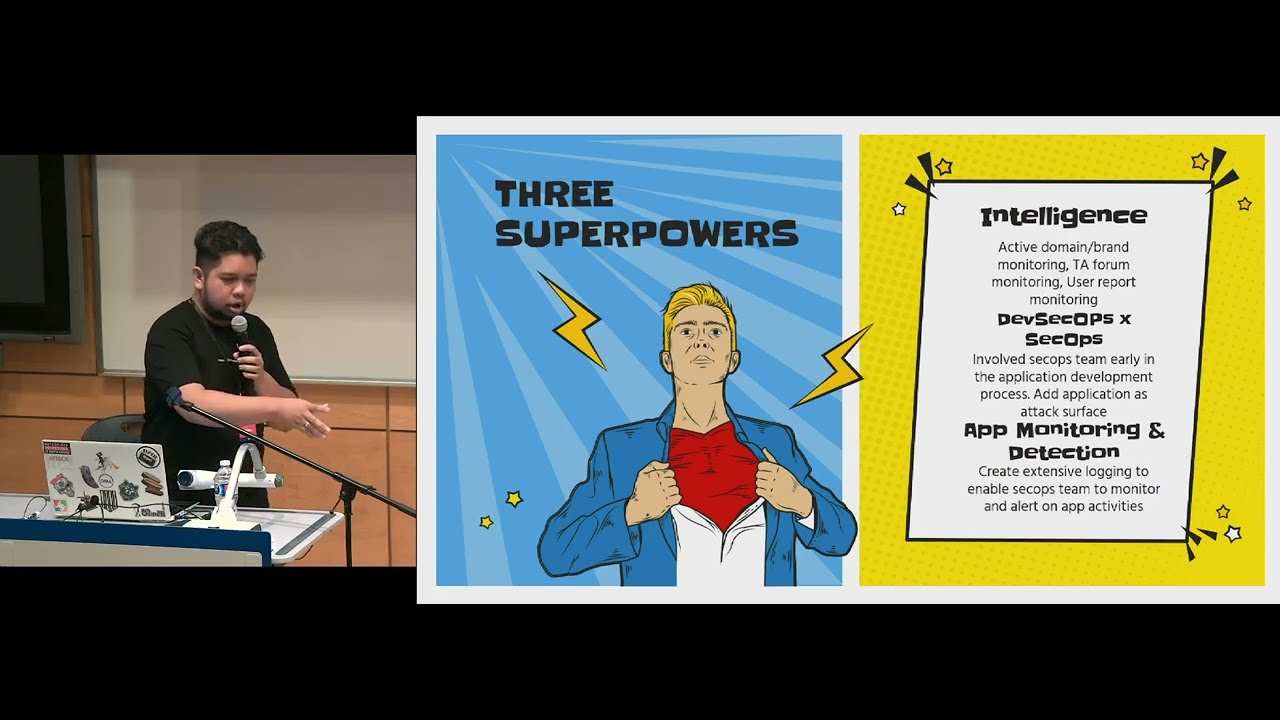
email email newsletter or maybe you you can Target certain user that are being targeted uh by sending like specific uh specific app notifications and then for the activity you can also check when user clicking uh you know like a chat URL from chat or like from messages so you can track if they're clicking some fishing links uh check user to user interaction and then check uh if suddenly inactive user becoming active it's questionable also uh another three superpowers that you can use uh yeah intelligence uh the reason why I found the connection between the booking.com and then with some other e-commerce platform because I use tool called URL scan doio uh so it it actually pretty good
because it connects the the the websites not because of the domain name it's more like the components of the website so the the JavaScript being used the CSS the HTML so it can it can connect everything so it's good to Cluster different uh you know like uh fishing page for examples you you have uh surfaces like uh domain or brand monitoring uh brand informations and such uh for for sure your TR people will definitely monitor the trctor Forum in the dark web uh and you you need to also act when user reporting something as fast as possible it it was not my experience with booking.com it takes them to reply to me like few months
after there there are news and so like yeah it take them some time so it's always good to to respond to your user as soon as possible and then again uh combining Dev secops and secops and then uh instead of just relying on protection and mitigation you have to enable application monitoring and detection because why because protection and you know like uh mitigation will always fail that's what I found you you see all the CVS you see all the other stuff the only reason they know about it either somebody told you about it or they they detected because they they see something suspicious it's not supposed to be there so I've worked on this framework with my
friends Wahu uh it's a detection oriented modeling framework in short Dum so it's combining a start modeling uh it's a little bit small but there I have a link later that you can see the white paper about it uh and then we combined with the detection engineering life cycle from the Megan Roi books it's a pretty popular uh detection engineering uh people uh so it's combining the step of uh a modeling so you're adding detection in in the middle of that and yeah so for example this is a for example you want to detect MFA byass so the threat is here is MFA bypass so how do you know when MFA is being bypassed usually you will see some
impossible travel from the user uh you might have unusual IP that not usually logging into your uh system you have unusual user agent in complete login chain so for MFA you have to log in you get prompted there's an MFA so that's the full chain if you check there is no full chain then it's a questionable uh thing that happened so and then you you ask yourself okay what do I need what is the capability I need to detect those so for example you need to collect data on the successful logins for example to to make sure the Lo uh the the chain is complete right if you don't know if the login success like how do you know when
they complete the MFA you need to you need the MFA operation again uh and you need aggregation platform because you are mixing different data together uh and then IP enrichment if you want to detect impossible travel you have IP you need to know if this IP in Russia or in Canada and lastly you need to collect historical data so you will need some big storage like 30 days or something how do you know something unusual unless you know something is usual right so you have to uh to collect the data and then detection components is pretty much like small tiny bits that I need to log when I build application I need to log for
example IP so I can enrich the IP so I know where's the IP logging in uh time stamp so I know if if this uh login is you know like uh last month or this month and then there are things like the login status MF status user agents username user ID Etc and then from there go to step D you you kind of look like and ask yourself is this worth our time or not is it worth our money uh so you see when when uh MFA bypass thread actor logged in when they successfully bypass the MFA they are technically inside for example uh on the booking.com when they logged into the admin panel they are the
admin so that's really bad that's already high like priority and then you're seeing a lot of like attacker in the middle platform such as EV engx 2 uh and some other platform so you know there the threats are out there people are exploiting it and then because of that you know that okay I will need to create this detection and then that's kind of like the idea for the framework uh this is just like some demo uh explanation that we we will feel it more and more and more so this is like my tery for web app abuse plus detection etc etc so yeah so we are we're looking for organization or people that want to
partner with us just to like apply the the framework in the organizations uh yeah so for example for the booking.com okay for the chat okay we need to lock the chat we need to lock the URL we need to maybe send the URL to like fire or something check the what's what's going on with the URL so those are the ideas and there are lot lot of functionalities uh from the web application that we can uh kind of draw like the attack Pat from so it is something that is not being seen not my attack not all us uh so yeah so that's pretty much the talk uh thank you so much uh yeah there's uh some thank you
for the people that have been helping me uh the slide that can be found on the barcode over there you can connect with me on the social media below thank you so much everyone
yeah do do
yeah I think I think those are part of the oaps I think it's probably like listed there as uh some mitigation part uh yeah those are things that you can definitely do uh but there are challenges you your product security so you know some challenges some for hotel for example they might need to uh for the user to upload certain documents passport Etc so it will be different between uh organizations and again uh yeah eventually the user sure you'll War warn them okay you're going out from the official websites to a fishing page or something like that but they will still click it right so that that's kind of that's kind of the idea of like why
detection is always important as the last layer of things but if you are able to do that it's something that you have to do fortunately yeah
yeah for sorry for the
yes yeah well what if they stole the token right so they can just replay the token I'm not sure how they work like how the the backend of things MFA will stop it for sure if if it's only like password uh stuff they might change it I'm not sure what happens with Windows uh days yes so yeah because for example when they're the info stealer also steal like tokens from web browsers and stuff like that so they might acquire the tokens
and yes yeah so yeah I'm not sure what happened here uh so the thing is
yeah yes so those are the things that they do good yeah so
okay it's good to know oh yeah so yeah so the uh the legy the Legacy Merchants uh in the booking.com are still Ed not enforced to use MFA uh the new Merchants are so there are a lot of uh good changes happening over there
yeah yeah
if so the question is like is it makes sense to instead of using external MFA surfaces to use the internal one or like kind of like yeah yeah okay
yeah yeah no well I first thing I'm not the right theme so I never asked that question so you'll probably be the the person that might be able to ask that question but I think I think if the sometimes it's it's difficult for the developer to create everything in house we are talking about different range of application booking.com maybe they they able to do it because they have like pretty extensive uh Team uh but for smaller firm it might not be reasonable but it's always good thing to ask maybe they can implement it yeah I I never had really experience to actually talk to developers yeah yeah okay great thank you so much Taz





