BrechinPiper
Show transcript [en]
[Music] deciding to come here besides Eric I know you have yeah okay you have I think we talked in the hall okay so anyone else feel like they're really good at uh identity management or access management things like that things that do identity no I think if you went to Eric's talk his point was like we're security people and we just kind of ignore identity that's someone else's problem Maybe should be our thing that's what I took away from it I don't know if that's what you wanted me to yeah uh so I'll say it's a new big asterisks around new uh concept because nothing in it is new uh RSA everyone's like oh public private keys are amazing
and new no they came out in 76 they're not new it's very old uh so we'll come back to that in a bit uh so about me uh I'm one of these dirty smelly people in this picture I was in the Army for 15 years uh I've been out for 359 days if my math is right uh so who's counting right um so that's how I ended up in you know the coveted last speaker spot on the last day is I'm the new kid on the Block as far as bside speakers go uh so some about me and biases uh and what is it like in the Army uh everything is harder when you're trying to do it while
camping uh seriously so a common task I'd have is like you know uh the commanding officer needs a mobile office to work out of like cool Breen you're the IT guy uh she needs some tents and some tables and some computers and I'm like Okay cool so computers needs internet we're in the middle of a field that's going to be hard uh we need power okay I need to go get a generator uh it would be cool if no one you know took the commander hostage so I security everything just gets harder then you hang out there for a bit you kill all the grass that you're working on and suddenly all the computers stop working
because they've eaten a lot of dust it's just everything's harder uh other fun things uh we're kind of like dogs we get the Zoomies like we go through frenetic periods of just working 36 hours straight and then we'll just pass out uh and be good for a little bit of time so we have weird deep conversations uh a lot of times making fun of the good idea Theory or big Concepts being like that'll never work it can never get applied uh that's probably why when I saw self- Sovereign identity as a Capstone or thesis project I went that sounds like a terrible idea I'm going to do it uh the other thing I want to talk
about is is just the users I'm used to supporting uh in the Army and I say this with the utmost affection uh most people in the Army are akin to cavemen when it comes to technology and I'll paint you this mental picture so I'll picture a bunch of dudes out in a field they look a lot like these guys uh if they're lucky they have a table uh I've just given them a laptop if they're not lucky they're probably balancing it on a rock so this guy's cold he's wet he's tired he's hungry uh the computer is acting up the application's not working uh Rock might meet computer computer at velocity uh if I can't fix it for him quickly uh
and they self admit they go we we don't really want it like if it doesn't work if it's not reliable if it's not usable it's wasting my time get rid of it uh not saying computers have been left behind vehicles and backed up over uh but I did have a bag full of random bits uh so that's kind of what I'm coming from as far as my bias of users uh if it doesn't work kind of like the Apple model like it just has to work okay so what's in the name uh first time I saw self- Sovereign identity I was given a list of Capstone things that professors wanted to supervise and I went what's that and I
did a quick Google and I went I hate this I'm very passionate about it I should probably do something with it uh the first thing I didn't like the name do anyone else like have an allergic reaction and they think like Sovereign citizens or freemen on the land like that guy who's going to rent your house and you're just never going to get rid of him it has nothing to do with that uh the name is unfortunate I think there could have been better names but this seems to be the market leading name uh you could say it's like tablets and iPads and things uh the first thing that I bought that was a tablet you would Now
call like a convertible or a slate um that was in 2007 uh so the name could change whole bunch of competitors up on the screen um people say like oh it should be trust over IP or multisource Identity decentralized or digital identity is also very popular um who knows what it's going to be called uh the other one military guy uh we talk about sovereignty a lot especially in the Arctic uh in my mind sovereignty is like the purview of nation states that's that's where sovereignty is so when he said oh we want people to be Sovereign over themselves whoa I don't like those words those word choices uh triggered me a little just based on my biases and
background okay so let's talk about some uh foundational knowledge some things we should all know just so we can talk about things uh using the same sheet of music and same terms uh so before I talk about the new sexy model for self- Sovereign identity what are the current ones so there's really three or four but I'm going to boil it down to two so I'm going to say the first one's The Silo model uh you're probably used to this I still run in The Silo model uh I don't use an identity provider for anything else so if you check my password manager I have like 100 accounts so I've got one for my Yahoo mail I've got multiple
Gmail accounts I've got a whole bunch uh for all the different services so everywhere I go I make an account and they steal a little bit of my information probably my date of birth so they can send me uh nice email saying hey here's a coupon or something on your birthday uh and they're not linked up in any way so that's kind of The Silo model we're all probably pretty used to silos uh the next one we'll call it the Federated model you'd also say there's a user Centric model and there's some other ones that are very similar uh it's really you've got someone who's gotten big like a Google a Facebook um some of the services I use
will actually let you use GitHub to log in it's funny right you can use an existing service that you trust to access a second one um I want to pause and think about that for a second of why a service like Google or Facebook or something would go through the extra work of letting you log into a third service using theirs so really they're becoming an identity provider so can anyone give me a motive of why they do that my friend their Core Business is advertising their Core Business is advertising yes oh I love it so based on what other servic I'm using they're collecting data on me they're getting my pattern of life so they can serve me better ads that's
like the perfect answer I've never met you before but I think I've seen you at some point I did not plant that answer that's that's exactly why um so these services that you're logging into at the very end they're going to end up with less information about you it'll be in the fine print about how much they get um some of the ones I looked at just said oh we get your uh email and access to your profile pictures about the less least amount some of them are
higher okay public key cryptography I'm sure everyone knows lots and lots about this basic things you know you have a public key a private key keep your private key private you can sign things you can encrypt things uh these are becoming more and more popular uh it seems like blockchain really popularize this and made people realize like this is a thing that we've been doing for quite a while https for instance uh the other thing that often goes with this is you'll have some sort of a wallet or an app or something where you hold these in uh and someone can send something to you it's really all we need to know about public key
cryptography uh blockchain just grab some basic uh images off the net I I always always look at this as kind of a decentralized data center so you got a bunch of guys uh and they're out there validating things uh and they're really running mirrored data centers and they're just getting it in very small bits and bites whenever they add a block to the the chain uh they're doing it via some sort of consensus mechanism whether it's proof of stake or proof of work uh or a Byzantine consensus Model A lot of times there's some rewards for validating cting some money to do transactions that's that's blockchain the big thing I want you to remember here for
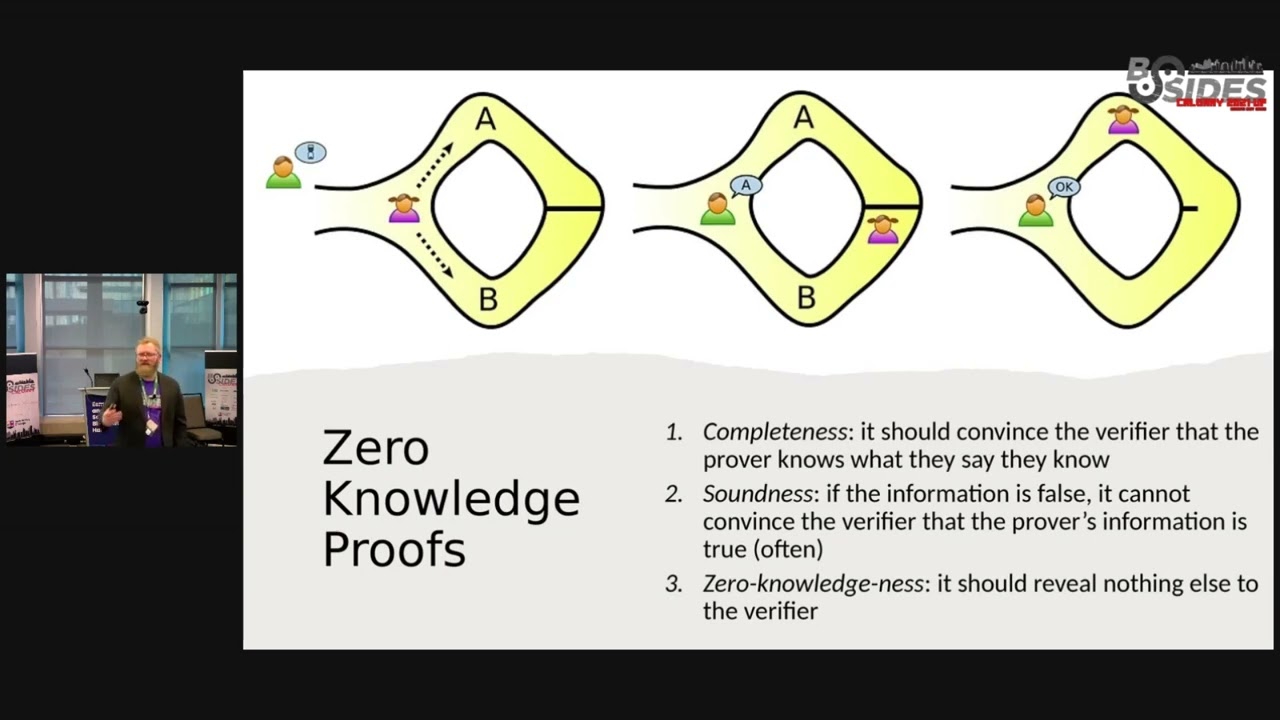
blockchain uh it's supposedly decentralized I'm putting air quotes around decentralized we'll come back to that in a bit uh but the other one it's it's immutable uh once it's on the chain it's spread out across all of these data centers people's laptops or uh big mining Farms in China or whatever it is uh it's very hard to change that information okay here's one that I'll spend a bit more time on just cuz people might not know this they might have heard zero knowledge proofs and you go okay well the name sounds like you're going to prove something to me and you're somehow not going to tell me what it is uh so the best example I found uh
is the one I've got up on screen here uh it's a very old example it's called alibaba's cave so you can probably guess how old it is based on that so here's the basic setup for alibaba's cave you've got a cave it's got a tunnel that loops around uh and in the middle of that tunnel there's a door or a wall or something uh and you need to know a secret word or a magic word to get through that so I'm going to say uh our wonderful little pigtailed person here that could be me I've had pigtails at some point uh is going to go into the cave uh and I want to prove that I know
the magic word but I really really don't want to tell Brody what it is because that would be the easiest way Brody the magic word is carrots oh now I know but now he knows um so no I don't want to tell him what it is so I'm going to go down into the cave and say Brody give me a minute I'm going go into the cave and then you yell at me which side of the cave you want me to come back out of you might say well the first time we do that I might have gone down path B and Brody yells B and I come back and I look like I know what's going on so the first time
you do it you're probably not going to prove that you know what the magic word was but if you do that a couple times maybe three maybe 20 maybe 200 uh when he keeps saying come down whatever side of the tunnel and I always come down the right one I will eventually prove to bro that I know the magic word because I'm somehow able to get through that wall that gate that uh whatever is in there so that's zero knowledge proof uh the other thing I want to say is it's not a mathematical proof um like a s plus b s equal c^2 um which can confuse some people I'll say the second principle here we've got soundness uh the more
times you check that proof the Sounder it will be if you only did it three times it might not be right if you do it 20 uh that's probably good if you do it 200 o now we're talking uh very unlikely that you're wrong at that point okay sound late some foundational stuff uh so let's talk about SSI and before I even get into that uh let's talk about the guy who popularized the term uh Christopher Allen has anyone heard Chris Allen's name before Eric anybody else no has anyone heard TLS yep probably all use TLS uh Christopher Allen's one of the co-authors for the TLs standard so if you go to the worldwide Web Consortium look up who
wrote The Standard that we all use uh Chris Allen and I think two other guys so he's probably legit he's got some street cred he's been around a while uh he's recently really gotten into blockchain uh then in 2016 he said you know we kind of have a problem like we we haven't really solved the identity problem for the internet because there's really no good way to solve it in his opinion so he said I'm going to uh write a little blog uh because he's one of those people that you know his blog is a trustworthy Source because he's cool enough uh so he came up with these 10 principles of the term I hate self-
Sovereign identity okay uh the first ones he talked about and if you check out his blog I really recommend it uh he's got a paragraph on each of these so I tried to boil it down as much as I can it's the first one he says existence um you can't just invent an identity for something it has to boil down to something so you could say I think therefore I am uh you could say it has to boil down to a human or a legal entity uh some people really don't like the idea of self- sovereign identity being given out to like an AI program for instance uh they're really looking for something that you're representing
digitally uh the other thing here in existence and this is an odd question to come from recently retired army dude big guy with a beard anyone here romance novels or romance fan no am I the only one okay uh a problem you might have if you find an author you like is you're like hey I really like this guy's books or this girl's books I want to read more of their stuff what if they have multiple pseudonyms and Pen names what if they have one per genre or one po uh one per publisher I have an author who writes under six different pen names and it's super annoying to find their books I'm like what did they call themselves
for this series yeah okay uh so maybe you want to have multiple identities uh so the concept we're trying to get out here is one person I can have multiple identities so I could write different pen names I could have one for my screen name if I'm an actor I could have uh multiple identities maybe one for my regular user one for my admin one for my super domain controller admin uh but it doesn't go the other way if there's an identity out there it should boil down to one person one entity one thing uh so if any rude and I decided hey we should make an identity well we should probably sort out like how do two
people share the same identity maybe we make a business then it's not just the two of us then it's uh any rud and Bre and Incorporated uh so that's existence control this makes sense we're talking about sovereignty kind of thinking autonomy uh whatever that thing is that that identity maps to should be in control of it uh access well if I control it I should be able to access it right I shouldn't have to uh jump through a bunch of flaming Hoops or rely on someone else for it uh transparency this is the basic you know don't rely on security through obscurity whatever black magic makes this whole system work it should be open you should be able to
find it on GitHub and inspect it and there should be a bunch of smarter people than I who have vouched that it's a good idea uh persistence well it doesn't help if I get a digital passport or a digital driver's license and my uh domain controller uh admin account and then it all just disappears that that wouldn't be great so we want it to be long lived uh but we also have to remember we've got gdpr and the right to be forgotten and I'm in control of it so I want it to be long list up until I don't want it anymore and then I should be able to somehow hide it or delete it uh might be a tall
Bill okay so the other uh six years we got portability if I've got it stored in a data center I should be able to pick it up and move it to a different data center if it's living on a blockchain or my phone phone's a great example uh maybe I'm not the best example because I've only ever had four smartphones in my life um I should be able to Port this to something else so if it's in an Alberta Data Center and I move to Ontario I should be able to take it with me if it's in my Samsung 20 newest thing I've ever owned and I get the 23 24 whatever the current model is I need a
way to Port that over I shouldn't be chained to something like that uh interoperability sounds similar right I should be able Port it uh interoperability is easier right uh if it's in data center a I should be able to show it to someone in data center B that's actually a lot easier to get it interoperable than it is to be able to pick up the underlying data set and move it uh and make it portable in my opinion uh consent so uh this gets interesting if I've got full control over my identity and you know I've got the sovereignty over it and I'm controlling it I should be able to consent to who's looking at it uh so this one gets into a
bit of kind of data sharing so if I'm using my identity to log into my email uh the information should stay with me and if I want to revoke consent for Google to know my date of birth or something there should be a mechanism for me to do that uh companies probably won't like this they'll go no I'm used to data harvesting and controlling all of your stuff uh that's that's quite what they're comfortable with that's the consent piece just like consent applied to anything else you can give it you can revoke it at any time uh minimalization so we're going to do lots of examples for this but really uh if I need to prove something to you like I'm
buying a house and the asking price is a quarter of a million dollars uh I should will approve to you that I have that much money without showing you my bank account and all my statements uh we're just trying to show that boil it down to kind of like a yes or a no uh kind of question uh then protection uh so this is one where I disagree with Christopher Allen uh he's much more famous than me so way on the side of him um he says the rights of the users should be protected as the primary thing even over getting a functioning network uh the reason
uh working of the network what if we can get some inal gains uh by sacrificing a little bit of this would we not still be doing uh good for Humanity if we can get it working and we have to you know give up a little bit of consent or control uh so that's the the big definition so Christopher Allen kind of coined the term uh as the first mover in the space self- Sovereign identity seems to have stuck around uh if you read his blog he really wasn't trying to say like this is the best model ever he said let's talk about this um and being a smart person and the first one to talk
about everyone said that's a great idea I love the name I love your tense principles it's locked in stone now uh there are a few people who have proposed other definitions most of them have uh a different name for it they'll call it decentralized Identity or trust over IP or something uh the favorite one I've come across uh doing a lot of research in the past year uh there's a security researcher named settle Meer he's got a bunch of friends uh they did a late review uh they wrote their findings they said you know what we should ask the tech community so they said here's what we think nine good rules would be or design
principles then they did 15 iterative interviews they selected five or six experts uh and they changed them a whole bunch the first seven really just boil down what Christopher Allen said uh the last two uh what they call Design principle eight and nine uh are something I think we were missing so they say reliability and usability are very important uh cuz I know you guys are all pretty technical uh maybe you feel comfortable being the sole person in control of your identity I'm not sure I do uh I've only had an Alberta Health Card for like 9 months and I already lost it once so maybe I should not be the only person maybe there should be a
help desk uh or some AI or some guard rails to help me out especially when we talk about uh some of the things that are going to come up uh if you're asking me to trust things so if I'm hiring someone out of the crowd here you say oh I've got a degree from Bo Valley College how do I verify that I would really like some guidelines and something in an app or a website or something to make that easy on me uh same thing kind of usability like if I if it's not user friendly uh my caveman users will not use it or they will smash it okay so let's uh let's model this
let's talk about some actors if you haven't figured out I kind of like Thor or Chris hamsworth depending on uh what you want to call him um
so see this we got Bo River College I don't know if they issue medical degrees but in this scenario they will uh they're going to give a medical degree uh to the handsome man in the center he's going to apply to work at a hospital and they're going to say hey you want to be a doctor do you have a degree he say yes I have a degree it's issued by Bo River College we've probably used some public key cryptography they've signed it it's almost looking like a certificate now uh here it is he's going to send them something to satisfy saying I got proof uh they might say yeah I'm going to double check that they might reach
out to B River College see is this thing still valid is this actually your signature uh so that's kind of the basic basic model we're really just looking at someone the holder the user you uh being in control of your things uh and being able to show them you could replace any of these with almost anything so uh is pant still in the crowd no okay uh who do I know is a teacher nobody else let's say I want to write uh a review of a restaurant I could say I'm going to write a review of a restaurant I uh ate at a Don airpl last night and they hyped it up and said it's going to
be spicy it was not I don't know if they assumed that I was white and the level of spice they put in was it going to be enough uh it was not I was disappointed so instead of going on Google I could send them uh a review it could sit in their wallet uh and if they wanted to show it off they could uh you could do this with almost anything you could do it with grades you could do it with your insurance anything you can think of that we do right now you could do it with a driver's license passport almost anything you could convert digitally right you might be thinking well this doesn't really seem
like a super good Improvement like is this actually better uh it it could be depends how it's done the big thing here uh kind of comes down to how does this get verified right uh so if I was going to hire someone out of the crowd and you said yeah I've got three degrees and a cissp and a this and of that uh in kind of the current model I know how to verify those things I can call up ISC square and say hey strey number this is this guy still valid he paid his dues uh things like that right if you presented that to me in some sort of self- sovereign identity model as a
verifiable claim clim is what we call it you can think of it just like a certificate um how do I do that right so that kind of comes back to what settle all said usability and reliability uh kind of giving me those guard rails to help make this system work uh so I can actually have comfort in it is hugely important uh some of you might say this looks a lot like just you know a server getting a certificate from a certificate Authority it is like I said this is not a New Concept uh really what's new here I w't say new cuz uh pretty good privacy and the web of trust tried this uh just
didn't catch on maybe it wasn't usable enough I don't know why uh really we're just empowering everyone to hold and store and issue certificates uh replace certificate with verifiable claim or verifiable credential in The self- Sovereign identity speak and you've got the core idea uh you can link in a bunch of other things you can say oh we need some storage uh maybe there should be a revocation list you can complicate this as much as you want but this is really the core thing uh and like I said one of the other big things we want to talk about is if I can issue a claim about someone else should you trust me I don't
know depends how is the system built out are there ways to verify that I'm a good dude and I Trust a Dude okay so let's talk about some practical examples and kind of how we can minimize data a bit uh this is an actual driver's license that someone used to try to get a uh job at a weed dispensary I think found it online I did not make this uh it is punny uh the other thing I'll point out is if you do the height conversion from centimeters to feet it also ends in a humorous number that starts with six so if I want to go buy weed smokes some liquor any of those things uh what's the
common thing they're going to ask well maybe not me because I've had a beard like this since I was 16 but uh someone who looks a little younger than me how old are you how do you prove that right you pull out your ID so how much stuff is up there on the ID too much too much that is the exact right answer so we had all these things and what are they really trying to prove can someone boil this down a bit more for me birthday I like that uh I heard a name I don't really care about a name oh age yes yes I like it all right I like this we've gone on like
three iterations so we have birthday age now we've gone down to just over under over under what
com oh I like this this is even better okay so I think we were getting it kind of like are you over or under the age of majority right so we can boil that down and then we say well who is it I I would like a picture I would like some proof that you are you the person presenting this is the person that this claim maps to when I talked about existence so that's great so really we could block out everything on this driver's license other than date of birth and a picture and we'd be fine I should be able to legally buy whatever my age restricted item was so let's look at how that could work
in SSI so let's assume we've got some magical app it controls everything on my phone we won't worry about the black magic that supports it uh maybe there's a QR code maybe QR code's a bad example because apparently I mystical Tech demo there's there's going to be some sort of a prompt saying prove your age uh or approve a question and you're going to get some little buttons there might be like some sliders you say oh what do I need to send maybe just a picture and a date of birth would be good that would be an improvement over what we have now but like we said we can get better we can boil this down further
turn remember the next slide okay so we can boil this down further so if we go back to zero knowledge proofs for a minute really we we said we just want to get to the age of majority are you over under you don't need to know when I was born you don't need to know if I'm 30 or if I'm 60 you just need to know if I'm over 18 yes no you almost think of it like a function en coding right function expected output yes no binary is this really with the Zer knowledge proof comes in right you can say oh I've got this I got a bunch of claims they're all hoarded in my wallet uh they're all safe
and I'm going to somehow do some zero knowledge proof stuff on it and out is going to come a yes or a no that's really what we're getting at to further minimization of your data and that's going to protect you right you're not oversharing information all the time makes it harder to steal your identity uh makes all the identity nerds and privacy maximalists the happiest they can be
right okay so I know I said I had I had WR blockchain in here just cuz I wasn't sure they'd pick me up as a speaker otherwise uh so one of the things that I saw uh and this will come back to what I'm doing for a Capstone uh so they had a sign up board on the wall and uh one of my professors said SSI plus metaverse plus Healthcare that was about all the information he gave so I had to Google what some of those words were cuz I'm like I know what Healthcare is and that was about the extent of my knowledge I said self- Sovereign identity like you want to let people be in charge of their own
Healthcare and then you want to put it in the metaverse like you're insane I need to be there to shoot down all of your ideas uh so that's how I ended up getting slightly educated about this uh and and my first big thought was like oh I really don't like self- Sovereign identity on its own I oh I really don't like adding blockchain to it why do we need to do that why can't it be in a data center uh and I've really come up with no good reason why but lots of people have websites saying you know you need blockchain to make this work I vly disagree with them I think they are wrong uh cuz I can go to
TD Bank and I can get a certificate from them the https and it works and there's no blockchain involved so why can't I do the same thing the question you might ask is well TD owns a data center I yeah okay I do too it's much smaller and 14 terabytes and has no redundancy because one of my drives just died um but the average user probably doesn't right so it's got to be stored somewhere so people are saying well why why can't that somewhere be the blockchain uh yeah bro non-repudiation yes or immutability uh so if I put some information out there and it's on the blockchain supposedly it's there forever or until people stop validating the
chain uh so that breaks your right to be forgotten right suddenly I'm not legally compliant with Europe uh that would be one good reason why you shouldn't do this in the blockchain maybe there's a smart way you can somehow delete that information but you really can't CU that breaks the principle of blockchain chain it's not meant to be deleted right the whole point is you hash information in Block one and that goes into block two and block three hashes block two and four hashes three so you can't change block four if you're on block six like it's too late it's done the information's out there maybe you could hide it or mask it some way but
blockchain storage is not a good idea I can't wrap my head around why you would do that I could wrap my head around saying this is just the identity and nothing is actually stored there it's just my public private key pair and it's an address and everything is stored offchain somewhere else and I go okay well now you still need offchain storage what you're just making this harder then people say oh the offchain storage can be interplanetary file system and I go I don't even know what that is why why are we roping in so many things that I've never heard of before into what could be a simple idea uh so really adding blockchain it's
it's adding complexity I don't know if it's actually solving anything uh for a lot of people and maybe I have a a western bias but uh I I pay taxes I feel like I get some good services from it some of them being data centers uh where information is stored you know I have information in a registry I have a little bit of information in Alberta Health I have a lot of information in other provinces around the country why don't we just make this a government problem they're talking about making digital IDs right maybe the digital driver's license and passport should be able to be used for more things may we can just expand this and
use our tax dollars uh that works for me Breen and you know privileged place I want the genetic l is was born here in Canada uh maybe that doesn't work so much if you're in uh a country that's struggling I can say uh my partner is a high school teacher she specializes in English as an additional language and Refugee mental health can anyone guess what the most common birthday in her class is January 1st I heard multiple people say it why it's easy to register yes if you're in a refugee camp and they sayh were you born and you say I don't know are you Whiffle and Waffle they just write down January 1st so in her class of 30 she's
had up to 20 kids January 1st is their birthday how much do you trust that well well I don't know how much do you trust their age even I don't know some of those kids have beards better than mine uh
yeah resettled or what very true yeah and that's um that's a tough problem uh I'm not an expert in it I I don't have the solution but I will make the problem even more complex so they're getting a digital ID from someone like the Red Cross or medicine on Frontiers Doctors Without Borders those of you who don't have French um great how how did those people decide that that was their birthday well they're using something from their home country maybe if they were lucky enough to have it do you even trust the documents from their home country uh there are countries and uh students that I've met who go yeah uh I'm here you know two sons and a dad uh where's your
mom and sisters well they're property of the state because the country they came from says as soon as you leave all property becomes the state and in those countries women are property and they go oh okay that's messy that's not great uh so how do you deal with stuff like that right like we're coming down to a hudia trust issue and then we're trying to make it digital so we're just in complexity on complexity here and that gets Hur uh so honestly does it need blockchain uh hopefully I've convinced you no could blockchain be useful yes it could have some limited uses um but just like AI it's not the Silver Bullet for anything someone still
needs to code it uh there's lots of issues around that right the other thing I want to talk about uh so I promised I'd dunk on blockchain being decentralized yeah go
ahead
y by a political argument uh and in this case I'm wondering how much of what he wrote is from a uh for lack of better way to put in Tech libertarian uh it's funny you came to the same conclusion in like the 30 minutes I've been talking uh I've never met Christopher Allen I don't know how he votes but if I was to guess I would vote libertarian and that's just from reading a couple papers of his I could be totally wrong um and I think probably a lot of people who go to uh internet identity Workshop probably feel the same way and that's a very valid criticisms a lot of people say blockchain will save
us from government overreach and I go maybe vote for Less shitty governments and you won't we worried about government overage right um is technology the answer to poor political systems probably not yeah uh it's very valid criticism uh and I came to the kind of the same conclusion of uh the reason he was uh he and many other people who like self- Sovereign identity want it to be on the blockchain is they're they're latching on to that decentralization and no Central party um than you exactly yep
yeah true yeah yeah it's very much an American thing
yeah there you go yeah yes yep I think that's fair and if you know him uh slightly better either way you're good all chrises are interchangeable right they're uh fungible tokens uh getting back to blockchain for a second oh Brody go
ahead
ver I think I'm not say age
yeah yeah and this is I'm GNA segue on this for a second just because I did it last night uh because I was curious about it and I don't think I'm a huge Target for identity theft uh made a post on LinkedIn because that's the thing people told me I should do when I go to the Army you should get LinkedIn it'll help you network so far it seems to be working uh and it said oh you'll get 60% more profile views if you verify your profile and I went okay cool what do I have to do to verify what flaming Hoops do I have to jump through to make this happen and they said oh based on your
profile you can verify two ways you can give us your uh student email because you're claiming to be a student at a university Concordia in Edmonton by the way uh and we'll send you an email six-digit onetime code and punch it in punched in my email and said that it doesn't look like a valid email we don't believe you and I'm like oh good chose a school with uh so much street cred that people don't even know it exists excellent uh then they said oh or you can take a picture of yourself do a selfie and take a picture of your driver's license and we'll verify you that way and I went oh that's interesting uh and I did it cuz I'm
curious you I work it worked for me uh probably because I looked very unhoused when I got my uh driver's license picture like I grew my beard out as much as I thought I reasonably could before my wife uh took a razor to me and probably nicked something in the process uh so I look a lot like my driver's license very very hairy very out of control um maybe it was lighting I don't know worked first time uh took a selfie took a picture of my driver's license scan the barcode on the back so probably tomorrow I'll have seven new credit cards um now maybe I have 60% more profile interaction or whatever LinkedIn was promising but yeah
like verifying it well I don't if I really trust this let's see where it goes so next year if someone else shows up here pretending to be Brack and Piper uh it didn't work well okay I think we've beat blockchain oh sorry I did have one thing anyone speculate on cryptocurrencies I say speculating gambling because it really shouldn't be called investment no no one wants to admit to it we're down okay I'm still green somehow but I think it's just because I'm uh I have a very high risk tolerance uh anyone familiar with uh Tera Doan no so there was a cryptocurrency he said oh it's decentralized and everyone brought in oh it's decentralized uh well
something went wrong there's a bug in the code someone drained all the money out of it uh and somehow Doan had a stop button he was able to stop the blockchain so I go is it really decentralized I don't know now Doan has arrest warrants in multiple countries the coin is worthless and I go doesn't sound very decentralized something went wrong one guy had the stop button and now it's it's basically dead okay go
ahead yep
sure
totally
yep matter so I I'll throw out some possible solutions because I don't know the the one answer that fits all um so some possible solutions like I said you can make multiple identities so if I wanted to be called Brianna tomorrow I could just make a new identity get
new I'll keep my same wallet address or whatever it is that that lets me hold everything just give me a new driver's license why can't I have two claims uh revoke my other one uh so there's multiple ways around it you can you can issue extra claims or credentials uh you can make a new address um yeah exactly yeah so there's there's ways around it uh I don't know if any of them are like super clean as they should be uh but I you know I I can see at least two workable ones anyway so I'm done dunking on blockchain I don't think it's decentralized as much as everyone says it is go ahead
oh
yep now the Security Professionals can't be bothered to go out and spend like I don't it's like 75 bucks or something like that to get a certificate that supposedly shows who they are what I wonder is is there anybody out there actually cares to go through whatever this be blockchain or centralized database since evidence would show they don't actually care to have an identity that is very insightful I love it it's Terry right um so great question here so I said this isn't a New Concept like pgp web of trust has been able to do that there's better arguably more secure emails than Gmail anyone have proton mail no okay oh I saw one all right
anyone here gone in and made a pgp account and done web of trust stuff and started issuing claims did were you doing it seriously or was it just like a a curious thing yeah yes who actually care yeah yeah
yeah if it's uh user hostile instead of user friendly are people going to use it it's not going to catch on right uh so do people actually want this I don't know man that's a good question uh based on you know pgp web a trust really hasn't taken off well maybe the reason it hasn't taken off is because it was painful to use uh I don't know true yeah yeah uh okay uh potential issues and I don't want to be accused of age discrimination this is just a stock photo uh and these are two of the people that came up uh when I first said oh we're going to put people in charge of their own identities
uh so if I live long enough I'll probably have Alzheimer's uh just based on watching uh older folks in my family get it at at that point I probably shouldn't be in control of my identity um it's an unfortunate fact uh so we're kind of assuming that everyone's a rational actor and I'm going to argue that there are many irrational actors uh if you've got a mental condition if you're ill if you're in a coma uh if you are having a mental crisis you could have issues anyone have kids in the room yep who's got kids under I'm going to say 16
cool yeah you've got them right uh so if you've got a four-year-old kid or even a 16-year-old kid uh should they have control of their identity I I don't know could you make it user friendly enough well I don't know are they a rational actor who should be allowed to exercise that control again I don't know uh so those are those are two people I go well I don't yeah uh those are some kind of big concerns there uh the other one depending on where you put your self- Sovereign identity uh if you put it in the blockchain uh has anyone lost money on the blockchain I had some Bitcoin in 2009 and my hard drive died
cuz I'm in the Army and it got hot and Dusty uh and I still kicked myself I don't know what it was 4 10 I just got it out of the Bitcoin faucet I hit something and totally forgot about it and then it became I'm like I had some of that I could be theoretically but there's no help desk there's no forgot password there's no way to restore it uh there's no 1800 help me like I had to do the embarrassing thing where I called in and said hey I lost my health card can I a new one they said what's your health card number I'm like well if I knew that I wouldn't need a health card oh go to
the registry so you can prove who you are like oh okay you don't trust me over the phone at least this is good um so for to decentralize it I really want some good guard rails and some good control over how do I restore that uh do you Shard the key do you spread it out to friends do you have password recovery do you put in a back door something like that but at that point are you compromising decentralization and security proper uh so depending on Whose definition you like Christopher Allen would say no don't do that don't worry about it being user hostile we need to protect the user over the network other people would say
no usability we need usability uh so it's just just a thought to chew on uh but then you know if we do put it in a centralized data center I I have friends who work uh for the provincial government in it at the data center in Edmonton I more or less trust them I'm not too worried about them going in and changing stuff uh other countries I've been to I would not trust the local employees so uh no winning either way I'm going to check my notes and make sure there wasn't anything super cool that I read down for myself dunked on blockchain yes rational actors yes yes okay uh last thing I'll say if I haven't
pointed out enough I don't think I'm an expert in this uh I think I've just done more reading than probably people in the room uh mostly because I need to to get a degree uh so I don't have Q&A because I don't know if I have answers but I will say uh in the next 10 minutes or until someone kicks us out feel free to engage in discussion uh the other thing is if you want to hit me up on LinkedIn my name's very unique if you can find someone else with the name good luck uh but you can get confused with the Breen City pipe and in Scotland all right uh thank you guys uh thank you Brody thank you Croc
for making all this work uh and feel free to hit me with questions I'm going to start dismantling stuff uh but I can multitask mostly sometimes please uh so I'll I'm on the fence right now I would like one but I do not want the responsibility of being in charge of it myself I want some guard rails and I want a help desk I want someone smarter than me who can reset it uh so for part of My Capstone the kind of final thing I have to do to graduate uh I'm putting this on the blockchain just to prove how bad of an idea is uh I'm going to make some healthcare fake information uh
we're going to make some actors and we're going to see how horribly off the rails it goes so maybe in a year if I can get this published you can say h it sounds like a terrible idea or oh Breen's finally sold me on it uh if I can convince myself I would say it's probably good but I don't think I'm there questions comments discussion yes I am yes yeah I'm about halfway
through
yep
yes yep
yep themselves couldn't geter true yeah yep yeah I think I think we can summ it up in like in two ways so there are uh countries states places in the world where um citizenship and the like the right to exist and be recognized by the government is closely controlled and not extended to everyone it kind of sucks uh there are other countries uh that have given uh extensive training to people getting ready to go there where you can't even trust the internet say hey no a Canadian device into theater you're all going to go buy burner phones in theater you're all going to get there and the first thing you're going to do is order a travel router using that
burner phone and then you're never going to use that burner phone without the travel router again because you can't even trust the network right um so if we're trying to combine this and say oh there's you know it won't work everywhere uh and some of that is honestly outside of tax ability to control like I I can't fix humans who have Prejudice and bigotry and failed States as much as I wish I could uh it's just I don't I don't think we'll get there anytime in the near future go
ahead
yep yep
yeah depends do people follow the rules uh I know there are companies in Europe that catch fines because they don't exercise the right to be forgotten in a timely fashion or at all uh it's just an open-ended discussion Point Eric I know you're going to have something
smart
yep true
yeah yes yeah anyone who's going to like give out a claim or credential they're probably going to have a whole bunch of dirt on you right uh and they're probably not going to put it all into claim in credential and uh encrypt it up and fired off into space they they probably want somebody to back it up
right
yep yes
yeping something like this to be violates the very princip of the idea yes that that is why not just should not but must not put it on the Block Chain yep yeah I agree um I would say if if the intent is like everything's going to exist on the blockchain uh I don't see how you can do that without breaking a bunch of the principles that we want to adhere to right uh I could maybe see in a hybrid thing where you say like it's just the wallet with your key and then it's stored somewhere else but then we get into added complexity and where is that someone else stored um then you could delete the thing because really you just
use the blockchain like uh I'm going to date myself and say C uh the blockchain is just a bunch of pointers to storage somewhere else and that way you could delete the thing you can get around a mutability and you just have a broken pointer I kind of yeah yeah maybe yeah I my other thing about nfts is oh it's a picture on the blockchain no it's not it's a pointer to a picture somewhere and the picture is probably not on the blockchain yeah uh if there's more please please keep going but like I said I'm going to start unplugging stuff uh
oh
totally
yeah yep yeah and that was um that was one of the things we were concerned about in the Army when I was uh signals officer like we had lots of issue devices so I gave people laptops I gave them phones I gave them blackberries I gave them all sorts of toys uh that I can't talk about and I go yeah where is it going like I don't worry about it I'm like no no no I need to know and I need to worry about it because if it went somewhere sketchy it needs to come back to me first and I need to sanitize it uh or it needs to get shredded or all sorts of security
things um yeah the world is a weird place and uh I think sometimes we lose sight of that how spoiled we are and how much trust we can place in institutions and isps and things just kind of work well uh mostly in the western world most of the time uh when you travel to other places you realize we're we're pretty spoiled [Music] yeah





