AppSec On A Shoe String by Sean Wright

Show transcript [en]
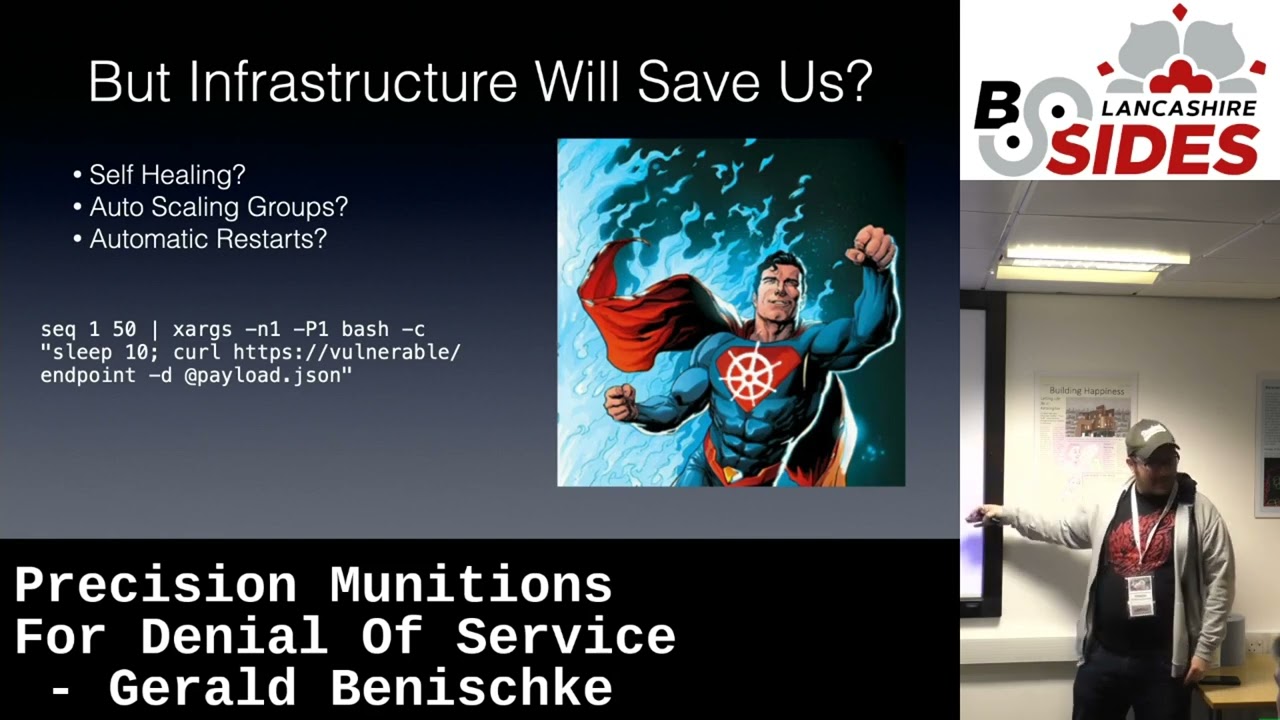
thank you well thanks for coming on um where I thought of this talk is it's often difficult starting up uh application security kind of program especially now with a lot of budget constraints um I think many of us can agree that if you're going to ask your um heads of and finance department many emails we've met with uh it's kind of a a difficult conversation so the point of this talk is is Iran there's a lot of things out there now that you can use for your application security to secure any applications whether it be things that you can get from third parties or your own internal develop web applications or sorry applications uh be a mobile or web um so yeah let's put this together as a relatively short work um so just a little bit about myself um I love doing stuff in the community so I studying things like b-sides I do some streaming on that on Twitter and YouTube I haven't done about as much as I've had to none this year so far but I hope I'll get back into that I'm not sharing that ideas and working with folks so active on the likes of Twitter and that and hopefully get more projects going into um so enough about me so when we look at application security there's kind of the different areas of tuning that I could see that you can have so you have things like that modeling this will be more at your beginning design phase um so things that can help you create a plan for security within your web applications or even existing applications um whether and um yeah important Security in in those uh then your SAS your your application security test and tuning so these will be scanning your source code trying to look for common fours in the source code um a big one for me and I think this is becoming more and more prevalent and important is your software composition analysis so your SCA tools so here supply chain being a big thing at the moment and that's kind of where that comes into I've done several talks in purchase vulnerabilities and threats around that and I really think it's a big area that needs a lot of focus something that's very very difficult to do but thankfully there are tools that can help with that um then if you look at after the last cycle it's kind of moves from the left to the right so your data is kind of getting more towards the right before you releasing things into production so your Dynamic application security testing kind of like an automated hand testing um this will actually do security tests against the running version of your application so typically a web application or an API and then some other things that you'll need is uh training so training run primarily your developers your QA folk but not just them it could be um your product managers and that kind of other areas you may need um and then finally vulnerability management this is a really important one this is useful for tracking all the vulnerabilities that come out of these tools and then what do you do with those um well my team great to solve everything that's just not going to happen so you need some tool to help manage that so as I mentioned at the beginning one of the challenges we're facing at the moment is budgets um I love talking budgets because it's always a often a a difficult conversation to have um a lot of the tools I'm going to mention you are going to hopefully make that conversation a lot easier they're not completely free the reason being is you're gonna have to have some money for running these tools but the tools themselves are free and that guy is going to be a lot easier to have the conversation especially if your organization has like virtualization attorney that makes it a lot easier um yes so you might have some friction because some of the stuff still requires competing resources in the cloud some of them are too small um so there is costs associated with that it's only a lot less than if you're trying to go off and get a full-blown commercial solution and just just quickly before I begin that um commercial Solutions do have a very valuable um position this is not saying you should replace all your commercial tools with this um it's it's about picking and choosing the ones that are going to work best for you so you might find that some of these like you SAS you might go with commercial but your sea for example or your dad you might choose a clear version It's all about trying to make the budgets work for you and the tour didn't work for you that's what so throughout mining this happens at the beginning the design phase um so this is where you want to try and identify all your bonding but it's still your threat actors where the weaknesses could be in your application that kind of thing so that's great one of the things you need to do is diagram and document this because this is where you're going to develop ment so there are tools out there so um threat Dragon really good one so this allows you to diagram your threat models using the thread modeling diagram tab all right systematics I think right um but basically there's different sort of specific diagrams Taps for each of the threats systems boundaries and that type of thing um the cheat sheets are also a really good resource you give a lot of information in there for your threat money nozzle also have a tool freely available that you can download that allows you to diagram and that will have really useful information on their site an interesting take is a tool called fragile um let's play on with thread threads and it adds well so hence the name treasure um it actually doesn't really take a diagramming but it does look like a more programmatic configuration type view it is a really interesting way this is something that probably get you developers more interested in because it's more like developing rather than trying to do a bunch of diagrams and documentation um it kind of like a wizard based so it is a pretty unique and interesting approach I quite like it the only downside to it is it looks pretty stale at the moment so in terms of developments but it is certainly worth having a Lookouts so the next if you move along the last cycle is your SAS so your scan your source code this is important because you want to make sure that any code that is developed before it's moving along the life cycle is free from common flaws and defects so there's a bunch of things out there um one of them is the spawn sick bikes uh this is now a OS Project um and this is uh for scaling vulnerabilities in Java code um you've got things like Bandit for scanning python code same graph is a really interesting one um so in the past the way these tools works is they'll look for common kind of weaknesses in the flow of uh code or code syntax Sam grapp is of the name suggest correct so you have these signatures bad known bad code that you would then look for so for example one common thing that you could use this for is checking if certificate validation is disabled if you know the syntax or the code that's used to do that you can use something like Sam grab writer Rule and I'll check through the code and then identify where that is so it is pretty powerful because you can now write your own signatures essentially and check your code for things that you want to identify and lawyers um bad force in your code um so yeah uh SCA also kind of uh moving along part of the development phase so this is something as I mentioned really important for supply chain um supply chain stuff is a bit of a disaster at the moment in my opinion because it's just a mess uh I pulled my house numerous times trying to figure out uh vulnerabilities details of vulnerabilities unfortunately it is where it is but it is getting better and tools like this would really hope so things like um dependency track this is really important because I see a lot of people go oh you need s-bombs and that yes so s-sponsor software available materials but basically tile all the components that make up a specific software great but you can't have them individually all over the place so if for example iPhone log4j for example everyone wins or aware where we use and look for Jay uh what pieces of code are using Oxfordshire at 9 noon um you could have had s blind but you still have to go through 10 20 50 whereas at all something like dependency track correlates that all into one tool so what that means you can go check this tool and then put in the log4j version all right these projects are using it off you go and you can fix it I also Tarzan with the vulnerability databases such as nvd GitHub um so you can get information in the tool relating to the actual packages that you're using and that uses something called Cyclone DX which is basically a format for generating s volumes there's another tool this is more for container-based scanning or grab um there is some other tool called group uh Trevi the graph is a lot better because it pulls in um from different vulnerability databases and this is really important because you've got other databases such as GitHub that can add a lot of contextual information rather than just relying on something like nvd so it's really helpful when you're trying to determine a specific package and the vulnerability worker and I try to see what it actually means uh and so again moving on um so the dust is as I mentioned you're kind of automated pan testing scanning um so there are several out there that's nectar um this is kind of a command line tool so that would be great for just quick and easy scans um zap is a pretty good tool um you can set up as a dash but it's also uh what's called a a man in the middle proxy um so you can use it to intercept requests and responses and as used as a fantastic tool but it does have the scanning capability you can board it into your part all part lines as well and then lastly at the bottom there this is quite new it's uh of course we get a dastardly it's a very lightweight Docker antenna again intended to do very lightweight scans it's from the focus Retreat and this again does a very lightweight scan on your web application so it's a very good way to find halibur hanging fruit so to speak training this is an important one um it's all very well saying you have all these tools but in my opinion training awareness is probably one of the most powerful tools out there this will enable different people so from your QA to your engineers to developers even as I said people like product managers this will give them the awareness and hopefully the knowledge to prevent issues in the first place so there's some really great things out there I've already mentioned cheat sheets there's not just threat money but it covers things from across that scripty to Essence Style or that there's a whole wealth of information there uh web Security Academy Again by Quartz figure really really good stuff um they cover things from crosshatch scripting to SQL injection and it's all Hands-On so you can actually see those vulnerabilities in real time play with them and their father fixes actually at the bottom is always that's a vulnerable web application again play with it see the vulnerability and see how they're working them in a real functioning application um and then quickly going on to vulnerability management as I said tie everything together so defects I enjoy all this project I would often got a quote um for a tour the the lowest level who wants to guess how much the quoted us 50K 50K yeah um so yeah there was uh it wasn't gonna happen so The Defector is it's got its quotes but it it still functional and works really well it has loads of Integrations and then something like Apache supersets you can do all the reporting from that right it does have some reporting in there but having something like superset will allow you to just expand that further and then lastly turn it all together you have something like Jenkins and use Docker Docker is a game changer in this world you can just throw all these tools and docket images have them and and Jenkins and that also means you can give it to so this is how you could tie it together um take all these tools put into your cscd doc uh Jenkins you can you could use Jenkins more traditional practice set up boards or you could use something called Jenkins pipelines which are luck that's kind of a mobile Dev devops way or devsec office way I'm approaching it where you can start writing code to call these scans bought them and then as I mentioned you can even containerize them with Jenkins so it's it when you run these scans you know it's going to have this the same kind of environment each time around the scan um and then putting that all into your defect loader so you get the results in one place and this is where your vulnerability management comes in a few other results to sign them or that kind of thing and that can integrate with things like jira through your boat tracking Apache superset you're reporting this one I want to mention um this is a really really really really cool tool again signature tap based uh I've actually found several things using this tool that haven't been found with commercial tools um so it is yeah it is pretty interesting how some of these open source view things find things at others and this comes to my next point is do I just rely on one tool if you can it's also useful not all the way all the time but it is useful having a kind of overlap of tools because this tool will find some things another tool may find some things so yeah um so yeah questions cool [Applause]