Intrusion Response And Detection By Knowing What You Don't Know
Show original YouTube description
Show transcript [en]
good academic hopefully goodbye to eat and will keep me from napping through through the sides from the post-launch coma my name is John SVG that were four alert logic and I heard the threat intelligence group and her here on stage Chris Thompson yeah Chris come to him the principal researcher on John's intelligence team so we're gonna talk about today is kind of lessons we've learned actually how to do it not to do so just a tiny bit about myself working for logic and its acquired a company or your ish prior to that the threat intelligence ever various groups that had the world cyber defense in the names at Microsoft for a few years consulting background Symantec at stake a TMZ and
so on and so forth and over the course of that especially the insulting roles had a great opportunity to see a wide variety of organizations and the types of attacks that that sort of word of demikhov's to have a changed per industry and I wanted to see a lot of that information is what led us to to to work on this and when I came to Microsoft working with this guy is so we so I was with mitre corporation doing research in the security world for a long time after that I actually went to the Microsoft where folks don't count intelligence 130 movie network security asset and threat analysis that's where I work John where
we were focused on believe the term was high-value assets and determine human adversaries we're not going to say every time you say apt have to give committee a nickel so determine humanity we worked on that for a while I accidentally the force of over work on anti-frog with Xbox controller unless you ask for excuse me and then I turn alert logic I wouldn't never take you to the US Senate need to be a security up until about about you and Ellen whatever all my stuff's over the shared history and we thought would be a good topic to share the variety of different experiences we had that converged on so good methods for smoothing out detection coverage had it
actually see complete attacks I do not over spend money among controls that are already functioning and so on so we figured that you know basically this also falls out into a discussion on blind spots figuring out what it is that you can't see by looking at some typical attack patterns and being a little bit structured in I think so today is short agenda basically an example of one ounce or radiant in some cases we're talking generally about more interesting advanced more things that are not really will characterize if we're talking about someone malware advanced things are very well characterized stuff that almost falls into an IT hygiene sort of category we're not talking my things are a little interested in
something else as an analyst you have to have the floaty hyper outfit and we'll talk a bit about whatever shares do you find some interesting like that we'll talk about the detection patterns and you know a couple of methods this is one way that we found pretty effective for driving out where your detection wine spots are which basically is a foundational piece or response or mutilation of the rest of the site oh my god you should freak out immediately instantly use it if that's your business model here I've apologized and it's the instinct especially you know awesome talk with our small media business here especially in terms of medium size business you have enough you know you
care you know patients to care but you're also a little bit concerned you don't want to be the person that things go wrong oh my god something's gone wrong it's just making know as quickly as possible well patch it will fix it'll be done it's good which is awesome if that's what happens but probably not a you have a serious problem if you people are already on your networking we're already behaving in a bad way closing the door at that point is a little bit late you know they're already there I'm guaranteeing they've already got the system access so all the way maps where they got in Newark we hope due to the ways I've got to see them get
it next time like it's in your already shot man it's too late to put bulletproof vests do something else you're in a different stage of the lifecycle so simple more focus on is okay if we're gonna he's the best might fix it we'll patch it will figure out the exploit figure out where you are analyst figure out what you need to know your first question is probably where am I what's going on like I'm probably already breech is that reason to be concerned yeah I figure out how I'm gonna reach but also I want to make sure that as I turn to sure of how I got breach I don't lose what happened after I got the days
of bad news breaching just a breach or pretty much over right nobody just does this for finding where it's a job so if somebody's breaching you they're doing it because they want to make money off of you or steal something of value something interests so if what you do is you run roughshod over the bit to figure out what they did after they got in in the rush to close the door you're going to miss a lot of things and then you're going to be behind the curve when you try to figure out what's the actual damage what's the impact to my customers what's my legal liability because you've already run over mostly your indicators
and here's the other exciting thing odds are pretty good if they're already in your network they're going to find other holes other problems so we can go slamming that when we're shutting almost immediately what you'll do is you'll tell them oh well you know they know I'm here they found me I have to be a little bit stuff here knew some of the other doors or ring itself they will adapt I mean the important thing remember again we're doing like acts a little grown-up adversaries they do this for a living right like if you're of your job one day and something goes wrong you don't know well graphically you think okay well I'll get around down what do I have to
do maybe have a bad day at work jobs no no right sing it in order to get a handle on this I think before it before we proceed with the rest of this discussion it's good to take a moment to think about great we need to be able to describe our adversaries it's particularly persistent wants folks that have tolling folks that maybe you know you're having an attack some somewhere in the remediation discussions for for persistence a tiger kind of realized that this attack was probably on the Gantt chart wall go with some kinds discussing all back like oh this is really somebody else's project and we just have to be in the wrong end of it how do you describe that
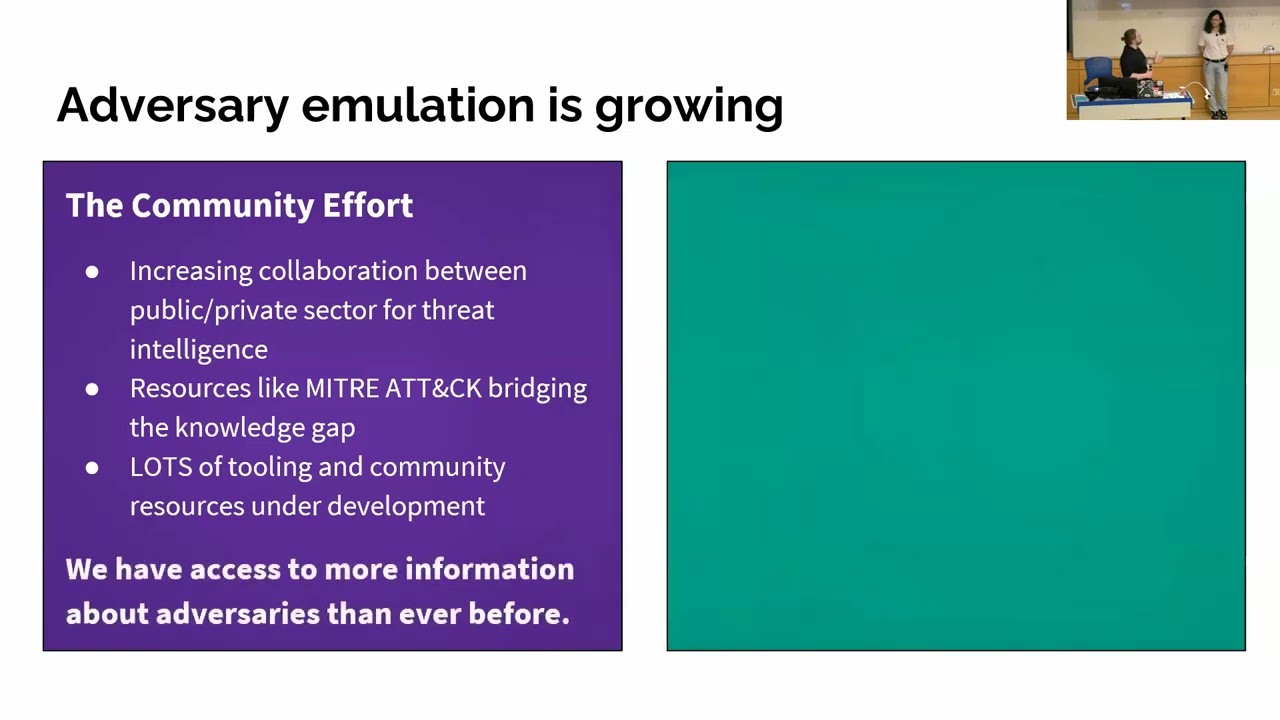
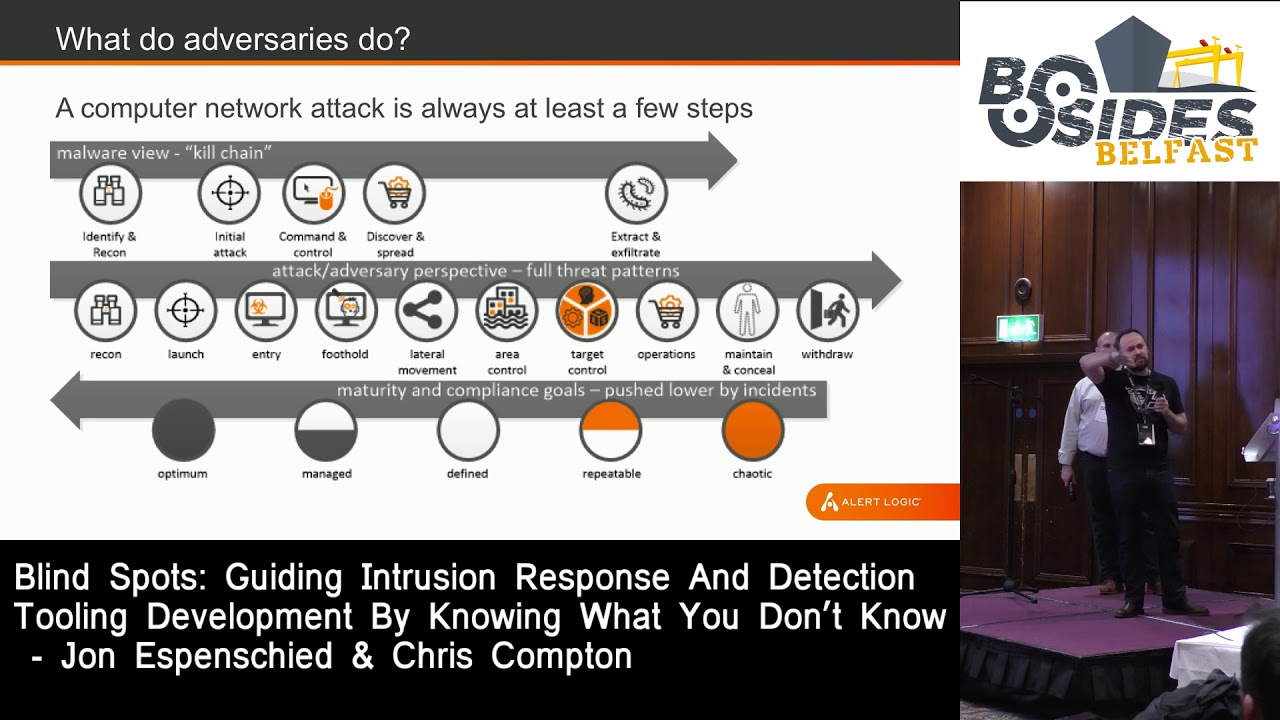
and before we can get into to answer the question of you know how do we protect against or respond to versus an attack we have to have some language this this you know reasonable one of the things that's been in the news or pervasive I think people are starting to pick apart now is the kill chain approach that's characterized on top which not not terrible it's very malware centric there there are lacks certain ways of describing operations repetitive attacks persistence and pieces but if you're being you know if you have a matter of a an adversary that's basically flinging you know pieces of malware at you through efficient into which is a phishing attack it might be sufficient
if you have if you're a higher profile target and you've got even a dusty little adversary or even tried to detention of user groups that perhaps have some national sponsorship you're probably going to need a larger language to subscribe time processes persistence house before we can get into you know figuring out blonde spots what that what they do that you can't see you have to be able to express it so it's just when it's worthwhile to look at you know a couple of different ways to describe a whole attacks looking at you know how do we have we expressed these things so that we eventually have some categories for a detection controls and then we can
figure out where they're not so good at the bottom here this is this sort of a bit of a piece to go up for another discussion but you also need to be able to talk to the business risk the enterprise risk comes when they come in wind when the non-technical folks have actually pulled on to budget for remediation controls Ritter for all that and they say how that is what's the problem being able to speak in a enterprise risk language to be able to map back from you know somebody has free rein for a lot of movement through your requirement that little being able to translate that back to you know a risk metric or a CMM metric where you think
you're a four or five and really your if you have an adversary that's showing you back okay out of state they understand that so that you can handle this both at a technical level and a business interested in tracking attack let's say you take let's take the middle is in the ten stage advanced a circle you can put that on turning math that against taught right how long do they spend in each stage how much time has been doing recon almost time they spend laterally when you start making these kind of interesting curves based on you know where that response time so let's take a look at these sophisticated this is organized criminal group there's not a
nation state or its ever did enter stuff together coming out of so this is graphic soft this is essentially a ransom water attack it's pretty standard this same attack looks about the same now in the same set attack or something like that it's also worth noting the dates its 2003 so you know we spend a lot of time trying to figure out new advanced attacks and different bands index great but they're probably not rent spanking it you know this still works nothing's changed but if we look like total time we'll look at the timeline here a whole bunch of time recon kind of the initial commencement the attack it's been a lot of time figuring out what
they're gonna do they don't come in and start banging around making noise triggers it's also worth noting a lot of detections out there are under the IPS model you know when we're being under attack and really that comes down to like entering for things which if you look at the time slice is just about the narrowest face in this grass so then you're into a really you know you're hoping you're looking at the right now eruption at the right time yeah that's a detection you've got to take we all have we wanted to read about that little window and that's cool if you do absolutely need to have that window we're gonna talk about how you would
expand maybe see the rest of the round all of the other things they do after they create okay long time figuring it out and by the way I have not never found a lot of love looking for attackers in their constant space there's just too much noise it's pretty tough sell everything that on the other hand what's there anything you'll notice they spend quite a few days bouncing around and screwing around finding other stuff all sorts interesting stuff so if you know it's a squared away to ever unless we're one of the ones that interested just ahead a little bit of Connor to the pain the the ransom this is a this is a 2003 ransom attack and
you talk about ransomware now since since he brought up we actually had a different set of graphs a comparison between this attack against graphic software which effectively this is where one of the earliest cloud providers is this is an infrastructure that looks a lot like what a sheared AWS does today is very early version of this happen to be the largest platform for gambling in the world at the time plus all of kpmg's extranet infrastructure idea she had a lot of other things when we translate this into a modern attack the Samson style attack pretty much the top of the grassman is a very recognizable the operations of the same tools are totally different but
what they're doing is the same as being able to characterize this attack in this fashion using it using a dependency model with buckets kind of built similar state kill chain this allows us to recognize operational similarity it's not just technical lots so we're able to tell what what kind of an attack what what does this look like in the past even if we have that persons that swapping tools and updated it so a lot of the research we do this we look at lots and lots of all sorts nation-state petty criminal organized nation state criminal and one of the things we found was we tracked technical sophistication of attack and operational sophistication attacks ever technical sophistication
you know how badass was this just you know there are PC become exploit was this like some crazies are in an operational sophistication was it just a one and done or with lots of complex steps together we found that there is ZERO zero correlation between technical sophistication and damage it doesn't matter super badass super simple no privilege there is a one-to-one correlation between operational sophistication and damage if you can string together a bunch of complex events or dangerous if you've been incredibly elite malware you might be dangerous so the important lessons to be afraid of your program managers they're Muslim changers with a less well-structured attack the gjx attacks her Herman's demon Buster's fundamental attacks were
all betrayed by the same group most of their attacks look like this this is this is by contrast of what a mostly manually operated attack run by folks who didn't do good recon that's kind of what this looks like you know in this case the this crew managed to get into a single business branch location get into the network phone around for a while get a foothold on privilege systems eventually get to a corporate backbone network get back and started building a sniffer looking for sixteen digit numbers off the we're trying to try to gain credit part of it it didn't work and then they got it to work and then that filled up and crashed
and then you know then they did various things it bubbled around for a couple of months before they actually got that's the morning and the point here again we didn't read up on the individual attacks at that point ask me about baseball card stuffs stuff later but one here is to be able to contrast these these kinds of attacks and if you see a lot of this pitting carried by versus a lot of this hitting your environment that gives you a better sense that maybe if this is what's hitting your environment you have a better visibility have a better chance of seeing this either you have to be really better at recon or you have to find these places where
you have a little bit better visibility or bigger time slice or some combination of the two because if you have weak visibility and a very short time slice you can't see you can't see what's going on you can either beat those up or by contrast you can look at something like this say where these guys were tremendously noisy and they're sort of lateral movement bouncing around between machines they were only not caught in this situation out of pretty much the shared companies the operators of the books they didn't do what they weren't doing monitoring its basic environment there's a lot of pressure than this environments simply do not spend money to watch anything inside they're
watching they're outside of the movies so so what happens when we can describe the kinds of attacks than we have and we can then figure out what what's likely to hit us oh look here is that David Buster's attack these are the typical kinds of things this is this is a nice little characterization of yes we can find distinctive parts of attacks if I see a whole lot of attacks that look like this that are hitting my organization pull out the distinctive piece isn't saying I need to look for this stuff I had better have my stuff together for these categories of services host compromised foothold behavior where you see something right after machine's been
compromised and someone is bouncing themselves parallel systems where some unilateral movement if you see a lot of these attacks then that's maybe where you should spend your your budget it's it's terribly frustrating and I know them a lot of folks in this room will look at you get hit with a ransomware attack it somebody says we need to spend a bunch more money on AV well maybe the AV we already have pretty good just need to update it don't it's not really you know that you're lacking budget or lacking the tools you need some minor tweaks but you were entirely blind to seeing an operating or spreading through the organization point here we can take
this sort of information where you can see the typical attack and take that and work now hey actually I have a set of tools this is just some things you might be able to see and just map it out just go through an exercise up hey actually I'm pretty good I'm seeing initial compromise on a host we haven't really we could seek immediate pose to compromise things I don't see what happens when I hit with something because it was updated immediately there's there's there's tools being brought down and someone's it's starting to move around that inland rail or maybe I'm really weak on being able to see concealment or maintenance maintenance activities for for a mercenary that
wants to serve the tip to sit around the network and maintain control with this sort of of I've got some idea what tools they have I have some idea of what kinds of attacks I have if I could think about in a structured way then I can go back and do an inventory thing actually you know the numbers on the left are the typical that's sort of the top attacks I see in each category so I've got maybe only four or five different kinds of recon that are typical of what I'm seeing out of my environment I need to be able to detect those or maybe I see nobody I see about six I've only got
controls that actually see about work I have a bit of a gap that everyone does the middle and mid-range here lateral movement I can see most things but now by contrast entry and footholds initial compromise on a box with mobile activities somebody printables throughout a network in this case I've got a huge investment I already have a lot of money spent on the snap tools and structure to maintain this maybe I need to have a look at tweak those but focus focus on the areas where you have a gap between the patterns of attacks we see and the detection capabilities of the tools you have it's kind of common sense of here we go of course look for things
you know hit by things you can't see you then there's no but there's sometimes a surprising lack of consistent methods to do this to be able to engage in that kind of structured thinking so that's one way that we've we've had some pretty good luck with working through that sort of a structured problem and also this gives you good language when you're speaking sort of are making decisions it kind of out of that initial panicking for you oh my gosh we've spent a lot you know wondering what you would now say it's entering foothold and we got hit we should spend more there maybe but maybe usually actually think about what else you have what other tools are available
where else can you grab that it's that versatility as opposed to just kind of doubling down on their turn so doing this lets panic and then speaking to this maybe you've got hit with with attack and it was successful at some point in that she was a graphical curve you had a control failure and they were farther than they really should but that may or may not be the best place to throw more money or effort that defensive her detected control so you want to have their you know detection capability and not just to panic and and throw capability at the last thing that happened to some understanding of threat history what's happened to you being
able to describe in a reasonable way other than you know say hey we have this at six months ago two years ago it was real bad can't do anything with that we need to be able to break it down into what part of it did you miss essential piece that you thought you had under control and you need to do something how many d'etre the controls what they what they actually see going through that exercise it's pretty essential patience a little bit of patience this is this is an area in which were forced to react really really fast - to bad things and in a lot of cases especially for the really bad ones if
you're on the wrong end of a of a an adversary who is attempting to manipulate behavior they're gonna they're going to keep hitting you want something that's described and maybe you're missing that they're effectively causing you to deprioritize you're looking for maintenance concealment is you spending all your time updating and chasing malware that isn't actually doing anything and you're you know you don't have enough time to see that there's modified that's not really what they're doing you know you won't find it unless you do some sort of structure analysis animal sanity we're talking about men attackers but at the risk of stating the obvious no it's important to you but know if this stuff gets stolen were defending
it'll really slash the problem down look oh my gosh they took over something about which I don't care oh my gosh it just happens we're both we're out of business that's an extinction-level event look you can slice those out it's all about whittling the problem right and that'll help you know where to be looking what a couple of notes to add to this what we did and I mentioned that person I have a bit of a shared history can come together and got apart at different organizations in a couple of different capacities put out a couple of stack of baseball cards little threat baseball cards at Microsoft those actually were the shiny silly friend to a threat
pattern database that we created and a way to communicate to the rest of the analysis and response staff at Microsoft and partners at Amazon Google where we could actually get them because they picked that up and went boo shiny then they turned it over and they started using the language we were putting in their mouth since they sort of described attacks and more in a better way that we actually can now back to our controls that was a that was a neat way for us me a little bit about you to do that that proves terribly effective there's a product being able to go through the last five years worth of history and saying what we could hit with these
things that weren't hygiene your hats interesting stuff let's break it down and see what it is Hey look the number of attack activities was pretty limited pretty small photo op tools all the time that do not swap that where the break it down is about all right we have 70% coverage for everything that's been done to us in the past few years informing people showing you know basically sharing that knowledge finding a simple way that doesn't you know cause people that want me to do 1,000 you know a thousand in that database finally some simple way to categorize and that about controls is hugely hugely effective and to Chris's point he's actually kind of inventory fine which
you have and now this is essential communication yeah I mean if you control all of your own budget right good most was done right let's just have to go to our executives and say look I know we've spent this much we've spent this much of it really well you maybe don't like that much well here's how are you squeezing those detachment when is for living right this is business so you can communicate through the way that sane and rational that's not super gallery yep coming back to being able to say let something bad happen to us entra together however our delight what we can we saw it we handled it it's it's done please don't reshuffle
my budget make me go buy tools that they don't need I guess you know I haven't been in an organization where we don't have things that are sitting on a shelf where yeah they want us present that while this for us we have four of these overlapping tools we don't use versus need there is being able to do this in a succinct way needs structure to our businesses look here's what we need there the gaps between the curvy line and then dandy what we have to detect much more effective to be able to drive that visible hotspots and to end even a demure detection the metaphor is if you have a fire suppression system if you're
super paranoid have to rank is one grows you probably not be six if you've already got two in your example I've just had this brand new fire suppression system is it better to get rid of the old one no okay questions thoughts comments criticisms
one of the ones that we thought about this is sort of the context of automating this was to be to map out the sort of the common attacks to give an example this was this was a little bit crisp Amazon we took the previous several years worth of incidents of Microsoft everything that was not a trivial event mapped out what was every action that the adversary took who filtered out what the analysts did to find it little natural language exercise there where to go you know if the subject or a predicate if the subject isn't the adversary that the filtering out all know it would filter it out and then kind of normalize everything they
did and the surprising thing was pretty much every single attack over half a half a decade they only did amount of forty things that masseurs only did for about forty they use tons of different tools to accomplish but the actual attack activities you know we were able to kind of categorize but then it leads to it's a couple of steps it's a couple couple logical steps answer your question but once you have an idea of sort of this normalized buckets of what's happening to you and be able to describe the the you know they're only knew four or five different kinds of sort of enable allowed or a little bit that over the curve for example what do
I need to be able to query those if the thing that happened before it only gives me IP hostname but account and so on if I kind of drive out the what I could query for piecework logical adjacent before an actor after that observed activity I've used up the investigative usefulness of the thing I have go ahead remediate just don't don't step on it before you actually ask the questions for what might come after other other thoughts questions is it really possible to identify actions without getting fixated on tools or techniques because I think conceptually actions make sense but then identify lateral movements I'm not sure that's that's that's partly there a practical approach to identify actions it was
effective look what tools are it's my in practice it's always a mix I mean there's there's a certain amount of free labeling like everything everything that comes out of my a be every work there is going to be effective my mind as you know who's top of us and of course they're gonna be a lot of activities that you see on a network where I'm not sure what's out here this is all for us this is authorized behavior I need to actually spend some time looking for certain behaviors over time so if you're doing extreme days detection it's very hard to find those and you might have to do correlation over time where I can
find it has the hash attack based sequence of connections and different usernames or a period of a few minutes or a few hours that I couldn't see and I'm just doing a sample and those activities it's only practical to develop the detection containers by looking throughout history and see what about it because I can't go to finding rules and it's a good organization for every possible action that an adversary to take but I can write rules for the hundred things that are we that we've seen that are actually happened to a functional organization there's the separation of malware is a tool is not it is a thing that a person is using to do something the person ultimately is
the first it's the person who's going to do something in the same way you're using your detection tools to figure out what they're doing the detection is a way of mapping that it is not the same as so the ability to discern these capabilities together whatever I hear their logic makes about let's string them together you know understand what you're seeing out of that understand what you're seeing out of your other capabilities looking you're just basic user to my usage deep you know ways to say try to rob a bank without using this more time alright try to control an effort without using than that and then the question for what are they doing different than all your users
if you're doing something bad by definition you're doing something different so what are your anomalous string all that together and actually really quickly and easier than you might think put together a recent picture of the problems your honor threatening attacks yourself any other questions if you think of super loose filtering premise John and alert logic see our similar logic this is what we do is our thing well I'm happy to worry you over dinner but these sorts of things I saw it so like if you want to talk more police business thank you very much [Applause] [Music] [Applause] [Music]