Beyond HTTP: A Crash Course Hacking IOT's Non-HTTP Attack Surfaces

Show original YouTube description
Show transcript [en]
cool so should we get started yeah all right welcome everyone hi uh this is beyond http a crash course on iot's non-http attack surface where we're going to kind of dig into what does it take to explore an iot device that doesn't have an http interface that's missing a web interface what do you do when you come across one of those devices now before we get started i'm sure some of you are wondering who this guy is hi i'm me my name is justin on the internet i go by almost json i'm a senior security consultant at car systems uh where i've been for about five years so in the in the five years where i've been at carve
i've spent a decent amount of time hacking iot devices i'd say i've hacked about like 50 or so iot devices at this point they come through i hack them i go on with my day and that's it and so at this point most iot devices just kind of run a blur i don't actually remember each individual one uh or exactly how they were exploited but i do kind of remember a few of the first devices that i ever hacked so let me take you back to roughly 2017 um it was my first internship i just landed in new york city and i was excited to start hacking something so i go to my supervisor at the time that's
max and i'm like hey max what am i doing this summer um and he goes he goes through the shelves and starts rummaging and pulling down iot devices he's like here's two of them have some fun hack this hack them this summer and find out like what you can do about them and so that was actually a really great experience for a summer of hacking and it was really really useful i ended up learning a lot about the spectrum of iot security and how you have very vulnerable devices and you have some secure devices so let's take a trip down memory lane and let's talk about a really insecure device this was an internet hotspot
and um you might be wondering why was this yeah why was this insecure well i've never hacked anything at this point so i did the one thing everyone should do when you don't know how to do something go on google look it up read the manual and i found a lot of websites that kind of guided me towards hey if you're going to hack an iot device and it has a web interface the steps you should take are pretty straightforward log into the web interface go to the diagnostics menu find that ping command it's probably vulnerable put in some kind of command injection payload i really like this string here because it's obvious when it
works the device just quits and reboots and then you hit the submit button at this point one of two things is going to happen it's going to reboot or it's going to fail let's say it fails well on iot devices that have web interfaces there's a bunch of other places where you can input some kind of command because iot devices let's remember here are really bad about input sanitization so maybe the ping command isn't vulnerable okay what do you do next go find the trace route that's not vulnerable okay what about uh the wi-fi ssid is that vulnerable so in the summary here is that when the ping command fails you kind of just keep on
going you keep on digging through and looking through the web interface and so this device is vulnerable it rebooted as soon as i put that command in there um so that device was hacked and i think this is kind of um a good example of one of the more insecure devices you'll come across these are devices that have web interfaces and you can just go find the ping command and they're vulnerable this is the low end of the iot security spectrum on the upper end of it on the secure end you have things like an industrial smart light that don't really have a web interface they're missing a web interface they might not have anything that's really
standard you can explore and in fact the um industrial smart light x i looked at didn't have anything i spent i think two weeks looking at this and i couldn't find a way in i didn't get roots i couldn't get anything to execute it was kind of disappointing to blow two weeks on a device where all it does is turn on and off and you can't make it do anything else besides turning on and off that's a pain but at the time i considered that to be a secure device why i had not really hacked anything at this point so i didn't really know what it was going to take to hack a device that didn't have a web interface and so
i went on the internet and i googled for information on how do i explore some of the alternative surfaces on this industrial smart light and what i came across was kind of scattered information it wasn't too great it wasn't as well formed and well pointing as web interface or web application hacking if you're going to hack a web app who here has used burp who here knows what man the middle proxy is who here knows what charles proxy is who here knows what xyz like all of these web tools are you have a good list of them and if you google them you have the oauths top 10 there's a great list but there's not that much
information on uh at the same level for uh alternative attack surfaces at least all put together and that's kind of what this talk is kind of doing so my goal is to cover three different attack surfaces at a really high level i want you to know what the burp for bluetooth hacking is going to be i want you to know how you approach an android application so that you can explore it and get access to source i want to talk about have you seen the in-map yeah probably but what do you do when you come across a random port and so to do that we're going to talk about project prometheus this is a really fun case study
so i carve we have like research projects every now and then and one that a bunch of our team was doing is exploring uh smart grills and what is capable what can happen when someone exploits or hacks a smart girl and so throughout this talk we're going to talk about project prometheus and one of the grills that we exploited and how we use some of the techniques they're going to cover to just export that girl and make it do something that's really not supposed to be doing so before we can talk about how to exploit something we need to talk about attack surface so it's a smart grill uh that means it talks to the internet and
it has some mobile apps it has an ios and it has an android app it has bluetooth and it has wi-fi which are all going to be the surfaces that we're kind of exploring and covering at a high level today so we're hacking a smart grill how do we get started well on the network interface most iot devices have some kind of network interface whether it's wi-fi cellular or an ethernet connection of some form iot devices need to be able to connect to the internet to do something now a lot of you have probably explored iot devices or kind of looked at network interfaces and you know what a web interface looks like you go to port 80
you connect to it you log in but what about some of these other attack surfaces what about these other ports that are open how do you find those well first for starters here in-map you probably have used in-map you probably know roughly what map is if you don't it lets you scan the open ports on a device or an ip and that's really useful for us it'll tell us what's accessible on an iot device what's not accessible and for us we're primarily interested in reviewing the output of nmap and trying to figure out well if we um we're trying to review the output of nmap and figure out what is what are these ports that are accessible what can
we do with these ports that are accessible so this is the output of an in-map scan this is actually just my home router or something along those lines it really is my home rider um and so when you do a stand of like a home router or something you'll come across ports that look like this in-map will tell you okay port 53 is domains it's probably dns or something 80 and 443 or http that makes sense and then you get some unknown ports what is port 4420 what is port 4282 i don't know inmap doesn't know so let's talk about what you do in this case so i have a list of ports and i like to break
down fortune two things that are useful and things that are not useful so map has already broken them down into two categories we have known and unknown anything that's known inmap understands as okay i think this is an http service because it's on port 80. but nmap also lists things as unknown that doesn't mean it's not an http service it just means it lives on an unknown port so let's explore some known ports specifically we're talking about known ports that are useful when you're looking at iot devices and you're looking to go immediately to root screw trying to do some kind of exploit you want straight route access and for that you're looking for three specific
ports you're looking for telnet ssh and adb now these three are really important because they'll take you immediately to root access if you can get a shell if you can get any of these and you can connect you get a shell iot devices are by and large really bad about privilege separation so they'll just let you connect and if you connect you get root access and that's always great but there's one challenge no one's going to expose telnet ssh or adb on a network or on on a device unlocked this is the problem you have to bypass authentication for uh these three these for these three protocols so how do you do that um i think the general
recommendation is if you don't know if you don't know a password use the default passwords go online google what the vendor's name is see if someone else has already done a little bit of work there see if there there are common threads in password schemes that have been used that's one way to approach it the other way to approach it is to take a look at some of other places where this password could be used mobile applications which is a piece that we'll be talking about are a treasure trove of information they often contain details about a device that you don't know that the manufacturer does know and that are required to do some kind of
exploration so this is just three random ports that i like to talk about because these give you shells and who doesn't like a good root shell but when you do an in-map scan you'll find a whole bunch of ports that are other ports that are unknown ports um or that are known ports but unknown to you an example might be mqtt or snmp you might have heard those words we might not know too much about those so what do you do when you come across a port of that kind port where you don't know what it does well this is where google comes into play and this is i think a really important point when we're talking about
iot devices there's a huge attack surface they all shift they change there's not a one-size-fits-all iot device they all have their own ports they all have their own profiles so you need to get comfortable with googling and searching i personally always find myself looking for three specific terms i'm looking for whatever service followed by tools people develop tools for specific protocols that are helpful github is a great resource to find tools for a specific service exploits are wonderful people package those up into useful useful files that are one click and run always search for that for whatever your protocol is but most importantly when you come across a random protocol you're kind of trying to find out what's its
usage you need to know okay smmp is a configuration protocol that could be useful to me i could modify the um the root password maybe or smp i might be able to enable telnet over s p the goal here when you come across some unknown um protocol to you is to find out what does it do and could it be useful to you as a tool as a tool for exploitation sometimes they're useless and it's important to remember that not everything is useful when you ex when you explore iot devices or open ports quite often the best thing to do is to do a little bit of recon take take note of what some port is and then move on
so when you move on you might get done and exhaust all of the known ports that that in-map gives you but you might come across something that is completely unknown this is probably a custom protocol when we're talking about iot devices now custom protocols are a lot of fun but they're also a really big pain in the ass because they're big time sinks you don't know anything about them you don't know how to interact with them directly and if the if the duck gods or google gods whoever you believe in for search engines don't bless you it's going to be really hard to get some information to figure out how to interact with these protocols so i often
take a very light approach to these taking just enough time to do something like make sure it's not an hdp protocol or it's not it's not a protocol that's it's not a port that supports http because sometimes this is kind of often you'll come across uh http servers that are living on some random port it shows up as unknown but it's just accepting http you might want to send some empty and some random data this kind of data will often trigger um an error message that you might be able to google and search finally don't discount the possibility of just sending help you'd be surprised how often you can ask for help and you'll get a list of commands that can
be ran this is a rebel you'll see you'll come across these occasionally so definitely do that but most importantly if you have a custom protocol and you have a mobile application the mobile application is where you want to be digging the mobile application has to know how to talk the customer protocol so your goal needs to be to reverse the mobile application to get those details and we'll talk about that but before we do that i've said words they've been a lot of words i think and um why don't we talk about how we can actually use some of these skills to hack something so let's go back to project prometheus this is the grill
hacking project and let's do a port scan on the grill so i've connected the girl to my hot spot and it lives on on 192.168.1.100 and i do a porch stand and this comes up ports 4577 it's open and then in-map is telling me it has ssl slash unknown so this to me means it's protected with ssl and then there's something else going on so like i said unknown protocols or unknown ports are a big pain you don't always have the ability to interact with them and it's kind of guessing so i just do the four steps that i normally do which is check is an http service is it or not and so i run a quick call command
on it and immediately it becomes obvious that uh yeah it looks like it might support http uh but i got an error back so this is ssl v3 alert handshake failure i've touched enough of these iot devices to know that this is a show stopper it just means that we're gonna need a special certificate to interact with this endpoint do i have the certificate no i don't that sucks what do we do next keep on moving you don't stop keep on looking for whatever comes next you can get some more information information is power in this game so you keep on going in our case we're talking bluetooth we do have a smart router here i mean a smart
grille here it supports bluetooth so let's talk about why bluetooth matters at least in general here so wi-fi is one network service or one wireless protocol that iot devices support the alternative is bluetooth quite often you'll come across devices that support wi-fi bluetooth and also have mobile applications associated with them so it's fun to also just keep on looking at the at the bluetooth interface because the bluetooth interface is also going to expose a lot of the functionality if it has a mobile app it's probably going to be talking over bluetooth and if it talks over bluetooth there has to be somehow a way to trigger functionality via the bluetooth interface so it's just a useful place to
go looking now before we talk about how to hack bluetooth let's talk about how bluetooth here works so bluetooth works in a client server protocol so how many of you have heard client server using the term in the context of http right okay so bluetooth is really similar actually in the way that it works uh relative to http so i'm gonna kind of try to equate http and bluetooth and hopefully it gets the message across so in the bluetooth world we have a client this is probably going to be your cell phone most everyone connects to an iot or some kind of bluetooth server using their cell phone it's really rare to for a user to
interact with it directly so in this case we have a smart calendar it has a bluetooth server on it but a server is kind of useless if it doesn't expose endpoints in http terms that is called that's an endpoint right you talk to it by making a call request or some some kind of form of http request to it in bluetooth terms it's called a characteristic so not an endpoint but a characteristic so our smart calendar has three different characteristics we have git events connect to wi-fi and connectivity check i'm sure you can kind of guess what these do get events just going to list out what our events are connect to wi-fi is going to connect to wi-fi and
connectivity check is just going to check are we connected to the internet or not so before we can actually start talking to the bluetooth device we need to connect and pair who here has used a bluetooth device in the past ever and seen a prompt like this it's asking you if do you can put in a pin and so this is the most common way to uh to connect to a bluetooth device this is one of four different authentication methods or pairing modes available for bluetooth devices now of these modes one it's called just works is um is unauthenticated this means you can connect to a device without needing to put in a pin but everything else
that's the la the bottom three requires some kind of data transfer they require an authenticated method of communication now if you've played around on the internet before you know there's websites that you can go to without giving over all of your private information like checking out uh maybe the front page of google you can connect to it without having an authenticated session right if you want to post something on facebook what do you have to do you have to log in you have to connect that's an authenticated session and so on um on web servers you have endpoints that require authentication you have endpoints that don't require authentication in bluetooth you have the same thing some endpoints in our case
git events and connect to wi-fi require you to be authenticated others are accessible without authenticating so you might be wondering now how do i actually send data back and forth over bluetooth if you're talking about http it's pretty straightforward you make maybe a get request and you get data and data comes back you make a post request data gets pushed and something comes back in bluetooth it's very similar except there is no get or post or delete or put or method names is just reads and writes you can read to an endpoint you can write from an endpoint and you can read and write from endpoint each endpoint has its own definition of what it allows
yeah so for example here our git events allows read connect to wi-fi allows write and connectivity check only allows read write so uh i said uh i said initially that everyone connects to a bluetooth device using their phone who has connected to a bluetooth device without using their phone before what what devices have you guys used raspberry pi okay and you had you wrote your own thing right your own library yeah you're using something the point is um you need a generic client you need something beyond a phone that you can just talk directly to a bluetooth device with now there are a couple of different generic clients that you can use so i like to use better cap
it's uh it's this badger looking thing uh it's my favorite it's kind of to me sort of like the burp of uh bluetooth hacking there's also light blue and there's blue utility which are alternative um alternative tool sets that you can use on different platforms and so the reason i like i like better cap is that it lets you scan bluetooth devices in your area it lets you connect to them using just works so an unauthenticated session so we can find out what's accessible without needing to authenticate and it has a really nice gui the problem is it's linux only so run a linux vm i don't know what to tell you there or use something else
uh okay so i've talked about bluetooth i've talked about how to connect to it let's talk about how bluetooth endpoints could be implemented so in um in our smart calendar we have get events get events is some kind of collection of events that are coming in the future maybe that's stored in a database somewhere maybe we can do a select events to pull down that data that's maybe how it could be implemented on the back end connect to wi-fi on an iot device maybe it updates some configuration file and that updates which which wi-fi network we're connected to makes sense the next piece is connectivity check how on a web interface would you implement a
connectivity check you probably implement it using ping this is no no different from a bluetooth a bluetooth device you'll come across bluetooth devices that use very similar um very similar set up setups and code as a web interface so in our case connectivity check is just a a system call to ping dash c followed by whatever user input you provide now that's probably likely vulnerable to remote code execution and this is where i want to talk about the kinds of things that you can look for when the kinds of things you should be looking for when you're poking around bluetooth so bluetooth you should kind of treat it like a web server in a lot of ways it
really is it might not use https gits and posts but data is being sent into the device it's accepting user input over whatever uh characteristic is defined and iot devices really suck at doing data validation so if you can send data to a device over bluetooth you should try to do command injection you'd be surprised how often that actually works especially if you're if you're digging around iot devices that are that are primarily linux based embedded systems rce is a great way to or just sending command injection payloads is a great way to find command injection payload or command injection vulnerabilities so this is an example of better cap as you can see it's up there's two
sections there's a red section and there's a green section the red section is what you'll see when you scan any bluetooth device more or less these are pretty generic attributes you get details like the vendor the color of the device if they want to specify it the device id and maybe like the company name and that's all accessible without having to authenticate you can also you'll see down here in the bottom on the green side come across other endpoints that are undefined these are random numbers and if we take a look uh they're readable right also we have that much information we can see that it's also lacks it also defines which ones require authentication and which ones don't so
if we look at that uh at the uh if we look back here at um the outputs from better cap we'll see that there are these random numbers what are those those random numbers are how you talk to bluetooth bluetooth like i said it doesn't use gits or posts it has these random uuids these are long strings of numbers that define what something is so maybe that f1341 is the equivalent of git events and if we want to talk to a device over bluetooth we're going to make a request to f134 using better cap and get a response if we want to post data we need to use the specific endpoint number so maybe in this case it's 63b we send data
there and something happens and so these are long arbitrary values they probably don't make sense right like who would have guessed that 631b would be uh get calendar events or whatever no one and this is a good uh this is something i've noticed that vendors tend to focus on they'll hide functionality inside the bluetooth interface because well who's going to go poking at the bluetooth interface when there's these random long strings who's going to guess that this super long string is going to be a connectivity check no one's going to guess that so what are we going to do if we're trying to exploit these things well we're going to go look for the probably the android application it
has to talk to it we can also just kind of guess guessing is always an option send random data to all these endpoints maybe we can do something but let's talk about what we let's let's use an actual example to see what we did so let's go back to project prometheus this is a grill it had a bluetooth interface the output that you saw here was actually from that grill again the red stuff is kind of irrelevant to me it doesn't matter it's just generic information what i cared about is the vendor-specific implementation details this was uh everything in green and what is highlighted here is that there's two endpoints or two characteristics that matter there is a
insufficient there's one that we get insufficient authentication error for that means we need to authenticate and then we get another one that returns an open curly brace and a closed curly brace that looks like json to me does anyone else think that that could be json yeah so actually this grill spoke json over a bluetooth interface is it unusual probably not really kind of i don't know sometimes it is you'll come across bluetooth implementations that are very similar to web implementations especially when you don't have a web app the bluetooth interface becomes the web app so i did some more digging on the bluetooth interface um one the fact that it only had two characteristics or endpoints was
kind of odd most iot devices have a number like 10 or 15 characteristics exposed all with a mix of read and write this one was also really interesting because there was one that was unauthenticated and there was one that was authenticated that kind of piqued my interest i want to find out what the unauthenticated one would do so i dug further i sent random strings back and forth and i got errors back i got json malformed errors so yeah that kind of confirms our suspicion it's probably json but here's the problem i sent properly form json but i didn't know what the keys were how do you form json when you don't know what the keys and
the value pairs need to be it's a black box it's kind of pointless to explore something when it's a big black box and you're just kind of banging your head against it so what do we do we're stuck again we keep on moving this time we move on to the mobile application iot devices if they have a bluetooth interface they're probably going to be shipped with some kind of mobile app so why do we care about the mobile app there's one reason and one reason only that we're really interested in the mobile app and that's the reference implementations inside of the app the app has to know how to communicate with our iot device otherwise the app
wouldn't work it needs to have the details and the information necessary so if we come across some kind of custom protocol the app needs to know how to decode and encode any data that needs to get sent in that custom protocol for us though we're primarily interested in the bluetooth interface so the mobile app needs to know how to talk to that bluetooth interface and it needs to know the json information so how do we explore a a mobile application specifically we're talking about android here so for android the first step that we want to do is we want to download a copy of the apk now you can do this a bunch of different ways i just like to use a
tool called ap keep and just want to give it a shout out because it's made my life so much easier it's it lets you download android apk files directly from the play store or from a third party source it's just it's just a great tool developed by the eff um so once you have uh the application it's kind of useless for all of us right so i can't look at an android application and just say okay this android application goes to uh does all this functionality like i can't reverse engineer it in my head alone it's you need some kind of tool to help you do that android is built on java and android applications
use java they use java byte code or similar so we need a tool that will take the java byte code and turn it from byte code to original java java pseudocode and for that we're using jdx gui gtx gui is great you give it a an apk file and once you give it the apk file it spits out java pseudo code i say java pseudo code but in reality you can almost always copy the java code into a working project and run it it's really nice how uh how good chad x gui is at reverse engineering on obfuscated android applications which sometimes they are unobfuscated so at this point we have a few things that um that we're
looking for right so we have a um we have a application we have the ability to reverse engineer it that's using jadex gui what are we going to be looking for what are we digging for well we're starting off by looking for some hard-coded secrets do you recall how the um how there were these known ports these known shells that had authentication maybe we can find the secrets to authenticate in the mobile application we're also looking for reference details about protocols if we come across an unknown protocol that we can't do anything about like i said the mobile application needs to know it so maybe we can look for some of that information in um
in the mobile app we're also looking for just details about how the device works the mobile applications are a great source of just general information even if you're not looking at it from the perspective of like let me hack a bluetooth interface or let me hack a custom protocol but rather for from the perspective of i want to hack a website the mobile applications sometimes have details about hidden api routes they have details about different parameters that you might not have considered or you might have not seen in a web application so mobile applications are just in general a great place to start looking if you're looking for some kind of information so let's talk project prometheus and let's talk
about um uh how we used jadex gui for that and so for um uh so for project prometheus we're looking for a couple of things right so we have in it we have an android application we're digging through it trying to understand how the mobile application works and interacts with the bluetooth device and so one of the we have a set of questions that we kind of would probably want to answer what are the characteristics we saw those bluetooth characteristics they were long random strings let's kind of figure out what those do what how to interact with those and what kind of data we can send we also came across port 4577 that was protected using tls
so we're probably looking for some kind of certificate that we can use to talk to the device maybe it's hard-coded in the app maybe we can find it the last piece um or one of the last piece here is what about apis are there other apis that we missed that we just didn't know about or is there other functionality in the app that could be useful that we should somehow be exploring so just as a recap this is the scan the output of a bluetooth scan on the smart grill and there are two services at the bottom one is an all one service the other one is an all two service or it ends in all ones and it ends on all twos
anyways so the first thing we're going to do when we look for when we go through the java source code using jdx is try to find these numbers because they need to be in the app somewhere so this is what the output of jdx gui kind of looks like i've cleaned it up a little bit but it's really readable java like you can you can read that and you know that for example the device ota is set to that uuid string of ending in all twos or that the device commands in point is set to the uuid string ending in all ending in five ones so this is really useful at this point we have a little bit of information we
know that device ota is the uh all ones endpoint we know that device commands is the two's endpoint and so i ask you what do you think device commands like so you do run commands what do you think device ota lets you do anyone here have a guess on what ota is yeah exactly it lets you update the device uh over the air so let's take a quick step back here the the one that ends in all ones that's insufficient authentication that's device commands the other one is twos and it looks like it does have a it doesn't have authentication maybe we can use the um device ota command to update the device and maybe exploit it
somehow maybe we'll see so uh we know that the twos ends is a ota functionality let's just update it but we still don't know how to send or communicate with the endpoint right we know that's a json endpoint but we don't know what the keys or the values are so again this is the output of jadex i dug through it dug for a place where the ble chard device ota variable was being used and i came across an ota function this ota function accepts two parameters url and shop anyone want to take a guess at what either of those are no
yes exactly yep url uh link to a url to download a file and then sha which is uh the hash of the file that we're trying to download now that's really useful we know what the data looks like um and then if we just follow it down a little bit there's a build message function that will just tell us okay if we want to communicate over bluetooth we need to send it in a very specific format this is json after all so we just have to send maybe a payload that looks like this ota followed by the url followed by the shaw or the hash of the file that we're trying to access but there's one problem
if we try to do an ota try to update the firmware of a device blindly this is how you get a bricked device a broken device a useless device we're not going to do that we need to get a copy of a of the firmware and this is again where the mobile application comes in handy it's treasure trove digging through there was a function it was a little bit more obfuscated than you know just get firmware url that gave you a straight firmware but it's essentially that um we could find we could go to a an endpoint on the vendor's website and download a copy of the firmware so we have a copy of the firmware we can do otas
uh let's recap and see how we could potentially exploit it so just to recap here the alt twos at the bottom device ota unauthenticated we can send data to it the data looks something like this ota url sha we just have to figure out what we're going to send to it how we're going to send a what kind of firmware image we're gonna send to and well we have a firmware image uh we downloaded one over the internet and so what are we gonna do to hack it well we're gonna create a malicious firmware image now this is a little out of the scope of this talk like how you actually create a firmware a malicious firmware image but
uh we'll do that like just pretend like that happened we created a malicious firmware image and then we need to upload it over bluetooth how do we upload it over bluetooth well we have the command that we're using we're using that json string we're going to send it using our better cap tool then we win we hack it or at least we try to hack it that's the goal but there's a problem when you try to hack some iot devices hacking a grill is actually a little bit more complicated than you think this grille didn't actually run linux so it's not like you can just pop a shell so what does it look like when you when
you hack a grill um grills have fire you can start a fire right now if i had a grill and i laid down fire what does that look like it looks like a normal grill you can't really show a fire on a grill and say oh yeah i've hacked that also girls actually have really nice safety features so if you're concerned about your smart grill know that even if someone compromises it uh your smart girl is probably doing a great job at making sure it doesn't explode we tried to make it blow up it didn't work out it's you know it has holes for a reason has ventilation crap so what how can we actually hack it like
how can i show that i've hacked a grille well these smart girls have displays what if we just override the display so that's what we did this is this is the example here uh we took the grill i've wiped out the name but we took the grill put in our logo and that's kind of a hacked grill now this is one example of how you could hack a grill um the what i what i wish we would have had time to do is make a like uh like a troll uh firmware that would just burn your stakes like oh yeah okay i'm gonna turn it on a little bit and then all of a sudden it flares up to as high as it can
go we didn't have the time to do that but we did have time to drop our logo on there so let's do a quick recap here so we started off with a grill and we looked at the wi-fi interface on it the wi-fi interface was kind of pointless it didn't really have anything but that's where we start we start by digging at the easiest layer that is wi-fi web applications if we can find them probably the easiest layer to explore unfortunately our grill didn't have anything useful there we move on to the next thing go on to the bluetooth interface bluetooth interface um we got a little bit of useful information we found out what was available there how
we could interact with it but ultimately again blackbox not really anything that we could interact with send data to that's pretty common got to keep on moving mobile application this is where we have our valuable information this is where we found out okay sure we have a mobile app we have a bluetooth interface the app knows how to talk to it so let's go and use the mobile app the information we got to exploit the bluetooth interface and this is kind of the path you take when you explore an iot device it's important to remember that for a web app yeah you can exploit a web app on its own without having much more information we have great tools there
the problem with when you explore non-web app applications is not having enough information so it's just a continuous cycle of moving forward getting a little bit of information continuing and keeping on going uh continuing and exploiting and that's ultimately what we had to do here we start over and over until we have the right information now you might be wondering why didn't you just start with the android application right like it had all the information why not just start there and the answer is we could have we could have that would probably have been the easier way but that would have made a fun talk would it so that's uh that's pretty much the talk
um my name uh oh yeah a couple of things so we at carve have a ctf running i think the prize is roughly um if the first person to solve it gets get some amazon card i think 100 or something so definitely try it out if you want a gift card or something we're also hiring too so definitely come check it out carver's a great place i've enjoyed it we get to do a cool research project so if you are interested in joining carsystems.teams if you want to find me on the internet again i go by almost json because my name is almost jason it's actually justin you can also find me on my website
sotontura.com uh like the title says root wall messages or rock wall questions anyone have questions go
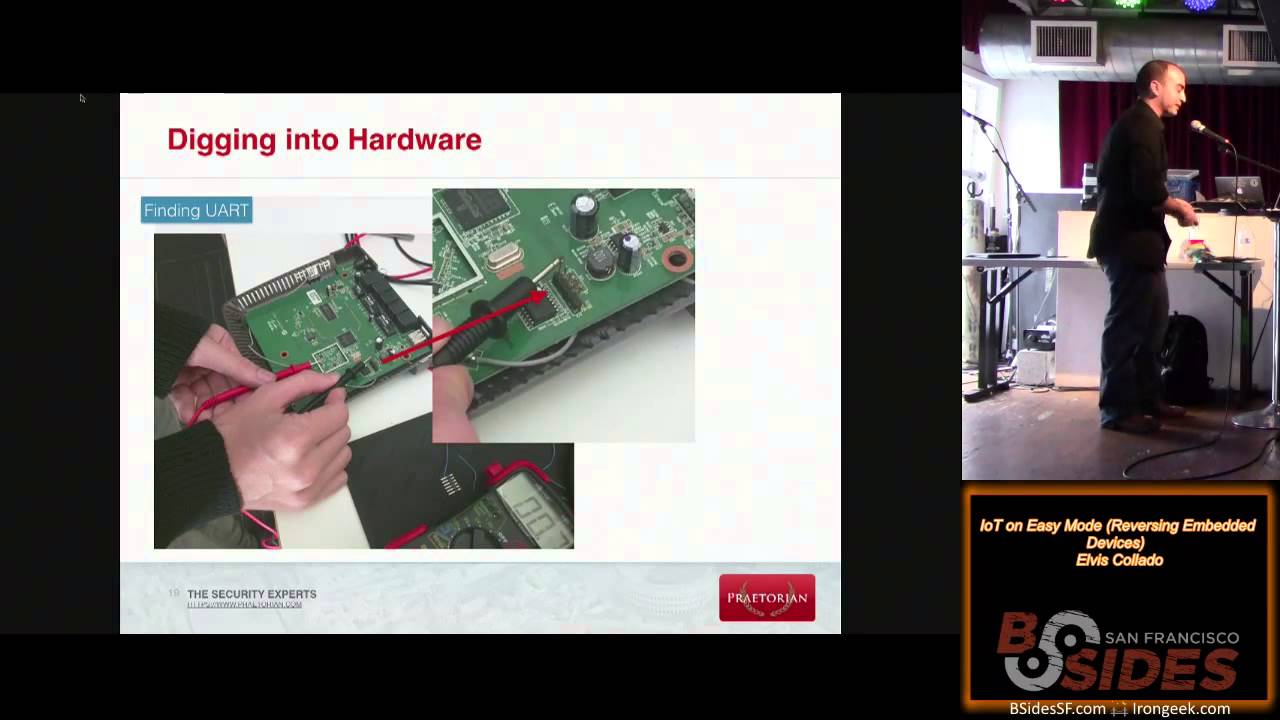
yeah so actually so a couple so the question was could we for this for this grill or i guess in general really like exploring uh hardware interfaces and yeah hardware interfaces are great places to explore for iot devices you'll come across you mentioned jtag uart and those are two of the most common hardware interfaces that you'll find those will give you root access sometimes if you get lucky um on these grills so i didn't talk too much about how we built the malicious firmware but the grilles were built using like espys or something which you know these are pretty off-the-shelf um embedded systems that you can buy so there was a good tool chain that let us
build the custom firmware but we did brick the device multiple times actually don't think that we only got it we only updated once uh we actually ended up using the hardware interface to recover it and restore the original firmware to do it a couple of times oh yeah good um what kind of iot devices would you start with any specific brands and types of devices oh i think this is being recorded i don't want to say brands i don't want to shame anyone uh what types definitely definitely look at routers routers are are great for um for a few reasons one if you have access to a web interface and you can compromise the web interface that makes
exploring the other parts easier so this is actually how i got started so i mentioned the the hotspot uh the hotspot you know compromised through the web app but there also has custom ports you'll come across custom ports that have um that are just like that are riddled with buffer overflows and stuff like that it's hard to find a buffer overflow and exploit it without having any additional context but if you already have root on the device you're working backwards it's essentially you have the you have the binary you can reverse engineer it you can learn a little bit and that's kind of the cycle you learn a little bit keep on going routers are a good place to do that um
if you just want to explore an android or mobile side you can also do that just by downloading android apps off the google play store for um for like iot devices you'll come across cool stuff like that too cool yeah was the uh w ids were they are they the same idea oh good question i didn't cover that yeah so uh the uuid is on the bluetooth interface they're random i said that right uh but they stay they're they're the same for all uh for all devices so they're um uh so it's like a name right uh it's static all of uh all of the endpoints for example for git event will all look the same on every device but they're
random and unique per vendor if that makes sense but not the device itself and device yeah oh no no not device not device just unique per um per vendor or whatever exploit you did on the one grill would work on all rounds yeah on all of this all those same girls would use the same uh would use the same identifier so you can mess up an entire aisle and target right now oh that's a good idea yeah that'd be cool um yeah so you could do that and that's that's also why the you know you saw that there were some generic values on there right so it's the it's everything here in red right those are generic and it's because
better cap can identify the strings they're associated with them and map that whatever's i think it's like 1801 up there maps to generic attributes and that maps to the next value 2a05 maps to service change so that's generic there are uh there are specs that define that
yeah um okay so the question is why didn't we just do traffic capture we did we did we did a bit of traffic capture um uh but i also want to talk about like when you exploit something and it's like just for fun so this was a fun project this was not like we had sanctioned from a vendor to go and hack a thing on their end so you can't like start messing with their back end endpoints for example so i can't just capture wi-fi traffic and send random malicious data to some back in that way but there's also a really good trick on the bluetooth side if you have a mobile app you can also capture bluetooth
traffic coming in and out and that's a great technique too i just didn't have enough time to cover it yeah so if you're using an android device uh you in the user settings there's a uh like there's a there's just a toggle you switch i think it's called bluetooth hdi snoop or something and it'll log all of your bluetooth traffic into a file and then you can read it in wireshark yeah it's it's really cool and then when you look at it it's like okay yeah yeah like this makes sense uh uh this is exactly what it's doing and you can compare it to the app just additional information right uh that's really useful to have
oh this yeah okay how do you keep a mindset when everything is stopping you uh you just keep moving it's honestly it's set yourself a time limit and just keep on going uh when you get blocked this is a problem not only on iot devices but if you're looking at like external networks or internals you're you have a massive amount of data you need to sift through sometimes it's just you just can't get bogged down you just have to keep on going time limits help a lot for that pace
so if you're okay so if you just the question is hardware for bluetooth right um if you're just looking to send data back and forth you can just use your laptop you can use better cap it'll send data for you like i said it's there's not enough time to do like an actual demo like you type in this command you do this thing to send data but better cap is really intuitive it really is the to send data you do ble or dot right followed by your data it's pretty straightforward and you can just use your normal your normal laptop there uh ubertooth is great if you're trying to sniff traffic capture it over the air but in this case
we're not trying to sniff over the air yeah go ahead all right last one i promise uh have you come across one of these devices that was smart enough so that would detect insufficient authentication limitations so if you can't enforce it yeah so um so there's a so the question is have i come across devices that will do rate limiting or some kind of protections against uh authentication so there's a few things here one if it's if it has an unauthenticated point so like this bottom one here it's not gonna do any rate limiting there you can just connect to it right if it's an authenticated endpoint uh yeah some devices are actually really really smart i mean these are uh the
bluetooth interface is typically written using i know like you can write you can write your own bluetooth how the authentication process is handled pretty much uh you can see that an authentication result failed um so i don't think we've actually seen one that will like just drop you uh but we have seen that like the the bluetooth interface itself will do some kind of rate limiting like you can't just spam it indefinitely um it'll start to do like okay here's a timeout you have to wait a little bit of time for me to process it or whatever yeah cool thanks everyone for coming thanks for listening i'll be around if you have any questions [Applause]