Cyber Kill Chain From The Eyes Of The Red And Blue Team

Show transcript [en]
hello yeah better now thanks uh shout out to Rio and Paulina for this amazing security conference for the second row for second year in a row and thank you for having me today I will um talk about the Cyber kill chain but Through The Eyes Of The Blue Team and the red team um yeah the normal disclaimer so U please try to use them all the techniques or the techniques that the Techni and tactiques that I'm displaying in this presentation for education purposes and uh we all know that cyber security is we have heard today volatile uh changing the landscape quite often complex so uh there's no one solution fit all so please do proper Dy diligence
proper analysis in order for you to be more protected uh so this is a uh agenda in um in a quick sweep um we are going to understand why there was a need for cyber security kill chain uh what were the key benefits and then we will go one by one on those phases to understand how a teers are uh leverage in those phases and how blue teamers can protect themselves and uh be more proactive and in the end some closing remarks um something about myself um I've been in market for more than uh 15 years in cyber security for at least 10 um quite focus on the information security side of it not specifically on the cyber
security because sometimes they are uh used interchangeably but they are totally different um I consider myself and this is my daily task or daily job uh cyber threat analyst and I'm very found of those reports uh where all our security researchers go through and uh granularly detailly display all the tactiques that the different tax are using some uh recommendations and some uh proactive measures that uh companies and organizations can do but also people um the occasion blue team or red team of course but no more on the concept of this new trending thing that that has come the purple teaming uh which is uh something that I'm quite fond of uh and lately the I'm I'm tipping my toe on the
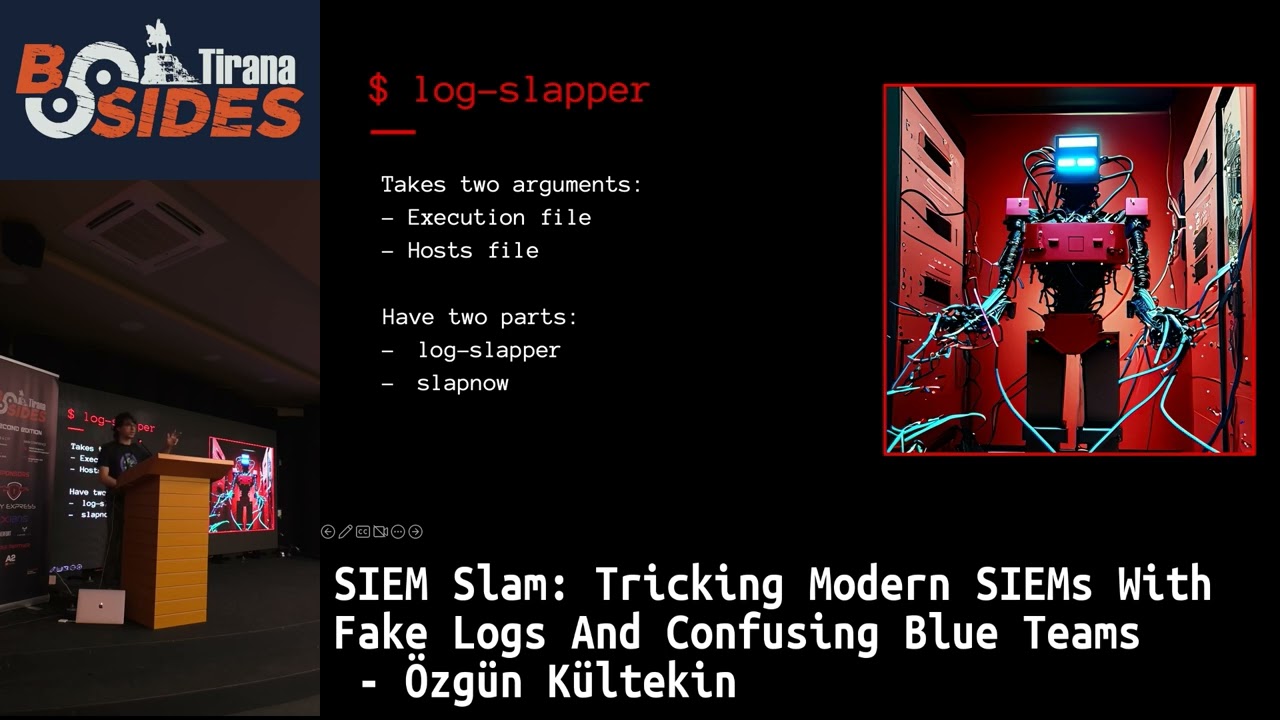
digital forensics it's quite interesting trying to understand so when those postmortem uh incidents or activities are handling how malicious actors or even redeemers have left quite a lot of footprints here and there and if they are not aware and one of those example amazingly was the log uh deception techniques so quite helpful I'm going to follow it on it uh but then I'm um quite uh let's say a sponsor on the continuous learning mindset so you you should always always learn more develop more be up to date because we have said that technology it's moving quite fast and we cannot uh be behind so yeah there are some Locos on my certification my achievements many
more to come of course but uh something that I always say even to my colleagues uh when I undertake a certification this would be my last but you can see there are a lot so yeah um why there was a need for cyber security so sorry uh cyber kill chain a new framework that let's say gave organizations the upper hand on on on red team uh um activities so uh yeah I split it in three major let's say um groups or category throughout the timeline of uh of previous technology evolvement um yeah it's it looks like a a triology of Lord of Lings but uh um I want to group it more on the 20s the 20
years 1970s and the 199s where there were the dawn of cyber security we had the we had uh development of farall the ipss we had uh all those companies implementing some kind of security because before that they had just a modem you could log in you were in in the infrastructure but yeah they uh said we need to do something they put some walls uh in order to protect themselves but also there was the time when some of the earliest antiviruses they were based on signatures hashes like basic stuff in order to detect Malicia uh intent uh and then we moved to late '90s and uh early 2000s so we have the hacking groups the
developer hacking groups um they were organized uh they were well developed and uh well informed uh what the threat the threat leg Escape was and they were leveraging this knowledge in order to infiltrate environments hack viruses and worms and yeah we have the uh devel the ra the rise of the first warm in 1988 if I remember well cuz my research went quite quite broadly uh but then we have the mid-20s so we have this new breed of cyber attacks the um APS the advanced persistant threat so and beside everything that they are but they are highly motiv organized and highly persistent so don't just think them someone in in in in their mom's the first floor that they are in
the dark but they are heav heavily organized and they have rooms they offices they have HR and uh yeah sometimes we have heard also those names like cartels of huging groups which is crazy enough so um what were the key issues the companies were facing back then so the landscape was quite complex so with uh we were talking about the time when there was a boom in the internet so everyone wanted to go online uh public on website public they uh they research and everything so everyone was accessible from everywhere so the the thread landscape was quite complex and companies were not able to follow uh and how to protect themselves so there were also a lack of understanding so how
an attacker was getting in by just getting some notification that oh we are hacked okay what we do now uh and then we we had more an approach of reactive so when the incident happened uh organizations and companies were taking some action so oh we got hacked let's do something um then we we had let's say um unorthodox incident response so the incident response were let's say not organized not standardized so everyone was doing something ad hoc uh in order to prevent some or to take actions uh because everything was reactive U then we had that Reliance that I said on traditional defense so we had companies that ring oh we have a firewall we have
IPS I'm secured uh but those IPS is those firewalls were relying only on some basic hashing basic signature which are were easily and every now today knows that they are easy bypast uh and then yeah they can get the upper hand the they can give the upper hand to red teamers and Hawkers uh we had quite a lack of coordination between teams so everyone was uh not organized uh working on silos everyone was doing his own thing with the development of devop teams uh we had also some challenges related to Shadow it so even organization they didn't know what they had because everything was up to other uh teams to manage uh we had SE silot
security tools so no integration no coordination between them uh and a team there was manage in the email security there was a team manage in the farall there was no communication between them so uh there was quite of the challenge uh and also something that uh we see I see actually today companies were focused more on compliance other in security but not as a business decision but compliance as an action for cyber security like mitigating to compliance which sometimes is quite challenging I'm not saying the compliance is bad it's a great but not the answer for your cyber security threats um so yeah that was the the rid of the Cyber kill chain um in
2011 uh Lo at Martin was the defense contractor um published this white paper I'm not going to name the name but publish where they presented the Cyber kill chain uh and it was a map that they delivered to everyone Security Professionals that they could use to navigate throughout the whole life cycle of the attacks so they know oh this is what they are doing maybe I can take some actions I can be proactive it's the same approach when you play chess if you know the moves of your opponent two or three before then you can mitigate yourself and protect better so there were um seven phases cuz seven phases uh that the Cyber shade introduced to uh
the world uh that are recognisance weapon sorry weaponization delivery exploit installation command control and actions so with this map in hand um companies were gaining some benefits so they had an understanding of the attack life cycle uh so they could understand indeed how they get in because cyber security is not just one event is a line on events uh that happen before you get hacked or you get the their on somewhere um they could prevent uh or Implement some early detection on the threat so during that reconnaissance phase or during that weapon sorry uh weaponization we are going to talk later but through the delivery which is the first impact that the red teamers have
with blue teamers and anymore so they could um assign resources better so first it was Implement firewall we are fine but then we need an NR solution we need an IPS we need an email security so this gave organizations some understanding that indeed we need some other resources to be assigned better and more proficient um it gave a benefit of com comprehensive incident response uh by by that I mean that um companies and organizations were performing proper incident response plans they were not saying oh I got hacked maybe I will call someone to fix it no they had proper templates in how to handle this kind of incidents with talking to the law enforcements uh triggering the business
continuity plan talking to Legal handling the marketing so everything was coordinated uh through this incident response playbooks uh threade intelligence which is let's say the Keystone uh advantage of organizations today so someone in the world we we heard the panel today that someone in the world at the moment that we are talking is getting hacked so if that information is shared with someone else he can take proactive action and protect himself so um we had the oici approach on attack so it's more to understand the whole uh life cycle of attack as I said it's not just one event but is a multi set of events that result in ransomware or any other data exfiltration any other malicious
intent uh collaboration and communication and also a reduced attack surface because if organization proactively take those action they minimize the uh their exposure and they improve their security posture which is quite advantageous and this is what we need to do today um what are red teamers and blue teamers um red teamers are groups uh and I'm talking about ethical red teamers not the bad ones but uh red teamers that want to help organization be more aware trying to test the security control so they can take actions up front so what they do they simulate the real word cyber attacks so they can make aware companies that look you have deficiency here and there we are we use them to get in so please fix
them so they identify vulnerabilities and weaknesses in the system they disclose that information to the companies they don't use it in order to leverage them in some way or to run some of them to yeah run some of them in a way they test the efficiency and also they um explore potential new attack vectors like social engineering or uh USB dropouts or any um third third party supply chain attacks or any other uh techniques uh as a blue teamers which are usually internal to the companies but sometimes can be also outsourced uh they defend this is the the other side of the coin so they defense uh from this cyber attacks and they monitor analyze
the whole network and they detect an response based on playbooks or a sore we saw today it's quite important in order to minimize the noise and to handle those let's say level one level two incidents that can take much time of the security analyst and also Implement security controls bless you um so what were the phases of cyber kill chain uh and how they were leveraged by red teamers and blue teamers so let's start with so the conance is the phase where um red teamers contact their research uh and planning and how to know the target better uh how they can excuse me how they can meet their objectives so what they do uh they go online because
everything is a line nowadays uh and we have heard about those techniques the active and the passive scanning so on the passive scanning there's no interaction so you are not aware as a company that someone is doing some research on you so they go through social media they go through to the company website they go to um third party that you interact with and they gather all this information and something that is being news quite often today is that third party integration because you might be safe and you have implemented all those mandatory requirements but your partner that you are working with has no uh protection at all and you are trusting him so if that
information comes from there you say oh it's fine I'm going to accept it so that is something that redeemers are doing today uh they go through the metadata analysis which is data about data so they go in the website of companies download any PDF that they have there like organograms or uh the new disclosure for the financial statement everything and they go through that information to see what kind of office they are using what version uh if it's office or maybe some other uh tool that they're using what kind of PDF they are using IF it Acrobat Reader seven or eight not sure what the version is nowaday nevertheless so they go through all this uh and it it it might take
months uh but it they they have quite a lot of information out day about companies and how at least to approach what can blue teamers do so it's more like they somehow are aware or not aware because as I said we have this passive and active so what they can do they cannot be more proactive let's say so use thread intelligence uh which is quite important because as I said every red teamer go through this recog usance phas one time before your organization was attacked by someone they had interacted with your landscape with your IPS with your website so if you have that information the domain they use the IP that used or any technique they use
maybe you can use it up front and create proper security control so proactively protect yourself so this is what blers are doing they have feeds of threat intelligence they download they grab those ioc's uh and they use them proactively um what they do they do also security training but security training not on that mandator thing that oh you have to fear here but with proper exercises they sit people in the room and they go through an action actual sorry an actual hacking scenario they sit them and they urge them look click here man and they click to that and they get compromised and get the pop it's is the control environment it's safe of course but this is how you can make
aware people that this is the impact they do if you don't take the proper analysis or the proper let's say understanding if there's an email that you don't know from where it's coming or this is fishy or uh I I remember Rio when he was talking three days ago he was saying that in for fishing scams in Albania there's a lot of uh and CH being used which for albanians we don't use it through emails so if you see something like that be aware that this something might be fishy so this is the kind of trainings uh that blue teamers do in order to implement uh to to protects proactively but also we have the edrs
the web application firewalls all the standards and traditional security defenses I'm not saying that that don't work uh they grab all those low hanging fruits which gives Security Professionals on The Blue Team inside some more time to investigate those that are more enhanced more uh complex um on the second phase the second phase uh as you see um there was a line that says the red teamer are affecting or are interacting with the blue teamers but on the weaponized phas there's not that line so there's not much interaction because what the red teamers are doing right now are gra grabbing all that information correlating improperly trying to there there's no interaction with uh with the organizations or with
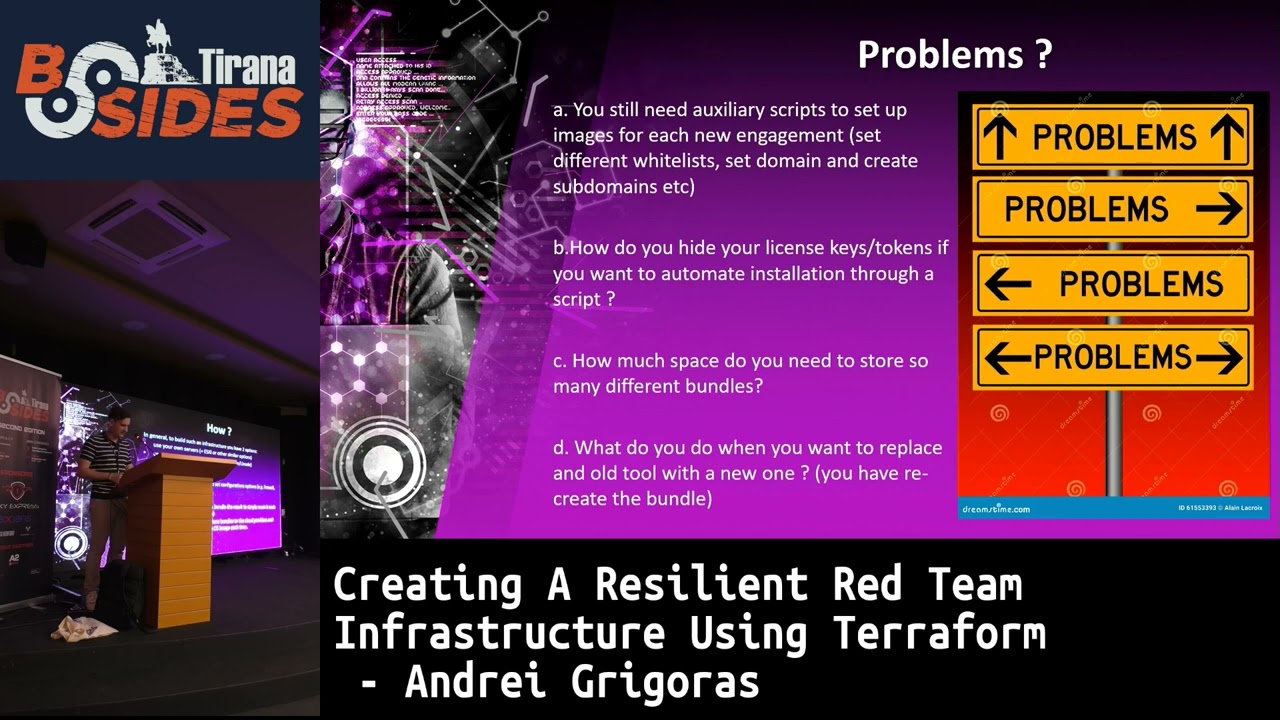
the blue team so they are developing the mware uh they use or leverage all that information that gathered from that analysis or the cense like the version of the Adobe Reader maybe there's an application on the website that is vulnerable or there's a JavaScript plug-in that has some uh vulnerability that they have not exploited or they even find a zero day you name it so what they do uh they build their structure they build the fishing template before sending it the any anti forensic techniques and I've used quite a lot so um I know that they are doing it uh persistent mechanism and they build a resilience attacking framework uh infrastructure um that resilience is
something that nowadays um security teams or um red teamers are using and leveraging quite often because we know that there's if there's an IP that's fishy or there's a thread Intel that says that Please block this IP then the whole infr they are using it's going down so it means that they are not doing their their job which uh it's not beneficial for the red teer so this is why they perform those resilency they just change an IP and the whole back end is the same but the front end has a different domain is have a different IP but this does not mean that the blue teamers should uh sit and and wait oh where where you're going to come so they
can do some things up front so the Implement and security controls based on technology but also based on analysis and uh something that nowadays blue teamers are using quite often is the user Behavior Analysis so why we have those Bob Alice why Alice in HR is using po shell it never happens it should not be the the case so um this is some of the scenarios that blue teamers use in order to proactively detect or even prevent themselves uh security awareness I said Network segmentation is something quite important because it gives an opportunity to organizations to stop the bleeding when you are hacked just cut your hand because you can you can survive as a business without that so
move forward try to focus on resiliency and business continuity don't focus on oh why that antivirus didn't work doesn't matter focus on business because in the end of the day you need to make money as a business or organization you need to not focus on that specific threat or that specific actor or that specific tool um credential hygiene is quite important because um we have seen before domain admin users uh log in in PCS to install a printer when when when you see that case then there's a hash of that domain admin in that PC so when that PC is hacked then it's game over that have that uh access you have also secure development life cycle that shift
left approach uh that businesses are doing because uh I mentioned the develop the devop teams that were developing everything they were using uh quite a lot of uh libraries and tools that were vulnerable so they were not aware because they are focused on functionality they are not focused on security it's it's okay but we as a security team or professionals we need to train them so the security development life cycle implements some kind of controls before everything is committed and moved to production uh and we have thread modeling so once uh there's an application being developed or there's something that has to go uh in the production they perform proper thread modeling so what is the impact if
something happens to this uh new asset that is in the in in our infrastructure uh the host the servers the applications everything so these are some of the techniques they are using and then we move to phase three and now it's game on so red teers convey the mware and then send the mare to uh the Target and they use different techniques and different methods so we have this uh fishing email and uh there are something to be cautious so there are quite a lot of um indicators especially in periods when for example after summertime so after summer you have a lot of fishing campaigns focusing more on oh your PC has to do this update because it has
been offline for quite a lot of time so you need to click here or whatever or for example um you need to download this latest and greatest plug-in that we developed once you uh away from vacations because they have already done this Recon usance because they scra the social media they saw your pictures uh they saw that when you are coming back you need to do something um focusing on that information so they leverage it red teers are quite smart people and as I said persistent um so what they do they uh over weaponize documents like PDFs uh USB drops we had that example uh from axians that they said USBS they use USBS uh keyboards and mouses to so it's a USB
drop scenario the social engineering approach maybe they send a link you are fan of I don't know this football team or that football team so you need to take ticket or if you finish the survey you are going to get the new Champions League ticket doesn't matter so everything uh is there and also supply chain attacks as I mentioned uh they don't hack you directly but they go through one of your partners and uh they know that uh you are going to trust them because you do business every day what blue teamers can do at this stage for besides um the the common the the usual techniques uh they can increase let's say their control in what what
applications are permitted to run don't let any kind of unsigned un um yeah unsigned exe running on your infrastructure even though it might be a custom application built an internal certification Authority entity so it can encrypt any kind of information any kind of file that runs inside your uh excuse me inside your infrastructure so at least you can lower let's say uh the risk um limit USB devices even though there might be the that case then yeah there are some USBS that can be um USB keyboards that can by the technique so block out runs Network segmentation leaks privilege is quite important trying to block users to do what they need to do in one of those machines as I
said uh don't tell the admin domain administrator to install a uh a driver of a printer in in one PC because it's crazy um and then we we go to the fourth phase uh I'm mentioning those phases because for every every one of those phases where the interaction is between the blue teamers and red teamers that have been a scenar scario when those controls have been bypassed so even though the blue teamers on that phase three implemented those controls that have been a case where the red teamers had bypass those control so they move to the next phase the phase four uh where the red teamers exploit the vulnerability and they gain this initial access and they can use a lot of
techniques uh one of the most us used are those malware injections especially for fileless attacks where there's no file dropped in the dis uh but everything is is running on excuse me on on the memory so the uh we have the D reflective uh scenarios we have the process hollowing we have quite a lot of techniques that interact directly with uh the memory but not on the disk and red teamers know that leverage that and uh try to gain initial access but you have also zero days exploit uh you have client side exploits and that information was gathered during that recognisance phase the Adobe Reader versioning that we had we were talking about but also as C injections um in
your web application for uh sorry web application uh where you have all the data of the clients or um any service that you want to advertise in the world buffer overflows but also Wireless attacks so we have drive by uh scenarios where malicious actors have their antennas they grab or they log in in your guest Network and they can easily uh pivot to your internal infrastructure and to the damage so what can Mal uh plers can can do to protect themselves one the most obvious because in the end everything and we are talking about Windows due to the fact that it has a very strong market share on endpoints uh monitor the windows API so uh once
during those actions the red teamers are going to leverage those windows apis in order to create a new process or to inject something in the memory or you name it any kind of techniques there are a lot I cannot go through all of them now but um they are leveraging now uh due to the fact that they know how redeemers are performing those action uh they do quite a lot of behavior analysis as I mentioned don't see when you see Alice from HR running power shell something uh must be must must be wrong uh patch management is quite important for uh blue teamers during those phases because it gives them uh some upfront protection uh for vulnerabilities not
only when someone externally disclose that information to you but you take proper actions and running the the infrastructure or your or on your end not waiting for some someone else uh they Implement Security in point and also go through the OS and application hardening so before having that that asset uh being connected to the network they go through all those um best practices to limit the exposure of any kind of service like services that are not needed block any ports that are not needed Implement firewalls beside the EDR one that are not needed so anything that minimize and hardens the application or the US uh and then we move to more on that uh reactive side of
it so because yeah you can be proactive you can protect yourself but then you need some kind of uh reaction so the incident response plans that I mentioned uh are being leveraged quite often because companies focus on the business they need to continue doing their business uh and they Implement those playbooks in order to be more Pro more active and continue performing those business even though there's an incident uh and then yeah we have security testing that is something that companies are building right now with uh teams internal teams that run pent test at Red teams not only external ones but internal ones that can help companies be more aware and we um more security
focused so yeah we have uh phase four um as I said there are always scenarios when redeemers bypass those controls and they move to phase four which is installation here Redeemer try to install persistency so um some of the persistence are trying to be playing playing sorry play playing with the names of the services that are legit for the machine like that uh CVS CVC host that you see always running always managing the application they they tweak a bit and make it SCV host so at the first glance uh with all those logs from Splunk or whatever SE it might uh not cut your eye but it's there so if you have that information based on the
thread intelligence you can build the proper security uh control rules and uh protect yourself uh we have register manipulations they use we have link files that they create you name it but uh one of the most uh abusive part is the code signing so what they do is try to leverage um certifications that are by spoofing other well-known companies that have digitally signed certification and they use it to digitally sign the malware because the company will trust it and run it and then they will have persistency but they use quite a lot of techniques like the anti- sandbox in the root KCK memory manipulation and you name it so on the blue side of it blue blue themers can
can do quite a lot of Tool uh quite a lot of techniques can take advantage of quite a lot of techniques to detect them to detect all these actions so one of them is using deception technology so this is something that is is increasingly being used by companies nowadays so they uh build this honeypots or the traps around the network where attackers let's say have access they gain privileg access route or you name it but they are being monitored they are isolated they don't know that there is a deception or there is a honeybot so it's beneficial for the blue teamers trying to understand what they are doing what they do what services they spawn which
register they touch what files they create anything that information is gathered through those um deception Technologies which is quite um yeah increasing right now uh the tier access control for the device manage as I mentioned the domain admin not not installing printers but also forensic is something that is gaining quite a lot of traction so uh they have on live environment forensic tool running in real time trying to grab because we we we said that red teamers use fileless mware and the ram being memory sorry being quite a volatile um storage it it formats it s it changes quite often so if there's some digital digital forensic needed to be done it's quite late if the machine restart or uh
it is the memory is overwritten so they use these tools when the machine is live and they gather all this information we have Yara rules nowadays it's gaining quite a lot of traction in order to detect this kind of malicious intent from uh the red teers excuse me and then moving to the uh command and control the command and control phase is when the mware open a Channel of communication to the infrastructure that the reder Redeemer created and they remotely manage the the machine or the victim in order to perform any kind of uh objective that they want to do um some of the techniques they use is domain fronting which is uh the domain the name
of the host you use leverages CDN infrastructures in order to hide themselves because companies trust those CDN and many of uh the cloud providers use nowadays like Amazon Google but yeah they are minimizing day and day but it's still there they use the domain generated algorithms where you have those big long websites with 65 uh strings uh in order to access something externally uh and it's it's quite use used by the red teers to keep uh the persistency in the environment but also uh as a data exitation because they can base 64 that information and then on the other side recollect it and uh decode it and have all the information they wanted um yeah they have flux networks fast
flux networks where they change the IP and they leverage the bot Nets environment so that they have already pre-built uh they have encrypted tunnels so it's quite difficult for blue teamers to decrypt that information if if they don't have web Proxes uh as a SSL decryptor in the middle uh they use this uh dation techniques based on that information they gathered from the recognisance so maybe uh in the social media they saw that there's a job posting for someone that you is uh should be known to semantic and point so they know that the company uses stic and point so they leverag it information to create the evasion techniques specifically for the tool and um what blue teamers can do um some of
the most important uh information they can Leverage is thread Intel and the that thread Intel can be used for that BNS in calling uh where they let's say drop like in a black hole any kind of well-known domain name IPS that they see from uh internally of the company trying to get access uh to the Internet so they use this information to start some kind of uh incident respon or analysis because the DNS calling is well-known domains and IPS that have been predi defined that are malicious uh they use rules as we said uh they filter Proxes for they use filters in prox for uncategorized domain so anything that is not uncategorized it's blocked there
less reders use archived domains that are based on financial and medical which it's by low not decrypted nevertheless uh something that can minimize let's say the the risk they perform threat hunting which is something that it's quite uh often being used so they even though the controls failed threat hunting is something that yeah maybe we are going to see it later it's quite important for uh companies to follow uh anomali Behavior as as we said forensic as I said trying to search for outlier so now red blue teamers up the game so they don't focus more on that signature pattern or on the trigger that failed uh to detect something but they go more on
the statistical analysis so what is an outlier for the behavior of this host or this machine or this user and they continue to uh follow up with uh a proper investigation and as we said we had uh we have honey Poots and uh honey Nets in the environment so coming to the last phase uh where red teamers they accomplished their mission goals they uh they maintain persistency they are there they are talking to the outside world so what they do um they move Lally and can use different scenarios so uh talking about active directory you can leverage any kind of hash that is um safety in the memory of that machine you can use caros thing
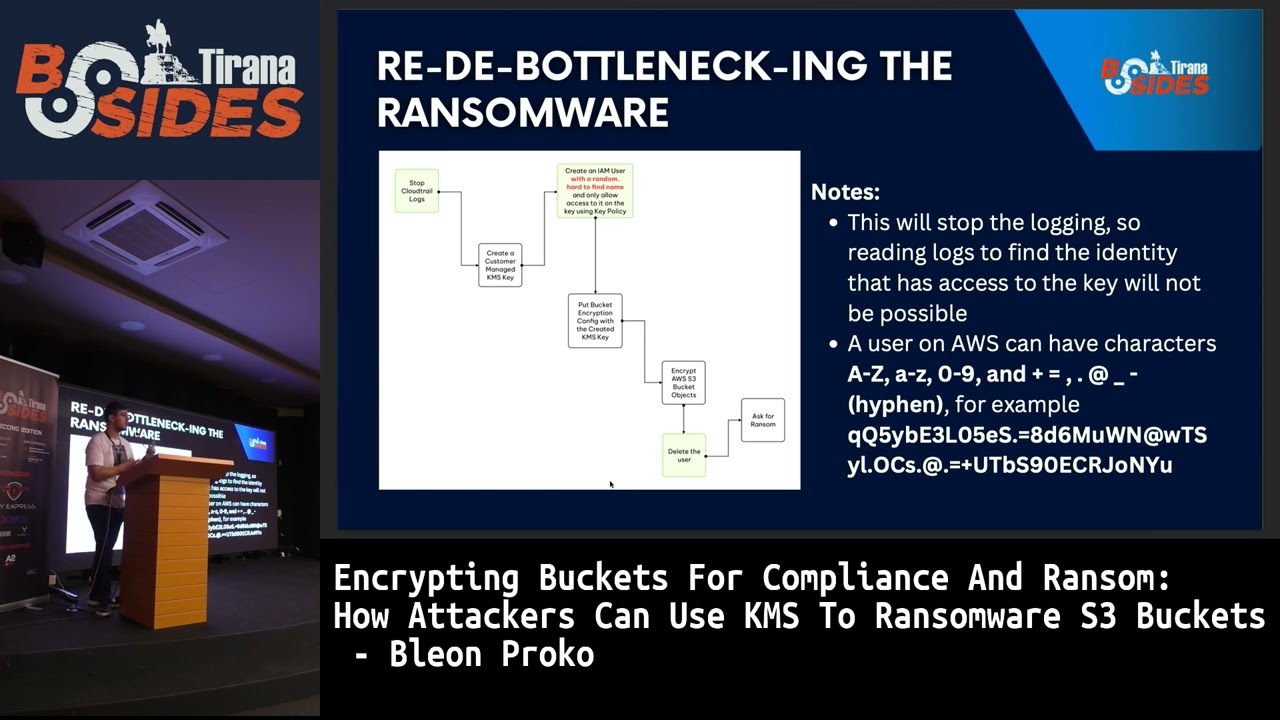
which is yeah quite a vulnerability being used use nowadays but it's not avability uh it's something that yeah you cannot do much but maybe you can do some uh lateral movement based on um that protocol uh they do data exitation through the those domain generated algorithms uh they try to cover their tracks they try to um disseminate logs in order for blue teers to get confused what's going on uh is this machine or the other machine affecting me so they performed in Al of service if this is one the targets or even the around somewhere they collect they also uh collect credentials so what the blue teamers can do at this stage let's say they are quite advanced in the
infrastructure so they need to trigger those dis recovery plans which is quite important for companies and the incident response plan playbooks uh how we handle one scenario on another how we handle email compromise how we handle run someware any kind of uh playbooks that they can come front up front front and they can determine as a risk uh they need to follow at this stage at this phase um they leverage cyber Insurance uh they they Implement secure backups offline secure backups so and they test it oftenly uh data loss preventions and digital forensic but also more on the governance side of it they uh play a lot with uh tabletops exercises so scenarios where something can go wrong what are
the actions that someone has to take War gaming is something that blue Demers are using now now days in order to improve their security posture so there's a lot there's quite a lot and uh um it's it's quite interesting because blue teamers and red teamers are never stopping uh and quite challenging uh if someone wants to uh yeah do this for for for for living let's say so uh I like this next one we say that working in infos is not a stress at all but uh it's it's it's a stress when you start talking to your cat and ask him how can I start hunting so but yeah it gives also some satisfactions because you can
take part of this amazing security conferences meet these amazing people and the yeah Network so uh as a closing remark um cyber security is always an ongoing battle it's a never stop even cyber kill chain nowadays is can be considered somehow an upsolid framework because we have the unified kill chain which includes any some other techniques and itics but still it's a good starting point for any companies that want to let's say improve their security posture um there are a lot of Frameworks unified killchain MRA n t you name it but at least you need to have an understanding and these are some of the key takeaways for that I want to leave you know your
environment know what you have internally and outside uh we have companies nowadays creating social media policy so training the the users what to post what not to post what kind of emails they need to use in order to register to those social media um so know your environment and train your people and then hope for the best but prepare for the worst so uh I hope you never get hacked but then you need to be prepared when something bad happens because um I like a saying it's not it's kind of let's say sensitive right now but worry during peace time because when it's time for war yeah you need to act uh and something important important that red
teamers must be right once but blue teamers should be right all the time so with that thank you very much I hope you love the rest of the conference