Would You Like Some Honey With That?
Show transcript [en]
alright would you like some honey with that thank you very much and thank you for being here after lunch break I hope you left a little bit of space in your tummy for just a little bit of honey and probably some of you will be very sick after that and don't want to hear the word honey at all for quite some time so Who am I just very briefly I work as a security engineer at a company in Germany called dot if we are doing mainly software for text consultants so if you've never heard about us and you are living in Germany chances that actually your statement at the end of the month was printed by us
are really good a short disclaimer that I need to say my views my views on my own and whenever I'm using examples I'm not really saying they are good or especially bad they're just examples and the mother show disclaimer because we have the earlier security our honey things generally security through obscurity and security through obscurity as many people will say me included is no security at all at least not in my opinion but in the case of honey stuff it really works better the fewer people know about it so you're not really basing your whole security infrastructure and honey stuff at least I'm hoping you're not so it's just an additional form of an early warning
system and as such not really security through obscurity in mind or as we could put it first all the fun stuff you talked about how to stuff which is kind of not what I'm doing here but I'm talking about stuff before we get to things we have to look at the traditional honey pots they really look like a vulnerable server at first and it can easily become obvious at a second glance that's not what I signed up for oh that's not a real server but by then it's too late because you already glanced at it or you already have to contact the honeypot traditional honey pots come in various stages like from low interaction too high interaction and
a low interaction honeypot probably just uses an IP address on your network and you can ping it you can connect it sort of it supports the services up to OSI layer 4 and once set up and running they do not require a lot of maintenance these are honey pots that are not advertised in your network so there's no legitimate service on them so whoever connects to a honeypot actually is considered to be an attacker because there's just no sales running their meeting interaction honey pots take it to a slightly higher level because they will simulate services like FTP or telnet and they also will allow an attacker to connect to those honey pots and leave their credentials that
they wanted to use and maybe look at the files the attacker wanted to have and they are a little bit more maintenance because you have to look at them and you can put a high interaction honeypot on your network very often these are machines that are connected to your back-end so high interaction honeypot just think about it is a really heavy monitored machine they really try to find out what the attacker is going to do but the attacker that connects to that machine won't really be content with a cat picture they want the real stuff so you have to connect it to your databases so they get some real data as you can probably see these require a lot of
maintenance and monitoring and this means that high direction honey pots are for very special places there are honey nets as well and I'm briefly touching onto them just in a minute but all those honey pots have one thing in common once you connect you already triggered an alert and this goes so far that when talking to to another machine on the network I the first thing that I need is the MAC address of the machine so this connection typically comes from the switch if it's a segmented network but this will trigger and already because the machine the honeypot really sits in the network doing nothing it's kind of like what we want to do when you're money two of
those things do nothing and before I come to the honey nets why is honey stuff important or why do I think honey stuff is important so detection is the new protection is something you might have heard the funny thing is that companies and enterprises are really really good at protecting the perimeter because that's what they have been doing for years and years and years but the funny question is where the heck is my perimeter nowadays because people bring their own devices that connect to the network I've got cloud services that deal with my data I've got partnering with others and so to define where the parameter is can actually be a daunting task so it's
easier actually to well easy and it's not easier and bosses do not like to hear that you should really assume that you have been breached and you want to detect that stuff and the honey pots or honey stuff is one method of doing that and I really need to stress that no honey pot or honey stuff at all will prevent an attacker from attacking you but you will know about it in instead of having of knowing about an attack a year after it has happened you might get Intel about the attack while it is happening and that is can be very important so the first stage that an attacker does usually is when they have
a foothold in your network they will try to spread out without a lot of noise so the group if you're on Twitter you probably are familiar with him said and many other people have said that as well you only need one exploit and once you're in you move laterally so whenever one mission is breached and you're trying to find out more interesting machines to attack there's one problem in modern networks if you've got a really nice amount of network you've got the friend internet here because I basically got sick of the red internet that is evil so I made it a little nice and you've got different networks someone's like the orange the green the
blue and you've got second segments you've got firewalls the firewall also has an IPS IPS and the reason why I combined those two is because most major vendors will do that when this purple sauce fire they put the whole source by intelligence on the NSA so you probably will look at the network traffic when every crosses network boundaries like from orange to green or green to blue but what you usually won't see is if somebody managed to reach your first file or whatever and this has compromised that machine and the sitting on this machine and it's just spreading out without touching network borders how big are the chances that you will miss the connection from the internet to
that server and I would like to say very high because who didn't notice that this machine got exploited so it's easy for an attacker to peena-pod if you've got honey pots and they get touched then of course you get another and you know there's somebody there a very brief excursion to honey nuts I've put some links in the links slide yeah about waterworks in the Train these are two projects that really took the concept of honey pots to another level because they build whole networks and fake water works for a small town that could be attacked from the internet because they wanted to know what would an attacker do how would they many plate the pumps how would they actually try to
break stuff and the same for the honey train this was a model train nobody knew it was a model train but it was on the internet it was a big story about six or seven weeks ago I think because they managed finally to derail it which for a model train is okay but in the real world [Laughter] when we are talking about honey stuff we are talking mostly about decoys and deceptive strategies and that's an asymmetric relationship between an attacker and the defender because the attacker probably has all the good stuff on their side and that's that as a defender we've got a really good advantage that we rarely take use to make use of and that is we should know
our networks better than unfortunately you know the boss of the NSA said that there is a knows networks of companies better than the companies do themselves but let's just assume you know get work and you can tell the decoys from the real machines that take account until they connect now that we've talked a lot about traditional honey pots let's see what else we could do to have these kind of strategies and how we could get results when we are putting honey somewhere else so how do we get an attacker to actually attack our honey sites or whatever we do we just have to think like an attack at us and if we've got a website we just have the
robots.txt and we put something in there like this allows - besides might help dot ppt I hope you are familiar with our robots.txt that is for the Google spiders and cameras and it tells a robot where to go and where not to go if a human looks at this and somewhere there's disallows leche et Cie past's WD password the password file they will go and check it out human attacker might check out those sites that are disallowed and of course you monitor those and send an alert if somebody touches the file a concept I really like is the concept how many people if you are well probably wherever you you are from you've heard about the CEO fraud
where some social engineers really get people to pay lots and lots of money by just pressurizing them into it there's a company from the town where I work in Newark who lost 40 million last summer by that basically it works like that the boss called somebody our rights and human says I'm in foreign country X and I really need 40 millions now hand them over to me probably not that easy but that's the the gist of it so if you want to see you whether somebody is trying to contact employees at your at your company then just create a fake profile about you for those people on the same or LinkedIn using an email address that
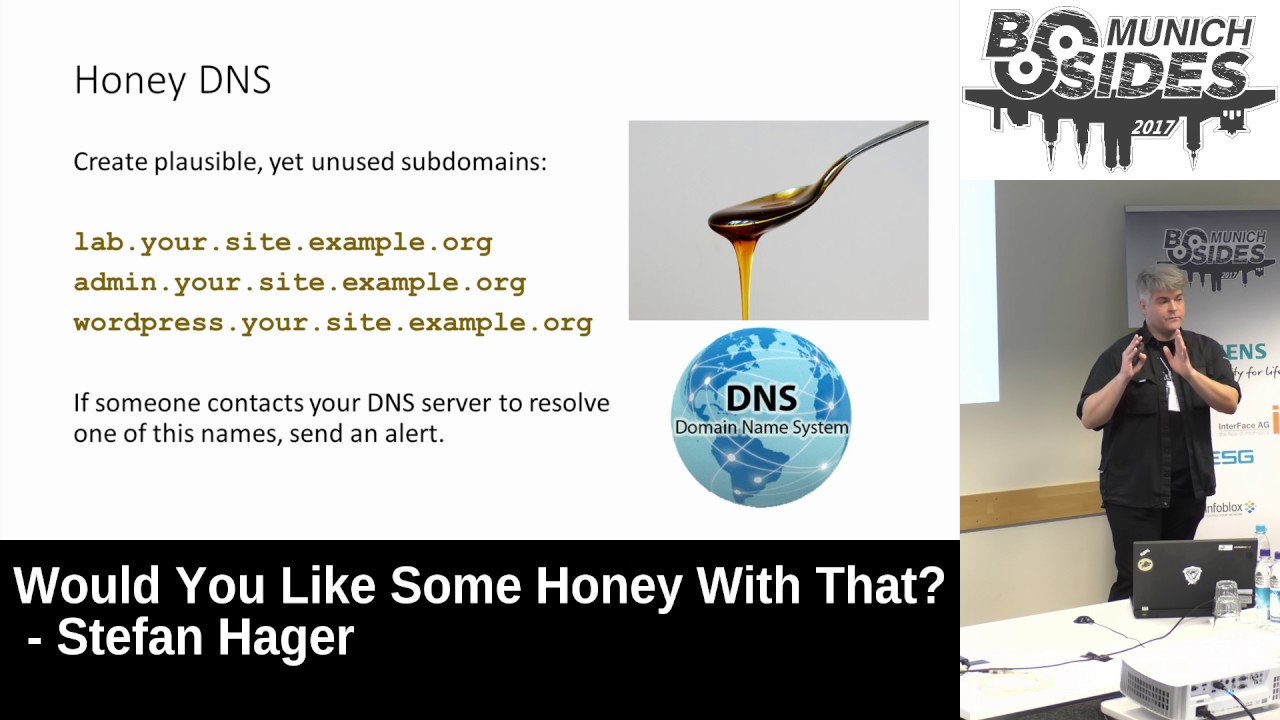
fits your company and give them a phone number too and format both to your security team as your security operations center because whatever calls up that phone or whatever sends them an emails either somebody who's a really aggressive marketeer or someone who's looking for an easy target for social engineering you don't really have to update those pages just every now and then just don't do a lot of work with them but may give them an interesting Chuck position not the CEO obviously you can get into a lot of trouble for doing that but some kind of personal assistant because these are usually the people with the power anyway for social in Chinese put honey in some DNS so create
a few plausible yet unused supplements like lab your site example admin WordPress whatever you're not using this kind of eats the purpose if you allow the in a song transfer but I'm assuming you don't so whenever an attackers checking out your web page and trying out subdomains that you might not use they might stumble upon a honey DNS page as soon as your DNS of a resolver says hey I got a request for lab your side exam to the dog you can actually set out on a lot and having pictures I've briefly touched on that as well if you have a web page chances are very great you've got an eval page somewhere about HTML so why not call it about on let's
go retune HTML and use that and of course you will have an about underscore v1 HTML that you are not using that is not linked anywhere but that is one of your honey pages and you alert whatever this is triggered because again an attacker might see your about page that is version two if I have a look at version 1 what are the differences who were people on version 1 that are not on version 2 what could I use for social engineering and things like that so it might give you some insights then there's something honey data for database use where you create a few fake people actually with free email accounts you put them together with other made up
data in your users databases or wherever whichever table in your sequel or no sequel server you can think of the purpose of these people is just to see whether the database has been breached because if anybody ever writes an email to that or you see the email on page or wherever it is leaked you know somebody has breached the database or somebody's able to read your database this is something with very much of the honey stuff it might just sit there for years and do nothing and you can't really know whether it has been breached or not but if you get a mail which is one of those emails you know that it has been
breached so it might give you that slight advantage you can put honey in files as well for example an interesting file like license top TST lying around on a server where you assume that could be breached from the internet and whenever somebody touches that file to read it you just periodically check the access times I've got the example for Leno's here it's the same on other operating systems so whenever the excess time changes somebody has a resolute file and you can say that on alert and you know the server's compromised we're coming to the concept of honey bitcoins and this is a very interesting concept I've read about that some time ago and I thought
well that is pretty you just put a honey Bitcoin wallet on your server with a small amount of Bitcoin and whenever that what it gets stolen or them it's transfer you know hey this server has been breached and I thought well wouldn't it be even more interesting to put a lot of money in that say five hundred euros or a whole Bitcoin because as an attacker if I see something lying around would I would I touch a wallet well I I might if I from previous experience no other there's really money in it but then again there was a company offering that as a service and they went out of business so I guess the idea is
rather to a paranoia a little bit if you are a manufacturing company have so many products for example have data sheets for a new product you're putting out this summer again this is not linked by your regular website this is just if you have product pages like pronto three dot HTML and just make a fraud oh six or something like that describe your product but nothing detail and ask the attacker for their credentials if they want to have more information like an address I'm pretty sure you feel like winning the lottery if it works out but it's not far-fetched because if you've read cliff stalls the Cuckoo's egg that's exactly how they captured their attacker by just saying we've got a new
product and please give us your address if you are interested in it and one more thing that I would put would like to cover in honey are QR codes so if you're especially paranoid and you think that somebody's thinking through your trash wherever you work and looking at all the stuff that you throw away and just put a QR code in there and again this pointing to your honey website of use and so if somebody really goes through your trash scans that in and costs so that website you know hands are the person of importance because they are digging through my trash cool and you also of course know that you are attacked so the question is should you put honey
on everything yes yeah please keep the original goal in mind as defenders or generally as people working in the IT industry we tend to be effective not lazy and we're looking for ways to actually catch an attacker that doesn't cost us a lot of work so if your honey stuff generates lots and lots of false positives then it's probably not the correct tool for you oh that's useful if your honey stuff needs a lot of maintenance and it doesn't give you any important information like you've got a honey net set up and nobody's connecting to it then it's the wrong tool as well so just find out what works for you and stick to that there are many more ideas where you
could put honey into so really find out what works for you this just one rule I'd like to stress and that is be creative being don't be too obvious if the following you serve is called luring this Kitty or hoping this $4,000 somebody might get suspicious at least if you've got an interesting and intelligent attacker and they might not touch that stuff so try to make it plausible something that could be on the server and everybody at your company that are on that server should know this is honey stuff they should be connected and lasts like more or less is honey a double-edged sword having stuff and of course it is like everything in our tea
if an attacker knows you're employing heavy stuff they can abuse that if for example I was in a tech and I knew that there are five honey pots on the network I could send them tons of alerts because the security operation center would get swamped other words from a honeypot should be shouldn't be false positives and so they could trigger their attack somewhere else the thing is I think you've missed the point in time where the home stuff is useful at the point where you miss the attacker who found out about and also if an attack is going on and you get tons of alerts on your honey pots you know an attack is going on you
just ignore the honey pots for that moment and you look for the real culprit I've put in some links as well the water works one is chairman the rest is mostly English and I can can really I can't figure out that yeah the awesome list of honey stuff there's reading more about honey that anywhere else
so thank you very much for your attention yes you are
[Applause]
let's say more abstract therefore more likely to be related to strategic dating of money first that's like like chronic person or money tokens we just need to understand there's something like solid that we could use for for starting with these things I in in the case of how many persons like don't think so in case of everything else you should have a look at the things canary jokes because that website is really cool they also sell stuff but you can get a lot of free honey tokens that you could put somewhere on emails where you know that if that email with with that token unity ever gets triggered then you get an alert as well the downside to this is
that much of the info goes back to things so it's not really something that you have fun in the case of honey people please also talk to your management if you give them a new personal assistant they have no clue about they tend to get a little bit upset if you fireman on scene of course I probably should mention that if you're doing that then also read the license agreement or the agreement you have with linked and of saying whether you're allowed to do that and decide whether you care or not questions you're choosing that guy in the back forgotten his name yeah I think I probably would choose the easy path and not put a
honeypot somewhere where it can be reached from the internet because when you're getting scanned from the internet you're getting false positives so if you put honey pots say on RFC 1918 networks only and then the attacker will already have breached you and there will be less false positives because I think everything that can be reached reasonably from sites like children or Google or something will generate false positives that's why men you shouldn't use sites you link to just put the HTML pages there and usually shown and Google are not as creative enough to just do what a human attacker will do great so I suggest if we can to continue discussion in one of the breakout rooms there's got
a really tight schedule this afternoon does everybody know where the breakout rooms are in case they want to continue the discussion was step on out of the room here to the right past the workshop to the right and right there okay thanks [Applause]





