BSidesCharm 2023 - Measuring Your Zero Trust Maturity - Elizabeth Schweinsberg
Show transcript [en]
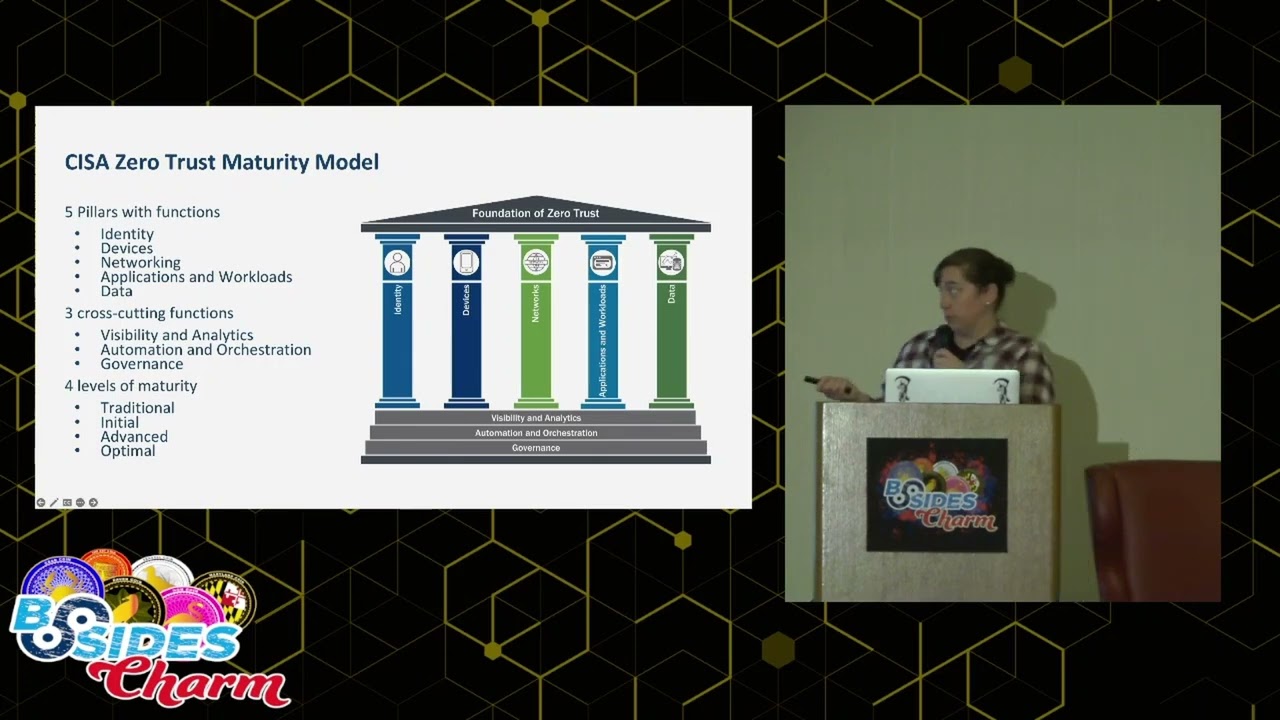
foreign [Music] welcome this is going to be measuring your zero trust maturity thank you for coming out on such a dreary day and staying to almost the very end of the conference this will be worth it I'm Elizabeth schweinberg and I work at the centers for Medicare and Medicaid services so a little bit more about me and why you should listen so my official title is as a digital Services expert at the U.S digital service we help different federal agencies with their Digital Services most of my co-workers help work on websites and other types of services for the public but when I ended up at centers for Medicare and Medicaid services we call it CMS because we're in Maryland we're just in Woodlawn on the other side of 695 we wanted to be one of the cool three-letter agencies um so I've been there about two and a half years and about a year and a half ago summer of 2021 I started leading their zero trust architecture so I'm a long time practitioner of digital forensics incident response and threat detection and I spent about a decade doing it in corporate environments when I made the transition to the digital service I became a zero trust architecture and a lot of that was because of my experience directly in the corporate world my companies I worked for had gone through zero trust Transformations and I was able to work with the corporate security teams and really understand the fundamentals so what are we going to talk about today so I'm going to start with and overall what is zero trust we'll talk specifically about the sisa zero trust model maturity model how to apply zero trust to your environment how CMS measured our zero trust maturity which was super fun and give you some tips for creating your own framework and doing the next best thing so what is zero trust zero trust is a security model that emphasizes frequently verifying trust relationships you move from checking permissions at the perimeter to checking permissions as one moves throughout the system user starts with zero trust when you show up and as you collect more information about the user you can choose whether to increase that trust or decrease that trust I like to think of it as trying to go to a professional sports ball game so this is a wonderful replica of Oriole Park at Camden Yards where the Beloved Maryland Baltimore Orioles play and when you show up to a game the first thing you do is you have to go through a bag check and a metal detector they want to make sure you're not bringing in anything untoward and that's similar to running anti-virus and EDR on our systems to make sure that they're healthy next up you're going to get your ticket scanned are you there for the right day the right time yes no better come back a different time this is like your Authentication and then when you get to your section uh your ticket is going to get checked again to make sure you're in the right place you're not trying to sneak into the more expensive seats as you go throughout the stadium you might see other checks like if you go to a concession stand and try to buy an alcoholic beverage you're going to have to prove you're 21. if you are going to the club level there's a check just get up there because they've got fancy concessions and not just anybody can get them so um that's you know making sure that you have permissions to different systems and applications as you try to do the job there are three popular zero trust Frameworks particularly if you are in the federal government the first one is the nist special publication 800 207 zero trust architecture and it uses seven tenants for you to think about as you are building your systems and they give three architecture approaches this one tends to be a little bit more Network Centric then there's the dod zero trust reference architecture they use Seven Pillars to describe an environment and within each pillar there are different functions there are three maturity levels and then lastly we have the sisa zero trust maturity model which has five pillars each with their own functions three cross-cutting functions and four maturity levels all right now um so this is it in depth the Five Pillars are identity devices networks applications workloads and data so when I talk about a function what do I mean by that so if you have an identity system there are some things it needs to do to be an identity system we'll start with you need a list of your users some sort of user store you are going to need some authentication to be a good identity provider you're going to need some sort of risk assessment and some sort of privilege management so each of the Five Pillars have very specific functions you fulfill all those things and well most of those things and you can do the job and in addition to those four functions for identity and across the line there are also three cross-cutting functions that each pillar must fulfill visibility and analytics Automation orchestration and governance so this is the main difference between the dod model and the sysazero trust model DOD gives visibility and analytics and automation orchestration their own pillars otherwise the other five pillars are the same just integrates them into each one calling out specific things that you need to have visible or be able to analyze and or automate and orchestrate and then as of April 10th after I had already made my draft of the slides ciso released version two of the maturity model where they went from three levels to four levels originally it was just traditional Advanced optimal and now we have a new level initial which actually I fully support so traditional is just the way we've been doing security for the last 20 30 years there's going to be a lot of manual configurations the pillars don't really work together they're pretty siled any uh permissions would be set at provisioning and you're going to have limited visibility As you move into initial you're going to start to have automation maybe you um use some sort of gold image to provision your laptops every time so you don't have to go through and click knick-knack next next on your windows you're going to start seeing some cross pillar integration one of the more popular things that I've seen is around device certificates and using those to enable network access so in gone are the days where anybody could walk up with a network cable plug into the wall get access to your corporate environment now it's going to ask for your device certificate if you don't have it maybe you get put on a special VLAN if you do have it great you can access the corporate Network you might start seeing time changes around permissions so I'm a system administrator sometimes I need to do really administrative things and it's going instead of letting me be the highest privilege all the time I can turn it on and after a set amount of time it'll turn off and then we're also going to get aggregated visibility so this is where we centralize our logs because when you put all your logs in the same place you can find them later moving into advanced automation everywhere your policy enforcement is going to be integrated across all of your pillars you're not just going to do time-based enhancements or dehancements to your different privileges but maybe there will be changes based on risk or posture so if you are coming from your laptop your corporate laptop you can do one thing but if on your you're on your mobile phone maybe it's a bring your own device kind of situation maybe you can only access your email and calendar and any serious data you don't have access to and then not only are we getting all of our logs on the same place we are also able to integrate the visibility of them then as we move into optimal we are fully automated just in time all sorts of all the pillars are talking to each other our permissions are dynamically set enterprise-wide and not just are we centralizing our information but we are also using it for situational awareness because um uh we can like look at the history of people and use that to inform us of what uh what is going on I'm going to preserve questions at the end so I was like sweet we got this maturity model I'm going to take it and I'm going to compare it to our environment and we are going to know how mature we are and then we started trying to talk about this and we found some very interesting things zero trust looks different in different environments so to continue with the sports metaphor I talked about how things look when you go to um Camden Yards now let's say instead we were going to go to Pimlico and watch the horses race in a couple of weeks it is a very different setup you've got the inside the track view um uh you've got the big tall building you can sit in and there's different zones how people move between the zones are different what you're allowed to bring into the horse uh well to Pimlico is different than what you can bring into Camden Yards the hats are different it's just a completely different environment that you really need to um think about differently so some of the specific things we found was one of the things was identity in different environments so when you're in your just talking about your Enterprise environment you're thinking about staff and contractors and how they use business applications sweet that's that's a little easier because you give them equipment you give them accounts they would like to get paid to do their job so they'll follow the rules As you move into your on-prem data center now you have to think about your system administrators and the developers what are they allowed to access and how should they have to prove themselves plus now maybe you're developing software for the public or for business partners that changes what you can expect of them and then when you're using infrastructure as a service it's for identity it's going to be pretty similar to um on-prem data center you have to worry about this is admins and the developers as well as your users and then thinking about devices this is where it gets a little mind-blowing so Enterprise it's easy we're talking laptops mobile phones things we can touch things we can count throw in some printers probably some iot for facility maintenance and you can eventually enumerate it all when we're talking about data centers we're talking about servers in racks and there are there well there should be processes for buying new servers and how to get them in your building and installed but they're big things you are you're going to be able to keep track of them also there's no physical server you're allowed to touch in infrastructure as a service but virtual machines are really just servers without the hardware and the containers are kind of like virtual machines but they're just really locked down so we started looking at these types of virtual assets virtual machines and containers as devices in this context and we actually explicitly leave out um end user laptops and mobile phones because we have no control over them the general public they bring what they bring so those get no trust and then we can think better about how we're going to trust these the first version of this is a maturity model did not explicitly address virtual assets it does in V2 so we're like great this is going to be exciting so this is what we did to build out our own framework and while this is a very good slide to take a picture of at the very end of the presentation there is the link for where these slides are available on GitHub so you can go download your own copy and look at it straight on so when we developed a framework you know seven easy steps pick an environment rewrite the maturity framework that works for your systems write some questions to help you determine where different systems will uh will match the levels for the pillars and functions get everybody to fill it out grade the questionnaire give feedback on the questionnaire and help them actually improve their zero trust maturity that's it so we started with our most popular infrastructure as a service provider um mostly because even though there are a lot of options in the cloud there's a finite number of services that one of these cloud service providers will give you unlike your own data centers where every team has chosen a different database and maybe a different operating system and it's going to be a lot less homogeneous so we went with infrastructure as a service and that is where we got started so I'm going to go through a couple of examples specific pillars and functions and how we adjusted the levels and made them more specific so I don't actually expect you to be able to read this slide um uh each of the different parts are going to be available in the following slides so I started in identity because identity is so crucial to the foundation of zero trust and when we were talking about Authentication similar to what I mentioned a couple slides ago we realized that we want to look at authentication and identity stores differently for developers and our end users because of that because of what we can control and versus what we can't we also made a third category of authentication and identity stores for apis because they too have a different way of authenticating so cisa starts by recommending for your traditional that maybe you use a username and password maybe use some light multi-factor authentication MFA and that's all you really take into account when you authenticate somebody awesome we're on board with this let's do it As you move into the initial phase you want everyone to be using multi-factor Authentication and you also want to start pulling in other attributes so this is where we started being able to get a little bit more specific so we're able to say maybe your application can only be used if you are using sassy or a device signal is available so sassy secure access server Edge is a don't tell Z scalar I said this but it's a fancy VPN but it's a way to more specifically broker your network connections as we move into advanced we only want fishing resistant MFA available so 502 PIV maybe moving towards a passwordless MF well passwordless MFA seems a little strange to think about and we knew that we wanted to be incorporating more device level signals or additional perf and then here well we've already hit the max MFA but we're continually looking at our authentication and when say an attribute of a user changes we re-evaluate the authentication so I don't know let's say your IP address changes in the middle of your session that's unusual so we should just do a real quick authentication and make sure everything else is still the same moving into devices I want to highlight governance um deploying MFA at any level can be a big lift and there's a lot of people to convince and you're going to have to buy some stuff but one of the places that is easier to get started is wrong governance so governance is basically what your policies are how you decided on them and how you enforce them so it's the whole thing so when we talked about devices we really started thinking about device life cycle and in this case we are talking about device life cycle of virtual machines and containers so we were able to remove some of the language specific to physical devices in another part like it says sanitize here you don't sanitize a virtual machine that somebody else is running you just delete it and the company does the right thing um and we also specifically called out digital Assets in here as we move into initial we started setting some expectations you need to have written down your device lifecycle plan that is a great first step because until you know the process you can't automate it and that's the the future steps so you have a documented device lifecycle plan you're implementing it manually you're doing some sort of monitoring and scanning of your devices that is automated say you're running a vulnerability scanner you take that information and then you do something with it and then we also called out routine patching initially you need to be doing at least monthly and then we also have a large um organization capital O within our cloud service provider and we have a team that supports making gold images so you should start using those um as we move into advanced your device life cycle plan we're starting to implement it automatically this is where our infrastructure as a code comes in some of our CI CD continuous integration and continuous deployment really comes in we're using gold images everywhere are routine patching now happens at least every two weeks very strict and then our systems are able to tell us when a device policy is out of line because when you have a whole bunch of virtual machines and you've deployed them the same way and one of them looks weird that's where you need to go look and then an optimal everything's automated we left routine patching at two weeks because that's our current expectation in our organization and then not only are you able to know when something is not in compliance you're also able to Auto remediate that device well probably look something like take it out of the pool for the application to use and maybe snapshot it and keep it somewhere safe until somebody can look at it and then the last one I'll go through is data data encryption the one of the maturity model actually in this section only talked about data at rest in the network section section rather they talked about data in transit but it's all been combined into one here so start pretty easy you only encrypt some of your data at rest or in transit and every team is doing something different about how they manage their keys as long as they're not checking them into GitHub and then moving into initial your teams are encrypting all of your data at rest all of it in your infrastructure and service providers make it easy to encrypt things even if you are just using their key encryption systems it is better than leaving it unencrypted and then we put a parameter here that we are encrypting all data in transit outside of the um infrastructure as a service account so anything that leaves our little perimeter got to be encrypted and we're starting to talk about how we're handling our keys managing them and securing them moving into advanced now we're encrypting all of the data at rest all of the data in transit within and outside the accounts and we have like real policies about how we handle our keys and then at the end we start getting into encrypting our data in use that's kind of the next Frontier that we're seeing it's still hard at this point um but I think I think we're going to start getting I think it's going to start getting easier in the next few years and then we're using similar processes enterprise-wide and we're doing really smart things with our keys so we're like sweet we've got this great maturity model and we had so much fun making it because we all really love talking about zero trust and Security in general so we're like how do we find out what people's maturity is I know let's ask them so we set up some meetings with a few teams that I knew better and I was like Hey read these descriptions and tell us which one resonates with you so this wasn't this wasn't scalable each conversation was taking two and a half hours there were at least 100 teams we needed to talk to and it was fun the first five times but I could tell it was going to get tedious on our side um so we're like we need to scale this also if we were asking specific questions we'd get better answers that weren't so tied to I want to get an A on this or I want to get an advanced or an optimal so we decided to go with survey questions but we can't call them surveys because surveys sound optional within the federal government when you want people to tell you things you make it a data call and then they think you're serious and you fill it out so we initially came up with like a





