HankFordham
Show transcript [en]
[Music] so I got a lot bigger of a room this year than I did last year um just a show of hands quick how many people got one of those weird tags at the front door how many people are kind of freaked out by it has anyone scanned it yet wow I wasn't expecting anyone to have scanned it yet the tags are uh something we made for a little bit of fun here but they have a QR code on the back the QR code basically uh it'll open up a calendly link uh if you feel like you want to risk scanning it um the calendly link gives you a free deep web scan with me
at my company X10 Technologies um so we we've been doing these Deep Web scans for a little while now and it's been pretty startling uh we have a 100% um success rate in terms of finding something or some kind of exposure for a company on the Deep Web uh and they never go for just 15 minutes everyone usually it goes for like a half an hour but if if you want free 15minute deep web scan they're also NFC enabled NFC coins and they enable the giveaway that we're doing um if you weren't able to get one it's cuz it was first come for serve so I think we gave out like a hundred of them but uh at the end here
we'll we'll give those a quick scan or I'll scan them for you and we'll do we'll do a little giveaway uh super quick again who gets nervous when they talk in front of people well there we go we've already got something in common um so my name is Hank this is going to be uh hackers on the Move tools of the trade it's kind of a I guess a soft sequel to my presentation last year um about social engineering and amigdala hijacking kind of the human element of cyber crime uh so yeah my name is Hank Fordham um I'm an Enthusiast and and luckily now professional hacker uh by virtue of that fact I'm I'm really good in front of big
audiences uh needless to say I'm still really excited to be here today and show you guys some of these tools um I'm now a cyber security specialist with X10 Technologies so uh I get to run the um internal and the external pen testing engagements as well as our fishing exercises and obviously the Deep Web scans uh I'm a guest speaker on the shift with Shane huitt where we talk all across Canada on the radio which I'm realizing now probably doesn't make sense cuz I sound nervous I don't sound like this on the radio uh but I basically get to um pick topics and we talk about cyber security different breaches any news or incidents that happen and make it onto the news
and we get to tear it apart um for The Late Night Listener I also have appearances on uh I've been on Vice twice I've been on Dr Phil um Washington Post I was probably equally as nervous to be on Dr Phil but all for good things all for ethical cyber security research and um disclosure projects so I'm going to move really quick into my agenda and just explain kind of quickly what I'm going to go over today um and keep in mind that this agenda is is focused around tools of the trade so there's not a lot of um Cali Linux I I will be doing a demo but we won't get too too much of that uh the
agenda is social uh kind of surrounding around social engineering um and how hackers are entering our networks and compromising our devices with low uh to no interaction social engineering I'll show some uncommon and common tools and techniques that hackers are using uh just to compromise again networks and devices like hacking toys um some car hacking stuff uh I saw someone else did a car hacking talk and I wish I got to get to that but I'll I'll catch the recording and uh just passive hacking and more and then we'll do a little bit of a demo and a prize giveaway as uh mitigations shouldn't even be here anymore cuz I realize I'm I'm preaching to the choir but I I think
it's important anyways that we go over just some really quick like how to stop this from happening so super quick I'm going to start with um my favorite definition of social engineering and that's one by uh Christopher Christopher had Nagi uh his is any act that influences a person to take an action that might or might not be in their their in best interest so clicking on a link or um downloading a file or entering your credit card number um so obviously in the context of this presentation it'll be using tools of the trade for low interaction social engineering uh so like creating an evil twin Network or a captive portal in spaces with low or no
service um so we went to I I was speaking at it for K12 in Vancouver this week as well and we set up a captive portal Network just to see how many people would actually risk logging into open wi-fi and I told my partners like we're probably likely to see five um because it's a pretty woke audience if you will and uh we saw just over 140 so we saw 141 in 2 hours and we didn't collect any info just just that that one account and of course the credit card number I'm kidding we um so I'll also talk a little bit how cyber criminals are using techniques to disguise themselves in their tools uh
and just a little bit how I'm guessing we all realize there's an open market for attacking new and old Technologies like um you know I I'm speaking less of ransomware as a service but I'm still me like that's obviously still included but but I mean um I'm thinking of like telegram tools and especially with the uh recent invas in Ukraine there's been a lot of um more access and a lot more tools and nefarious tools being made available to a western Market just because selling them is a lot harder for them now obviously so we're seeing some pretty weird Russian tools come up and stuff like that um and from different countries as well like
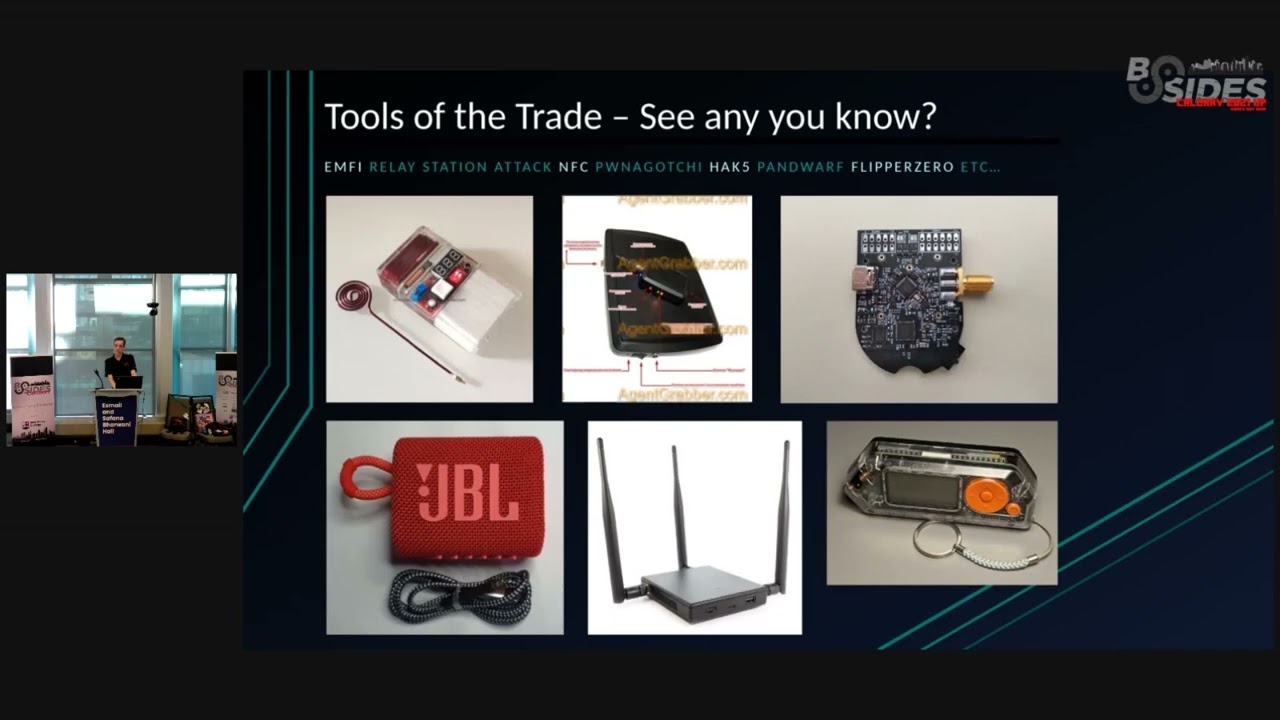
Italy dances um so again an example being uh you know setting up train where someone's phone who might be you know set up to automatically connect to their home Wi-Fi is going to be unlocked on that train and if you have a Wi-Fi pineapple then it becomes pretty easy uh not only to trick that user into connecting to a malicious Network um but you can also create or complete attacks like a half handshake attack for example where all we need is that Network remembered on your phone to get the password in most cases uh so I guess this is hard to ask a big audience but does any I guess put your hand up if you recognize any of these at
all there we go yeah I knew I was preaching to the choir today uh so the JBL one on the bottom left is probably a bit odd it looks like a Bluetooth speaker if you guys went to the car hacking presentation or if you've been researching car hacking at all I'm not sure if he went over this but uh this is a tool that criminals are using to steal Toyotas and steal different um car models through can bus injection uh the the one on the top left I'll go over all of these tools today except that JBL Bluetooth speaker um and you might even recognize the one on the bottom right The Flipper zero uh this
one's transparent but they usually come in in a white like format uh so there's some Cool Tools here but the reality is that companies need to re Iz these tools have the the full capability to compromise their Network and their device whether or not I I realize there's a stigma Around The Flipper zero right now and I'm going to speak a little bit about that as well but um all of these tools are dangerous and they can cause damage or loss of property so the first tool that I'm going to mention today people looked at me weird probably CU I have a light bulb in my laptop bag um but this is an electromagnetic frequency injection tool it's B
basically an EMF generator I guess you could call it like a pocket EMF generator they're super duper cheap to make it's about 20 bucks in Parts but the device is resold out of Italy mainly um as a slot machine Jammer and uh it obviously doesn't work as effectively as a slot machine Jammer now in North America um just because there's obviously been mitigations and one of those being painting the inside of uh slot machine cabinets with uh an adhesive not adhesive a conductive paint uh just so that if someone does try and attack anywhere on the outside of the cabinet it's signal through that conductive paint so super easy cheap fix but um they do tend to still be uh being
abused in some places obviously in other countries where the gambling or Casino equipment is a little bit older but uh also in Canada where we have tons of different bars that offer Casino equipment um one of the things I mentioned to it for K12 is also that uh it has the potential to work on some models of change machines and vending machines and um just to like give you guys an idea cuz you're probably like this light doesn't really help you understand it but when you put this through a coin slot on a machine and you're fishing around and wiggling it it's you're finding an integrated controller and if you can find something to manipulate oh this might not
uh this antenna has been didn't had better days but if you can find something to manipulate then even through like the coin slot you can trick Electronics into activating when they shouldn't um so you can imagine it does a lot of really weird things to a lot of different things um it can break a lot of things it can mess with your phone uh at a few offices that I've tested it on I won't name any um you can hold it right next to the wall and it can actually trick Radars and stuff into opening doors so there's lots of weird phenomena that this device can create and it's scary because kids are buying them with with a curious mind everyone
and and criminals are buying them with a curious mind and thinking where can I where can I use this what what does it work on does it work on a machine change machine what about a parking machine uh doesn't work on parking machine but so you can imagine they're getting these and they're holding them up to different things and vending machines and readers and seeing what they can get to happen uh so there's a lot of documented abuse in recent years um and again it's being mostly sold as a slot machine Jammer that's kind of a scam uh to get people to buy it cuz in North America it's it's not going to be that effective anymore
but uh having said that I do have a video here and I I guess this might prove me wrong in saying this isn't effective but I'm just trying not to get in too much trouble oh do I have audio okay here let me just switch my audio
devices you know what we might have have to
just the video should be good
enough put out ofs of dollars right yeah thousands on thousands of dollars and on Christmas Eve at that I found out how police say they did it and how it was all caught on camera you can see on this business surveillance video people playing a game at the Grand Riviera it's a sweep Stakes parlor on Rock query Road customers play games distance their actions seem ordinary but zoomed in you can see one of the men pull out a device and push it into the table police say that man at 20-year-old kadaria peoples used the device to trick the machine he put it in in the dollar slot making the amounts he was playing for go up they say peoples
was working with this man also at the table 23-year-old Damian Parker police say the two won nearly $7,000 extra dollars from using the device they didn't take those winnings home though and instead ended up in jail the two now face felony charges thereal to be way count so uh yeah they got arrested [Music] um I'm just going to go next so I I that doesn't keep going but yeah you can imagine like again maybe build one of these I posted the design files on uh hack forums and I'll also post it on my GitHub I'm a big fan of get it out there and then it won't work anymore so um if you guys want to download that you can
I'll share my GitHub at the end this this next tool here is called a relay station attack the uh silly criminals are selling it as a a car hacking tool it's a keyless go repeater is what they're calling it um I tried to censor out that website but I'm realizing now looking from afar that I didn't do a very good job but um these are these are low cost they're also like 80 bucks to build um but they're extremely expensive to purchase from a criminal or black market uh for obvious reasons they're looked at kind of an investment by car thieves um so there's there's a bit of just like you would see a pay wall in
front of things like um burp Pro or nessus Pro um you see the same this pay wall where they've they've put a price in front of this tool that stops anyone from purchasing that wouldn't be interested in purchasing it for its explicit use which in this case is for car thieves uh obviously this isn't in my everyday carry but so I don't have one here to show you today but if you're interested in joining me in the adventure of reverse engineering these uh shoot me a message because I I have gotten my hands on one and I've been taking it apart and taking good photos of it um that also made it so I could
test them so that when I'm telling you about it um I'm not blowing smoke um so they are really effective they're very very effective considering PK passive keyless entry system was invented in 1995 uh so and cars car companies didn't start becoming more privy to people trying to abuse things like a a car's fob code until around 2021 when they made it so uh not only did they add things like rolling codes but there's time to lives and there's a there's a a ton of other things that are beyond my scope to explain to you uh on on car hacking and how they've mitigated that in in the past but because of this there's this massive two deade like
almost three deade window where any car model built inside of that time that has passive keyless entry enabled is vulnerable to this device and and so if your car has it where you walk up and you put your hand behind the handle and as long as your key fob is in your pocket the car unlocks that's passive keyless entry and the way that this tool I put the JBL tool there because it steals cars I'll explain that in a second it's different though um the one we're looking at is the black one on the left side so if you look at it um you might see it's a little bit hard to see but you might see there's a little box
on top of a big box uh and the way that these work they're sold together as a package and the criminals like go to the website and check it out the the criminals have a really cool funny way of of advertising these things um but the small box is built so that it sits next to that car handle door and the cars have antennas like low frequency sub gtz antennas all around the car and they Broad cast a challenge so if someone were to walk up to a car and pull the door handle it issues a challenge the key fob gets the challenge and it answers the car back and that's what unlocks um so with this tool a
hacker will sit by the car or a criminal I shouldn't say a hacker we're the good guys but someone will sit by the car with the uh small box and it's literally in Russian it's described as the small box um and then another hacker or cyber criminal will stand uh near the house or an office or in a cafeteria big um technique that law enforcement has been seeing recently is people going into malls and trying to go around the cafeteria and you don't have to carry it like this like looking obvious you can put it in a laptop big but the idea is that these two boxes relay that attack from the fob back to the car so car to
fob gets it relays it back to the car and because of this rolling codes don't matter and there's there's a time to live on these challenges but the time to live is so long that until again until 2021 um it it it's it's the time to live is so long that that relay the actual time it takes to relay that challenge it it's very quick it's millisecond so it's very easy to beat that time time to live um and so obviously because of all of this there's been a lot of increased abuse um in recent years and obviously with more access to a western Market because it is Russian technology it developed in uh in Russia and now it's
being sold out of Bulgaria um because it's uh it's harder for them to sell it now so uh and again it's also mostly sold on the Deep Web I should just say Telegram that agent Grabber website is not on the Deep Web um oh jeez well there you go but um so that's not on the Deep Web obviously uh and again like I said this guy they they're advertising these things for $155,000 and it's in Bitcoin conveniently enough um so when I saw this I thought it was extremely fake I I even thought the attack was fake and I asked a friend um to to help me get one and he went to Bulgaria and he got one
and uh brought it back and he let me take it apart so thank you um I'll show you guys a video now of this
tool so you can see uh I guess I'll pause it super duper quick there's one guy over here next to the car and the other guys holding the big box and he's looking for where in the house is this key located it could be in someone's pants pocket on the floor uh or maybe it's in a [Music] nightstand so they basically and you can see a lot of videos of this where they go and they try for a while to find this and he's looking again for the signal cuz he's lost it they want to start the car so now they've start the car and they'll drive away um obviously that doesn't work once they get more than
like 200 M away so what they'll actually do is reprogram the car for a new fob and then they'll Reven the car uh and then and then they'll sell the car what's the range oh yeah also I forgot to say this please feel free to interrupt me and ask questions but good job uh the range is like um so with the small box the range from the car um to the small box can be 20 to 50 m and then the range from the small box to the big box can be up to like 300 to 500 M because that one you can operate at a higher band frequency it's using like 2.4 GHz and whereas the the car's
challenge is actually operating off 315 mahz so it's a much higher much stronger frequency and you can get a lot further and so what they'll do is they'll Ste steal that low frequency Challenge from like 20 50 m and then they'll relay it with a higher frequency to the other box that box demodulates the The Challenge and then it repeats the challenge again at a lower frequency uh so that I can get it from the fob and then um rinse and repeat and you get a new car uh this next tool this is one of my favorites has anyone ever heard of this tool before yeah oh cool I love that so the pagi is really cool I didn't make it
I don't I don't know the guy that did but um the pagi is basically a wi-fi hacking project that's meant to introduce people to the concept of um machine learning and wi-fi hacking and so it's super inexpensive I used to have a really weird range on here of $10 to $200 and I realized that was nuts but you can get the uh raspberry very pi0w chip for 10 bucks depending on the chip shortage going on and where you get it um but roughly you're going to end up spending $100 if you want it to like have a screen and maybe a 3D printed case or something um no I'm not selling them this I this is the only one I have
uh the the neat thing as well about these is um while they're considered kind of a kids toy they're not really they're really effective on pen testing engagements if Wi-Fi is in scope and you don't have the time to go and test an office or if you want to just send this device out and have them turn it on or plug it in then it can actually do a lot of the Wi-Fi assessment for you as long as you've trained it in effective environment because it's it works with machine learning so if you trained this um by leaving it in your basement for a few weeks and letting it try and hack your home WI Wi-Fi um then it's going to
be a pretty dumb AI but if you train this by walking around downtown and I'm not telling people to walk around downtown but theoretically thinking if you were to train this by walking around right here uh then it would be a very very smart AI when it comes to wi-fi hacking it would be much more effective this one I've had since 2019 I like to think it's a smart AI it's really good at what it does um yes and no no um you can actually the another cool thing with these is there's a lot of functionality you can disable and enable to make it so you're not worried about breaking any
laws from this why work for a company now I'm not allowed to turn it on I but I but I did do it last year and I got the we so these things have the ability to get messages there's an inbox on them and someone had messaged my pagi last year and because you can connect it to the internet I actually got to respond to them and we uh we set up to go out for a beer so I thought that was kind of cool but uh yeah they can like what he's referring to is when one of these sees another one in the same room because they can communicate using Wi-Fi and they use machine learning the
developer thought it would be a cute but creepy idea to make it that if they're in the same room they'll actually see each other and on the screen it'll say oh hey Nano nice to see you again and they'll actually start working together to make things faster and hack Wi-Fi faster and uh you you just reminded me of a really good story I so I got I used to get to teach kids how to make these which trust me was a good thing not a bad thing um we would teach kids about the ethics of cyber security the ethics of and reprecussions of breaking the law around cyber security um introduce them to 3D printing as well as little
computers machine learning and hacking so it was a an absolute blast uh getting to work with kids and it it showed me that I'm like they're going to make me look like nothing in a few years that they constantly think outside of the box and they're really really good at learning this stuff um but back to the story we were I was teaching one of these classes in the sutina police station and uh which is an interesting place to teach a wi-fi hacking class but when in the ethics course it it was very clear that we were to whitelist the police's Wi-Fi and uh so all the kids went through and they had to learn how to
whitel list and and work in scope to the demo Network only but the police chief's daughter uh didn't listen to that part of the demo and so despite all of our best effort except one person in the room the police chief's daughter uh everyone's um pagi started getting the handshake for the sutina pleas Wii and because there's like 20 of these things in the same room they all started trying to work together and get a better handshake and then one kid learned like how to enable a plugin to connect it to wiggle and WPA SEC so that it would share the location that it found the the handshake but it would also automatically crack it for them and
so now uh within minutes before you can even tell the kids to turn them all off everyone had the password for the sua police Wi-Fi network that wasn't part of the presentation I hope I'm not in trouble for saying that but yeah you reminded me about
that oh really yeah see and and it's so to me like when I try and explain this to a non- haacker audience I say this can literally lead to ransomware it's weird to think of but if you have active directory internally on your network and that's not configured in a way that when I get that Wi-Fi password and I can connect I can if I can pivot and I can get more Privileges and and we have a pentester at X10 eigor Chell who he has a 100% success rate and even going into a company that's already had an assessment done and finding a lot of V vulnerabilities in active directory he scares me and so I'm like yeah this
could literally lead to ransomware because if they're getting if they can get you know if you're not using Wi-Fi 6 and if you're not using a secure password and they can get that and access your active directory environment and it's not configured securely this kids toy just just led to a ransomware attack I hate to explain too much but um obvious viously as well having said that these are still being heavily abused in recent years and so there's 29,6 49 active units when I made this slide and I very quickly realized the next day how popular these were because um the number jumped to 3,090 and this was a c like a week ago so I imagine it's even higher now uh and
you might be able to see the number next to Canada there is 1,33 uh but that's not accurate just because of or by the virtue of how networking in Canada in relation to the USA works that number is likely a lot lot higher if we look at America's number it's 11,500 at the time of making this slide so it's likely closer to 5,000 active units in Canada and most of these units are possessed and operated by uh well low to no experienc cyber Security Professionals and um and and youth and and cyber Security Professionals a mix of it uh but the main demographic would be the Curious mind that doesn't realize just how powerful it can be just
under sorry just under 31,000 right now yeah see and it's climbing when I made mine there were like 2,000 unit units Global uh there we go this is one of the fun slides um I hope everyone re who who knows what this is good okay well actually I guess it's fair not to expect everyone to know what it is this is a flipper zero it's um if you don't know what it is now you probably will soon or you'll see it on some YouTube video or some short or something uh there kind of making their way around social media and around the internet right now and uh it's it's a hacking toy well I shouldn't say hacking
toy it's a hacking Gadget um it was kickstarted in 2021 I want to say and it raised just over $4 million uh which which was pretty big considering their ask so uh again they're kind of considered a kids toy but it's not really um I'll explain some of that as as well because there's there's a documented a lot of documented abuse in recent years and so Canada Border Services Agency has actually started to seize these devices uh because they just obviously they don't see any benefit to letting any more of these in the country uh it's banned by Amazon right now it keeps getting unbanned and banned so I know this week I think it's unbanned I think there
might be five left right now and then on eBay it's banned this week so next week um it might be the other way around you might get it on eBay but not Amazon um but cbsa might steal it it was a pain to get this thing I had to get someone to deliver it to Vancouver and then um bring it to our office and then confirm it was real and then Courier it down to me in Calgary so it was a bit of a pain to get one of these but um when I say it's not really a kids toy it's because of some of the features that it enables um people with little to know
knowhow or technical knowhow to execute so there's functions features and attacks inside this device that uh I I actually I brought something today to give a a little example of of what I what I mean but if we look back does who actually who recognizes the name Sammy cam car there you go if you know Sammy camar you're researching in the right places um so Sammy cam car made an exploit a few years ago and he called it open sesame uh it's based off of a toy that was sold by Mattel um his his attack wasn't based off of this toy but it it was something that um he used one of these toys to
demonstrate that attack so it's basically a girls toy that was sold by Mattel in like 2 oh it stopped in 2010 so it was pretty old uh but it it was basically a girls texting device so girls would would plug the USB into their computer at home and it would have internet so it enabled them with this device to go message their friends around the world it was like old school texting I guess uh so you didn't have to pay for a plan but inside of this device is a Texas instrument cc1101 chip and there's another chip in here um that enables uh an attack on radio frequency so um what Sammy camar did is he
developed the the open sesame attack and he programmed this toy so that it would guess all of the codes for a garage door in in seconds and it did this using the uh boy I can't remember the algorithm's name I probably couldn't pronounce it anyways but debruin the de bruan sequence he used the debruin sequence to guess every single code within just a few seconds and at the time you can imagine criminals were very very excited about this and they really wanted their hands on one of these devices and by ver like if they got their hands on the device The Next Step was get your hands on that code and Sammy camar posted his
code for open sesame on GitHub but he famously bricked the code so that if anyone and he actually said this on on the repo um anyone that didn't know what they were doing probably doesn't have business um using this code anyways so if you know what you're doing it shouldn't be hard to fix it and so back you know even a few years ago a couple years ago I would argue even in 2018 and 19 right before Co and and before this got uh developed and released it it would have been very hard to fix that code and make the open sesame attack work properly but what the flipper does is makes it so if you plug a cc1101 chip
which you can order now on eBay for two bucks uh if you plug it into the general purpose in outboard here the uh GPO board on the top uh it comes preconfigured with the open sesame code on bre so my my point when I say that these aren't really a kids toy I I constantly hear people say they're kids toy and it's it's silly because it enables people now with little to know KN how and technology or hacking or anything to carry out an attack that before would have taken us some hardware and a little bit more knowhow uh on how to how to carry out that attack so now have people that that are like just like crazy they're
trying to sniff for radio frequency or they're doing Bluetooth spamming I see um is Wayne still in here no oh okay I promised him I I wouldn't do this but uh for this next part I just want to show people a really quick demo um this was a little more relevant in an it for K12 audience but there was a a service that these two students in 2017 were off offering and and even more recently there was another case of this where a student was offering a service using this the one in 2017 was using an esp32 Dev board so like a node MCU um or aen but what they were doing is they were offering students the
ability to uh have their their classes crashed on demand so if they didn't want the class to function properly that day day uh then students would actually they would launch deauthentication attacks on the Wi-Fi they would spam the Wi-Fi network with um like fake Beacon packets uh and there's a ton of other things they would do but if if you pull your if you want to participate in this you you pull your phone out and unlock it if you don't I don't blame you so don't you're not hurting my feelings I'll hold I'll hold mine up so you can see as well and hopefully this doesn't mess up our stuff but uh yeah hopefully the big old cross your
fingers but so this actually got a couple students arrested and charged because they were offering this denial of service um service and uh one of the students was doing it by virtue of using a flipper zero and so basically he he purchased this and with very little to know technological knoow he set up that service and attack and another student was using an esp32 which is a little bit more knowhow you have to program it um but right now it's sending out a Bluetooth uh request thing you've probably heard about this online like the Bluetooth attack that these flippers are starting to do and uh if we left this running for a while in it for K12
the idea was if you can make it to your Wi-Fi network like just see if oh boy okay there we go and there oh so see if you can get to your Wi-Fi network and then imagine that happening uh in the middle of like a hospital or a classroom or an industrial control environment um any kind of in interference like that can actually be detrimental to not only obviously an educational environment but a critical infrastructure environment um or your business we're just about done here um these this next slide I just wanted to show everyone because I think it's important that um everyone kind of explore some of these hacking gadgets a little bit
does uh well I mean that one probably I'll bet you they weren't very secretive about it I think that's how they got caught um there are there is yes yeah you so you can identify a deauthentication attack by actually um well so how I identified the authentication attack would be watching the network in like in monitor mode and if you're noticing packets where the header is a DE authentication header it says it's a deauthentication packet if those keep appearing in in a frequency like say there's more than 3 a second then you're dealing with with a deauthentication
attack I'm better at at breaking things than I am fixing them so I I'm working on that blue team flag still but um I couldn't tell you I I know how to see if one's happening and uh I imagine there's some pretty like cool ways that blue teamers have for actually tracking down the source of a deauthentication attack um but I wouldn't I wouldn't know exactly how without like my silly movie ideas like I I would set up a web of node MCU or ESP 32s and each of those would watch for dooth and if if three of them went off within 50 m over here then he's probably over there probably some stupid way overthought method to detect
where they are I bet there's way better ways now especially with um EDR and Sims like how powerful those Solutions are becoming I bet it would scream like a Christmas tree where where this is originating from at least what device it's originating from uh so yeah hack five um there's more than just hack five I kind of regret not putting those other ones on here but um there's like hack five lab 401 hacker Warehouse uh those are the good ones actually but um these are very very cost efficient and high quality tools they're very good at what they do um in some cases they might require a little bit more KN how to set up but they they
enable pen testers to carry out an engagement with a lot more ease and so one of my favorite tools here that I pulled out was the land turtle if there's one tool that I suggest any anyone here even if you're not a pen tester um actually I'll say two two tools if there's two tools I suggest everyone here by even if they're not at pentester it would be the land turtle and the the USB rubber ducky and um both like the rubber ducky offers you not only insight into some of these hacking tools and how they work but it it's also um it can help you automate a lot of it um processes that you might take uh but
it also helps you automate hacking people a USB rubber ducky uh for those that don't know is basically a USB stick that operates as a human interface device so uh if you guys have heard of stuck net um where they dropped a bunch of USB sticks outside of an Iranian uh plant this is basically how that was carried out was with malicious USB sticks um so anything you can do with a mouse and a keyboard in half an hour this can do in about 1 minute and uh there's lots of cool payloads on the hack five uh repository as well um the land turtle this is an Ethernet USB adapter maybe the USB is making it
obsolete now but um that's something that uh I wish I could name companies but on like one of my most recent pen tests with this land turtle I was able to get it plugged into a computer on the back of a computer that was like a spaghetti monster like they just had so many cables coming out of this computer that um when we plugged the land turtle into that computer we actually had a full shell into that active directory environment for the entirety of the pentest and so we were able to find a lot of misconfigurations and obviously we pivoted and got domain admin uh and it was like lots of fun going through that pen test but I highly recommend
familiarizing yourself with some of the hack five tools um even like this OMG cable these things are the coolest thing ever the elite version actually got a new update called hix stealth or something like that uh where you can plug it into a device like say you're sending it to a client in a pen test and they plug it in to charge their phone or computer it'll work on both devices the phone and the computer but um it'll also create a reverse shell using Powershell on that victim device so you very quickly can get access just with a charging cable onto a victim device uh we'll talk more about those next demo but um again just like everything else
obviously these are abused heavily in recent years but they require a little pinch more knooow to to make work effectively uh this one's going to be a super quick slide mostly because I don't think I'm supposed to have it but um this is a fairly expensive tool especially with one of the uh Services they offer their Kaiju rolling code analyzer um it goes from $1,000 to $14,000 and uh in reference to our talk about the rolling codes earlier if your car or your garage is using or your home alarm is using a rolling code if this is able to get a copy of one of those rolling codes and they can submit it to an analyzer like hyu rolling code
analyzer they can actually Brew force it and generate more valid rolling like rolled code so uh they can use this device to still steal cars that are using rolling codes and to disable uh home alarm systems they can disable uh and hack like gate codes like an RFID reader the The Flipper can also fuzz RFID readers to mention but I think that's not a kid boy um they're very effective depending on on the version purchased and uh obviously some of these features well any of the devices you get are programmable the way you want um to get it pre-programmed with that home alarm features and all the juicy stuff uh for criminals is is only for law
enforcement and government so we can take a little peace of mind in that but if you work in or around law enforcement or government at all definitely take advantage of that to order one of these uh and then cuz I consider it a kind of a right of way um I don't care carry one in my everyday carry because I why I don't want to lose it plus um honestly you can do anything with this if you want to save a few thousand uh you can do anything with that with a procs Mark or a chameleon tiny um or actually hack RF would be the good way to go I would actually buy a hack RF way before I bought one of
these which that'll be for another another presentation too too uh this this slide is the evil ring this one is not something that's developed in oh yeah I'll be I'll be quick we'll be good this is a like a super cheap quick little demo I made um by the way if you're leaving right now and you have an NFC tag I hate to call you out but uh if that NFC tag is a winner then we might not be able to scan it um I have ways around that too I planned ahead uh so this one is super cheap it looks really ugly right now cuz I had to hot glue it together so um don't drop it
if you do buy one but uh they're sold by dangerous things which also sells um an implant kit like if you are so interested at all I actually do have a friend and and she was here uh for this presentation where if you like they they sell a needle with a sterilized um NFC chip so can inject it into your under your skin and then you have one of these NFC tags on in your hand instead of on a ring uh so you can be cooler than me but um this one only works on Android uh the demo I'm about to do only works on Android a lot of people just by me saying that probably
are cluing in right now I'm seeing a couple people oh um I I made this cuz it's most mostly educational to a non audience on why uh we should keep our devices close and we should have good security settings on those devices um so we'll do demo
time this is all we're all we're doing on C oh boy so I I put the put the ring on the phone so we'll we'll kill that session there we go all right so the idea here is that this ring is NFC enabled it's sold by dangerous things they're like 14 bucks I don't know what they are now but um if we hold on to this phone so I'm going to hold on to the phone it's going to scan the phone uh for a record and depending on the phone's firmware version and obviously what device you're attacking uh there's no interaction needed here um and there's a few exploits now where even if your APK file is an unknown APK
file you can bypass that feature on Android that's not part of the demo cuz it's a little bit longer but uh if you go on Google and and you search Android APK bypass uh there's a pretty new um method for this that came out so just with a couple of clicks here if we make sure it's on the internet and wait for that to go
through there we go so we got a reverse shell um so I'll take yeah pretty pretty quick e um so you can imagine if someone were making a phone call I mean that's easy and I've done it um so now hold the phone like this and what we're going to do is we're going to list the webcams on the phone and we see it still didn't wake up um if you take one eye and point it at the phone and one at the screen you'll see now I'm just kidding uh that hopefully I didn't hold it for too
long oh I did it I didn't get in front of it in time but now we can take fot photos through it without even waking up the screen uh or unlocking the phone or anything we can take photos but there's a lot more we can do too um which is kind of scary so if we hit help you can just um I because this is a a tech audience uh you can see you can see background apps um there's like you can start or stop processes you can start a reverse shell you can write files um View files so if you wanted to view photos or uh text messages or contacts um you can do
networking so if config normal commands system info you can record audio record the webcam take pictures blah blah blah um but one of my other favorite ones to show to people is geolocate and so this is a very very accurate latitude and longitude if you take that latitude and longitude right now and I guess actually we're we're done after this so I'll just for the sake of fun that long to
address and we'll just throw it in
here hopefully my wife if I isn't too
slow the link doesn't work cuz I I didn't want to expose my API key um yeah so I know there is a link there but it it won't work without a Google API key see uh so anyways if you look up that latitude and longitude um on Google it will show exactly what room we're in right now uh so if we zoomed in on the college um B Valley we would actually see we're in this room um if we were to to kind of look and overhead picture so like I told you guys um I will give you my GitHub repo um so if you want to make your own evil ring for 14 bucks or just with one
of the NFC tags if you were here early enough to grab one uh then go ahead and and grab that repo and program your your NFC tag or your ring um I was going to go over mitigations but again I'm preaching to the choir so basically things like don't don't remember your Wi-Fi network don't automatically connect to Wi-Fi um disable NFC when you're not using it disable Bluetooth when you're not using it uh don't trust anything monitor everything uh and then at it for K12 the big kicker here the big important point and especially if you're involved any kind of blue team activity with clients is Implement EDR Implement endpoint detection and response and it's very
important that you marry that with a Sim as well because if everything isn't communicating in a way that you know what is happening on your network well then this flipper could lead to a ransomware attack and so that's it for me today um if you got one of those NFC tags come up to the front and we'll scan it and whoever wins can bring it to the end ceremony with James Karen and uh we'll get your your Wi-Fi pineapple so whoever uh gets the winning tag will uh you'll get a Wi-Fi [Music] pineapple





