Federated Trust
Show transcript [en]
hi my name is thomas coppola i'm a three-time entrepreneur my last company we took from zero to 100 million revenue in five years i spent two and a half of those years trying to figure out how to share data between my team my employees and auditors customers vendors suppliers everyone else that i had to share data with this is a problem that we end up spending hundreds of thousands of dollars on dozens of people go through the same thing i ended up selling the company to private equity firm i never solved the problem so after i sold that company i did a lot of research and i started to really think about how to solve that problem and how
how we can better think about trust and aggregate right this is a problem that everyone has to deal with because trust used to be in a single organization right i hold a perimeter around all my stuff all my stuff's in some data center somewhere i have one one port of egress and ingress i can control who touches it who uses it what they do with it everything was done inside the perimeter of a single organization and i trusted my employees i trusted the people in my organization there was never the thought that somebody would do something malicious or some somebody would would snoop around the inside of my organization to take data to give it
to other people or pirate or sell or what have you but then as the cloud really expanded right not just the internet but really the cloud all that changed right so suddenly we have to leave ports open and we've got to connect to different cloud databases and all your employees are in sas applications and you don't know what half your employees are doing half the time so suddenly everything everything was everywhere and everybody wanted access to everything all the time and then how do you really manage that right and so what i realized was the cloud architecture as we know today has fundamentally broken the back of traditional security right and and all the websites have become data driven
everything we do now is connecting to some you know simple front end that's all data driven on the back end that has to be connected to real time to all the data and all the resources and all your pci because you know that's the best customer experience right and so the more i drove the more i drove into startups in other businesses the more i realized the magnitude of this problem and and i began to look at the question of you know how do we share that data all those libraries of information which is so important to our organization but how do we share in a way that we know it's properly handled shared securely
and managed appropriately right so how much easier would it be if we could if we could enable external parties to access your internal data exactly where you have it if you if you have your stuff stored in some ec2 bucket why can't you just somehow give really secure access to some third-party to that ec2 bucket where you don't have to move anything right so what if you had a single pane of glass that controlled access to applications documents services and you use it to govern both employees in your workplace as well as users outside your organization but with the same security and effectiveness that that's the question that we posed as a team and we tried to
figure out how to answer and we asked ourselves effectively three simple questions how do we determine the absolute validity of identities at the organizational level and then be assured that those identities are true and accurate to represent that identity outside of its owner's organization right so everyone today has an iam system everyone has them some sort of idp whether it's ldap is your ad duo octa what have you right so we figured that out as an industry but then and it works great inside the workplace but how do you how do you create portability among those identities how do you take identities that are known to your your internal workplace i am system and use them or extrapolate them and
still still have the efficacy to know that they're certain outside of their organization that's the first question we asked once we figured out the identities question we began to think how do we use those identities in a cross-organized organizational manner to co-author policies between organizations right you can write policies day and night and all of us have done this we'll read policies that govern the workplace or or the workers within our organization but now i want to invite someone outside my organization to access documents inside my organization and so how do i how do i do that effectively and ideally i would co-author a policy i would i would determine the the the heuristics the specifics all the
parameters that were critical to my security architecture and i would tell those to that third party and then i would create conditions additional parameters that that third party would have to adhere to right so you've got to be using your work email you've got to be on your your a a work lap a work desktop or maybe everyone's going to be on a laptop or maybe you can only do it between business hours or maybe it has to be from a a us-based ip address or whatever you could come up with a hundred different parameters that would fit your security architecture based on your own your own your needs and issues right so how do we co-author policies between two
disparate organizations so that we can control access to assets inside of our own organization that's really the second question that we asked and the third question we asked was once we're if we can create dynamic policies that are co-authored between two different organizations then how do we ensure a hierarchical understanding to ensure that only the right people have access to the right data and the right assets at the right time so that that even though you have multiple parties co-authoring a policy potentially with multiple idps involved that we always obey the owner's rules the the the owner of the of the asset of the data so how do you create a hierarchical structure between the the identities
and the the architecture of the applications to know that only the right people are accessing the data as described or as demanded by the owner of that data that's the third question that we pose to ourselves and so what we did or what we came up with was something that we call federated trust management which really in a simple terms is a summary of the who the what and the how anyone internal user or external users are accessing data and resources that we the owner of the data control so we talked a little bit about the who so let's go back to that for us the who became the iam of the iam industry is a 13 billion dollar industry
jour has you know really figured out how to federate workload or manage workload identity federation federated identity is super popular today everyone's at least running ldap and so um the who for us always becomes that whatever corporation whatever companies single source of truth whether it's an ldap an idp an external party like an actor or a duo what have you that's the easiest way to manage the who then we build hooks to be able to take that who from other organizations and pull those those tokens and information that we need out of those jwts so that we can use it to create what would become like almost an avatar right an avatar of that identity but in
in our own platform the what always goes back to the author of of who's controlling the asset so it could be a service an application a data store um anything you can put behind so any kind of api and so the the what is always focused from the point of the owner of the asset what does the owner of the asset control and how does he want to share with other people the how becomes the third piece right because people today everyone works remote everyone has multiple devices everyone is mobile it's very hard to control those people and so we enable customers to to create heuristics around how people are accessing that data and you can come up with dozens of
parameters from the time the geos fencing the hardware used the specifics the terms the read write the control can i download can i copy all of that and so there's a there's a whole set of tools today that we look at that everyone's familiar with to control or create parameters around how people can access that data once we once we figured that question out then we started to figure out wow if we could actually if we could actually co-author dynamic policies between multiple parties not two not three could be five but if we could co-author dynamic policies between multiple parties then we got this this crazy amount of benefit all of a sudden right we had
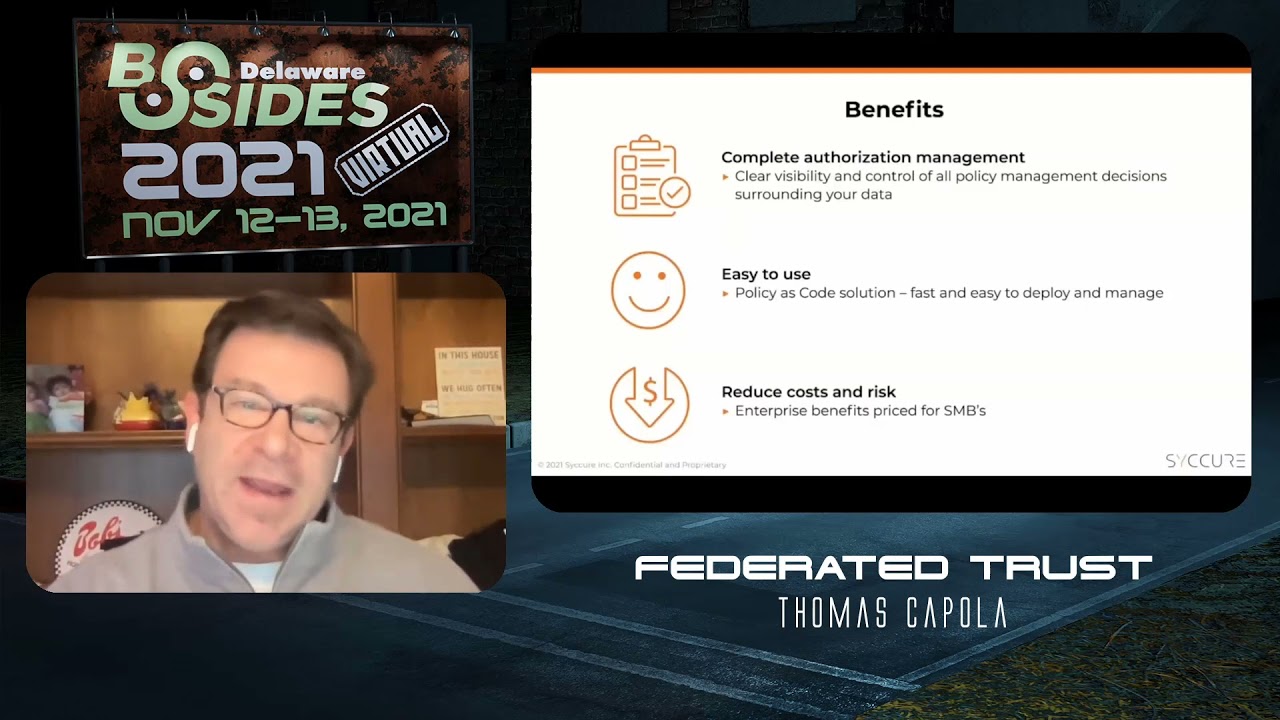
clear visibility for all permissions under a single pane of glass right we we could we could reduce the workload of sharing critical data inside company a and allowing company to share that data with company b or c or d or what have you in in hours or minutes let alone days and weeks that it would normally take to create the connections this the standardized connections between multiple organizations federated trust enables customers to define granular rules around who what and how people can access their critical data and asset services applications what have you while always maintaining absolute control over the entitlement rights surrounding that data and that word control is the key because with federated trust you gain control
you gain visibility and you can do it at an exceptionally lower cost than you would really any other solution we found federation federated trust extends an organization's iim system to both push and pull contextual intelligence related to one's organizational identities and then use those identities to co-author policies that were governed also in another organization so we simply become almost a middleware platform where you can exchange keys because it's all about aligning the token requests needed to access whatever application or service you're trying to demand to your idp is still going to be the single source because any any any application in your organization is always going to go to your company's idp the key is that we help that
company's idp reach outside of the extensions of that organization so that we can we can create better jwts better better jwts with more information about both the off and function the access function as well as the auth z function the authorization function and by combining all that data in the same jwt that when it gets to the application then we have a much more granular effect on the application for what people are allowed to do or not do with that application and what data they are or aren't allowed to access right so it's important for for technical people because creating trust across boundaries solves this this intractable problem which today has been solved candidly by the
enterprise crew but you know the enterprise applications today that saw this start in the hundreds and go to the you know multiple hundreds of thousands of dollars and for us it was unrealistic i'm a startup guy right so my whole universe is startup people and you got 10 people in a 2 million budget you're you're not going to spend you know 250 000 on you know federated trust across sale point or whatever else you have to figure out right you need a simple way to tap into your ldap or google or g suite or what have you and be able to federate trust across boundaries right um what we did was create a platform that
enables people to do that very very seamlessly by using all the same tools they have half the people we we work with simply use ldap and that's fine because we can stack that behind an api we can use your ldap as your single source of truth for your for your employees and your identities and still be able to pull that forward and co-author policies written into block um which i'll talk about in one second so for us for for guys in the startup community federated trust is the only method to do it because it's super simple super cost effective and you can create these cross organizational workflows in literally minutes you can write policies with two three four five other parties
let them sign off and and accept that everyone hits the same parameters and you can do that and it takes 20 minutes not you know two days or two weeks so for us we view it as critical that we have to build ways for information and assets including access applications and apis and everything from workstations to iot to be able to be trusted across organizational lines today we talked to dozens of prospects who who have you know iot devices that they need to share information with regulators or they need to share information with their suppliers or vendors and taking that speci those specifics of data in real time basis and and extrapolating it and then trying to
kind of collate it to share with people outside their organization is becomes this monstrous disaster to do and so we we keep telling people leave your data inside your organization wherever you have it wherever your employees are used to getting at worry about the focus of having absolute certainty over the policies and the parameters that are used to allow external parties to access that data it's a very uh it's a very google beyond corp approach but it works amazingly well i know i know that now that if we need to share a library with a partner that the authorization that they get access and use and process that information is based on something we can
trust even across organizational lines because we co-authored the policy and we're using verify verifiable identities to manage the access to those resources so how do we do it and it's this is actually you know it sounds pretty simple it is pretty simple we write dynamic policies which we didn't invent hashicorp osopolar opa styro the guys at cyra are very good at writing dynamic policies so we write dynamic policies but we write them to block and we combine that with the use of verify of all identities to create what we call federated trust so we asked earlier and we talked about the verifying the identities of the people or or the parties that are requesting access it always comes down
to an individual's iam system or idp provider it's that simple and it's a great place to start and people invested a lot of money in the i am framework today so we just we leverage that right we also talked about you know how to create immutability or how to create certainty around those policies that were running around call co-authorizations and as you guys know um a lot of the work in the hyperledger universe today allows you to create chains and code chains and sub chains we do the same thing we simply use hyper ledger fabric to extend instances of block between one party to another and that way they can co-author policy which is then going to be written into block
so it creates a phenomenal analytical trail it's phenomenal for your auditors it's phenomenal for compliance because you can pre-define from a compliance standard everything you have to have happen i i know that my is pci compliant okay here's the 18 things that all of your policies have to conform to as it relates to accessing data around those pci parameters so you can pre-pre-load in block everything you're going to have to do increase in order to create a policy that's going to that's going to grant people or deny people access around those pci assets so you get right up the curve way quicker and by doing in block you get this immutable record between all the parties
of what's happened and more critically of everything that's not happened so for us every time there's a request to access a piece of data it hits block if we evaluate the policy in real time against real-time parameters we check all the other external metadata and parameters that we have to do that's going to be able to fulfill that policy once all those things click we issue a request token to the user that they can then hit the application so it's like real-time dynamic authorization and authentication of every user every time to every asset based on policy that's written and blocked this becomes immutable so you get this fantastical audit trail of everything that has and hasn't happened
around the data in question so when you go back to your auditor and you say you know let's discuss my pci compliance and you want to talk about who has and hasn't access your pci data you have this fantastical record of every request that's hit the block since then and all the parameters surrounding it which creates great analytics for your compliance and regulatory framework so um we use blockchain we use simple templates and we use policy as code policy is code where you can build everything in your infrastructure today around you know everything's policy is code security is code is finally getting there we're not the only ones to do it there's four or five good good really solid
players in the marketplace that are doing this today but if you're building infrastructure as code and you're building application as code and you're building services as code you've got to figure out how to start writing policy as code and security is code to really match the dynamic capabilities of your policy and your authorization and your authentication systems which should match the scalability the the dynamicism of the rest of your infrastructure as it relates to scale particularly in like retail apps consumer apps anything anything that has a hyper scale back back end which is scaling in demand to the front end so for us excuse me for us now if if i if i have a vendor who i
have connected to an api but wants to send me malicious data that i'm not i'm sure about that doesn't happen you know could a prime contractor on our contract pull data from our source code database you know no because everything's only going to be read only our data is always under control even once we've given it access to someone else because everything is on a time-based short-term token which has expiration rates predetermined by my policy rules and my compliance standards so federated trust is all about controlling access and authorization with plenty of abilities to limit that access and even cut it off it's easy we have customers that are highly highly regulated highly highly secretive so you get access tokens that
are good for minutes seconds sometimes and if anything is not right they'll simply cut access to the data rather than rather than bend or make exceptions it's good in some cases it's frustrating in others so how does it really affect information security well red team testing for us got a lot more interesting that's for sure and blue team testing got a little bit easier though right so with a centralized source of authorization blue teams can feed that data to a scene where they can use any products built in analytics functions to filter and sort and look for anomalies because it's really centralized authorization which is managed in a distributed manner that's the power of block by tying
dynamic policies to block it gives us the ability to have a single source of truth as it relates to policies but it allows us a dynamic distributed method and different and different policy decision points to enforce those policies so again compliance becomes a lot easier because because a centralized source of authorization with immutable transactions and distributed consensus you have a fantastic way to get wonderful analytics out of the system right there's no there's no way to tamper with the single source of truth you also have great visibility into the access and who's doing what and who's touched what and on what terms so for companies which 30 years ago were single-celled organisms you know living
in a in their castle of a parameter where they could control all their data and knew what their users were always doing right now it's time to really move past that right this is what federated trust is all about it's time to build pathways and trust among functional subsystems between your parties and different vendors to to enable a more seamless sense of functionality not just for your customers which is always the the paramount but really for employees especially in today's distributed workforce right we have to have federated trust we have to build ways for information and assets including access applications apis workstations etc to be trusted by and across organizational lines right that's the key to what we have to do i
think that we have a great approach to it i'd love to talk to anybody in more detail about how we do it the specifics of how we write to block how we use ledger and how we build trust across boundaries in an inner organizational way thank you so much for your time and attention i appreciate it my name is thomas coppola i'm the ceo of secure and i appreciate your time and attention thanks





