Living Off the Land: Windows Post-Exploitation with Built-in Tools

Show original YouTube description
Show transcript [en]
all right i'm chris this is matt we're uh giving this talk living off the land and the minimalist guy the windows post exploitation so what we're actually talking about is the fact that defense is real we heard this morning uh blue teams are getting better right you guys are all here um just by showing you the blue team awesome testers
so well terrain network defenders and admins the the blue teams are getting a lot better so really it's kind of like up your game what's the next spell it's actually the use built-in tools not introducing things so we're going to talk about wmic and nsh and something that we're kind of fond of uh windows powershell so if you're not the right talk
is all right so what is homesteading in the enterprise what are we talking about we're talking about post exploitation right we've already delivered our payload we've sent efficient email about some web exploitation web vulnerability and excluded that work in the enterprise how do we stay there how do we avoid detection how do we live there for as long as we can get as much data as we can and really that comes down to living in memory the more you write to this more likely you be caught by antivirus or other software that's actively looking for new or strange things so we use the tools that are already there use the protocols that are active and being used so you
don't stand out on the network side either you don't talk when the network is quiet so if you see things going on at 3 o'clock in the morning because you have your interpreter checking in at 3 o'clock and then 3 30 and then 3 45 and they come in the next day that's a really easy way to get caught and another thing that i like to do is use their infrastructure if you're an attacker or a red team use their infrastructure against them demanding control from air servers use what they are using we'll talk about that all right so throughout this talk we're going to be talking about the traditional way that pentesters will do
things which is the minimalist way which is generally the way chris and i do stuff called a now i just want to preface everything just because i'm describing something as the traditional way that a professor would accomplish a task in a post-expectation environment it doesn't mean it's the wrong way and you're still going to see the techniques that we describe as the traditional way all the time right all right so in uh in your traditional post-exploitation environment gonna do well they are most likely gonna want to upload binders right so they're gonna do everything that they can to avoid antibiotics so say they want to run uh interpreter payload right it's really easy to generate from msf console
uh it's beautiful you run it through an encoder a bunch of times so you'll run it through the shakatika knock encoder a thousand times hoping that it won't fly against myers well yeah that's effective some of the time but the bottom line is you're still running an executable that's on the disc potentially susceptible to being taught there's mimikats which is a fantastic tool i love it it's designed to capture passwords memory does a great job at it but again it's also a binary so in the case where i would want to limit that i would want to do it offline so there's actually a new feature in it that allows you to analyze a windows crash
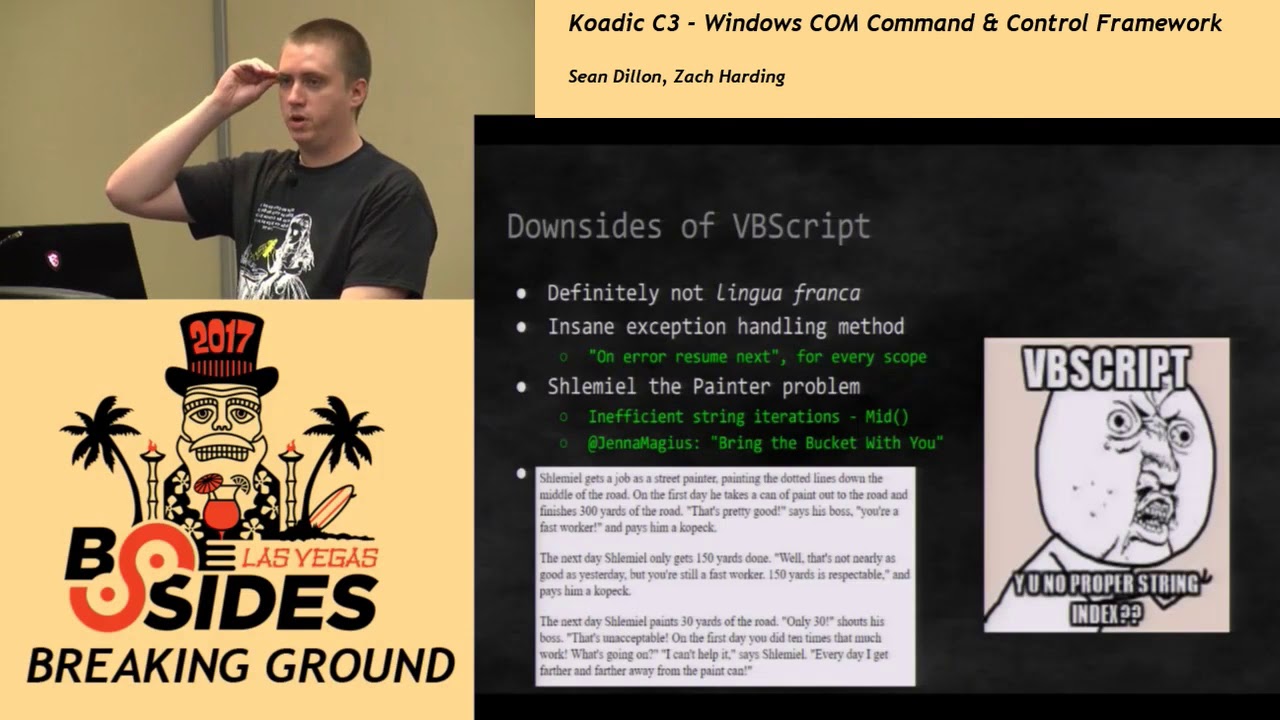
build so you get a crash cell which you can get as a user with no elevated privileges and pull passwords out of memory from the lcs.exe crashdrum and there's actually a tool in powerschooling which is our post-exploitation framework powershell that will generate a crash challenge so you can certainly upload scripts baby script and back scripts that have been around forever you know 20 plus years they certainly have their place but you do have to drop those scripts to disk uh bb scripts i would say is only slightly more powerful than batch i like to say that the vg script is just bashed with access to compound such as slight additional functionality but again you have to drop the tools
now for minimalist post-exploitation you're staying resident in memory using the existing tools on disk so two of the tools that i really like to use built-in besides powershell our wmsc which gives you which allow you to exfiltrate a ton of data from the network and nsh which allows you to do the same thing but you can also pivot through that sh and wmic as well and then of course there's powershell so with vbscript and that again you have to drop everything to this with powershell you have that option but you also have the option to run everything in a one liner i'm going to talk about how chris and i do that all right so a little a little bit of
background for powershell raise the hands who here is using powershell so you're probably already familiar with how powerful it is but as an attacker it's awesome so it's one a scripting language two it's also a dot-net encoder so you have the entire.net framework library available to you which gives you access to say creating sockets using crypto libraries but it also has some cool functionality called pmo and reflection which allow you to get to the low level and execute the low level payloads that say your traditional execute will run so if there's a binary that you want to execute on this there's absolutely no reason that you can't do that in powershell right and again you don't need to
execute anything from this uh and so baby script and batch again it's not as powerful it doesn't give you native execution all right uh execution policy so whenever i talk to anyone about the offensive uses of powershell they're like well i could block all that with the execution policies right because that's just going to stop all of your malicious scripts outright well again i said you can run everything from a one-liner command line completely by passing the execution policy so what is the execution policy by default in powershell it has the restricted execution policy which makes it so that basically you can only run scripts that are signed by microsoft well microsoft gave you the ability to just
provide the bypass switch on the command line so microsoft's mentality was you know it's not a true robust security feature really the intended purpose of it was to prevent unintended scripts from being executed so if you got a pitching email with a mobile show's ps1 script and some dumb user decided to double click on that well for one it's not gonna execute and two by default the default file association for powershell scripts is notepad so it's just gonna open up the contents of
um there's a really awesome feature which personally uses all the time to where you can basically c4 encode your commands uh and so you just provide everything on the command line so that does provide like an additional layer of optimization
but it is really nice just to kind of help hide the tracks and it does enable you to have really complex scripts you know thousands of lines compressed into a single base64 so this example here is pretty cool it's not a well-known trick where if you're in powershell and you do cmd slash c echo and then you give your child script it'll automatically get 64 for the period because otherwise you'd have to use some dot net classes to encode it um that just allows process mortgages all right so chris and i prefer to do it we prefer to use powershell as a command stager so think of it like the equivalent of using curl to download your payload on the
linux box and then dot sourcing whatever your module script is this is the equivalent of that so iex is an alias for invoke expression and all we're doing here there's some there's a.net class or calling the download string method which is going to download our malicious script and then iex is going to execute that simple so what this allows is most scripts of an arbitrary size because at the command line i believe the character limit is going to be connected to something like that so if you have a large malicious script there's a lot of different powers for it this is
okay we'll talk about a couple different ways that we can do that going back to what he discussed before uh so for phishing emails i like to send macros and my macros now are really really simple um it's just a vba that is executing one so it's four lines in the macro and all it's doing is then executing the stager so that's all it's doing the actual payload is not in the vba just the download plus it's the powershell stager so that's one way
so here's an example of the typical payload payload that you want to execute once you count the constitution you want to get a buy chill so what is a bind shell well it's a payload that essentially listens for network fans and once you connect to that compromised machine you get a command prompt so there's a lot of ways to achieve that you know if you were masochistic you could certainly write your own shelters right here in payload there's a lot of built-in uh fine shell failures in the metasploit that you could output as an executable if you could run netpad that still works great there's no reason not to use it if you're not worried about
uh antivirus um you know if you are worried about antivirus we do have to have a script that helps bypass flight signatures like this so it doesn't doesn't help get past your
uh yeah i've been doing some shockwave research recently and i did develop just a perfect concept by shell that when i compile it for c the x64 version does not black so there was a bunch of likes if you want to do hold on you like you may want to check that out i ran out of my exponents okay so we talked about the way uh the traditional way of getting design show so uh a buy show is something listening on the target that you can send commands to and then it returns stuff back to you so you can come in most of the time anyone can come in after you so buy themselves attributes are not good
for pen testers but attackers use them all the time one simpler method without authentication is if you compromise a box that has one desktop and you are able to get to system level privileges you can copy uh cnd.exe over the set hc exe system32 and then from that point on if you ever want to connect back to the box you connect over 3389 through rdp and you send the shift key five times and then a command prompt system well you've not logged in you've not created any logs and you've got a system command prompt which has worked in some rare cases so a quick note about that is uh nla which is in the latest version of
mstsc.exe the remote desktop security feature that requires an authentication before connecting so requiring you to authenticate before it gives you the actual command to log in you might want to enable that for this uh reason invoke http backdoor i've got an early version of it on my github eventually i will meet the coding standards of matt's powersport project and it'll get moved over there i've used it a couple times if you've seen i've talked about hacking appliances i like to get into linux boxes first because they sit out on the internet and then i'll use those to go after the windows boxes so one way our commanding control the windows enterprise from you know say a cheap proxy or something
that's sitting out there on the internet is with with this http backdoor so it's just using a net class to start up a http listener that will receive commands and there's a little bit of authentication i'm working on and there's some encryption with https and appreciate aes key but currently in its proof of concept form you can send commands so that's an example of sending an umi and host name you just base64 encode the command and you hand it as a session so you can use um curl w get whatever a browser if you want to and it works just like a web shell on the boxes so you can deploy this out and uh and command it that way
but the biggest thing with that is you're not in both of these cases we're not introducing any new binaries even though we're overwriting something which is detectable and we've got a new import listing also detectable but we're not adding a new binary that's now listening that can be found by av none of these none of the things we're suggesting are foolproof or magic waves there are always going to be ways to detect this stuff so we're trying to push on the blue side as well to start looking beyond did this a new dll get dropped in system 32 did a new executable and dropping all users startup look beyond that to other things like where did this port this listener show
up and then maybe start looking at memory currents etc all right so privilege escalation so uh pet testers how do you normally do a privilege escalation on a windows box so you get instead of phishing email and you get user get system right right everyone uses it it's awesome does everyone know what gek system is doing in the interpreter but um get systems of post exploitation command interpreter where you basically just type get system and then it tells you've got system via one of i think they're up to five techniques now in this case it's uh technique four so four is actually a tetrapod um which is an old privilege escalation exploit so it's trying the
local privilege of escalation exploits and then hopefully you get it uh it does a little silly stuff like schedules a task using the old task scheduler method it does all that stuff for you and it's generally pretty effective another one i want to plug is srv check um which kind of holds but it's checked for uh bad service permissions that allow a standard user to stop the service replace the binary and restart it so services generally run this system so that's an easy way to do that by default an xp xp with no service pack and service pack one had system services that were vulnerable now you really only find like third party you're super easy to get system there is
that usually effective against a fully patched system absolutely not if you're a fantastic you have ran into multiple cases where not only is guest system that works a b product is you saw that exploit flagged it shuts your shell down and you're done so i don't typically ever run get system on anything like ccdc or like capture the flag events because most hips most modern products are going to catch one of specifically hydropod one of the ways that it's trying to further decimally we would certainly prefer to exploit misconfiguration versus vulnerabilities of fire right because there's a more susceptible thing called so going back to the whole minimalist thing all the stuff we're trying to do about
exploits i mean the majority of enterprise compromise can happen without ever throwing a single x point so instead of trying to throw exploits kids plot for an example um why don't we just go look for passwords so this it's unbelievable if you're a pentester you know this but if you're not looking for passwords in your enterprise and you decide to do it on monday you're going to find a domain admin password somewhere and it's going to scare scares you scare you to death but that's really probably 90 of the the actual privilege escalation that i do comes from these methods so unattend.xml lots of different deployment scripts that are out there people are using powershell now and making in the scripts
are picking in the credentials which is terrible uh get 2pdp password does anyone know what has anyone seen group policy preference passwords a couple of people so the rest of you uh we're going to do a demo here in a second and you're going to be shocked uh with this awesome feature they introduced in 2008 uh and then here's another method that was very effective when we're an army red team one of our our one of the other operators suggested this and i thought it was a terrible idea coming from windows enterprise background well let's just guess password so let's just look at what most people are saying the password so we have these long
complexity requirements 16 character passwords and we've got to have all kinds of crazy stuff in there so he was like well what are the odds someone's going to use a keyboard pattern so now all we need to do is do some recon there's going to be a great recon talk later do some recon come up with the names of all the admins use that with this common password this keyboard pattern this password 124 whatever we'll take one password try it for all the users and i know of at least probably ten examples where the first day we were done because we did that yeah we generate a lot of logs but we only tried one password
against every account we didn't lock any accounts out and we got one that's all you need so you get one you move on from there so guessing passwords is insanely effective so we're gonna do a demo
so this is a low privilege domain user logging in right here just showing up in the day and they're like oh i want to install this really cool thing i've installed at home uh e and c do you everyone know what what dnc is because i want my desktop at home so we're going to go ahead and try to run it but you know users who want to install vnc typically don't have admin interviews hopefully so mr normal user is going to try to log in it doesn't have admin rights because you don't give advance to everyone right so group policy preferences so now we're enforcing the same password on every single box which is a nightmare for
attacks like class to hash but with this great easy feature that they originally plugged everyone should be doing this we can enforce with group policies which the policy is awesome we can make sure the same password is on every single box so mr normal users heard about power split somehow and besides that he's going to download get gpt password which is just a powershell function so even though they're all about ps1s we don't have ever call them they're just functions you've got to call them yourself it's going to open up as a normal user open up powershell and a simple bypass so we run this who in mind to just make sure you didn't magically give ads
so then all you can do is copy and paste the function so we're going to dot sources essentially paste it into the interpreter the interpreter does not enforce your execution policy at all so now we can call the function and that's all you have to do to run this third there's nothing you have to pass as a parameter and then bam he sees that admin password the admin username has changed and has presenters and the password is recycling times three for the win so it goes back you can now try that password you have no way to log who did it other than who's simultaneously logged in but you really don't know who did this
and there are a lot of enterprises that this is deployed in and they have no idea until pentester shows up and does this to them that it's this easy for their admin password to be discovered the other thing that you if you go on monday and you disable it great also go to the domain controller and go get the old group policy object where the password is encrypted with a pre-shared key that they have on technet um don't delete that because your old password could be as valuable as your current password if there's some sort of a trend or some box that that doesn't get pushed to so right a normal user's just going to
install vnc but we're going to take that and immediately push out through a message that matt's going to talk about to push out actual powershell which i'll interpret whatever we want to every single box that that password is on so maybe this is a stupid question but why does your normal user have a public id address they can expose me and see it in the first place that was just a demon
right exactly um if you've seen any of the new like hyper fast scanner software that's out there it's like it's getting the whole internet uh do that but it's a c-band app right so zmapp you can scan one port in the entire
and if you don't know uh which pnc old b and c is vulnerable to authentication bypass so you can just properly hit 10 boxes and take it over to their stream which is um yeah
so then we'll show you exactly what we do at that point in two seconds we have a show and we'll show you that in a second the residential networks if there's a surprising number of completely unauthenticated yeah exactly all right so we're redirected so what are we talking about for redirection you get out uh say say you pop up a website and you're on a box that's in the dmz and you want to pivot through crazy windows box and you want to pivot through something you can access a closed port on the internet or from somewhere else and you want to use that to then give it and so you use port redirection so what anybody you see this list any
contest use anything else to accomplish i mean that are pretty standard tools that uh been taught in different uh fantastic classes uh but they all most of them still work so you set up the box to listen on say 443 is closed on the internet you say forward this to this remote 3389 and then you just connect your rdp from the internet well you can do it with a tool um that's already there netsh will actually do this for you uh i found this in windows documentation several years ago it's been talked about at a uh derbyfound talk a couple years ago chris gates and rob fuller talked about it in their talk but it's that easy to set up on a
windows box for it to listen for any connections so now you can start playing with admins and network defenders you can start pivoting and redirecting all your traffic around so in one case i actually use three redirections because they were so actively killing us so we would do that then they would catch it and we'd redirect through something else but once we had once we got here in admin there really wasn't no way for them to figure out where we actually were persisting you're only persisting on one box but through redirection by doing this remotely through wmi which matt will talk about we were able to set these redirections up all over the place and it made it very difficult to
detect all right so you know you may want to deploy a keylogger as well you know you may want to capture passwords you know see what network resources people are going to right pretty self-explanatory there's plenty of payloads out there that will do key logging for you um majority of them are binary aspirables they drop off discs that are going to be flagged as instantaneously by antivirus some smart people wrote out their keylogger and c sharp which is generally not as susceptible to being taught by antivirus for whatever reason av just does not have the introspection and to manage type holes as they do unmanaged like we're all native to people binaries um so if you're thinking about you know
writing malicious payloads c-sharp is definitely a way to go and that's essentially all we utilize in powershell it's not c-sharp but dot-net to bypass the same thing to say so what what does a keylogger typically do how's it implemented well most of them typically just are in a polling loop calling the function get async state and just to see which keys happen to be depressed at that polling interval uh there are more advanced ways to do it there are better ways to do it but um for example you can call the function set windows hook ex but that that requires that you draw the day well so essentially all chris and i did was just
implement that same logic that pulling logic of calling get a sap state and did it in powershell so we're not dropping anything
all right so running in memory is great you know do it as long as you possibly can but at some point you're probably going to want to survive a reboot so that's why you want to persist so there's plenty of plenty of ways that you can persist you can drop an attribute hole or script into the user startup directory you can modify registry fees so that your payload runs every time you do it uh there's the ad scheduler uh sch tasks on uh i believe it's vista forward machines to get your payload running well those are all insanely easy to detect you just run the system terminals autoruns tool and it'll show you all of those
persistent mechanisms so my aim was to develop a technique that used powershell to persist all the network without being detected via normal needs and i'm using wmi so it's not very well known but there's actually a system where there's a service that runs a system that's constantly pulling four commands to execute all you have to do is use wmi to register an event that when that event is triggered it fires and you also have to register a consumer to execute your payload so that's what i'm using uh powershell to accomplish and this technique is not affected it uses some relatively obscure wmi syntax there's a whole language within wmi wql with my query language to accomplish
this the first time that i ever heard of this technique being used was with stuxnet only they were using it to get privilege escalation so they had an arbitrary file right vulnerability and so they can write anywhere on the disk so some really smart people figured out that if you drop what's called a mob file it's basically a compiled payload for wi events and descriptions if you drop the specially crafted file into windows system 32 wbem that you would hit that polling loop that bronze system and then you get code execution well i'm using that same polling mechanism just to get persistence so what i'll do is i'll use the wmi event subscription uh to detect when
your system has been moved for five minutes
all right so the last thing kind of something i've talked about in other talks on the persistence so if you drop hashes and you have all the credentials really if there's any way to authenticate with those credentials from the outside from the internet there's no reason to actually persist you can come back in whenever you want so there's a vpn uh bnc rdp if any of those things exist there's no reason to persist you come in when you want to take what you want you leave you don't leave anything behind so once you've dumped the hashes it has anyone seen the pasta hatch firefox it's in the pasta suite it's in cali it wasn't backtracking so uh a buddy of
ours wrote that basically you patched firefox to take a hash instead of uh password so once you've dumped the hashes from the domain controller you come back in and you know dedicate to owa sharepoint anything that has ntlm ssp pushed out to the internet you can come back in and authenticate that way just imagine how easy it is to have persistence when you can log in as the ceo into owa that way citrix is another example of ways of persisting without actually uploading anything or leaving anything behind all right so packing captures i pack captures are awesome and i've used an interpreter uh packing capture utility for a long time there are a couple ways
to detect it i've been told uh on red team someone's called in incident handlers and they've detected that that specific thing i'm not really familiar with all the ways that it can be detected but it does a great job of giving you captures once you've elevated uh privileges so capturing all the packets sometimes you're you're not just getting the authentication of the box that you're on you're also seeing other things going across the network you can catch things like nclm v2 credentials coming across there are lots of reasons why you would want to do a packet capture you're doing web exploitation you get on a windows box you can then see all the users authenticating they're using basic
authentication at that point you're just collecting credentials i've seen i was on a contest with someone that installed wind keycap uh i would generally never do that and i'll show you why i wouldn't do that but there are some uh classes out there that teach that uh installing what you've got within the command line so that you can do backup captures he leaves a huge forensic footprint should be pretty obvious there's a windows packing capture utility anyone know what it is not medicine but something else come on there we go all right so netbond is microsoft's capture utility windows admins seem to not really know about it occasionally i see it deployed if that's there
use it no need to use sh just use that tool it's typically only on servers but this is pretty cool i was helping somebody work through uh an incident handling scenario where they actually were tipped off that the red team was there which should not be doing but he was tipped off so he kind of figured out the box that they were on and he was like how are they on this box so uh he didn't want to tip them off but he wanted to do packer captures he didn't want to install anything on the box so this is what we settled on doing in that case but it has obvious uh offensive um uses as well so you just create a
capture with nsh and you can do full pack captures without what format is that it's it's going to be in uh cap and it's actually going to have some interesting extra data um so if you want to open it up in something other than netmar so you have to basically use netbond to view the data if you want to open it up you can output from netmon to xml and then strip the extra trace there's two extra fields strip that out through your python or i use powershell to do it and then it's very painful and then you end up with something that wireshark that the wireshark can import at that point so the reverse shell
is ideal to a bind shell what it does is it falls out over the network to your listening machine and shovels your shell over to the box that you control and the reason that's better is because it'll bypass um it'll buy five house power orders so you could shovel yourself over four four four three or four eight the the same problems apply if you want if you want to execute your payload you may want to do that by dropping a binary you're going to run into av again you could pack your binary those are triggered all the time for example the gpx binary it has the uvx string and the sections which are easily flagged so it
would be like it's suspicious a lot of babies now are just analyzing the entropy of an executable so if the entropy of your binary is too high it's just automatically identifying suspicious you can certainly generate your own custom binary and veil is an awesome tool to achieve that so in in one of the configurations you can package your payload into the python interpreter and that to my knowledge is not the mere fact of running the python interpreter
you can do the same thing in powershell only you're not going to be touching with this so i i wrote a function called invoke shellfoot and i added some metasploit functionality to it so it will talk over http https so you set up your metasploit listener on the machine that you control you run into a shell code provide the payload in this case we're using https configure the ip that you can call out to and report it balance the payload and sets the shell back out to all all in memory now so this i think i've referred to this it's the easiest way to get a show like ever so from any box on the internet you can
run that single command and that's going to call out to github pull down the function outsourcing and run it just like that that's all you have to do to get a show all right so dumping hashes the normal way i mean everyone should know a million ways to dump hashes because you run into lots of problems with this if you're a fan tester uh the poopest guys are working on some great updates fg.pww these are great tools i've been around a long time and uh they're they're still working on them which is awesome uh tim and mark wrote bss own which does uh volume shadow copy and we'll dump those things off for offline analysis
which has become very popular lately so uh with built-in tools um with vss owned you're doing the same thing but you've got to push that bd script right so you've got a right to do this so we wrote get password file which does the exact same thing uh dumps those those volume shadow copy things off for offline analysis but you can do it from the command line you don't actually have to upload the script um the there's power dump which was added to uh metasploit uh gabe kennedy which we didn't mention before but dave kennedy's powershell talk from defront a couple years ago kind of inspired us to start working with powershell um defcon 18 i think uh he had the original
execution policy bypass and all of that stuff so he's been hugely inspirational on a lot of this stuff i just had to use that top method i don't know if anyone's ever done that you can use reg.exe to save off hkom sanding system pull them off and use stamped up to pull the hashes out that way uh but just a quick thing on the password file it figures out whether it's on a dc or not and then we'll dump the ntds we'll find the actual location on tbs and give you that so it actually does pretty much everything for you taking screenshots doesn't matter if you own the dc right the ceo doesn't care he
wants to see a screenshot of the desktop so when you have your own custom background or you're not using noticeably this becomes kind of a challenge um so one way that i used to or i was taught to get around this is this little utility nerf command if anyone ever seen it it's got lots of little built-in functionality one of them is that uh you can take a screenshot so i would upload this and then call it using the command weight save screenshot and then you would have your screenshots and you downloaded it which was kind of cool if you're uploading a utility you're leaving stuff on the box that you shouldn't do i think
i've had a call before where someone like a year later found nerf band on a box that i've been on like did you leave this there yeah probably the only person that ever uses that so yeah so now we do it this way so i originally wrote get time screenshot because i was doing something uh pretty fast-paced so i had a short window and i was going to be hacking a whole bunch of stuff and i was using a linux vm on a windows box so i'm like i want to take screenshots every five seconds so that i can look at it and figure out what i did so that's what i actually did because stuff
happens so fast you can't keep track of all of it so then i can go back and say i look at that because so i like to key log myself which we talked about before uh which was the inspiration for our original powershell keylogger and to take screenshots but it obviously can be used to go after remote boxes take screenshots that way and then pull them back all right so today once we've compromised the machine and we want to spread deeper into the network we want to leverage pivoting to use one machine to compromise others typically the way that you would accomplish that is exec that's the tried and true method again that does get flagged
despite it being signed microsoft executable it's easily detectable and it says it sends credentials to the wire the way that we prefer to do it is using wmic so we'll queue up our malicious powershell command and you can specify slash node through there and it will spawn uh powershell.exe process on the remote machine you can accomplish the same exact thing leveraging wmy
all right command control c2 the um how do you guys do it pen testers you get a bps uh amazon you know one of those methods you can pour forward through some you know router or device that you purchase and put on the internet um you know you could get creative and create some uh some fun attribution to maintenance apt-1 get your bps out of china and so when they see the callbacks of china they freak out um if you're a red team that might make them take it more serious than they otherwise would uh the minimalist play is instead of standing up for your own infrastructure which is new and unknown go use things that
their users their enterprise is already talking out to so uh there's been a lot of recent stuff with dropbox and evernote and all that stuff is awesome and it's exactly what i'm talking about i've used twitter before i give a talk where i introduced anybody's twitter bot which just uses twitter as a c2 it's a powershell script that will call out and look for specific statuses twitter changed her api and i was using xml so i need to update that for the json stuff at some point but you can use blogspot pastebin but what i really like to do is look at their external infrastructure look for some way that i can comment on something
look at their actual social media sites on their facebook page is there something that they are going to that i could add something to even if it's just a number one or a great job and then i build that stuff in so great job equals command.exe you know bad job this is terrible equals run this command you can build all that logic into the script beforehand deploy it and then the rc2 is you creating a random user posting that message when it sees that message it then does something that way so you're using their own stuff against them if they've got a reiki site it's just too easy to go in there and do that as well
so being more finally over using irc for community control yeah i mean i typically we typically use https because that's really the only way that you're gonna get most of the organizations that we would go against are going to have a proxy so everybody needs to be proxy aware and it's going to have to go through human someone's going to look at all the traffic so it needs to look more legit that's kind of what we're preaching stay with it hide in the noise look like they're normal traffic and it's surprising how far you can live for long term engagements you can live for months and years in organizations using these methods so just a few built-in tools so we're not
introducing anything that might potentially be black later but yeah you know uh vimicats is great the day that it comes out with the new version it doesn't fly ap you deploy and you want to use it three or four weeks later when the signatures catch up with it it flags your burn they're calling in you know mandiants come find you that and that's bad so use the tools that are already there and uh and reduce your forensic footprint uh powershell's awesome microsoft did a great thing it gave defenders as well as offense an easier way to do things but if you're a admin or a defender all the ways that you can use powershell to make your job easier
i think are greater than the ways that an attacker are going to use powershell we've only really seen one public example russian malware that's using powershell but i've seen organizations that are reviewing their logs using powershell scripts and quickly finding bad things on their network uh we love any ideas that you guys have talk to us later um or right after any ideas for scripts that you like written you know at some point we run out of ideas and stuff to add their power support i write defensive scripts and put them on uh on my github occasionally so we're not just ranking guys so if you've got any of those ideas or you'd love if you'd like to contribute
something uh by all means so we'd like to thank all you guys for coming this is great um and the organizers the powershell security community is very small that's it that's it literally unless there are people that are i'm sure there are people out there that you know but and then the authors i think we've read every book that's out there on our show there's some great books and some great offers and then those are our blogs and our github pages and our twitter handle if you have any questions we generally answer questions on twitter or on our email shoot us an email i'm uh obscuresec gmail matt mike
so my question is what is the pun with max vlogging
and if anyone would like to contribute to powerpoint definitely us because we're always seeking new ideas and new scripts to add to the model anybody have any questions
so it'll be up there probably uh monday yeah and all the code for the most part is up on the github if there's anything else that you have a question on um feel free and if you see powershell being used by some malicious actor and you want to just tell us that that'd be great i find that stuff fascinating and i had to put in three hours to help people any other questions if you guys consider doing anything uh to just do a reverse shell where like you've got something persistent in the network talking outbound to 443 somewhere else and then you connect there kind of coming on a triangle so you're i mean most networks aren't doing
egress filtering so they'll never know if there's something going on so yeah well we typically go against organizations that have uh ssl scripting processes we do pretty high-end contests uh so the people that we're going actually it's kind of the reason that we've gone this route when we pushed on the powershell and uh just staying true to the work hours of the organization being super important
inspection of the traffic itself they need to be able to look at it and say this looks like real web traffic other if you if you could just pop a reverse shell out of 443 and not stay https compliant
yeah any other questions we'll be around for a while
10