Mystical Vulnerabilities: Exploring The Oddities In Cybersecurity - Massimo Morello
Show transcript [en]
as well uh thank you guys for being here so I'm MIM Morello I'm an associate information security specialist at the deche B and I mean the age probably is not relevant but still let's let's let's put it there and as he said I'm going to talk about vulnerabilities and mainly we will be focusing on vulnerabilities that um they are supposed to be so but in the end they turn out not to be so let's uh let's have a look um let's say the paper is a bit on a ironic streak we call them mystical because they have a lot of uh trades they they make them unique and in the end as I said they just create noise
and from governance perspective unfortunately it's a mess also from compliance perspective because you have a lot of high numbers and then in the end you don't have a process uh or or some tools to filter them out so H we call them like this because usually in the MVD they are disputed the is a dispute between the researchers who are filing them who are in the Quest for fame because having a CV in the resume is nice and everyone wants one and uh the the the actual uh you know the product uh managers who are uh disputing them so it's U it's it's really easy to see in MVD disputed vulnerabilities and another criteria we can say that
vulnerabilities can be mystical if they have unconventional method of exploitations or unpredictable predictable impact and we're going to see uh some of them uh yeah I mean that's uh that's what what happens uh most of the times uh hopefully not not many times to you hopefully um the let's say the research relevance uh from my perspective it's first of all sharing awareness spreading awareness for collaboration between us researchers vendors and so on then also exploring the Dynamics because we just find vulnerabilities in database and we don't know what's behind how to validate them and so on and uh another one can be developing some strategies uh of course we not going to change from scratch the
MVD because the whole internet is running uh on it and so on but uh we can add some layers to uh a bit um scheme out the noise uh yeah I would say we should bother because of uh because of this because it's cers some no uh vulnerability management it's strictly related to to asset inventory to management mainly and also unfortunately to compliance because there is always to comply so big numbers uh they are always a bit scary and we need a granular approach we need something that we can put as an ex lay layer and filter out the info so let's let's have some numbers because I'm I'm talking a lot about this and uh the fun fact while
researching is the fact that there are some papers out there uh like it's being studied actually in Academia the um inaccuracy of the MVD and also miter miter because it's the one feeding the MVD and uh 56% the is vulnerability type uh 85% root cause 38% you have the the percentages here and uh it was interesting to see that then also from threat perspective since we can easily say that unfortunately CVSs scores they are not so threat oriented then um it's oneir of the vulnerabilities they don't have a c uh we associated with that so you cannot link it back to a threat also uh cross site request forgery and and cross-site scripting um I there are 111
instances uh of um vulnerabilities missing the um user interaction which is needed I mean if uh it's this kind of vulnerability you need it and it's not there and also for cross site request forgery also 59 they are not super super super huge numbers but uh uh from a global recognized standard uh of course you expect that they don't miss this type of info um especially considering the vulnerability and then another fun fact is there are many bodies who are like the federal civilian department and agencies and the PCI Data security standard who are explicitly uh recommending to use the CVSs score as a risk score score and by definition is not so I think there is
something wrong there and uh I don't know it's under our nose and things under your nose are difficult to see usually even though they are closed so we need to spread a bit of awareness uh let's see a bit of cases because um the first case is vulner I call them non vulnerability bad intentional because it means that the vulnerability in the end is not a vulnerability okay and the bad intention is from the person who is filing that meaning that is some guy or girl out there they want a bit of Fame they want a CV on the resume so they they see something that they know is not a vulnerability but still they know it
will be Val it will be validated by the MVD they know it will be filed so they do it so let's have a look this is the CV and this is a second order SQL injection nice you have all the the the stuff out there uh do you want to know what's the product affected dvwa so I mean the it's actually still there the record so uh if you don't know I mean it's a platform with implemented uh uh thousands of vulnerabilities on purpose because it's a learning tool and the vulnerability stayed uh there in the MVD uh with a high score for some days uh five days then it got rejected uh but still it's Waring the fact that you uh
file something against nvd and uh sorry against dvwa and nvd says oh yes yes yes let's accept it then the second case no vulnerability but this time good intentions meaning that we can assume the person who filed that um had good intentions they say they know it's a vulnerability and they do it okay it's postgress and uh uh this is the vulnerability H why in the end is not a vulnerability because uh un trusted users cannot send this type of signals so in the end is not and uh any way uh n the nvd they accepted it and the status uh got rejected but again after active um let's say complain uh from the vendor otherwise it would have
stayed there but again it was accepted uh and which means there is not a filtering process there um yes now the other category uh we said mystical vulnerabilities either they are not vulnerabilities or yes they are but they are unpredictable and one of these cases uh I'm sorry to scare you out is not Halloween anymore but sometimes we see op SSL and heart bleed out there let's let's let's talk about that and then we forget um the why is it unusual first of all the score the initial score was uh 5.0 even though it affected 30 to 70% of of the global targeted systems then it moved to a 7.5 score which again a vulnerability that manages to create so
much pain uh highlights the fact that the CVSs score cannot be considered as a as a as a full score and that's it because 7.5% when you ha the word um let's say it misses a bit of granularity uh then there is of exploitation and then unconventional exploitation method and um uh interesting fact four four years ago which means 6 years after it was filed then still 200,000 machines were vulnerable uh yeah not good I don't know what's the current status I checked a bit but yeah that's uh that was not good that's uh I hope you change your password guys uh then uh let's talk about Solutions and best practices um again uh probably you are really
thrilled uh because you think I will change the MVD but the answer is as you cannot change the bgp and we know it's flowed but the holder inter internet runs around it then you need to start by the MVD and then you need to filter out some info so let's say the goal is contributing to more filter oriented mindset um both from technical people and not technical people because they see critical vulnerabilities and they think they needs to be patched but if you have a way to show that they're not critical then it's it's it's uh it's good and my suggestions which are either complementary to the MVD or maybe alternatively uh there are in terms of
culture scoring system decision making sources and databases so culture um the first uh solution is not even distant from the process because it's simply becoming a CNA so it's something obvious but at the same time uh open- Source projects that were really really overwhelmed by vulnerabilities they um started joining now because they understood that otherwise they would see a lot of vulnerabilities concerning them floating there and they will not be passing by them but they need to pass by them they need to be validated by them the downfall unfortunately is that there are still some white hats who are in the end are not white hats which are vendors that they get the CNA and they don't um
provide um much info to the MVD and they keep the vulnerability as uh on hold they can do they can keep it reserved if I'm not mistaken for 2 years and they the excuse is that they have uh big uh release Cycles so that's another thing let's say to fight unfortunately and then uh that's from culture perspective there is another thing if you think about bu bounties right there are there is an army of back bounties going around finding bus why don't we also incentivize people to validate vulnerability ities when it comes to you know inaccurate submissions that maybe they spread the cows and so on so an army of BU validators can be a
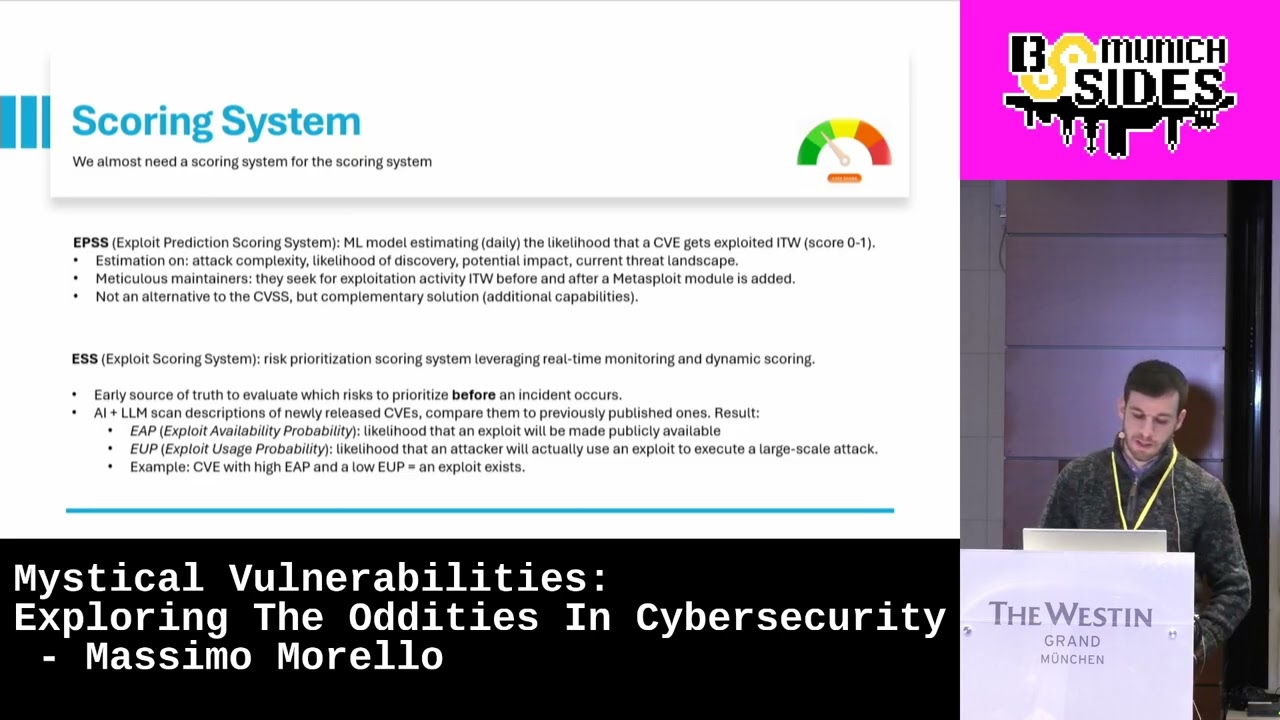
good one and I wrote this term back bounties because there are as I said there are some supposedly researchers who want a bit of Fame and and recognition so they beg you to you know to accept either their their their CV or they exploit the MVD or maybe they scan some domains and you find an email you are vulnerable uh please give me some money um I mean a bit summarized but I have some slides so I cannot go a bit more in deep than this scoring system uh we almost need a scoring system for the scoring system uh yeah unfortunately but yeah and then uh the solutions let's say complementary to what we already
discussed one of them can be the epss because first of all it's uh exploit which means threat oriented and it can be used not to replace of course the C the CVSs score but to filter out what is maybe critical but then is not exploitable for example okay so it's still a complimentary solution and also um it it can Works let's say a bit uh in the future let's say because it's a it's a predictive model and it gets a lot of Sear ver and see the patterns so it gets met exploit module exploit DP and and so on and uh it it can uh it can be a good Aid and the ESS if you didn't um hear
about that I think it's like a version um a bit more upgraded than the epss because it gives you two scores the exploit availability probability and exploit usage probability um it gets a lot of sources a lot from uh from Trend mro Trend Micro and so on non exploit catalog of cesa and so on and the the the nice thing why did I put in Bolt before because um most of the times when a cve gets uh released you don't have the CVSs scoree for a long time but with DSS every time a CV gets uh out then you already have a ESS score because it's based on historical data it sees the pattern it is what happened to similar
vulnerabilities and so on it sees if there are some um let's say hints of exploitations around and so on and it calculates two scores uh and uh if the exploit availability probability super super high doesn't matter what happens to the exploit usage probability we can already say that an exploit exists even if you're let's say again it's a forecast so that's uh how it works uh and then this is a bit let's say um Niche topic because it's related to table so uh it's uh I I thought to put it here to talk about that because um okay it's similar to some of them uh but uh the nice thing is that if you're talking about patching strategies and
Remediation strategies um remediating critical vulnerabilities based on CVSs scores okay if you take them you have a certain let's say time window but if you use the V if you use this one VPR you have way way way more efficient results as you can see 20 times more efficient in patching uh emerging exploitations in the wild and so on exploit code maturity uh it's uh so here are some numbers that uh I I can read but uh as you as you can see uh we can also discuss uh at the lunch break can't uh you can have uh you can have a look it's uh it's quite uh it's quite interesting then decision making uh this is another this is
another thing this time is not related to the scores but it's related to a decision because in the end vulnerability management it goes to patch management right so what do I patch first I mean we don't have uh we are not infinite uh like employees in the world and not everything can be automated and not to a certain uh you know uh it's always to to a certain extent so uh a stakeholder specific vulnerability categorization is basically a model OKAY cost benefit analysis uh that can you can also integrate with other methodologies and cisa implemented based on the template their um decision making model uh with different outcomes and the tree according I mean for what they did looks
like this it doesn't necessarily have to be a tree structure it can be something else but um uh you can see exploitation it can be active or not automatable it can be Yes Or Not So based on this you have a decision at the end and it you can use it to shape a single vulnerability management process so uh not not single vulnerabilities but single vulnerability management um processes let's say batches uh let's let's call it like this and you have four stages track attend uh so one requires uh you know maybe we take a look the other one close monitoring the other one involves the uh upper level and the last one management level then sources and
databases you have the one from uh um let's say if you want to have a bit of uh clean sources uh the one uh from the cloud security Alliance uh probably some of you heard of it but the good thing about this database is the fact that um informations there are collaborative everyone can collaborate and also in some security databases um some info are hidden and so on there is not that much visibility but here everything is a bit it's clean and is accessible to everyone and again it's collaborative so uh you can also think to make your vulnerability management process start from here and not from the MVD and another one which is super super
important is the open source because it's a uh for unfortunately Hot Topic in vulnerability management uh uh and uh you have the osv so open source version in schema that you can automate and you have the API they are accessible and uh the way they they do have a database and the way uh vulnerabilities look like the records they are like this so either you have the CV or you have another identif um identifier and once you open the instances you have a lot of information like um exploitations and and if there are some modules and so on uh but somehow you need to have a clear clear view when it comes to open source
libraries because there are supply chain vulnerabilities so so far before we were talking about vulnerabilities that in the end they turn out not to be vulnerabilities but now with Supply chains we have the opposite so vulnerabilities that are like m okay they're hidden I don't see them I don't do anything but in the end they turn out to be very very concerning like the solar winds example and and so many examples and uh uh thanks to this I mean it's a project by Google you have uh all the dependencies there you can uh you can you can search uh and uh you have a uh nice graph uh and U yeah uh and then uh the last one probably some of you
know but uh attacker KB I think uh as a source let's say to ah maybe you get concerned about the vulnerability maybe before doing something you know like a bit in a rush you can have a look uh to attack B not just because it has um a lot of uh uh fields that are nice to see but also because everything is complemented by besides a technical analysis also a comment sections by expert and H you have all the exploits listed but the comment section as you can see for example you see three views and two comments that two comments uh it might be also five or 10 it's nice because sometimes uh it involves um
maybe people who are closer to the vendor and so on but basically it's good for um scheming out the Panic that creates uh for for this uh conclusions um I would say lack of data Quality Security researchers they uh exploit put oversight so we have novel challenges because what we thought being white ahead so I find vulnerabilities for the sake of the word in the end they do it for fame they do it for the recognitions not all of them but um that's they they exploit the fact that the MVD doesn't check much so uh trust but verify approach unfortunately towards uh industry standards because everyone is recommending uh miter and MVD but uh you
also need to not trust them blindly the this is about the second slide which is also in Academia they're studying the inaccurate of the MVD and then as you could see there are interesting ID AIDS out there to like scheme out uh the noise and uh complement them uh with uh with uh with the CVSs core and and the CV so you can use them as an additional layer if you want to be threat oriented if you want to be exploitability oriented and so on so you could see and then now now the stage is yours I there is a lot of text here but it because maybe some people will not will not um
know about some of them I put three vulnerabilities okay the great worm solar winds and and then you have log for shell and uh uh there will be a yes that's maybe maybe some of you but uh me me not yet I I will I will be like that probably um and then you can choose your your fighter you have a mentimeter uh okay uh I will give you the QR code now and uh you can decide which one do you think is the like most mystical and the most uh unique vulnerability I will keep it here for like other 10 seconds uh but uh but yeah I wrote there also because they are bizarre and uh and so on and
you can choose your fighter there will be a textbox so if you don't like any of them or if they are too scary and you have like maybe tra for them then uh you can you can easily choose your fighter I think it's supposed to work you can try it out if uh if you [Laughter] want doesn't work no okay I open the oh W I did open the survey so if it doesn't work uh my bad ah wow o yeah uh we see the results later if you have suggestions is fine you have a text box and uh I'm curious about your uh insights and we have six mes which is
cool the Great great warm is not uh yeah 30 years ago
so so among the ones that we listed log for Shell seems to be the most mystical and I think I agree yeah there are a lot of reasons why and then yeah the trend is that one then we can also see the others [Music] cve 2000 oh wait this is a bit in the future I hope to live enough uh let's uh okay then I think I have some jokes here okay then uh overall we can say that the winner oh wow 2008 ooh 0166 so the winner is L for Shell but if uh any of you in the audience uh you know uh can have the the word maybe and then we pass we go to the questions for
5 minutes may I ask if you're not shy to share the details about CV 20080 166 I don't know where is the microphone ah nice oh thank you for the
input hey I added that one uh a long time ago there was the problem with the Debian project where they uh couldn't accurately or reliably create random numbers anymore and so all the SSL keys were like reduced to a very small set of SL Keys everybody had the same right and to this day I believe it's an intentional back door that was added to the deian project and nobody believes that but I do and so that's why I it thank you so much look at it I think it was the greatest CV ever thank you for the input now I believe it as well but I want to check a bit but uh thank you for the
input ER then um if you have any questions I uh just wanted to show the cat so now we can have the questions
uh first of all thanks for the talk was very interesting and I wanted to ask you for your personal opinion about epss because um we also deal a lot with uh a lot of vulnerabilities with high cbss and then for some of them you see super low epss do you really rely on on it to like kind of reduce the noise and say okay we don't take care of this or because I think it's a little bit not so transparent like where these sources are coming from or the like data of the exploitability so since it's a machine learning model uh first of all of course it's learning tweak by tweak twe and repeat twe and repeat and the besides
having historical data it's um the nice thing is that what you said might be true today but not be true tomorrow because the because they keep ingesting data they get it from uh they get it ex I mean meta exploit um and and exploit DB and uh and other other tools so I would say uh I wouldn't say go for that uh now but I can say that that there might be some there might be some noise there okay okay but uh I personally think that the fact that things evolve um dynamically it's for sure a good hint okay maybe you can say that it cannot be maybe reliable for things that don't have already some hints out there
but it will for sure be reliable when whenever they get some sources out there and they inest it then the score it's uh is nice and they will use it to learn for next time so it's always a evolving I would say yeah thank you thank you for the question okay we have one last question and then you could yeah empty stomach talk I'm sorry for that interesting topic um one of the things that I have concerns about when it comes to uh CVS cves is that quite often I mean there are it it creates a bit of a bubble because there are vulnerabilities that are that don't have a cve for various reasons either the vulnerability
researcher did not bother I know I'm guilty of that in the past um they might have released an advisory but it got no cve um or um you have the Developers for open source projects as well not just closed Source Who do not create uh the cve um and so on and so forth so and and you kind of lightly touched about this when you spoke about the supply chain uh um problems um what are your thoughts about you know having a bubble just because uh if you rely on uh C numbers that's a good question so I would say that um I can say that for example the bgp protocol is flowed so it
has a lot of flows and it was invented in the 70s and you should not use it but unfortunately I'm afraid that um so my I I would say that my talk keeps in mind the fact that you have something and it's recognized and you need to use it and it will be there and you can either fight it h meaning that you can add some layers and you make things more qualitative in your decision or uh it's quite uh hard to think that it will it's a it's a replaceable you know what I mean so you have a problem and you can work on that problem but thinking that maybe you have another Avenue H it's like uh it's not like
rewriting the internet and bgp my example but uh it's I think it's quite hard and uh to the point of the open source vulnerabilities uh the the librar I would say that uh for example here some of them as you can see they don't have a CV they have the how do you call it uh they have the ID of maybe the vendor and so on so not everything uh it's uh it's relies on the the the CV and and some open sources project that I listed they are uh still detached from that context okay so I would say yeah that's uh that's my answer and thank you for the question yes okay so thank you for for the
interesting presentation please give it up once more





