Tool
BSides talks featuring maraki1982
1 talk mention this tool across 1 BSides chapters.
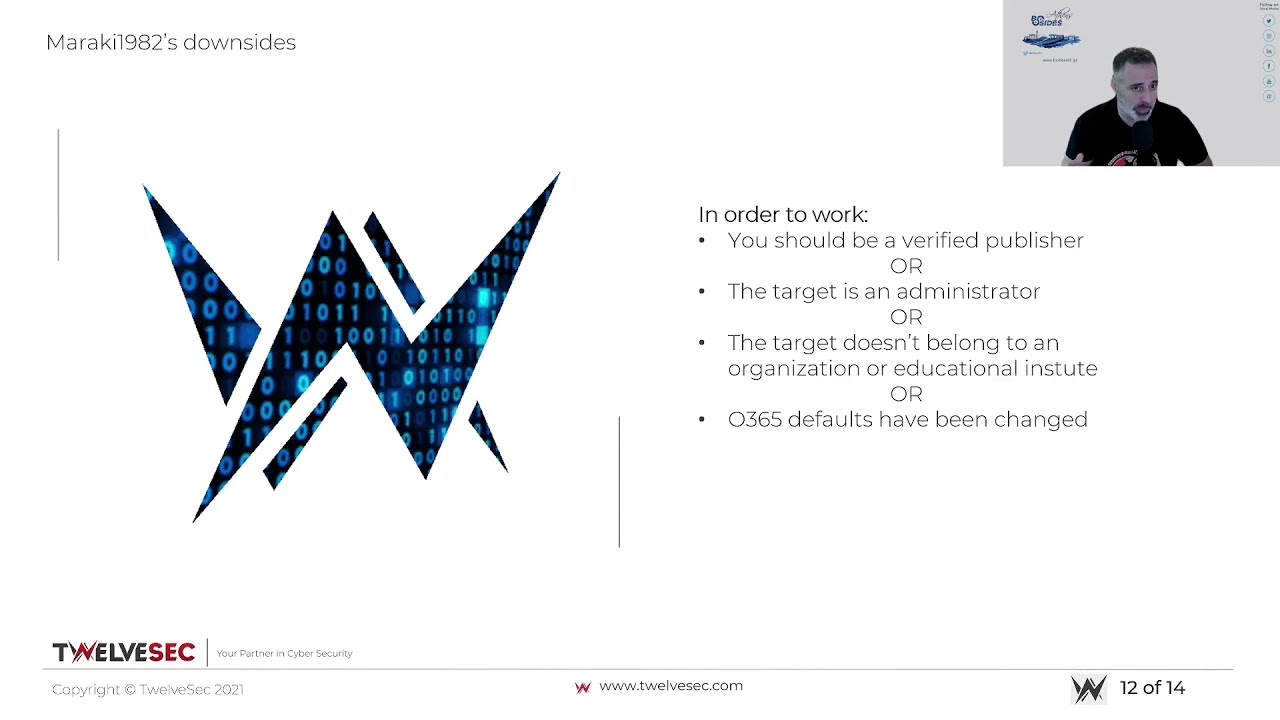
Open-source post-exploitation toolkit for OAuth2 phishing that crafts malicious Microsoft/Google authorization URLs to harvest access tokens and exfiltrate emails and files from compromised cloud accounts