maraki1982: A Management Tool for OAuth2 Phishing
Tags
CategoryTechnical
About this talk
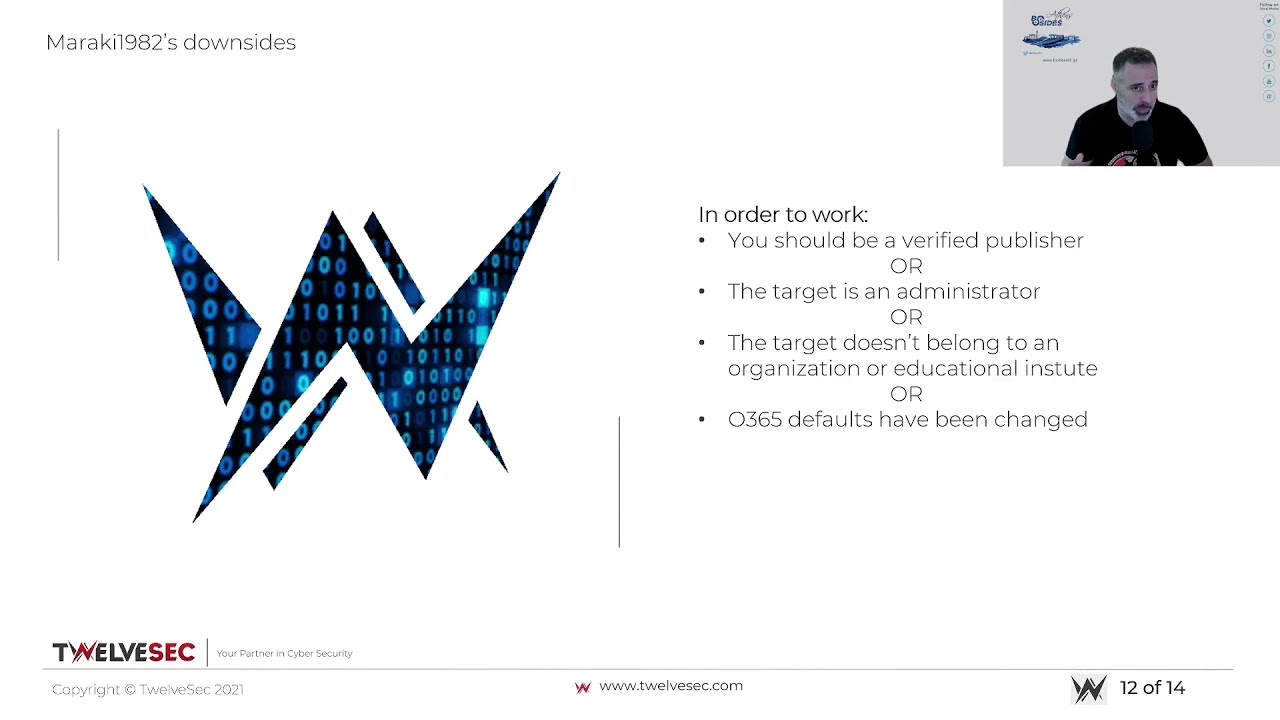
Abstract: Phishing attacks cannot be prevented by Multi-Factor Authentication (MFA), and the reason is that threat actors can leverage the OAuth2 framework to access user data. To be more specific, typical phishing attacks would require credentials harvesting, but this would not bypass the MFA security control. A threat actor could trick users into granting permission to an adversary application by crafting a malicious URL for the OAuth2 tokenwhich is granted permission to the cloud based resources; how could we use it? The answer is maraki1982, an open source post-exploitation tool. Bio: Yiannis has over 15 years of experience in the Cyber Security domain, specializing in the consulting services area. He has offered IS consulting services to various companies across the globe, gaining valuable, hands-on experience. Yiannis has been a penetration tester for the most of his career whilst trying keep up with his research and community contributions. Dimitris is a highly motivated cyber security enthusiast with more than 9 years of experience in application security and software engineering. As an application security consultant, Dimitris provides companies with the tools to secure their SDLC processes, as well as training the teams on security matters; At the same time, he focuses on discovering ways to automate security and effectively secure software applications.





