Inside the Information Stealer Ecosystem: From Compromise to Countermeasure

Show transcript [en]
We're excited to have you and we're going to uh kick off our first session here with um Olivier Bilo and I will hand off to him now. Enjoy. Uh just a reminder if you have questions uh go into the Slidoh area and enter your questions there and we can um follow them along there. If you have a question, um I do have a mic as well, but it'll be easier if we get it into the slidoh and then we can kind of just ceue them up and go through them quicker. Uh and then right after this session, we're going to have uh lunches available for everyone. So enjoy. Where can they find the link for the
slido? Because I I didn't put it on my slide. Sorry. It's probably in the program, right? Yeah. just go to the uh Bides website and then uh it's Q&A. Okay. Thank you. All right. Hello everyone. Um do we have a kind of a busy agenda but still before we get started I just want to say like please pay attention because if you ask a question the first good question will get a hardware badge. So these are from uh Nords sec an event in Montreal and uh it's a fully functional uh ESP32 many uh LEDs in it and it's fully reprogrammable. It has like open it's from an open source stack that we is published on GitHub. So the first
question will get hardware badge. So that's cool. So thank you for being here. Um this uh presentation is about information stealer malware and the ecosystem around it. So it's very cyber crime oriented uh activities that I think should get more exposition in conferences because it's dangerous cyber criminal activity that has uh that yields millions of infections uh every year. So before we get started uh just a quick uh we're we're quite large there a quick show of who worked on this research. So myself um 12 years of experience in cyber security. I used to do malware research at ESET. Basically everything I did brought me up to this moment if in my life if you want. So
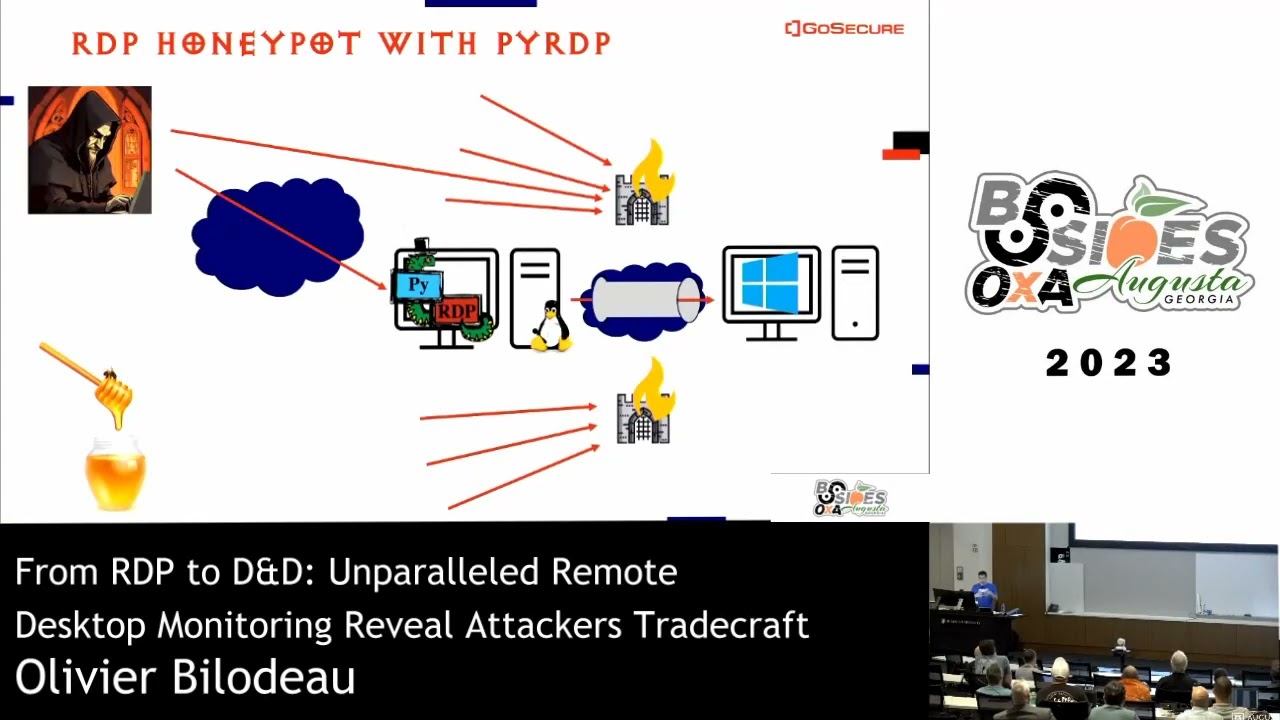
malware research at ESET where I got in touch with the cyber crime stuff but then at go secure I was more luring adversaries and I did talk about RDP interception a lot in the past. Uh but also um other people contributed to this presentation today. Um, so we basically have done many great things and we can cross arms is the gist of it. Uh, but today's agenda, uh, we're going to go over just a quick reminder of what is information stealer malware. We're going to go through victims, uh, screenshots. So information stealer malware captures a screenshot on infection. And so this tells a story of what are the big infection vectors, which is pretty interesting. Uh, then we're going to go
beyond. So, a lot of people know that information stealer malware gathers credentials. And we're going to go beyond that. What other artifacts are stolen from the the computers? We're going to cover the red line takedown that happened last October. And we're we're going to wrap up with like defense and mitigation strategies, but also I have uh other gifts than the hardware badge. We have community contributions in the form of source code and sample of information stealer logs uh that I want to share. So, uh packed agenda today um together. Please don't try to fall asleep in the comfy chairs, but feel free feel free to recline if necessary. It's pretty fun. I did it while I was
waiting here at the beginning. Okay, information stealer malware. Let me just drop this. Here we go. Okay, so quick reminder. um the it's um malware that will you know explode on your computer and will gather every information that it can in order to leverage it and and like send it or sell it to the cyber crime forums. So I want to highlight here that like administrative rights are not required for this to be useful to cyber criminal criminals. They um basically go after browser uh saved uh credentials but also browser full browser history um autofill. So every time you type something an address or something in a field that is that the browser remembers uh this will be stolen
as well. It will gather like um some browser extensions. It goes after many browser and many profiles. So if you have more than one profile, the other profiles are still being slurped. Um, so and it it will take a screenshot as I mentioned OS information. So like graphics card, amount of RAM and everything. Um, so it it does gather lots of stuff. Usually it like runs in one shot. It will gather all of these artifacts and it will upload them via a C2 mechanism. Sometimes in the past, most of the time in the past, this was um via some sort of Xfill domain either compromised or bulletproof hosting. But uh more recently, it go it's going
straight to Telegram. So Telegram being like whitelisted in many organization because it has legit legitimate uses uh will usually allow them to upload even in in harsh or more locked down environments uh the content of the computer that was compromised. Another thing, another point I want to make here. So admin rights are not required, but also there usually there is no persistence. So this is not they're not trying to move on from this foothold. There's no like lateral movement planned or stuff like that. It's really like stealing everything, packaging it up in a zip file, uploading it to a Telegram channel that is secret and um then uh deleting itself. usually finishes with a finishing with an error message like uh
the the cracked software you just downloaded didn't run because you're missing some obscure DLL. So that's the that like they have you think you're not infected basically. So we're going to go through the anatomy of a stealer log. This is quite large but I made it larger because at other events the screen were not big enough. So uh here's not the case clearly but so um it's also like quite pixelated actually. Um so uh we see so part of the stolen artifacts you see all of these like semistructured information every stealer lock family will uh carry it in a different fashion. So but here we see autofill are being organized uh discord we see like
installed browser important autofills and stuff like that all categorized. If you look at one text file, they usually carry an advertisement to their um uh malware family to their the the software itself and then it will be a highly structured file with like URL, username, password, application. the the fact that the user the URL comes with the the the the URL comes with the username and and password is what makes it a a very powerful way to conduct cyber crime because you have the context of where these credentials can be used which is not the case with the usual like big databases of leak where you don't have necessarily the context to where to try
the credentials. So in today's world basically this is like there's two ways that cyber crime happen. One of them is the elite like RC0 day attacking some like Windows stuff or some appliances and then you have the like the this the script kitties you know buying stealer logs and then from like a pimping lug clouds thing but both of them will lead to compromise of organizations. Um now you know you've learned about the malware now like what's what's uh like our expertise is more expertise is more like on what's around the cyber crime ecosystem how it's sold and and and and all of this. So it's operating under a malware as as a service model which means that you
have advertisements and so we can join these channel and be aware of the features and the updates their change lo when they they update their versions and you have like feature sets like these these are screenshots of telegram messages you see the supported browsers like um all chromium based browsers thanks to the same open source core are supported not a lot of safari supported by the Um then uh you see like the the feature set they use icons like it looks like actually kind of kind of fun and cool. So they use also like their own slang. So FUD here is not for the old school like fear, uncertainty and doubt but it's more for fully undetected. So
that's the cyber crime slang for when the malware is not triggering AV. In mo in many cases it is triggering AV but in some cases it's not. Um you have like options when you do your build. So you put can put a a custom icon you can offiscate. You have a file pumper. So so that will make the file so large that AV will not necessarily analyze it. Um, you can have droppers. And so campaigns are set up like someone who wants to make money with uh stealer log will like buy some stealer malware and then create and there's a lot of educational material on how to do this on on in cyber crime forums. So they
will create a video. They usually going to take over an account. Uh but sometimes they're going to create their own accounts but takeover is is safer cuz it's less it's not flagged as fraud as quick. Uh then they will upload the videos on YouTube. This is one trade craft. There are many many trade crafts but um with the video then they will link from the the description to the the malware itself. Uh and us they they might even say oh there's a username and password on the archive. So they b they this is basically a long social engineering ploy where people are going to get value out of it because they're trying to crack some software or they're
trying to have like free Robux. This is all stuff we've seen. Um then these videos will be advertised uh on Tik Tok or Google ads and then you're going to have victims and these logs will be collected. Um this is an example of a classic campaign. Now distribution. Uh so once the the cyber criminal has many of these he then bulks sell them. Some of them will leverage the the luck they steal but in most cases they are resold in in uh in bulk and they do it under a subscription model. So this is one example of someone advertising on telegram. You can pay for one month, two month and lifetime. I would never trust
lifetime offers from cyber crime. They these guys keep backstabbing each other all the time and we have many examples in this presentation of such a behavior. Um but so yeah so this is like joker loss one example then you have one that are doing it on websites. So they're like they have like fancy arts, a fancy art and they uh they still have like these tiers like uh one month, three month lifetime um where they say they have like 150,000 to 200,000 new victims every month, right? So some of it might not might not be true, but we do have uh seen and collected a lot of these um in our collection. So like some there's a
substantial amount for sure. Now the uh where can these highv value logs uh go? Well, as I said, some of them could be directly leveraged for targeted attacks. They could have filters on specific domain that they are interested in. We don't have much visibility over these, but we have to assume that it's a possibility. Uh what we see more is like the it's going on the dark web forum stuff. uh it's going on Russian market which is one specialized uh channel where you have like samples and um you have also illicit telegram channel and we believe that these are also leveraged by uh initial access brokers IABS so these will usually buy steeler lug get a
foothold in an organization and then sell that foothold in an organization IABS is what what they do so they could use steeler lug as leverage again not much visibility into this part of the of the ecosystem. Uh you also see like the other way around as possible. So they trying to sell but you can you also see buyers. So like people are looking they buy in bulk from a 100,000 uh of them. Contact me if you have it regular. So like WS English here but um so it's it's basically goes both ways right? Some are selling others are interested in buying. Um another uh market or another area where this is uh happening is you have
free samples. So, the cyber crime community will do a Costco style like, "Oh, you you might be interested in these steeler lugs." And I have to admit, this is a good way to get people interested or hooked. Like, the first time I downloaded one stealer lug and I went through it and I realized like, you know, the person's shopping habit, you know, where they they buy plane tickets, you know, the bank they're dealing with because this is all stored in browsers metadata. Um, you get kind of hooked, right? So they they are the cyber criminals are doing it but there's and and the lowv value luggs are usually recycled like if there's no corporate uh
accounts and like no Netflix Spotify the kind of stuff that kids go after um it will be uh shared on as a free sample but you have to be careful cuz as I said these guys keep backstabbing each other we've seen stealer logs that were carrying payload for to to infect the people looking at this free samples. So, they're basically like, "Yeah, free sample, but oh, by the way, I'm going to collect your computer as well and leverage it in my collection." So, evil Cusco lady. Um, so how do an infection happens? where we we think like this um like going through screenshots of victims is a very compelling way to understand like the extent of the number
of infection uh and also stories of how people infect themselves. We here like you have to keep in mind like each screenshot is a different victim like it's not the same victim but we took screenshots so that it would tell a story. There's kind of a progression here. Um, which you'll see where where it goes relatively quickly. Hopefully this is not too bright. I was told like the white could burn the writteness of people, but I think it's the IMAX room who does that. I think we're good here. All right. So, we have people googling for midjourney here. So, victim number one. Uh, we have the result of victim number two is the result of midjourney.
And you can see like the first sponsored ad is ai.mid-journey.org. People familiar with midjourney the image generator know that it's this is not how you generate images with midjourney. Midjourney is a discord but there's a website right now but it is not this domain. So uh basically here we have a victim but what what happened exactly? Right. So we have a screenshot now of the someone on the the the website and you can see that it's a download for Windows or a binary now instead of a a Discord bot and you have here highlighted it is possible that the computer security system may falsely trigger. So you're already like social engineered in expecting some error
messages or some anti virus interaction. Now, some people in the room might be like, "Oh, why? I think I used that major AI butt before. Should be careful." No, we're security professional. Never happens to us. Um, here we have like someone who downloaded the executable. So, mid setup.exe. And um then what we have is oops, an error message, disable anti virus, and try again. So this uh the builder the one the person who used this info stealer malware decided to put that error message in there but it is likely too late already because we have this screenshot right so the infection did happen although the error message then we have someone who's like oh I downloaded this midjourney but it's
not working and I'm not sure what to do let's look at the task manager here and try to like u react on stuff. Next up, we have like how can I disable bit defender? Like I need to it's saying it's not working because of my AV. I need to disable it. Um then oh here we have a defender user. So he's infected at the time where he disabled or he or she disabled defender here. Um here we have like ai.mjourney.org or virus, you know, like someone who got suspicious like I I downloaded this executable, I disabled my AV, but I never successfully generated any AI image. What's what's going on here? Then we have someone who is trying to delete
it like, oh, whoops. I I installed it and I'm trying to delete it. This is not midjourney here. This is Cinema 4D. So, a a montage uh a nonlinear video editor. So cracked software is often uh used as well. So what we have here basically is like free midjourney being on the road to a triple extortion ransomware attack. Right? So how much of this do we see in in our telemetry? Uh we collect on approximately 1.5 million logs. So 1.5 infection per week. This includes duplicates. So like some people are buying from private channels and then reselling in other channels. So we have there's a lot of duplication um happening on online but we do dduplicate
him based on certain characteristics and in in our collection so far we have 120 million total logs unique. So we did deed up them uh roughly like 15 millions of them will contain credentials associated with domains that are of corporate nature. So company names, organization names um and it has been said to be responsible for major breaches, right? And uh another thing like we we want to put emphasis on is like we are no longer see well so based on our biased telemetry because we're watching cyber crime forums but what we see is like people are leveraging more cyber crime forum is more used to resell credential access than to talk about zero days like no one
like our my bus wish there would be like insane PC's in the darkness out. But that's not the case, right? What's happening there is they're selling infected computers. They're not selling PC's. The the the open-source or the the public cyber security community is faster as at developing P and talking about exploit than the darknet. They're just mostly reposting the news or they do so in entirely p private uh places where we have no visibility or that we can't infiltrate. AP don't discuss on on public cyber crime forum unless they do cyber crime as well which happens. So I promised you to go beyond just the credential. Let's take a quick dive. So this these are going to be
different angles of stuff I've analyzed. Uh and the hope here is to have you like understand more what's the the impact of of an a steeler infection if you are responding to incidents. So there's there most of them have file harvester module they they so since the zip is uploaded via C2 uh they don't like gather everything right they avoid specific file types and they focus on user um like documents folder desktop um they go after documents uh spreadsheets txt file uh keypass sorry databases and the the the the idea here is to keep things small right if you go after executables or zip files, you could blow up your uh the the size of
your thing and then makes it harder to distribute on Telegram and stuff like that. So interesting thing here and this is a the natural victim and uh you can see that it's French speakaking. So I'm a French Canadian so I I related uh but we see also like there are like philosophy exams or final uh work there. So probably a student. We also have his or her resume which could be uh something interesting to look at if we have time. Um so this stealer log was uh this was how it got infected. Um so basically this was the screenshot part of the of the stealer log that we collected and you can see like this was
someone after Adobe Illustrator cracked. So again, you know, real path to um to being a victim of steel log is uh cracked software. Um another uh area of of things that can be discovered that is beyond just traditional credentials is like some MFA bypass technique. Uh when I analyzed this, I was like, can this really be the case? So this um stealer log is going after um specific uh Chrome extensions. In this case it's called authenticator and and it will steal all of the files that are part of the extension. Now if you look at some of these files there are log files which are in the level DB format and the the Level DB format will uh encode integers
but will not encode strings. So it's kind of easy to extract the strings out of it. And that you also have tools to do a machine view of the of the file type. But so this is a JSON encoded and it talks about TOTP. So TOTP being a standard to generate tokens uh timebased. So I was like do we have everything we need in order to like recreate the MFA of the victim? Let's let's confirm. So I uh in a VM uh downloaded that uh that extension uh created a totp token uh then I stole so that's the left hand side is victim right hand side is the attacker then I stole the the the extension files like
exactly what the stealer log does and then with this I extracted the secret so super mega secret here and then I used an online totp token generator to see like if we put in the same parameter do we get the same MFA token and the the answer is yes. So I think like uh lockdown environments should uh prevent these browser extensions from being installed. They are dangerous and I I I cannot see how it could be designed in a way that the secrets would not be part of the extension. It's kind of necessary information. So this is why I expected it. Now we confirmed it and if let's say you would add a layer of encryption it
would still be like the case where you need to have access to the secret in order to generate it. So I think that serious corporate environments should block these browser extensions. Now is this niche how many of the of them are they? So that specific one uh was the top Chrome authenticator app. So if you look in Chrome you say I wanna I want to use my browser for my totp instead of my phone. Uh this is the the first one and many browser extensions related to totp are covered by the the cyber crime. They all steal from each other by the way like the the the extension list of targeted grows and grows uh with time.
Now um to look at most uh targeted browser extension you can look at in your own computer to evaluate let's say your attack surface uh you can look under like these path um under and and they will go multiple profiles. So they will enumerate all the profiles and go after each of these files and slurp them but they don't gather all of it like they go after specific browser extensions. Um I mentioned that the file are like index DB level DB and this in case you're interested is a link to a tool that will parse these files. So if the integers uh for your analysis matters this thing will will extract them will analyze them. Um then uh what
else right I looked up uh there was some uh uh password manager browser extension and I was like okay these password manager are cloud-based are they safe or not? What are the artifacts left in them? Uh is this dangerous? Now I this I use bit warden as an example but this is because like both where I work flare and northsek the the the conference I run in Montreal we both are customers of bit warden so I was like worried about our own stuff so I'm not picking on them at all actually you'll find quite the opposite but uh many browser extensions are are targeted uh in the same fashion so first you see that uh multiple
browsers and multiple profiles are supported Then if you look at what's um what's available in the the stolen files, it looks like a log of some sort. Like it's not the full vault. Um it's kind of maybe some developer log. Not quite sure. Uh there's there was a lot of like keep alive messages. So these are out of of me megabytes of logs. These are the kind of entries that were that we uh that we found. And here we can see that um important parts of the log are encrypted beyond just the password like URLs are encrypted uh names are encrypted and I was like is this just obfiscated or is this legit like good
encryption. I digged into a bit warden source code and I confirmed that they are using the same like uh encryption with hashm like best of class with an with an an ID and a format um with the IV and and the hashmack. So they're doing best-in-class uh encryption here with this and the fact that they're going after name and URL I think is really compelling. they're they're really doing what they the best they they can. So now the the only thing I would need to uh finish like this research uh would be like okay if I have my master password can I decrypt these strings or are these even using a temporary uh password that is just
available to developers. This is like on still on the to-do list but so far everything sounds safe. Um password vaults. So I mentioned before that they steal keyyp pass password vaults KBD and KBDX files and I just wanted to see if there was a realistic attack path here and there is. So there's a tool part of the John the Ripper suite uh that can extract the keying just the keying material in a format that hashcat and John supports and with this thing then you can mount an offline attack. So it means that you're not at a super high risk, right? It's it's basically you got your files stolen, but now how good is your master
password becomes your your uh your your the concern. Um, so one thing I would like people to keep in mind like if you reuse a password or if your master password is a derivative from something that is saved in your browser then you know you're at larger risk than if you are using a completely different of the record password. I actually um we have a a workshop where we actually go and do that, right? We derive a a master password from the passwords that were breached to uh we put pass them through John the Ripper mangling rules and then we successfully access the vault. This is just done in um it's all fake environment but still you can see the
risk and imagine like the collection being uh stolen. It's it could have big consequences because you know you are dealing with a sophisticated user if you're dealing with password vault like that. Now there's another thing that I found strange and now being in San Francisco I'm worried about like bad mouthing Google. Um but but and and I spoke to this with Google engineers I know in Montreal and they know about it. So, it's not like it's super uh unknown, but so there's a thing called that they call the bad guys call the Google master cookies. And apparently with some uh tooling, you can restore legit cookies that work on Google properties. With this master cookie, um there are cyber
crime tools that does it. And I was told that um this is like an important part of the Google's authentication story. And it the the source code is in in the Chromium ecosystem. So it's not like they reverse engineered or they had inside secrets or what or they leaked source code from inside Google. No, apparently like this is possible for some reason that still I still don't understand. Uh but the the cyber criminals that did the tooling apparently got inspired from some of the Chromium stuff. But so with this you can um generate for a a given browser uh a g and a given Google domain valid cookies out of this master cookie. Pretty scary. And apparently it doesn't
work all the time and Google's very actively like uh they have a lot of telemetry. So if you're trying to use these cookie you better get everything right like the country the the the user agent and all that stuff right. It's not just like if you would you can come from another country and walk in the YouTube account or something. Now anything else? Yes, there is. And you know it would be um worth analyzing a lot more. Um Azure stuff, Discord, Steam, Any Desk, ProtonVPN, Electron, Metam Mask, lots of of crypto wallets being targeted. These guys are after quick money, easy money obviously. So it's easy for them to steal it. And these most of these um
crypto wallet extension they don't store this stuff in the cloud. This stuff is in the browser extension. So this is why they go after stuff like that. Haven't analyzed them much but I'm not a crypto person. So didn't I wasn't really interested in this. Uh they also steal cookies. uh so um they uh basically gather all of them from the the browser's SQLite files and these can be leveraged uh quickly you know to hold valid session obviously like if you're a bank and your cookies are valid only 15 minutes then it's not of much concern right you um your users are probably safe but if you are like a consumer product which h which in which the
sessions last super long then is something worth uh evaluating like expiring them or or invalidating the sessions as quick as possible. How like this is fairly technical, right? So for the cyber crime folks, how are they leveraging it? Well, we found out that they use tools called checkers. So that's a screenshot of such a tool. This one is called BL tools. uh if you want to interact with it, I would recommend doing it in a VM because it's heavily packed and it's probably infected the ones that are available online and probably you will end up in stealer log malware uh steeler log logs. Now these are like super turnkey, right? You have like the properties you want to attack.
So like YouTube, Twitch and everything and they are proxy aware. So you can pin your your attempts through different proxy and it will they take straight out the the information stealer log format. So dump in a stealer log and then you know say you should go through this country which is information you have in the steer log use this browser and then it will just try to authenticate and and it will tell you which account work or not. So then you can sell access to specific account. Oh you want a Netflix account? You want a Spotify account? Luckily for us defenders uh they go after like uh household names property. They don't go much after uh business
access. Now uh I promised defense and mitigation strategies. Let's start with like what's happening uh in the field. So first the vendor's response is like AV is doing its best and I believe that I used to work for AV. uh they they're they're whack-a-moleing these things like usually you you you have like a one day two day window until the thing is detected properly but they this is enough for some infections and other infections happen via social engineering they get you to disable your AV so it doesn't matter right um but also they flip on the flip side they don't publish much about it it's hard to be accepted at conferencing conferences talking about this stuff because they're because
they're all focused on AP PT and state thread actor. So I wanted to get that out. Um uh operating system vendors I wish they they would do more but instead there are adding recall which is like a super nice database of user information and PII indexed ready for extraction. Okay, I have to admit that since then they've updated it and it does sound a lot better. you will need admin rights probably and to interact with service. So I don't think we're going to see this in steeler loss soon but we need to sur to watch the change loss but it could have because it could happen. Uh Chrome and Chromium the chromium ecosystem uh is doing defense in depth. They added uh
in last September I think applicationbound encryption and this is significant so I'm going to talk about it a little bit. Um the applicationbound encryption is basically they so the the the the crown jewels of the browsers was in a SQLite database inside the user folder that so basically you need you open the file and you talked SQLite and you could extract all of the information in a structured way. Now they put this behind a service. So they encrypted the file and put this behind a service where you need to interact with that service and be so because of that they were able to uh uh make the file not accessible to non-admins uh and even protected uh uh further like
they use basically like how Windows protect the SAS processes and stuff like that like it's really locked down but this uh elevated service is still basically you will need to provide the credentials to the user. So, Chrome can talk is allowed to talk to this elevated service and request credentials. So like they basically did a sand c line in the sand and preventing like anyone to get in. But as you know security conscious people will be like hm this could probably be bypassed and it was and very quickly like couple weeks it was bypassed already that technique. Um and what are the different bypasses? Well you can launch a headless chrome with remote debugging and then
interact with the remote debugger and script it to dump the credentials. So this works one of the stealer malware used that technique. You can dump memory. So this requires admin but you can dump memory. Uh you can interact with the elevated service using come objects and impersonate chrome. So this is doable without admin privileges like the first uh bypass technique as well. Or you can disable application bound encryption with the regist with register keys kill the browser process which you can kill because you're operate the malware is running at the same privilege level as the as Chrome and then on relaunched since you uh change the registry keys application bound encryption will be disabled so the file
will be readable and accessible. Now this could sound bad and I could be like Google you suck. But no, it doesn't matter that it is bypassed because we get better telemetry. Okay, the situation before was file IO and you can you could access all of the stuff. No one has granular amount of log where you have all file IO that is done. So if you do any IR or if you are anti virus or EDR industry, you can now rely on a on better signals in order to protect the the computers and or have telemetry. Uh basically there's just a ton more visibility because it requires admin in some cases or and or also it
will be brittle. Right? If you are memory dumping, you are going after specific offsets in memory that will vary depending on the exact browser that is used and the version of the browser, which means more code to develop on the side of the cyber criminal. So it's I know it's hard to accept to have a countermeasure technique being bypassed so fast, but I think we really need to understand that this is a part of the of the war and it's a defense and depth uh thing, defense and depth activity. Another defense uh measure that we advise a lot is test your credentials like this data is available in the darknet. Many there there's many way to
get it. So why not download it and have a pipeline where you can automatically test your credentials. Um but you have to be careful right because it will generate logs and you can lock out accounts. So you need to be smart about it. You cannot just simply you know brute force every thing of in your own account. This was create noise. Now, now I'm going to go fast over the red line takedown. We have like officially 5 minutes left, but it's lunchtime after, so I might go over a little bit. Um, but so the red line takedown in October 2024, uh, the red line uh, and meta malware and malware operation was seized by the police. Uh, what we witnessed was
like that this was a major uh, operator in that field. So we see a lot of telemetry and then we see a drop at the end and the little little bump is probably like uh resold. I I told you like cyber criminal resell a lot of the stuff that they already did. So it's probably someone who resold older loss. Um but so this is the uh the impact of it like we're talking like uh 1.5 million a week in the peak of the meta of the red line stealer. Now, at first people thought that this was um different that these were different malware strains, but they looked similar and eventually like we found like they
shared certificates including private keys and we found basically the uh a very similar feature set a very similar UIs. So basically what we have to deal under us here is that red line and meta was were basically doing fake competition between each other's brand in order to have more of the market of infoscaler. Um now it took like uh we started collaborating with uh ESET for the takedown uh and it took uh two years before our first public presentation about red line and the police takedown. Um they they like when they so when they did the takedown uh uh they launched a website called Operation Magnus and this is a super funny tongue andcheek thing
that the police did. It's one minute long so we're going to listen to it together cuz it's just so good and we have a cinema screen.
This is the final update for Red Line and Meta. This update has been made in partnership with international law enforcement. We gained full access to all Redline and Meta servers. Did you know they're actually pretty much the same? This version of Redline and Meta includes unique insights in your data, username, passwords, IP addresses, timestamps, registration date, and much more. all the red line and meta source code including the license servers, REST API servers, panels, steelers, and Telegram bots. VIP status for all Redline and Meta users where VIP means very important to the police. Thank you for installing this update. We are looking forward to seeing you soon with the handcuffs at the end. Yeah. So yeah, police is are uh are
doing Oh, what? Sorry about that. Yeah, the police is doing awesome job. I find it really funny. And um so the yeah, VIP means very important to the police. It's kind of good. So I promised um community contribution. So we here we have two things that we're going to share to people willing to uh scan the QR code and uh fill a form. Now uh we are this is going to be like besides warned us like we're going to be p we need to be like privacy and v vendor agnostic here but we cannot release this as open source the credential testing script it works a little too well and uh it works like even on other uh entry ID tenant so
we don't want to make this open source we we it would be just uh in inadvisible and the sample set of steeler logs They are um anonymiz they are not anonymized. I'm sorry. Uh but they are from alleged cyber criminals. So we're like, we don't give a damn about these guys. So let's just like share the stealer dogs. So if you want to see what it's like when you get your hands on stuff like that, um feel free to submit. We can also like discuss at our booth if needed. But um but we really want it to be uh like respectful of of people's privacy and there's you're not going to be added to marketing lists and it I'm a researcher
trust me like I'm not going to do that. Uh but I cannot make it public. So this uh is our gifts uh accompanying this talk. And now we're going to wrap up in in like a couple in the next couple minutes and it will be you'll be able to go for lunch. Uh but I wanted to like recap by saying putting the emphasis on the fact that stolen credentials are really important. So this is from last year's DBIR report. One breach out of of three it has um stolen credentials related to the attack or in in the attack path or like uh some part to do in the attack. Now we're going to go after three aspect. So uh understand,
educate, protect and remediate. So one thing that I think that more of the security community should be aware that administrative rights are not required. So it's not like if you remove admin rights from your user, you are uh invincible to uh stealer log. Uh stealer log malware can come from v various sources including crack software, malicious ads, Roblox uh YouTube videos, fake updates, free PDFs. Um, also we we advise people to to uh tell their staff that there's rarely a reason to disable AV. Like I know it's it should sound obvious, but it's not something we hear often like wash your hands, never disable AV. Um, you shouldn't share work computers with family members. And this
is where the Roblox or the the Roblox skin, you know, come into play. Like if you're at the hotel and then you're sleeping and you're like, "Yeah, play with my computer. It's okay." you don't have admin on it. Well, you might get infected. Um, also it's not limited to just password. There are more things that can be stolen. And uh part of the education for cyber security staff like play with one, look at one, realize what's in there and this will help you better protect your organization because you'll understand more the risks of what could happen if such a thing would happen to a corporate computer. um to protect I want to like put some
emphasis on that in the fact that password manager are still effective so they're still protecting people uh Windows smart screen is working for like the midjourney uh stuff uh and uh yeah so I'm I'm told to stop so basically the remediation part is like search and then protect um but that this is it for me uh hopefully you had a good time this is the QR code again and I'm sticking around for the next two day looking forward to meeting you all. And we do have a couple questions. Uh the first one is do you see a resurgence in new info steeler players after meta takedown? Yes. Uh so we saw that uh Raccoon and
Vidal I think are the ones that are researching after red line that are taking the space. Oh, I should mention Luma C2 as well. uh lots of Lumac C2 and I would say SteelC uh are ones like I'm not I don't know by heart which ones are the the fastest growing but basically this created space and that space was taken by other players. Any other questions? Yeah, the other one uh similar. Have you looked at other Steeler services such as binary packaging distribution campaigns and so on? uh Luma for example. Yes. So the question is for Luma C2 if we looked at the the binary uh packaging and the distribution. So our expertise is really
more on the victim side. So we collect the the infect the the steer logs. So we kind of um we meet in the middle with like uh anti virus industry or EDR in the fact that we are telemetry is based on victims. they are more looking at the files and so we we can together like have better stories or explanation of of who's gaining market and what's working and one of the the things you have to know so on on the binary distribution side we have no visibility or almost none but um the the what what we could see though is like how many victims there are but one of the caveat is we're biased on what we
have access to so like we could be we our view could be limited and like if we break into new telegram channels then we would have uh more nuance. So basically all this to say other vendors can have different numbers. We're not saying ours are perfect but we are pretty proud of our collection but right now the major strains were the ones I I mentioned that we saw. Okay. Thank you very much. Um everyone, uh this wraps up our first talk. There's lunch now in the um fourth floor in City View, uh noon to 1:30. And um we're going to clear the room now. And if you want to join us after lunch, we will reopen. And thank
you again so much. And we'd like to thank our sponsors for uh BIDES 2025. Thank you.