The More Things Change, The More They Stay The Same - Tim Burnett
Show transcript [en]
[Music]
good afternoon I hope you all had a nice cup of coffee plch of cake um yeah this is if you've read the little thing in the book you'll know this is about me thinking not a lot to change in security so lovely little quote past is a different country they do things differently there well I would argue that actually insecurity terms probably not this is me I'm just Tim um I've been kicking around in this job for about 30 odd years s's now gone um I've done all sorts of jobs consultancy um I'm now an independent data protection consultant and I do a bit of trashline background that's that's my hobby so that's who am i s right so how did I get
here well I as I say I've done lots and lots of different jobs for quite a long time some of those companies no longer exist um that wasn't my fault in terms of Technology I've been involved in sort of all all of that lot um I don't know whether I'm looking around that yes there are some people here who will remember net buy and ipx and SPX and um thin net thick net um and there are some people who are going what what the hell yeah um the technologies have moved on and when you think about it 150 years ago we were still in the industrial revolution I'm not that old our Railways only stopped using steam
power in 1968 that's a year before I was born and 30 years ago the IBM PC brought out and there was no thought that we'd ever have sort of a PC in every home and now what we got we got these things on you know we got phones all over the place they've got more processing power they got connections to the internet and so on so you know this stuff's all moved on so look back very very briefly you used to have computers either Mainframe or maybe a network maybe a server and so on and then this internet thing appeared um and we used to dial up over good old pots telephone lines um without freaking them if you were here
earlier um then all of a sudden we put least lines in maybe 64 kilobyte I put first connection I put in was a 64k line um into Janet that's 64 kilobits not megabits not terabits or anything like that um so we threw a firewall in because it was thought of like it's a good idea to put some kind of filtering in and we had a mail server a web server and we put antivirus on and that was security done um we didn't really move on from from that for quite a long time um but then all of a sudden people started wanting to be able to access the computers the the office computers from home um and we started to introduce
taets and phones and stuff like that so uh we got we got a bit clever then we had um third party suppliers connecting into our to our corporate networks um and we were doing electronic ordering and and so on all over the Internet and know this is this is when we had dial up before but this is when we started using the internet um oh Cloud oh that got exciting somebody else's computer so you started worrying about that and our attack surface had suddenly grown so yeah obligatory hacker in a hoodie um and now where are we I mean it's just it's just ludicrous you've got everything everywhere nothing connected everything interconnected um social media
digitization um wearables you know smart smart wrist watches and stuff like that so everything's got fantastic and it's all got really brilliant and we've done it so much in 30 years but not really in security I would argue that nothing has changed and why do I say that well go to a Tech conference like infc or DTX or whatever and you know the business conferences not like this where we've got proper security people doing proper hacking stuff um and you will hear the same I went to the reason for this speech is I came went to a conference and sat there listen to the opening Keynotes it was like I heard this 20 years ago and it was all the same old um
stuff get the Sea on the board have a security should be a business enabler protect the day all this stuff when you can read all um we take your security seriously oh yeah oh yeah we do if only only it wasn't for the how many times we hear that if only it wasn't for the users oh and then this year's buzzword I mean we've gone through blockchain and whatever but now of course it's AI so where's it going wrong well these are the things you hear all the time security is saying no security just it we're failing to the you know the obvious stuff um too much technology wrong technology no Tech vendors here so I can slag them off a
bit more and really it comes down to it we're still human we're still talking about putting firewalls in strong defenses you know so we build our you know first line of defense oh bit that got breached put another line of defense in oh that got breached put a bigger one in where is your perimeter in a cloud environment so let's get back to the basics this still holds true CIA confidentiality availability and integrity it still holds true because it still matters because we're still looking after information to much emphasis is placed on confid on confidentiality in my opinion not enough on integrity and availability um which some talks earlier on ransomware ransomware often hits a
ability it doesn't affect the confidentiality your data has your data is still there nobody else can access it you can't access it though um an Integrity of data is is is very rarely talked about but it's one of those things that comes up I'm a data protection consultant we talk about in in gdpr terms one of the one of the requirements in there is to make sure that the information a company holds about you is accurate and is up toate we don't talk about it often enough we talk about encrypting stuff and we talk about locking things down we also forget about Legacy technology there's an awful lot of stuff out there that is very very old still in use
Windows NT for servers um Cobalt programming this kind of stuff it's still running our critical National infrastructure and people forget about printers print servers I was in atos back in a while ago many years ago um we got hacked we got virus in infection or virus infestation um where was it it was on a print server that was running Windows XP with no service packs or anything like that on it um it was it's just too easy if you've got sort of old stuff that isn't patched in there another little issue flat networks it's very very easy to put flat networks where everyone's got access to everything if you get a breach something gets infected that just goes
[Music] everywhere so why aren't these segmented because it's hard because it's difficult because it's all because it's painful users yes we have got a problem with users we got a problem with users because they move around the company so we had a case uh client I was working with not very long ago where one employee had been in that company for 13 years they worked in most of the jobs so they've been in all these different departments so as they've been in all these different departments they still had access to all these different departments guess which account was the one that got packed when it comes down to it we're all cavemen in an IT world you know I
think if you took someone you know took him out of a cave put a suit on them put in the High Street let still look like a person we haven't actually evolved as fast as this technology sorry there are some Brilliant Minds in this in this building um but there's an awful lot of people there who are still struggling with with with you know with the basics so we get told have passwords make them memorable don't write them down about eight characters that will do must contain three of the four clever characters and we got to change everything days so this month's password of course is j4 this guidance was changed at least three years ago I mean this is published
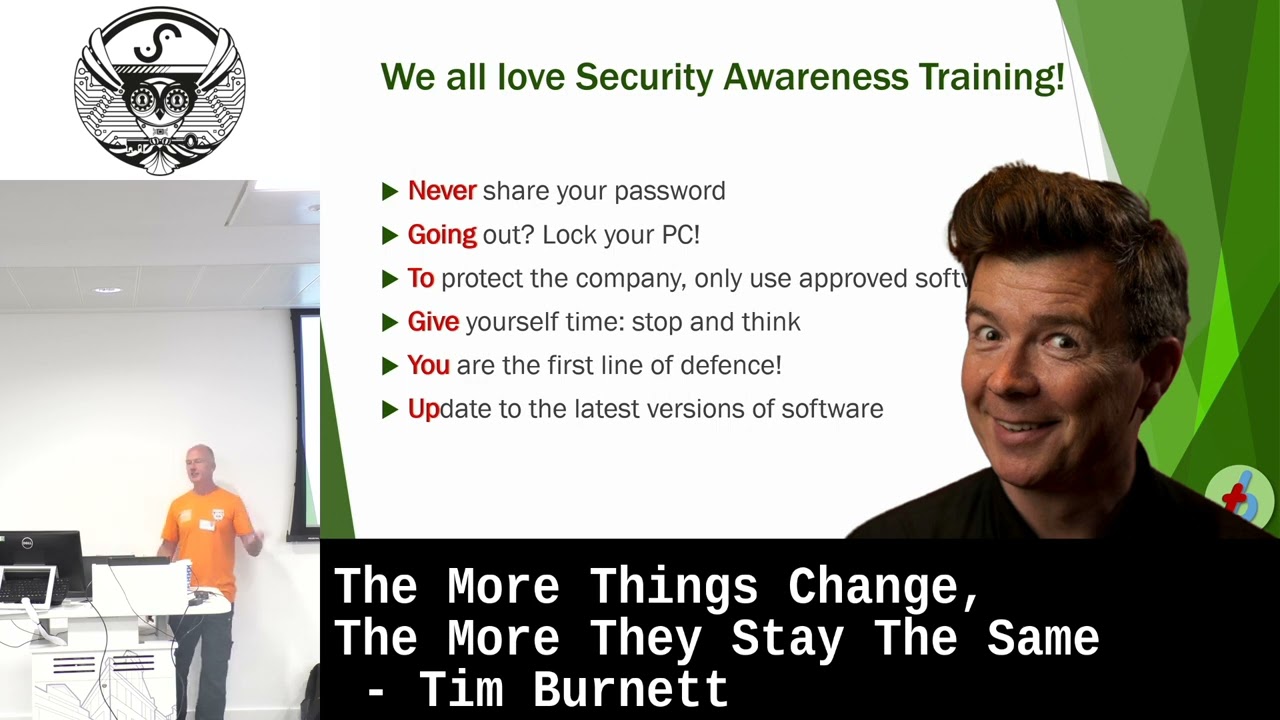
guidance from ncsc was changed three years ago to make it you know long three three long word three memorable words don't change it all that kind of stuff but we haven't moved on we haven't changed the guidance we''re telling people you go into a corporate environment they're still putting this training Rell because we all love security awareness training don't we and we see all this stuff once a year I'm looking to see who spotted
it oh come on it's afternoon it's late I know you've had a work hard
today oh sorry I've got that one that's out thank you okay security awareness training the way it's done typically is once a year tick a box it's crap nobody listens to any of it let's come on we can do better than that we really can do better than now Bill Gates said this in relation to getting stuff done in that a lazy person will always find an easy way to do difficult things from a security perspective people are human they will find a workaround I'm sure we've all seen these sorts of images gate in a field no fence and you know why bother having a barrier if you can drive around it humans humans I've read Sarah AR Sarah
Armstrong Smith's book um which I picked up at bides in LS by the way another be very good um and she introduc she introduces Tony Sals she's had an interview with him and he talks about humans are driven by two things fundamentally fear and love so you can attack people by going for these raw emotions we're emotional people we you know emotional creatures we go for these emotions so you're told that a purchase has been made on your credit card and you go is it really click the link um or or you know I send you an email and tell you I love you you go oh that's nice can you send me some money for a c for you know for a plane
uh flight you know this is we're going for the emotions aren [Music] we it's too easy to hack humans you know get some get a free offer tickets to something that you really really want to go to especially B not the Olympics so we go back to training so how do we tell people not to do it we say to them and if you obviously Holly speech first thing this morning was brilliant cuz it was just like let me straight into this humans will click on anything or or certain s humors we tell people to look for these things people who write these emails are marketeers they are very very smart people they write in a way that people write adverts
they will encourage you to do something and it's not just the threats of oh do it now because you're going to you know you've been attacked so people will push the button they will click the link because they are told to BU the marketing now it's not their fault they are human okay technology so we've got too much technology and Technology causes a problem so let's just throw more technology at it yeah yeah that's going to work it out there are no silver bullets I know there are no werewolves either but there are no silver bullers and there are two significant problems that I've come across with technology there's more than that but these are the significant
ones firstly technology sales people they will sell you what they've got on the Shelf now I've been there I've worked in the organizations that do this kind of stuff and they do and they they were like I've got one of these and I need to sell it so I will flog it to you the other half of the equation is the people buying the technology it's the techies in the IT department or the security department will go oh sweeties more blue lights so again this is human nature the sales people want to sell stuff and they will teching people like new
tech I should have had a PO of your child this is the buzzword you're going to get hit with the buzzword all the time I went to DTX every other speech was it was by our AI
system how the heck are you going to cope with all that technology when you keep buying more and more of it you're lucky to have an IT department that's capable of running Windows let alone what does it say 13 different security vendors worth of 31 different security systems my view on this is have one decent security system that you can exploit to the hilt because you can train people in it you can run it and if it does 80% of what you need you're far better off than having eight or 10 different vendors equipment that only do 10% of what you do but you don't know what's going on and don't talk about single pain of glass because that's just
one single pain in the so how do we do better firstly let's have a look at a data breach very little of it is actually electronic very little of it is actually hacking most of it is human error and that's not bad human error that's just people doing D things because they're people and they're busy so more some more technology is not going to solve the problem if 62% of the problem is [Music] people security departments have to stop saying no yeah it's an old one we know it thank you to Dan card for his tweet the other day um we can do better you know we can we can say yes instead of no maybe it's no but or maybe even
better you know moving on yes but I want to do this instead of security saying you can't do that because it breaks the policy like okay that's very interesting how can we make that happen doent processes will get into will will help you so having processes that actually work that actually work for your business and are not just off the shelf and wer up you know were last updated five years ago I will encourage you to automate as much as you possibly can providing the automation actually provides benefit to you and not just you know just you know crap in crap out and when you take technology that helps us while gets in the way I'll come through an example of
that a fishing attack it's the simplest obvious uh most obvious and and most straightforward where getting into an organization so the email shouldn't get through in the first place all right so the email does get through but the URL embedded within the email shouldn't you know should be blocked so if the link works on the on that email then it shouldn't download because we should have something blocking it if it does download it shouldn't execute okay but if it does execute well it shouldn't then connect to the command and control server that it's trying to connect to so all of these bits this is just layer stuff this is Swiss cheese stuff it definitely you
know get to the next point if it does execute does connect we shouldn't be uploading data or we should be identifying that we've uploaded data and finally not users shouldn't have access to everything so if I open the email and I click the link the only thing that should be affected is what I can access which means if I work in finance yes Finance might be screwed but the HR System is still okay worked many many years ago with RS Components um they had their it systems locked down so tightly that when a team in Italy 13 people in Italy when one of them hadn't patched his system hadn't done this did get hit with a piece of
malware and and it was an encrypting we would call it ransomware now but at the time it was just sort of encrypting malare the the 13 of them all got affected and their server got affected but the rest of the organization was fine and that was just because IRS components had an approach of really really lock it down I have never seen it like that anywhere else that was brilliant that save them andly stop playing people being human we're human we make mistakes we get it right get it wrong we do stupid things we're busy we're stressed and after all we're all just cavemen with fancy it thank
you I am open to questions I can ask anything answer I totally agree with that and I I don't think Cod bigger now is it legy I IED I had to write on 6502 assembler at one point that's that's my coding days and Tiny now it's bloww is it sorry C so yeah and I told you know you have when I used to WR software every bite every bit
you look at obos and they give the top 10 cing the things we did in 2003 are still being today Legacy software is there because you don't like new software because people can't about softw just invol so how do we correct that to educate next generation Our Generation how Next Generation nearly gone we do is how do we educate the Next Generation in our schools and universities to provide high quality secure day one well I think that's a brilliant brilliant question there you go your consultant answered that one didn't they yeah the consultant answer that was what a brilliant question what do I say now security from day one again we talk we we talk about it from you know
security built-in security uh you know from from the ground up and and so on one of the best ways is to makeal security team get involved with the devs I used to work with the team of devs I was Data Protection Officer and head of security which is a conflict of interest was an interesting one but and people come to me can you sign that off no you should have spoken to me eight weeks ago when we could look at what we were doing so get it in early um how do we get the kids involved show them this show them the damage show them the sort of stuff that Can Can Happen get them into a b Sid um
can we as Security Professionals get out to to to to to
schools yeah yeah people get it and actually get to validate their age yes and it's really interesting people never think oh POS yeah yeah and not and not dollar minus yeah get it in five minutes yes it's it's I mean it's incredible that yes I don't we can't change curriculum we're not going to you know change
children you have a plan set up now so [Music]
I just want to ask something Israel saw teaching the in the school security and in China they started from age of so if you are behind yeah I me go toon and it's it's we used to you know there the raspberry pies came out and things like that people were doing all these C one of the other tricky things I think is you got all this bloated code and it's too easy to to go to a repository and pull code in and say I love that and that and that and that and all these sub routines get pulled in who where do they come from who's who's validating them and and and where are they tested and we end up with
with with you know BL blow you get 20es yeah [Music]
yeah I I I worked at 3om Sonics and we had we given ourselves a deadline to get um version six of the ISDN router code now ISDN those who may not know this is a digital dialup thing it doesn't exist anymore um we we'd come committed to getting the code out on this date and we were testing it and testing it kept failing this just is a pile of poo we can't do it we' committed to get it on out on the day we got it out on the day we pulled it the following day so yeah we did used to do things and that's and that's you know chief executive saying got to get
it released so we got it released and yeah we did bad stuff Al Tech and it seems that we don't learn from our L and knowing that the nature of the human we are good at exing but we are not good at being proactive are you trying to say that partially we should accept it but I think we have I think we have to accept it because it seems that we are still want to say no we are going to fix everything with all of this technology uh yes that are the technology people the technology people will say we will I I think the technology people will tell us the technology will fix everything you know
AI will will will replace us all so there'll be a robot during the speech next year great um I don't I think we're still humans we you know we we we're still going to be making mistakes we're still going to be um we still have our weaknesses I think the important thing there is to understand that we've got weaknesses know that these exist Holly speech this morning was you know absolutely brilliant because it sort of brought home the fact that we're all different and and yet we're all the same and we're all messing up um so I think we have to accept that we are still going to keep screwing up and people I mean the other thing I think I
failed to mention you know they're are bad guys human nature means they are bad guys you know first caveman who made a new club next guy grabbed it off him hit him over the head with him and stole it you know it's we've always had thieves we've always had fraud we've always had bad stuff um are we we're not going to change that you know we're not going to suddenly become a a beautiful nana we have to we have to live with it we have to understand it
so actually time yeah ring doorbell classic exactly and that's
top yeah but the first to Market will be the market leader so I said ring doorbell there must be a dozen video doorbells out there but never heard of any of the others um so yeah so the first market wins it even if the product's absolutely a pile of nonsense security right I've got two minutes looking at that clock I just going to say a quick comment on that is if you look at Dash as a really good example first maret if you look at pretty much every Dash across that's currently available the they're all like two or three designs that are just replicated and they all use the same sensors we all use it's so it's
it's what what manufacturers are doing rather than updating the hardware they're just increasing the amount of features but not actually improving the thing we should do which is the product itself in the first place yeah so they'll just build features and features and features because that's what people want no that's what you've been told you want so marketeers will say how can I make my product different to product a and if and you know if I had a blue light on the back you'll buy it so yeah brilliant regulations you think we've had things like Rec
yeah is that going to work no no I don't no regulation regulation will always be about three years behind the the technology and the technology will always be adopted and abused by the criminals before it's mainstream um and and we have to do better and I think that's where the security Community does really well at getting together at events like this and having a chat and going well that's a paa poo what can we do about it and we'll do it I think that's my time thank you very much indeed for





