SCADAsploit: A Command & Control For OT. How To Break An ICS System - Omar Morando
Show transcript [en]
So hello to everyone. It's a pl I'm pleased to be here for the first time in Prague is my besides number eight around Europe and uh I would like to introduce a different kind of approach regarding the cyber security in OT domain. Uh briefly I introduce myself. I don't know where I can stay on stage. I'm a an offensive researcher in OT domain. I'm I have more than 25 years in OT. It's very long time and um especially I developed the scatterasloit is a common control for OT adversary simulation. Currently I'm the director of OT cyber security advisory in Italy. I live in Turing and uh more or less it's all I presented scatterloit in besides black
hat Europe London two years ago and last year in the sun's ICS summit it was very interesting experience for me so before to introduce this catastro I would like to put some question some important notice I think is relevant for for for all in order to have a baseline of knowledge related to OT. So why operational technology cyber security? It's very easy. The answer ICS is a very interesting target for APS. uh it's easier is uh very impacting in in u in economic stability, national security, human and environment safety and the targets are energy transportation are telecommunication but also manufacturing big manufacturer and is very interesting some characteristic of domain are very it it seems are specifically developed
for attackers because insecure by design in is a standard. So it's very funny for attacker. It's not so hard and the result are very interesting also for only for the attacker not for the companies of course. So I don't want to bore you with staxnet. Staxet I would like to underline only two topics regarding staxet. But first uh staxnet as you know is the first malware or better is the first cyber attack against the instructor in 2010. Staxet was able to damage the um nuclear plant of an atans in Iran. And this is the most the the first topic interesting topic first attack against second interesting point straight that is possible to damage something using
software before staxet malware and attacker were target to steal information or um to grab dollars and money. But with STAXNet, they was able to damage something a physical plant using software. This is interesting. STAX was the first um is in 2010 but the hacker team NSA it's possible that be NSA uh tried it before in 2007 then they restart with a new version and then the final goal was reached in 2010. Good. But Sax is not the only malware targeting OT especially specifically developed for OT target. One of another malware interesting for OT is indestroyer. Indestroyer in 2000 in the end of 2016 was able to damage to destroy a power plant in Ukraine in
Kief. same uh result more or less the same approach in destroyer is a specific malware targeting power plant generation. Why it target or better how it target energy plant? Because it use typical communication protocol used in this kind of plant. That means protocol use it to control water, gas, critical manufacturing, some uh electrical switches and so on that use this kind of protocol. A indestroyer is able to target to identify the the correct target in term of PLC, DCS and SCA system and apply the attack. Of course, in the Sawyer V2 report in [Music] 2022, a better better version with some improvement. Of course, another interesting malware that I would like to present you is Triton. What's Triton?
Oh, better. Why Triton? In industrial plant there are some strategic components that are called SIS that means safety instrumented system. When you are in production plant and there is an emergency situation, you have to put in the safe situation your plant and there is some emergency red button to stop the production or to plant the production to put the production in a safety situation. This situation these equipment are called as I said safety instrumented system. One of the most important company worldwide is TrionX that produce this kind of object, this kind of safe PLC that you can put in your plant. Triton is able to attack the specific version of Tririconnect SIS. That means that when you are in an
emergency situation, you go fast to push to the red button and then Triricon X or better Triton is able to do the exactly opposite of what is safe. That means that he can I don't know destroy or bypass the emergency situation. The consequence could be absolutely catastrophic. It's the end of the plant interesting but not so not so funny. So what's inside an IC system? ICS is industrial control system. You know very basic information. Uh I I have this slide in order to check if I know the right version of the ISA. So please correct me if I'm wrong. So starting from the bottom these are part model level zero is the process sensor actuators. Then you have the level one
is a process the PLC's and control system. Then you have level two are the software that handle the plants and control the plant. Then you have the three with operational and control database and so on. Sometimes you can find a strange part that is called a DMZ very very uh not so often okay I can say the level is the 3.5 is called 3.5 and then you have the enterprise but okay is not our domain so starting from the level zero you can find the sensor and sensor is something that can transform a physical value in a digital number compare temperature pressure I don't know speed and so on actuator do exactly the same transform a digital value to a
physical action this is the level zero then we have a a PLC programmable logic controller that means a strange equipment that control or better get the information from the sensor elaborate the process the programming side and then activate the actuators it's very easy and then communicate with other device and do something of strange that can be useful for the plant. When then we have the HMI. HMI is human machine interface are some monitor industrial monitor industrial equipment to interact with the operator. And then we have the SCADA. SCADA is supervisor in control and data acquisition is a software inside a computer standard computer in a control room that control the plant acquire information send recipe send
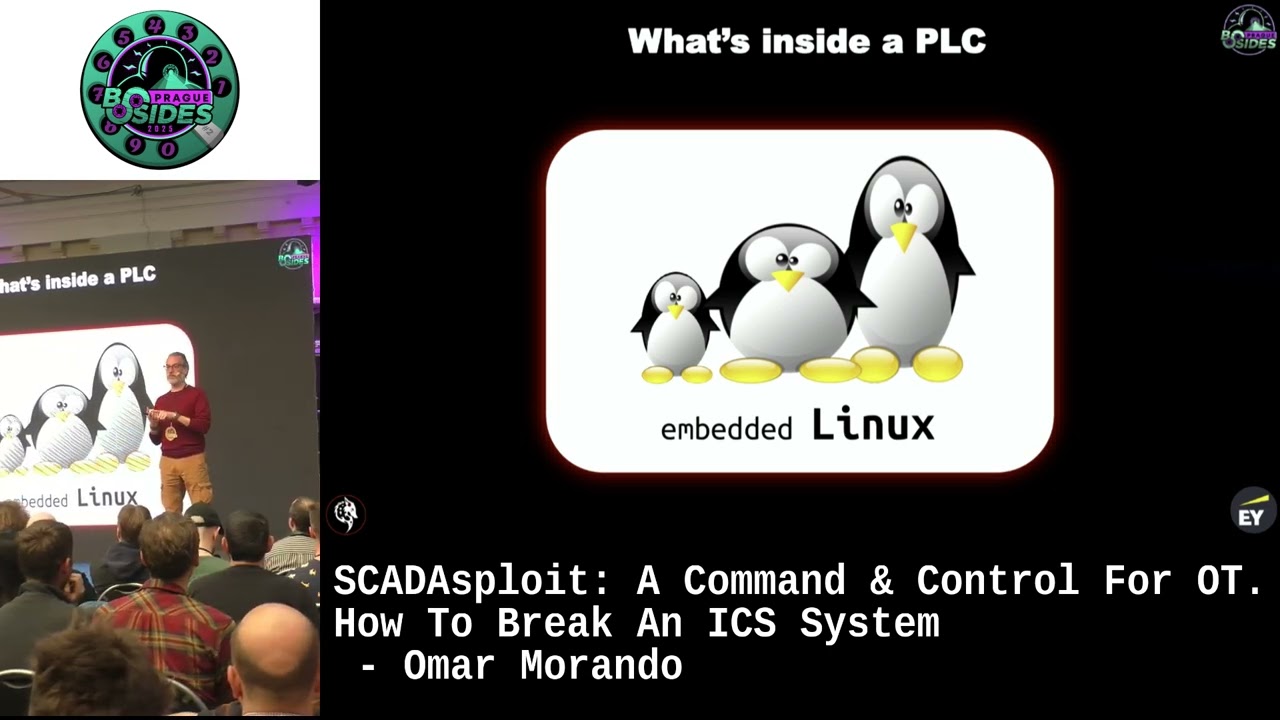
historian send all or better get also speaking generally speaking is a is a standard configuration of an industrial plant but what's a PLC the dark side of the force. PLC is a strong equipment is something absolutely unknown for the most of the of the expert uh it expert but it's absolutely a basic embedded Linux system in most of the case that means PLC is a computer with a sort of link Linux or Linux like operating system with realtime capabilities without monitor without keyboard without mouse sometimes you can find a USB port back off is a producer that put inside a PLC a USB port I don't know why but okay but is a computer with industrial
capabilities that means means industrial grade in term of temperature, in term of power supply, in term of humidity, but it's a computer and inside a computer you can find more or less Linux based operating system. For example, Aaron Bradley very long story micro OS9 is a version of Linux B&R producer Wix works. Wix works is a standard Linux used in real time application. Wix works is used also in aerospace for example. Uh it's used for industrial keep and generally speaking. Rockwell in the control logic use Wix works Schneider I worked at 15 years for Schneider Electric so I know a little bit in details and uh it use Unity OS Linux OS Wix works Schneider in old
version Simmons Simmons S7 1,200 1,500 it use Adonis what's Adonis Linux and then we have some strange equipment call it win IC is is a mix of uh industria computer and PLC in the same box use Windows real time. It's very funny and then Bago it's use Linux realy. So why I I use this slide or I would like to underline the presence of Linux because if you are a very uh expert in embedded system you can also are expert expert in OT and PLC is more or less the same. The approach is the same. I show you if you take a Simmons S7 1,200 PLC is a small box compact PLC. The price is around
5700 up to 1,000, no more. You can open this picture. I I did it. Uh you can open the cements and inside you can find a very simple CPU that is called it cortex ARM Cortex R4 that is the same uh CPU of the M4 but with realtime capabilities. Cortex M4 maybe is could be possible is inside this one. It's very simple chip, very low price. uh used for I don't know cortex m4 Arduino do you know Arduino uh electronic device for IoT for for the garden or for the light and so on okay use M4 Cortex M4 for example the R4 version is the same with the sub the same subset of register information but but with the real time
capabilities that is more reactive okay but it's more or less the same cortex R4 Four is also used for embedded application automotive I imagine or mass storage if you have I don't know NAS NAS or industrial MCO components uh it's very interesting because uh when you put this object this device to control your plant you don't have a octaore with I don't know 32 GB AB of RAM with high performance uh uh multi-threading, multipprocessing. No, you have a very simple and small CPU, mono core or dual core. Sometimes it's depend if you want to pay more. You can take the one 1,500 PLC version that is more powerful two core. No, not not bad. But the the level all
the application that run inside the PLC are are handed by this small chip is very small. The the the image is big but the CPU is very small. That means that this CPU is able to communicate using I don't know profet S7 all the industrial protocol for the SIMs handle the application that means read the input elaborate program activate the output and then again for 30 years maybe has inside a website. Why website? Because industrial 4 technology it you can browse your PLC using a standard browser. You don't need to have the specific engineering software that in SIM is call it TIA portal. You don't need it. You can open the browser puts the IP address and then
you jump inside the PLC. not completely inside meaning page inside obviously but the web server is handled by the mo small chip that means that you if you are on the network you are on the network you are connected in profet modbust DCP or aetcua what you want no worries if there is a switch with a port you can connect your PC and then you can do a end mapap scan It's very easy, very simple. You can do an NM map scan using a T4 parameter, very aggressive and very strong. You can put down your PC in maybe 5 seconds, no more because this PC is not able to handle all the special crafted request sent by and made and map
and in a aggressive way because the the CPU is is alone. It has to communicate. It has to control the process. It has to web server. It's very complex. Adonis. This is Adonis. You can revert the the firmware of the PLC. It's not so hard. It's it's funny. And you can find the extractor of Adonis. Adonis is the operating system is a Linuxbased kernel separating two library two services I say. Uh the okay the light is impossible with the screen. Uh on the left you have all the operating system uh operating system services to control the file systems communication and all the device on the right you have all the automation related services that means the
application services provided by semens that means uh semens uh I don't know control IO alarm subset or um automated web programming as I said before the web server inside and so on. But if you are talking about a standard Linux more or less a standard Linux kernel, we can use the same approach to attack this kind of hardware. For example, for the web server, if you run, you can open the browser as I said before, put the IP address and you reach the PLC. Then what you can do you can open a terminal and you can use your deer dearbster nikto go buster standard pentester tool use it in it you can find interesting uh command and uh or in this case using
barset uh you can find some get request handler to discover something that could be interesting for an attacker, not for a for for the Simmons or for the user of course, but okay. And you can find some comments that you can use to interact with the device to grab more information provided as a standard. Okay. Another important point is a Linux and the application are sandboxer. That means every application in this kind in in this case the standard application are in the sandbox. But as as a standard approach you can have or you can find for example some vulnerabilities as in this case is a sandbox escape that means you can bypass the limitation of the sandbox and then
you can reach other part of the memory other part of the file system other part of I don't know of the system okay you you can say oh this old CV is a 2020 20. Now we are in 2025. Okay, consider that PLC the the life cycle of the PLC is more than 20 years, 30 years, sometimes 40 years and in some case the PLC are never stopped. That means that they work 24 hours, 7 days, 375 days by year. without stopping and is not so easy to update the firmware even if you find the vulnerabilities and sometimes I don't know someone tell you guys there is a vulnerabilities in your PLC please update okay next time that means I don't know
one year later because when you update your firmware inside the PLC you have to do two important things one is stop the production and if you are in a standard or low-level manufacturing plant that is not a problem if you are I don't know in a critical situation you cannot stop because it's more expensive sometimes one day of stop of a plant means $1 million okay so it's very uh hard to stop a plant to update and solve a potential vulnerability inside of your Okay, I know but I have to work. Business is business. The second point when you update the PLC inside the sorry the firmware inside the PLC you have to recheck all the pro the the plant retest
all the plant because a new future or new version of firmware can introduce a different behavior in industry. It's absolutely standard. Okay. So it's very expensive. It take a long time to do that. So customer prefer to okay cross the finger. I know that there is some vulnerabilities maybe but okay we are lucky. So why a C2? I I uh generally speaking a commonant control uh is very interesting to evaluate uh the posture the cyber security posture of the infrastructure IT or OT is the same. So adversary simulations this a standard kill chain is a Loit Martin cyber killch chain is a standard approach when you do a pen test uh you have the similar or the same approach
that means you have a recognization phase the first grab information uh browsing or scanning the network find finding some vulnerabilities using map using I don't know nus using tenability or all specific for OT you can find OT of course clarity noomi guardian uh I don't know radiflow IC there's a long list of potential uh technical provider of of tools or scatterlo why not okay but okay you can grab information on the network then you have a second phase is a weaponization that means okay I found some vulnerabilities now I prepare my exploit to um to take the advant to to exploit the the vulnerability. Then I try to deliver my tools, my exploit, my beacon, my stage. Then there is
exploitation phase installation common and control. When you reach the level of command and controls means that you have the total control of the target and remotely with a very simple user interface that is called remote commander you can interact with the target with the victim uh doing lateral movement uh pivoting grabbing information and so on. I will show you in a video why adversary simulation in OT because sometimes when you scan a network searching for vulnerabilities you are not able to really understand the real posture of the cyber security is a realistic track scenario that can find the real potential attack vectors. not only the potential in term of theoretical vulnerabilities is a response evaluation. Sometimes
uh with it in Italy we we use this approach in many many plants in many situation and uh sometimes used for also for sec sock assessment security operation center assessment that means okay uh our our um our detection system our configuration our analyst are able to find and to interact act and to identify potential threat in real time maybe yes but you have to test it maybe yes is not the right answer you have to evaluate because if you don't do it someone else will do okay so how a common and control works generally speaking you have a team server sometimes the team server server is a web server is a standard web server I don't know that uh sell a t-shirt for
example so you can reach this website and you can find the standard website when you interact with the website using a specific get and post header you have access to a back end that is the theme server that's why it's not so hard and it's not so easy to identif ified team server on the network they are present but they appear as a standard website for travel for by I don't know for social for example but are in but in the back end they are team server for common and control we have the commander remot commander to interact with the team server and then we have the agent or beacon or stage I don't know you can
call as you want but is a small software that affect the victim and communicate with the team server exchanging information in different protocol HTTP, HTTPS, DNS over HTTPS for example and interact with the team server. The attacker has a list of the victim and then decide okay I want to interact with this victim. I want to grab information avoid to steal information or get I don't know some screenshot or use the victim as a pivoting computer to reach other computer on the net or you can approach using external C2 for example you can use one drive drives lack teams to communicate with the big team it's more difficult to find to identify this this path but it's absolutely common
using the common and control this more or less the standard architecture of the common and control so why a situ for OT as I said before this is a standard architecture level zero up to level five the dream here in yellow the the Chinese industrial and the pink is the corporate and some uh uh vectors standard vector used by attackers to attack plant are for example insecure Wi-Fi connection of course supply chain attack if you are a big company maybe you have you are strong in the cyber security but your supplier is a small company that produce I don't know a very small machine and be not so uh strong in the cyber. So usually attacker can grab try to grab
the credential of the third party uh supplier to reach and to go inside the network inadequate access rule internet consection fishing and so on. And another interesting uh behavior, strange interesting behavior in in not is of course the infected USB. USB in OT is absolutely common. You need to have I don't know a manual. You need to transfer a file from one machine to another. You need to I don't know to store something. USB absolutely used in in OT domain. And the other one, the last example is in infected the laptop. That means I'm a maintenance, I'm a programmer, PLC programmer. I need to change the I don't know two lines inside my PLC. I use my
standard laptop that usually I use for email, for teams, for download, for navigate on internet. Then I go to the plant. I change I connect my computer to the PLC. I change the software inside the PC and then I come back to my office. In this case, I bypass all the potential DMZ firewall rules ACL. I don't know what because I use the same physical PC that I use in IT domain. I put it in the domain. Yes, but I have the ADR inside. I have a very strong antivirus. Yes, it's true. But sometimes the malware is targeting the OT domain. That means behavior analysis doesn't work because it's able to identify that is in IT domain. So
it's absolutely uh quiet is not active. But when you put your computer in the OT domain, the malware is able to identify the industrial protocol like Modbus ICS um modus TCP or Profet or device net or other industrial protocol and then the malware wake up. Okay. So scatterloit is a commonant control that you can use for adversary simulation in IT but I developed around 100 modules auxiliary and exploitation that are targeting OT domain that means that you can is able to bypass ADR up today tomorrow could not be true I'm C1 ATW bypass anti- sandboxing anti-debugging and so on. But what is absolutely important that is the post exploitation the the arsenal of the of
the database of the modules is targeting 10 minutes. Thank you. Is targeting uh PLC producer like Simmons, Schneider Electric, Rael, ABB and others. the dropper file how to compromise the target the dropper you can drop using filebased dropper or PDF a PDF is more or less the 65% of the dropper today in IT domain okay then office you can use some interesting approach using XL to bypass the protection of of Microsoft USB web so you And you can this a typical approach used in in a sock assessment that we did last year using for example an open EXL uh that can that was able to bypass the mark of the web for example and is not a
macro is a is another kind is a DLL for Excel and is accepted by Excel by Microsoft by Windows by by the user usually and it's interesting. So a demo demo I have uh a video here with three virtual machine. Go ahead very quickly. The video is 25 minutes. No I'm joking now it's 5 minutes. So we are in time. Absolutely in time. So this is a virtual machine with Windows 11 updated. Okay. Uh, I showed you that I enabled the defender and another ADR that I don't want to show you, but okay. The real time protection is activate then. Sorry, I can Can you see? I'm okay. More or less. Okay, I can do that. It's better. Yeah.
So on the left we have a simulator PLC simulator inside the virtual machine. On the right we have another uh virtual machine Linux virtual machine with a HMI simulator. Okay. This is the remot commander of scatterloit. I have the same logo here. So I believe in the project I think more or less. This is the commonant control uh the remote commander of the of the scatter spot. You have uh sorry very very very very quickly before to uh very short introduction the team server is something that is run on the website okay and is always always is listen for a victim. So you have to create a listener using a different protocol different IP address
a different port and is wait for a victim. Then you have to create your malware your stage to compromise the victim. There are some parameters uh you can select uh usually we use window shell code shell code with uh encryption with some uh other uh parameters if you want. We can go into in deep detail but it's not so important now. Uh is encryption to bypass the the ADR protection the defender protection. Then you can generate your beacon. It is the beacon is developing in C and R assembly language. Then you can put in your folder. It is my computer. So there is no secret inside more or less. And you can save your beacon. Now you have
after that you have to compromise the victim. In this case you can compromise the victim using PDF and so on but there is no time to do that. So very simple. I open a browser. I in my computer I have appd doc a web server that can use in Python. I put the IP address and then I download the malware. In this case is a demo. Okay. I download the malware. Defender ignore completely the malware. This um Windows tell you do you want to store? Yes. Keep away. No worries. It's only a malware. Then I run it. It's very simple. And the magic happen. Boom. This is the victim. Now the victim is connected to the web
server, the team server. And now I can this team server. I can interact different command. I can interact with the rhythm. I can try to grab information uh from from the PC. I can send some exploit. I can send I can do something. But okay, I try to interact here. I have a list of potential command. Who am I is the first command and now this information of the Windows 11 in the virtual machine. Okay. The groups or the information domain and so on. Yeah. Then scatter. Okay. I can grab a screenshot. For example, this is a cast the screenshot of the PC. But is his joke is not so relevant. Oh, maybe. Then I can use
scatterloit in the right version. I mean I have two one PLC and one HMI connected to the Scattera system. my Windows 11. Okay, clear the screen and then I use a command of scanning. I mean I reached the target. Now I have to find the OT devices PLC and HMI. How to do that? There is a command. In this case I use a Modbus TCP protocol. I use a command that is called it OT Modbus scan. I put the address a range of the address uh CD CDR that means slash24 or in this case only two address and then I find two device the PLC and the HMI exactly with the same information provided by the B2 machine the
simulator. Okay, I found the two device. I go a little bit faster in my network map. I have the PLC and the HMI connected to the Scattera system and I can interact with the PLC. For example, I know that this kind of PLC has a vulnerability that I found seven years ago. So I can use an exploit that can do a denial of service of the PLC. The exploit is this one. I put the IP address on the bottom and then the PLC when I run the exploit the PC go in crash. It stop. This is a simulator but I do with a physical device. That means you can stop the PLC and you can stop absolutely all the
communication, all the interaction, all okay. Okay. So we are in time uh sorry. So make it safe. How to do now? Uh it's absolutely important to put in place organizational measures of course security assessment, security assessment, risk assessment, business impact analysis, supplier management, policy and procedures in term of technical measures, asset inventory. You need to know which kind of IoT device you have in your plant. An important customer in Italy said, "I have 500 PLC." Okay, we do an asset inventory and the device was 960 more or less the double. Okay, vulnerability scanning, network segmentation monitoring endpoint protection, secular PC programming and so on. There are a lot of standard industrial standard like EC6 uh
62443 or MITER attack for ICS. The knowledge is on the web is not so hard. You have only to put information and to to want to do that. Aware awareness of the security important on validating is the takeways knowledge of how is very useful red teaming and take care of your cyber security or system because if you don't do it someone else will okay thank you so much. I'm in time, I hope.