You Got A SIEM Now What
Show transcript [en]
all right thank you everybody uh for coming uh topic today is you got a Sim now what we're going to go over some predeployment uh some deployment and some configuration things that you should do with the SIM to get the most out of it whether it's from an MSP or from a uh an open- Source Tool uh a little bit about myself I'm lead security engineer at integral uh I am the co-founder and principal security engineer for adonic information security I have taught uh the same topic with cyber X Elite um I have a degree computer information systems I've got you know your laundry list of Standard Security certifications not that they really matter uh you don't have to have a ton
of that stuff to uh get into this field anyway uh overall 19 years of it experience and N9 years specifically in security with the majority of that coming in The Blue Team operations uh Sim side of things so this I thought was funny which is why I added in here I hear from a lot of clients and a lot of other people that uh they think Sim is dead you know according to Alysa I'm committing the cardinal sin but this one was funny so again a lot of people think these other tools can take care of and do everything that a Sim can do when in reality the Sim is what you need to correlate and
bring all of the information from these other tools to together to provide actionable information on your security events that happen so what we're going to cover kind of touched on this a little bit we're going to what a Sim is predeployment some Sims that are out there what the what people think are sims that may not be may just be log collection pros and cons of having one where you should start you know regulations that kind of stuff if they requirement what to log how and where you should get it from deployment and configuration you know I go through a stepped phase for this and we'll touch on those phases later in this talk uh avoiding aarm fatigue and
your business use cases this is huge with a lot of Sims people get them throw them in assume everything's just going to be good and this is where they lose their value because people just don't know what to do with the thousands of alerts that come in um I'm going to touch on adding threat Intel into your sim and how you can use that to better correlate and enrich the information that you're getting and then I'm going to go over bringing it together at the end which will allow us to kind of have a good idea comprehensive how you go from start to beginning with your sim deployment so what is a Sim this is kind of what I use for it
it's your information invent management a lot of people can consider them to just be log collection systems uh I'd consider that more a log server or CIS log server um Sims you want to trim the information that you're sending it to be more security specific uh you don't want to just throw everything at it because then like I touched on you're going to end up with your alert fatigue you're not going to know what you're looking at so using it for your specific security event information and uh setting up that uh rule-based statistical log correlation so with this using surot snort tools like that that are going to analyze your network traffic and see those tools like HIDs wazo osc that are
also going to provide you information that you can use to correlate and uh generate events normalization of logs you get some Sims and some other log collection platforms out there that don't actually make them human readable uh so when you do the research make sure you find one that's going to make them human readable and you're not going to have to sit and actually search through each of the fields that your logs are being sent centralized logging this one I kind of touched on a little bit earlier as well but you don't want to throw everything at it if you throw everything at it you're going to have a headache you're going to lose value you're going to get
sick of it and you're either going to waste your money or your time depending on if you went with an MSP or an open source software preim so with the preim there are some things you should have in place before jumping to a Sim everybody thinks Sim great right so okay what are you actually going to send to it what do you have for information that you can use having an IPS or an IDS system in place is going to give you something to send to the SIM for correlation AV EDR logs do you have a centralized log source that you can send these two having this in place pre Sim will give you that
information that you can also sell uh also send firewall logs these can be used for a lot of different things depending on how your firewall is configured you can be using it as like a web application um casby type solution where you're going to figure out what kind of applications are being used or just your typical Network traffic what's logged what's dropped you know what's blocked kind of information other security tools and information and applications so what I mean by that is your casby's your waffs all of your other shiny little tools that vendors like to sell you to try to secure your environment having those in place and configured correctly is going to give you the information that you
need to send to a Sim to get the value out of it Cloud environments these can be tricky uh you're going to have Azure GC p and AWS you know some that you can send from Azure Defender for cloud cloud security logs things like that AWS you've got Cloud watch cloud trail guard duty all of those are other ones gcp you've got all other kinds of logs that you can send from there as well um kubernetes logs and things like that that you want to send and monitor uh can all be sent to them some some Sims don't actually work well in Cloud environments and others do predeployment so these are things you know you've now you've gotten
your approval you've got it coming in you've got decided whether you're going you know open source or not um is it compliance mandated you know do you have a HIPPA requirement where you have to maintain logs so that you can size this appropriately you want to make sure that you are having enough cold storage and hot storage in order to be able to search these if you get audited or in the event you have something happen you can go back and pull the necessary information from them without having to say oh we only kept two years of logs when in reality you may have needed seven so you have to be able to set configure these
appropriately uh is there a certain subnet are you limiting what you're monitoring so in some environments people only want to monitor their PCI environment they only want to know if a credit card has been accessed or that data is going across the environment so you want to know what you're monitoring uh whether it's your whole network a specific subnet specific environment subset of servers even you want to know what you're monitoring and how you are going to apply these loging Concepts to your sim are you looking at everything having that idea again going back to the tools that are in place and your endpoints are you doing EDR is it on all of your end
points you know what's your success criteria are you wanting 100% coverage are you okay with 80% coverage having that and understanding is going to give you the idea of how big you have to scope this do you want everything no you don't we touched on this earlier you only want your security specific information and things that could indicate something nefarious going on within your environment how big is your sock team this helps with if you're going to go with an MSP or use an open source software if you're going to use something open source like Alien Vault or alien vault's osim or security onion there's a lot of deployment and configuration that has to happen along
with maintenance if you're going with an MSP you could have a one or two person team as long as they're doing the appropriate analysis and using you as the escalation point then that would be what you would do typically again a lot of this is dependent on the size of it touching on this mssp or in-house this really comes to budgets is are big like if you have budget to get an mssp great if not there are open source tools there are things you can do to at least get something in place to give you that visibility into your network and seeing what's going on paid or free and open source we're going to touch on this on the next slide
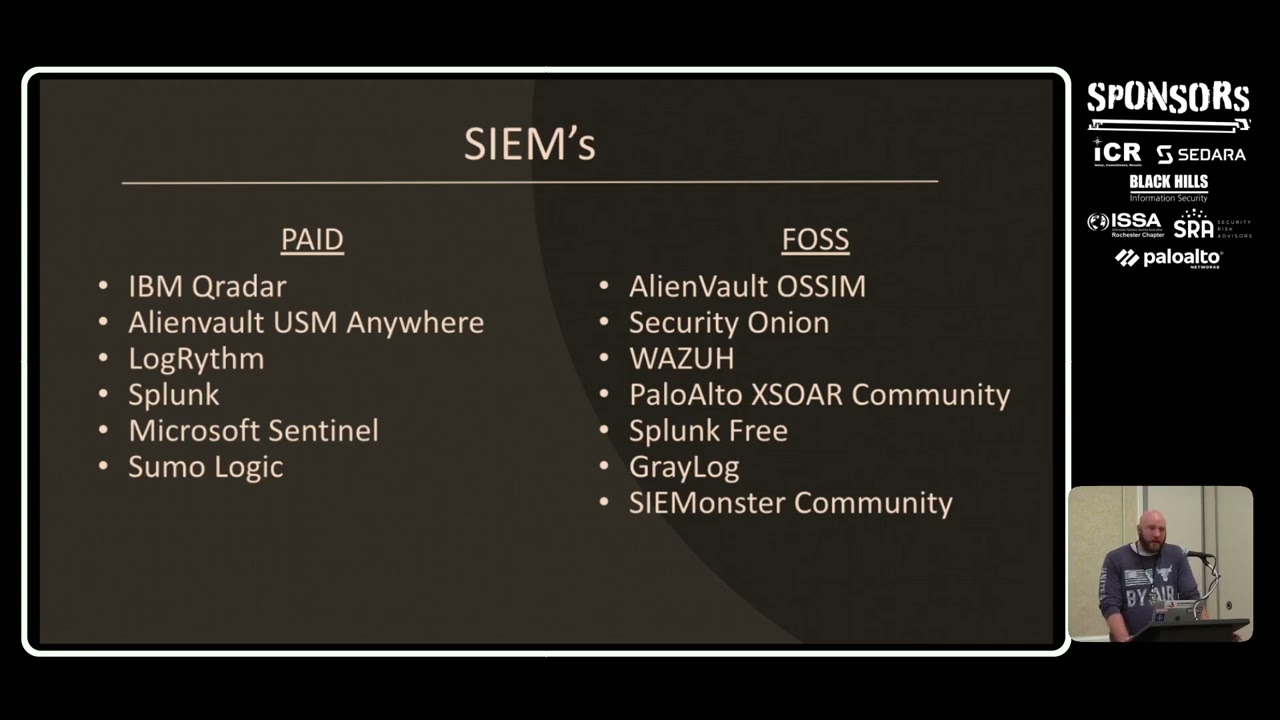
a little bit about certain ones that are free certain ones that are paid and how you can use those to your your advantage so Sims your paid ones a lot of them are IBM Q radar Alien Vault USM anywhere which is mainly in the cloud at this point logorithm Splunk to me it's more of a log log collection and Big Data tool than it is a Sim Microsoft Sentinal and Sumo logic just to name a few Google is coming out with a new tool that they are going to be putting out um allowing you to do a lot of sore and Sim automation Within gcp free and open source ones which I tend to use a lot with clients and or smaller
organizations so that they don't have to see sticker shock when they get these paid versions of a Sim you got Alien Vault oim yes it does have a limited set of rules but you still have the ability to have some kind of visibility into your network and you also have um some other parts of it that you can do with HIDs and vulnerability scanning within Alien Vault security onion is another one they do a lot of work on this uh so if you do select security onion be aware there will be some maintenance on the back end they're currently looking at decommissioning oek and moving to wazo specifically because it does offer a lot of the same
information so if you currently have a security onion deployment when you go to upgrade there's going to be a hefty uplift for your upgrade uh wazu this and themselves does offer a lot of of different tasks and things that you can do within it as well as HIDs and nids and correlation engines like snort that allow you to um operate in that Sim functionality palow alto's exor Community Edition I haven't played with this one too much uh but it does give you a little bit of information spunk free this limits you to I think five gigabits per day or gigabytes per day that is extremely small uh for most people it's not going to be
even functional it's more of a POC type thing if you're going to use it gry log there's a lot of rules a lot of Community Development you get into the paid version of gry log you get a lot of the correlation and different kind of stuff with the free version you can use sidecars create your own rules and do a lot of it does have some good um readability with the logs uh Sim monster Community this is one I've used it's very res intensive so you're going to need hardware for it um it runs a lot of really good things from The Hive which is a um a case management type system to doing vulnerability
scanning and HS and nids traffic analysis as well so these are some free and paid ones there's a whole bunch out there um that I'm not probably for that I probably well I am forgetting as there's new ones out there all the time so always keep an eye on it always look uh are you g t on the yeah yeah so just to touch on that real quick paid can uh if you don't have an in-house sock you're going to just be paying for a tool and not really having an understanding of what's going on uh free and open source like I said does require a lot of um de not I wouldn't say development but maintenance and
understanding and the ability to get into a lot of these are deployed on Linux so you need Linux engineering to be able to understand the coding and modifying of the rules uh a lot of that understanding really to to make it so you're going to have a lot of information a lot to do with the um a free and open source one they're community supported so there's not a lot of support if something breaks if you get a paid one there's usually some kind of support you can call that comes with it so those are some of the just a few of the pros and cons of that and we can I can so this is just the gardener
quadrant you know everybody likes to show the G cadant for everything um you know this is just a basic you know who's who of the popularity contest really because as long as you use your sim the way your business is you could have the one that's down here in the you know low completeness of ability and ability to execute B as long as you're using it for what your business case is and your use case is you're getting value out of it that's all that matters benefits of having a Sim again we touched on a little bit of this uh you've got centralized logging for compliance again I talked a little earlier you could have a hippo
requirement PCI regulation gdpr uh you got to be careful with that not to pull your stuff across the the the pond if you do have that uh especially if it has IP information in it it can it can get dirty to try to do that um event normalization this allows you to make them human readable most of them are but if you've ever you know C at a log file in Linux they're not very fun to read they don't they don't make it very easy dashboard views of alarms These are nice um having a dashboard to look at for an alarm or a number of alarms makes your life a lot easier rather than sitting
there and actually having to go through something one by one um security onion does have a dashboard it's in kibana but when you're looking at them one by one in the security onion console can get a little tedious for that um the ability to search logs so this comes to having all of your logs in that centralized location if you wanted to do a threat hunt you wanted to see what was going on you want to look see if anybody's executing PS EXA across your network you can do that from this from centralized console and having that uh correlation of events when you do a search searching to say hey I have seen this event here
around the same time of this other event there may be something suspicious going on here and using that to correlate that information minimize your time to detection not having something in place and then just kind of responding out of the blue is not going to help anybody uh when you did you know hearing your user say hey uh I got this Ransom note on my desktop is not always a fun fun phone call but if you were able to detect something suspicious going on with someone scanning internally on your network doing internal Network Recon trying to use privilege escalation you can probably see that prior to the malware executing within your network which again minimizes your time to
detection and creates the ability for you to stop getting to that final phase of the attack and again it gives you the whole picture like I just talked about of what's going on in your environment cons of having a Sim they're complex systems this goes to your question about uh having a paid versus uh free and having um support they're very comp complex systems and without having someone who understands it or can support it you're going to not get the best value out of it you're going to have someone who's doing a lot more time researching things than they are managing it writing rules rules reviewing alerts and alarms and things like that a Sim can become a oneperson
job uh if you don't want them doing anything else um it's not going to be something that keeps teams busy all day it can depending on your loging gestion and the number of logs you're getting but if you're a small organization a Sim deployment can become a single person job which will put a lot of your other Security on the back end time to deploy again paid versions they'll usually help you deploy it uh free and open source you're on your own you got to deploy the HS agents to the machines make sure they're connecting validate the information set up your span ports and all that stuff training for someone who doesn't understand the system when you
purchase a sim a lot of times uh they'll give you credits for a training class to get some kind of certification Alien Vault has their Alien Vault certified security engineer which you can get if you've purchased their their Sim uh again a lot of the other stuff like security onion Community Based not a lot of training out there you have to pretty much read the manual which can be tedious for a lot of people I don't know a lot of people that can sit in front of a computer and read hundreds of pages of a manual in order to actually understand how something is going to work to get it to be the best possible solution for you
what to log in why so your DNS logs these are key I know everybody's moving to the cloud which makes getting these DNS logs hard but having these is going to allow you to see malicious DNS queries it's going to allow you to detect queries that are to domains that aren't coms you can go toos do you know cosos all of that stuff and even detecting other DNS queries that are malicious or in malicious in intent you know djas things like that can all be detected using snort or surcot which gives you the you know makes these huge also during the investigation phase having these makes life 10 times easier if somebody says hey I clicked on this
link you can say oh okay around this time you clicked on this link and this site was where it took you you can then correlate that with the DNS log and say all right I can actually see where this traffic happened I can see where it went then if you want to go play in a sandbox environment you can go to that link download it on something put it in something like any any or any run. apppp which will then show you network connectivity and things like that and give you more ioc's to go and search your environment for window windows and Linux system events a lot of these uh you'll be setting up on a domain controller
typically uh you'll do things like adding an admin to Enterprise admin schema admin domain admin users being removed from those groups um Linux CIS log events somebody pseudo to root somebody changing file permissions uh if you're doing fim things like that are going to give you a view into what is going on in your environment on those systems again in the cloud makes it a little harder because you've got Azure VMS and you know if you have something to collect those logs in aure are great otherwise you're going to be paying for bandwidth to download them somewhere so having that deployment figured out and understood early on is going to help you uh with these as well your AV EDR logs
again we touched on this earlier having that centralized logging which is going to allow you to pull that information and a lot of Sims will have a connector or an API ability to pull those in which makes it easier again Pro versus con for paid versus uh unpaid is paid is going to have support for that API probably going to have documentation for that API where you're probably going to spend a couple hours searching for it for an Open Source One Niche traffic I love this but as people move to the cloud it's making my life a little bit harder uh nich traffic gives me the ability to see what's going on where traffic's going look at things
like data transfer and put in rules to say if someone uploads more than 50 megabytes in 30 seconds I want to know about it and gives me the ability to really look into that information that net flow data are huge which again getting into the cloud is a little bit harder you can still get this kind of stuff in the cloud but it's a little harder just because of the way things are set up in the cloud and if you don't have your v-ets and firewalls set up appropriately you're going to get a lot of stuff you probably don't need to see but Niche traffic will make your life a lot easier in an incident uh response
role giving you the ability to see a lot more of what's going on if data was actually exfiltrated if data was taken things like that um how long they were in if they downloaded anything into your environment things like that you can see command and control uh type uh things application logs so these tend to be more audit based than and they do um uh yeah they're just they're more audit based than Security based but having some in there that you could get from a W uh or something like that that gives you the ability to see if there was a SQL injection attempt or some other kind of attempt on that Network or application to either escalate
privileges break business logic things like that within your environment will help you Cloud environment logs Cloud watch data dog cloud trail Defender for cloud uh Windows security logs in um Azure the application security logs from Azure ngcp you can get um other kind of other logs as well which I don't have a ton of experience with but um the AWS and Azure ones are the big ones so these are the four phases that I typically take when deploying a Sim whether it's open source or paid uh I kind of try to dictate the deployment as best I can to avoid alert fatigue and to make my life a little bit easier so with HIDs you
determine whether you're going to use osc which I spelled wrong up there wazu NX log or SS log NG um a this is going to help you with your asset inventory you're going to see what you have for a number of machines sometimes you're gonna see that your cmdb doesn't actually match up with your HS and you're gonna say oh well we've got more computers out there than we actually should or that we knew about uh it allows you to view authentication logs and things like that but what you want to do and this is the big part here for each of these steps is kind of a a wash rinse and repeat type thing you want to look at the alerts and
tune as necessary before going to the next step and I can't emphasize that enough because it's going to help help you avoid alert fatigue doing this at each level and each phase is going to make your life easier rather than just throwing everything at it take the time to review these logs Now understand what's going on at this point understand what you want to see tune stuff out if you have to but don't just move to the next step without reviewing these alerts because if you do you're going to be in trouble DNS logs again a lot of these can be done with the same agent uh again it helps with your queries you're going
to filter you can filter unnecessary ones these can get noisy there are you know DNS queries to Windows update um and legitimate traffic that you actually know once you've let this run for a week week or two understand what your business is doing Within These DNS queries you can go in and tune out things like Windows update or Google go.com those other types of known safe sites if you want to call it tune those out you can still collect them but just tune the rule to say I don't want to see these specific domains in alerts that will allow you to minimize the number of logs you have to sort through when you have an event and then the number it'll
keep the size down in your actual hot storage you can just store your other ones in cold and again look at them as you're doing it make sure you're tuning it make sure you're updating it make sure you're communicating it and continue to move on to the next phas firewall and nids logs so these you can for nids logs you'll typically set up a span or a tap on either your firewall or your core on the internal side so you can see your North South traffic this is what helps you view your um your data exfiltration if somebody's downloading something potential C2 commands things like that um firewall you're going to do your firewall rules
whether something's been dropped added um new rules been added removed packets are being dropped you're getting a certain number of inbound packets on a specified Port things like that whatever your firewall can alert you on from those certain things and again you're going to determine your use case for these and then you're going to tune what you specifically need you don't want to keep anything that is going to cause noise or you a headache because you didn't tune it you didn't understand what your business needed you to do and you didn't understand the use case behind it so phase four EDR and application logs these are typically your last ones you bring in and along with Cloud which I don't remember
if I put cloud in here but so we'll touch on that as well um a lot of these for your paid versions have apis they can use for your free versions they don't um you can have things like gry log which has side car to pull stuff in you can have the ability to send stuff to it via just CIS log if the Sim supports it again the last two steps are huge you're going to determine your use case understand what's going on in your environment and tune as necessary so I'm going to go back here just because I want to touch on cloud and that's the same thing you want to understand and configure them to send
to your sim whether your sim is on Prem or in the cloud if it's on Prem you need to figure out how you're going to get these logs into um whether you're setting it up with a forward node in the cloud or if you are just using a single manager type node that is going to collect everything on Prem which will then allow you to then you have to send everything on Prem which means you have to pull it down which means you have to P pay for bandwidth within Azure and AWS those are things that you want to think about because if you're having to pay for that that's going to increase your costs of
your sim whether you're uploading stuff to the cloud or downloading it and then you have to pay for storage uh in the cloud as well so you got to think about those things because you're going to increase your costs which when you go back to your manager and say hey I need another five grand because our bandwidth costs went up because I'm pulling all the stuff down or sending it all up they're not going to be too happy with you when they've already approved you know 50,000 for your sim that you just wanted threat intelligence so bringing in threat intelligence at this point is going to allow you to bring in things that are being done by for example Alien
Vault otx uh there's a lot of good Feeds out there a lot of companies a lot of uh researchers will submit things create feeds that you can compare against your data so you can compare against your DNS queries against a list of known malicious domains to say hey this malicious domain is in my environment why am I getting this alert who's going to that uh so you can do that and that's why DNS logs are huge misp sharing servers and then this GitHub link uh is also a great source of threat intelligence um but there is also there are also things like paloalto um mandiant threat feeds things like that there's some paid stuff out there that
if you choose to go the paid route for your threat intelligence you can uh but threat intelligence really adds enrichment and value to your sim once it's configured correctly uh I wouldn't jump to add this in until you know it's functioning correctly and you're getting value out of it because again just like with taking the phased approach this would be phase five where you want to actually make sure things are working and um functioning appropriately in your environment this is just a screenshot of one that uh was deployed early on in my career where I just threw everything at it and didn't really do what I'm telling you now to do this is what is going to cause alert fatigue
you're going to see a whole bunch of alarms a whole bunch of information that you really don't know what to do with um this is a screenshot of an Alien Vault deployment uh so as you can see you've got a whole bunch of delivery and attack up here which is that line that's got a bunch but um had the stepped phase approach been taken it probably wouldn't look this bad it' probably look like the other three um maybe it would have been the same depending on what the alarms are seeing as they look like their Brute Force authentication it's probably something from the external somebody was scanning trying to get into something but again had we taken the time at the firewall
log level we may not be seeing these because we could say all right let's tune these out and do that now when you're trimming the noise this is what it should look like this is what you want it to look like you want a limited number of events per day you want actionable events things that are either going to be misconfigurations actual events things that happen in your environment this is going to allow you to get the most value out of it allow you to really get that business value to show to your executive say look we're getting value out of this we're doing X Y and Z we've gone from 70 alerts down to five alerts down to two alerts per
week and we're being able to focus on other things because we've got this tuned we've got the correct information and we're doing all this a lot of people will take this and be like oh I can't show this to my boss because they're going to say I have no work to do wrong you can spend your time doing threat intelligence research finding other rules tuning rules writing better rules to help your business case Sim engineering isn't all about just doing uh alert response it's writing new rules it's updating the systems it's making sure things are functioning verifying logs are still coming in things like that avoiding alarm fatigue I've touched on this a bunch through this and this is
a huge part of it even socks at msps can experience this because of how quickly they try to onboard and deploy and just move on to the next client take the stepped approach for getting logs to the Sim it's going to make your life easier I promise you that understand the business use case and the rules that are necessary not every rule is going to apply to your business there may be a rule that applies to a financial company that doesn't apply to a healthcare organization there may be those two that have the same rule that doesn't apply to a school take the time to understand what you're looking for what you're understanding and what you're trying to
achieve prior to throwing this in and it will make your life easier don't assume that all of the alarms need to be closed at once just because something says it's critical doesn't mean it's critical I've seen critical events that are absolutely benign just because of the way the rule is written now that comes back to your business use case understanding that you can then lower and tune that rule to a lower value allowing you to then get better value out of your sim tackle the alarms based on priority now when I say don't close them all at once just because they're critical I don't mean ignore the critical ones look at them understand what it is and then say
all right does this matter if it's a brute force from the outside but you know you have a WAFF in place do you really need to close that and understand that alert right then and there probably not you have a compensating control in place you have the ability to see what's going on you can come back to it if you didn't have a WAFF in place or you saw brute forth authentication happened for an hour and then stop you might want to look into that because they may have gotten a successful authentication when those type understanding the attacks and the miter attack framework helps because you can say all right this attack happened maybe may need to look at this these
other types may not apply to you test it once you've get it deployed don't just assume everything is good to go everything's happy go-lucky and you have nothing to do use Caldera use something take a test machine detonate some malware that you download from mshare or something on the Internet and actually test it if you have a sock test their response time if you have an MSP run Caldera against the Sim test their response time if your contract has a 10-minute SLA and they don't get back to you for two hours then you have a conversation with them and say hey what's going on why am I not getting what you promised me I've seen
it happen I've been on both sides of it um you know again it comes down to You'll usually hear all our staff was really busy we had more than one attack going on at a time blah blah blah but every client deservs the same attention especially if they're paying for it so testing it is going to be huge it gives you a the ability to see if it's being effective and B it gives you the ability to test your sock and your MSP if they have it so using Caldera is something that we do and and we've done it for other clients so having that ability and understanding the testing that you're doing is going to allow you to really
tune and fine-tune and continue to work to get better at what you're doing and help your MSP get better but also help make your business get more value out of the Sim you're going to bring it all together at this point we've done it we've deployed it we've tested it now we want to bring it together keep repeating it from phase one every time you get a new server new endpoint new software new something do it again go back through the steps take the time to understand it don't rush it just to get it deployed continue to improve this goes to continually testing it continually test it run something new against it write a rule you know set up some kind of
malicious script to run to see if your sim can detect it um if you have a pen test and your Sim doesn't detect it take the report and ask the testers what did you do that my sim didn't detect use that information to write a rule because their offense should always inform the defense and help us get better it will always help and that cycle will always help so asking them and using a rule to create the using the information to create a rule is going to make our lives as Defenders easier learn from your mistakes if you miss something go back and do it again figure it out Alyssa touched on it earlier everybody has
their mistake well I'll tell you about mine I did an RM Dy SQL star on a Sim that was not good spent three days restoring the sequal database for all the alerts all the logs all the information for the client that needed to be restored so I learned you don't ever put dashy after any RM always check it to make sure you're removing the right thing never never say yes benignly think like an attacker if you can uh use the miter attack work use Caldera to inform you um read offensive articles communicate if you have an internal pent test team communicate with them to say hey what are you doing I want to ride along with you for 30 minutes so I can
see what you're doing to test against X application or talk to your vendor that's doing your pent test and say hey why didn't we get an alert here what did you do to avoid detection things like that those are only going to make you better only give you more information for your sim and more information to make it better and more complete understand the system and how it works this one it's it's hard um a lot of us have more than just being a Sim engineer on our plates we've got deploying tools managing EDR responding to EDR alerts um you know a lot of at my prior job I was also governance and doing policies and procedure stuff so you get
all of that stuff thrown on your plate along with vulnerability management and things like this you you don't get to really focus and hone in and understand a system so what you want to do is try to understand it the best you can a lot of us do learning on the side and after hours it just makes us a different breed of people because we always continue to learn we always continue to make things better so that really concludes it uh does anybody have any questions H uh in cases where um your uh Sim is being managed by um an mssp um what are some things that can help with tuning alerts when you can't get your hand
yourself so I'm actually experiencing this myself so the question is what can you do when the uh MSP doesn't want to let you get your hands in on the tuning yourself so dealing with this myself um you've got to push back you have to push back and you have to say look I need the ability to either a you give me a concrete SLA that is going to say I'm going to give you a rule that I need written and you're going to turn it around in 24 hours or B you're going to give me access to get in and test it and do it myself it's I've kind of won the battle that I'm fighting because I'm not
the only customer that has has been complaining about it a lot of sim Engineers prefer to get in and have their hands on it and be doing it and tuning and making things better for themselves without having to submit a ticket say I need this Rule and then wait two weeks for the MSP to turn around and say okay now your rule is created or better yet they'll turn around and say sorry this rule only applies to you so we're not going to create it we can't push it out across our customer base which I've seen happen so keep fighting the battle don't give up and eventually if you have to find a vendor that'll let
you go ahead app rules rules app
locan for do that and try to test so do you
so I just want to make sure I'm understanding you're asking about testing different locations so what I do is set up a Federated type environment where you can have a manager node and then at your smaller locations or offices set up forward nodes which would forward your information up to the manager node and then you have a storage node which is going to allow you to store all of your logging and information and do your searching from the manager node but yeah start with the smaller one and you can do a POC there but understand that you're going to have to scale it and Federate it in order to cover your entire
organization anyone else yep go ahead you mentioned um sis logs um and one experience I'm thinking specifically it was basically just a log agor um is there a methodology that you prefer for pulling some because obviously you're not going to let it off but pulling some of that into the Sim so typically what you'll do is you'll pull it all into the Sim and then write a filter okay so what you do with that is you'll get those logs into the Sim because cismon itself is just going to pull it and you're going to point it where it goes some of them you can write filters locally osc you can write a filter locally with a comp file that
allows you to filter out what specific logs you want or pull specific logs you want cismon I haven't done too much with it it's possible that that could happen but worst case scenario you can filter it out at the Sim level and say I only want X Y and Z logs from this Source go ahead so I've used before and I know you said that 5 GBS G
data notot ieas many right what would you I knowly depend for a small business what would you say the amount you want to think about like how much data could you from from an environment you if you I know if you added all the windows laws and all the you know endpoints it would get ridiculous you're just beur events and firewall and some other Stu what what type of so every environment is going to be different you're going to have some that could range 20 to 50 and you're going to have some with one server that could be seven if you include endpoint points um I tend to avoid Splunk because of that because I don't like the um the the
limit yeah I tend to go more towards the AL only invol oim uh security onion Sim monster Community which you can do up to 500 endpoints I'd prefer the endpoint method over the gigabyte method so if I can do 500 end points and I come in under 500 I can get a free and open source software that's going to do more than Splunk because I got a case manager I've got nids I've got surra cotta I've got all kinds of stuff that are in it as compared to Splunk which is just going to say oh you reached your limit and now you're done basic yeah yeah well and I mean it's counterintuitive right like if you're
sending your information to it and then it just starts throwing stuff away on you and you can't get it back either it just drops it yeah yeah yeah UDP it's if it it's dropped it's gone yeah yep anybody else yeah go ahead I I know you mentioned some of these uh Sim Solutions are aren't quite Sims but more just like log um what functionality functionality do you think kind of pushes it from merely just log aggregation to a true solution yeah so what I feel for me what I feel like pushes it from a log AGG ation tool to a Sim is going to be having the nids correlation engine so something like surot or snort built in
and then also having alerting because I want to know what's going on if something comes in that says hey I'm critical I want an alert so being able to configure whether it's a slack message a email whatever I want some kind of an alert to say hey send me that I know that there are some free Splunk for example has the ability to do a lot of that but in order to get that functionality you have to pay for the Enterprise license which is huge so a lot of the other options have that ability uh to to get that alert but that's where I feel really kind of pushes it from one to the other because it gives you that
ability to really get alert and get correlation out of the system with your HIDs your nids and all of your stuff pulling it all together and really enriching it so that you have a better view of what's going
on and haveing a software so that piece of communication needs to be done to the team the engine using it the work station so that we are aware that we have to again TW the there is a so it's going to depend on if you're sending those application logs to the Sim if if so say you bring in a new application but there's no logs that can be sent to the Sim so that you don't have to repeat the process but you bring in a new firewall and you're using it for standby hot spare you need to send though you need that firewall needs to be configured in case the other one goes down so you can continue to get those
logs so you repeat that process if you're bringing in a new EDR you're ripping out an old one then you want to repeat that process if you're bringing in something that can send logs for example you standing up a new server spinning up a new domain controller that is Windows 2016 whatever the new version is 2019 20 it's it's one of those but you're standing up a new one and you want to then repeat that process so that you understand that server is now sending those logs and then you want to verify it and then you can decom your other server anybody else it's only it com system that will yes have to repeat process yes if
there's a system that's sending logs to the Sim and there's a change to it or a major Network change where a switch is going out that you're sending CIS log repeat the process thank you m anybody else





