PG - A New Host Touches the Beacon
Show transcript [en]
all right hello everyone and welcome to a new host touches the beacon let's do a quick question does anybody here play a little game called Skyrim cool has anybody played Skyrim with mods all right even better you're going to love this I'm excited to talk to you today about how we combined our passion for video games and hacking and applied the hacker mindset to explore the landscape of one of our favorite games in a brand new way just a quick note I will share a link at the end that contains the original blog post and these slides my name is Devon Clary I'm also known as a romac I am a penetration tester and I've been taking a crack at
this cyber security thing for about six years now and down below is my better half partner in crime Marlo W Clary also known as isne um she cannot be here today due to a last minute family emergency so all that means for this talk is that you're just stuck with me for the whole thing um she did earn her place to remain on the slide as she is important to the story really I just couldn't figure out how to remove her without breaking the whole slide but we won't tell her that we're both big fans of Skyrim and this all started as she was gearing up to start a new playthrough to summarize Skyrim real
quick Skyrim is a very large single player open world role playing game that's full of quests Landscapes magic and Dragons so what makes Skyrim a great candidate for this project well almost 133 years after release people just keep playing this game why well partly because they keep focusing on making content for the Fallout series and not giving us Elder Scroll 6 anytime soon but also one of the greatest greatest attractions to Skyrim is the modding community so let's talk about mods for a second mods are developed by fellow players and third party developers to modify and alter some aspects of the video game for Skyrim there's just so many mods out there enhancements to character Creations cosmetics new quest
lines graphics and textures like you see in the screenshot here on the side comparing a non-modded scene versus a modded scene so there she was isney looking to start her like 11th playthrough of Skyrim and as she was browsing through the mods she notices like virus scan safe to use label on the website and that made her curious like what does uh what does an unsafe Skyrim mod look like so we started talking about it and the timing was perfect because then I was just starting to get into studying mware development and I thought of this idea that would be a great challenge isne said and I quote I cannot even play this game until we figure out
this mystery so we began planning out on how we were going to make this happen some may even ask is anyone even playing Skyrim anymore at the time of this recent screenshot there were more than 24,000 people playing the game the game has around 22 million owners and had an alltime peak of 287,000 plus players on release now keep in mind these stats only reflect the steam platform on PC so not console Gog Alexa fridge lawnmower or wherever the hell you could play Skyrim anymore these days now keeping those numbers in mind let's take a look at the bottom part of the slide exploring Within a popular mod website we see that both versions of
Skyrim have more than 60,000 mods available to download and more than 6 and a half billion downloads combined how does one even make a mod for Skyrim there's two popular ways to get started making a mod the first one is using what's called The Creation kit and this was released by Bethesda game studios with some restrictions in very limited coding languages then we have skse which stands for the Skyrim script extender this is a community main mod platform that allows Skyrim mods to be developed in C++ so now that we have covered some of the basics the question was can we make Skyrim something can we make Skyrim summon external programs in Windows by Conjuring something to trigger it or in
other words can we make Windows execute something based off of an in-game event the answer is yes and I'll show you how in just a minute so I'll have to borrow a line from Todd Howard here and ensure you it just works but first we just needed to figure out what conditions should be met in the game for our code to execute and since our end goal is to execute a C2 Beacon we decided go with going and picking up Meridia's Beacon in the game Meridia's Beacon is a quest item that spawns into the world once the player hits level 12 once this item is found and picked up by the player that allow voice comes
through probably through your headset and says a new hand touches the beacon no one to Skyrim players to be trolled by this experience so what do we need besides Skyrim we've tested this on the Gog and the steam version of the game so either one of those should work fine we also need skse that we just talked about the Skyrim script extender Visual Studio to compile our code vcpkg which is just a C++ package manager a scripting template available on GitHub just to get us started our proof of Concepts that we've put up on our GitHub and finally a C2 framework and for this project we chose to go with Havoc here we see an example of local
code execution this entire code just says do something when when a hit event is registered and the only purpose of lines 8 through 11 are to open the windows calculator app so putting this logic together we say when we hit someone in the game open the windows calculator app I think we're ready to check out a quick video of what this actually looks like so here we go we're running into the village like a maniac smacking an NPC in the face boom calculator this is an exciting Milestone When developing any kind of malicious code because if we can get something like calculator to run we can get just about anything that we want to run as we
will see soon enough since everything in this project revolves around picking up Meridia's Beacon we needed to find a way to obtain the beacon item other than hitting level 12 and running all over the world looking for it to figure out how this game interacts with its objects we went down this Rabbit Hole of form IDs and Base IDs so I'll try to summarize this concept the best I can form IDs are unique identifiers for everything in the game so everything has one everything from quests NPCs dragons followers lockpicks you name it it's got one now this matters because we're going to cheat the system a little bit we're going to be using an in-game console
system and just spawn the beacon item in front of the character instead of spending all those hours looking for in the world right as you can see in this slide we found Meridia's Beacon form ID pretty easily on the web Elder Scrolls Wiki page and that is the 4E for 4 E6 you see here next we're just going to use some logging techniques to find out how the game generates a copy of Meridia's Beacon and how the game tracks that item here's the meat of the logging script we use to log how the game is able to identify Meridia's Beacon item in the world we compile this in Visual Studio to a dll and then we load that
dll into our Skyrim game okay let's take a look at a video that will help us get the final value that we need here we're going to use that in-game console to spawn the beacon with a specific command player.pl at me4 E46 which is that form ID that we just found and that Beacon will be placed in front of the character the character picks up the beacon and then we're just going to completely exit out of the game for now the objective here is to locate and review the logs located within the game's directory this will show us how the game recognizes the copy of Meridia's Beacon that we just spawned here we find that
new value or the base ID for the Meridia Beacon item listed here at 32742 moving forward we will utilize this new value to finish our Quest so we go back into the source code of our mod experiment and we start figuring out how do we use that base ID that we just got to expand on our malicious mod we see here in line 20 22 towards the bottom of the image we start implementing this if statement or if condition that says if an in-game object that matches this specific ID 32742 is activated or picked up by the player execute this following code let's take a look at lines 10 and 11 towards the top of the screenshot we
see here this is just where the attacker would put in their IP address and their listening port number the rest of the script is simply just reverse Shell Code obtained from the ever resourceful worldwide web let's let's see this in action first we quickly see a netcat listener on Port 8000 we go back into the game we use that console system again to spawn the item hopefully on a flat enough surface the roundish beacon item doesn't just roll away on us the character is going to pick it up we'll switch back bam we have a reverse shell cool mission accomplished right right we'll check the IP address listed here with the one shown against on the desktop to make
sure they match so reverse shells are nice right they do the job but we couldn't help but ask ourselves what could we do to take this concept A step further as mentioned before the ingame item is called Meridia Beacon so in the O so jolly Spirit of the ls we're going to upgrade this reverse shell to a command and control Beacon uh we're using Havoc C2 straight off of GitHub and notice here that we're using the windows Shell Code format for the agent which is going to generate a binary file uh if you ever tried viewing a binary file as a plain text you'll recognize this format of encrypted Beauty seen at the top of the
slide but how do we get this binary code into our militia C++ Skyrim mod code in comes a program called xxd to save our day xxd is a command line tool that primarily used for creating and analyzing heximal dumps from files all we had to do was utilize this command line to tool to convert the binary file contents to a hexadecimal represented on the left side of the screen then we place that Shell Code within the C++ mod Shell Code placeholder seeing in the red box on the right side of your screen from here in Visual Studio we simply build the code load the mod in the Skyrim and check the results this time we set up three
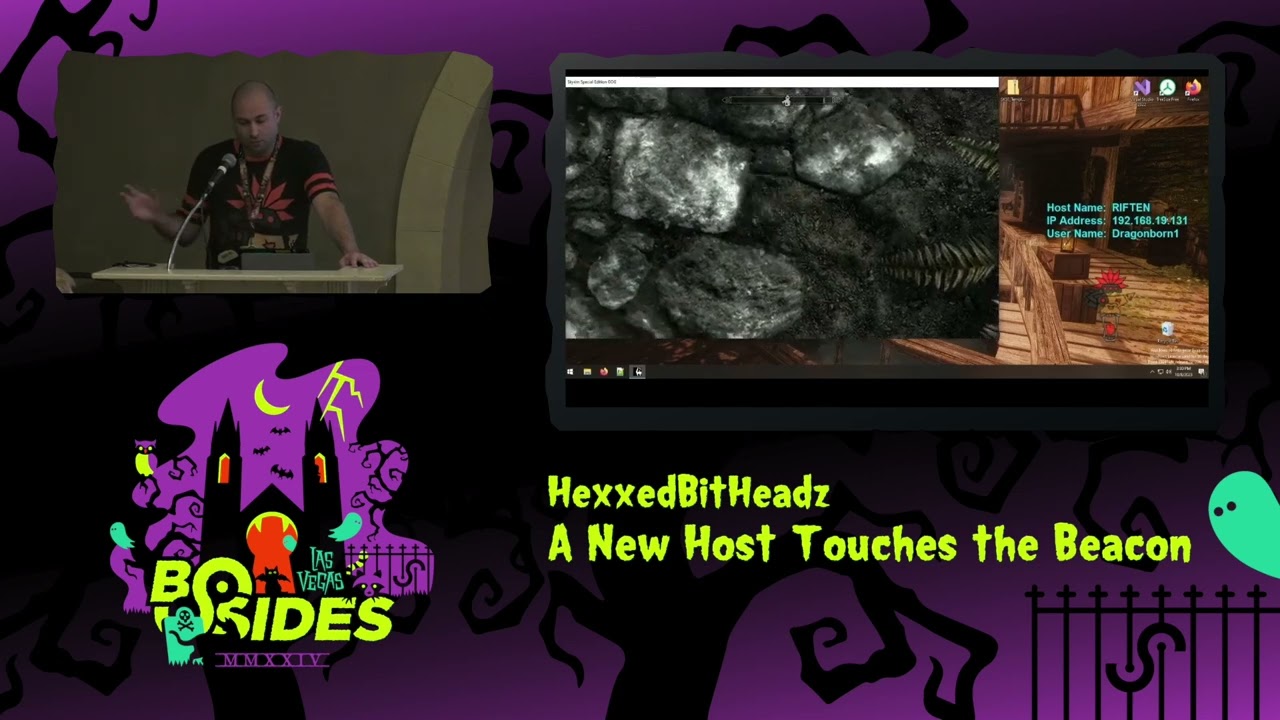
separate virtual machine instances each running Skyrim all with our new Beacon mod installed we set up havoc on one uben 2 virtual machine and then one by one we cycle through each virtual machine each instance of Skyrim bring up that console command system spawn the beacon item that triggers our code on pickup we can see in the video here that each Beacon executes separately and successfully calls back to our Havoc C2 server this is a very small scale demo for a proof of concept but imagine this kind of functionality already hidden within the popular mod you'd be seeing a lot more beacons here and now that we have all three beacons we go through the IP addresses
one by one and verify with each Windows host IP address that we see on the desktop this is definitely cooler than a standard reverse shell but again how can we take this concept A step further so we just demonstrated figure one with separate instances of Skyrim running within separate virtual machines but what if we were able to turn Skyrim into a multiplayer game or all players are synced to the same server in the same world instance of course this is Skyrim so there's a mod for that too called Skyrim together let's see what happens when we chain that mod with our mod to further the chaos here we see a blank Havoc user interface no beacons
running and now we're going to simulate three players in the game on the same server at the same location bear with me here as I cycle through each player to show full control one of these players is going to simulate as our cyber criminal and the first thing this player is going to do is open up that console system and spawn three of those malicious Beacon items straight into his inventory next this player is going to go and drop off two of those malicious beacons and do a random barrel and keep one for himself we'll now swap over to the second player and we're going to have this player go to that same barrel and
pick up one of those malicious Beacon items this player is going to open their inventory and show everybody that they do indeed have the beacon item in their possession the last player will repeat the same steps it's going to go to that same Barrel pick up one of those malicious Beacon items and expose their inventory to show us all that they have it perfect now let's switch back to Havoc server and see what happened we successfully finded all three malicious Beacon callbacks excellent so we we built this code off of a pre-existing in-game item but just imagine the kind of possibilities with proper mod support like for example new spells could be created and when it
strikes another player this kind of malicious code could execute almost like a twisted game of tag for hackers and maybe this is all too much and maybe like a stealthier approach is desired to be taken let's take a look at a a different path where instead of a reverse shell or a beacon maybe we just run some basic system enumeration Comm commands on the Target also to change things up and to show the flexibility of this concept we change the if condition to execute only when the player dies so getting rid of the Meridia Beacon thing altogether so only when the player runs out of Health represented in Code by the first box our new code executes and performs a handful
of enumeration commands on the Target and then stores those results into a local file and all of that's represented by the bigger box once all those results are collected that file is then sent to a remote HTTP server set up by an attacker so let's get a visual of this concept and see what kind of information those commands are able to give us at the bottom right of the screen we see this Troublemaker get what's coming to him by the fine citizens of Riverwood as the player goes down take a look at the top left of the screen we see a new file gets populated on the HTTP server nice the game continues to run
completely clu list of what just happened let's review what kind of juicy details the attacker was able to obtain from the victim for the best demo of this instead of using like a test environment I actually ran this on a computer that's used day-to-day and just redacted anything sensitive details obtained included local username local admin accounts personal user name and email accounts for various services such as like Microsoft Adobe GitHub there's even some of my remote desktop IP addresses and usernames saved here next we find the good old System Info results informing us of the target's operating system and security patches installed not shown here but we could have just as easily obtained like thirdparty software that's installed on
this host helping a malicious actor discover various attack paths here we see SMB shares uh available to this specific host these kinds of details can give an intruder a decent idea mapping out the target's environment and finally my favorite part here we see an example of stored Wi-Fi SS IDs and their plain text passwords from the target host I've even set up an example just for this talk seen here named bides demo and the password shown at the bottom besides demo password well folks our Quest has been completed and we have reached the conclusion of this talk hopefully what you take away from today's talk is just a reminder that code is just that it's
just code and when you're so busy staying Vigilant all day doing everything in your power to stay safe from cyber criminals it's just so easy to sink into your favorite pastime and forget that malicious code comes in many different forms including video game mods that can look quite attractive for your next playthrough I hope you walk away with the knowledge that not even the gray beards of high Hoth guard could provide you Dragon borers and by the nth have a fantastic bides I do want to give a quick thank you to bsides for letting me stand up here and talk about our project and a b big thank you for all of you who came to see it no Lolly gagging there's
only a few minutes for questions and please feel free to visit us on our website hexb heads.com to find this blog these slides and check out more of our adventures thank you [Applause] I don't know if it do we do the microphone thing in here we have one of those I sure of like the viability try uplo like NEX mods or anything like that a part of me wanted to sorry a part of me wanted to but no I didn't go that far yes
do I I don't um and the the hard thing is and I thought about this is like looking even analyze this one if you wanted to try and test mods out there how would you even do that because you can run the mod you can execute the game and you can play for hours and it may not actually trigger anything like this example it doesn't even trigger until you hit Level 12 and you pick up the Meridius Beacon so you could be hours into the game before you even notice right so good question yo do so so are the mods not Source available on like the modding sites running aary typically they're compiled in dlls so no no right yeah how portable is
this so my my 9-year-old son plays Sky switch okay and I could foree malicious code running an environment like that and basically breaking the console how how transferable it at least to to the last of my knowledge since this does require that skse framework I do not believe that's available on Console platforms I believe that is PC only cool thank you anything else
y engine um I believe the other one was Fallout 4 that they have an skse version of Fallout 4 I have not tested it myself for this proof of concept but I I'm sure with some tweaking it would probably be very similar yes yep for that multiplayer demo they all have to have the mod install or just the server the they all had the have the mod installed yes yep just curious because so manys is
there so Nexus does some form of scanning which was almost making me curious if I upload mine what happened but I didn't um but when when we did this this is this is not known or signatured right so even Windows Defender didn't care I mean so I think it would be pretty difficult to to track something down is when you talk about over 60,000 mods and trying to you know if you're on the Reddit or something you see playthroughs with 400 plus mods easily you know it's it's a lot oh oh I don't know yeah to get Ser to you could um I'm sure you could inject the server I I did play with it a
little bit I didn't get far enough to to make that kind of proof of concept but I'm I'm sure um I'm sure you could figure out a way to even if you had to redirect and have it download elsewhere but yeah I'm sure y what's the limitation and you work with mostly uh command promp tools could you use Powershell could you use RM Could you um as long as it compiles in in C++ yeah and executes there there um I did use CMD because specifically the um the netsh command that took the Wi-Fi stuff that was like that was the only thing I got to work and that took a little tinkering but sure I'm sure you yeah have a poers
shell alternative As You Wish yeah this might be just a guess question do you know how many Skyrim installs on corporate machines versus person I'm just asking for I guess it depends on where you work and what you're doing on late night shifts and when you're supposed to be working but uh no don't have any numbers like that and if you haven't already I do have a couple sticker things left but yes go ahead do you have any ideas as to potential defenses against techniques like this like is this something that like skse could be could be patched to not allow AR Run Like That ored by itself there probably could be some defenses built on sksc but we do
also have to give those guys enough credit because they put in a lot of work to get to as far as they did so anything beyond that I mean it's just um it's hard to try to convince somebody to sandbox Skyrim for an entire playthrough to make sure you don't have any listeners pop up right that's insane yeah did you skyex Skyrim e yes skyrimse.exe because it was using the special edition yes yes yes cool good awesome thank you so much for coming again I got a couple more sticker packages up here if you didn't get one [Applause]





