Beg, Borrow, and Steal: Growing a Security Program From 1 to n

Show original YouTube description
Show transcript [en]
hello there good morning uh my name is uh robert and uh i'm the check manager for this uh for this session the session that we're gonna be uh enjoying today is uh beg borrow and steel grow in a security program from one to in the um there's the the speaker is going to be david gilman he's a senior security engineer at a rapidly growing startup focused on application and cloud security previous roles including building a security program from the ground up and working at a satellite communications company previously worked in uh product management he got degrees from texas a m and soon to be georgia tech so without further ado i'll uh pass this over to david
awesome thank you so much for the introduction let me go ahead and share my presentation it's great it looks like great so thank you to everyone who's choosing to attend my talk on this saturday um to give another bit of introduction uh my name is david gilman i'm currently a senior security engineer at mparticle we are the after mentioned rapidly growing customer data platform startup i've also worked at favorite delivery which is owned by epd so this is san antonio i'm sure some of you are familiar with that acquisition and maybe even we talked pads previously and before that i had a security role at a customer data platform called or sorry another uh company
called bicep catalog company that was mentioned and then i have a degree from texas a m and finishing up my master's online at georgia tech you can find me on twitter at prime mover an infrequently updated twitter account for any questions or if you want to reach out and network after or on linkedin or elsewhere i'd love to chat so a few disclaimers given the nature and the uh provocative title of my talk first of all don't actually like cheat or steal i think it's important to you know in the workplace i'm certainly not enjoying being a sociopath or machiavellian in your approach to workplace politics i'd definitely advocate for a collaborative approach over anything
else and of course these are my own views they don't necessarily represent my employer my boss or any of the companies that i've worked out in the past so a little bit of an overview i would like just to talk about what we'll be talking about um as well as each of the categories of my talk this i think presentation is most relevant for those of you who work at software startups or small and growing businesses in the b2b or b2c space i think it also could be relevant for smbs where maybe the security program is becoming modernized as of course software is eating everything so more specifically what i wanted to discuss today is obviously growing your
security program at a startup so today your security program is small maybe non-existent but you want it to grow and i'm trying to answer that question of how you can you go about that effectively and who might you be in this situation so you might be the first or only security engineer at a startup uh you might have a title like security manager cso but you have a small or non-existent team or you might be someone who would like to do any of these things i actually sort of got my start on this journey that i'll be talking about today when i was attending lazcon i watched an awesome talk by a gentleman named leaf
about being the first security engineer and later that day i got a call offering me a job to do just that so maybe you'll have a similar experience taking the lessons learned from this and getting to apply them in your own journey uh so welcome to security at a startup um you're probably already familiar with this but you'll start out you know implementing some policies and procedures fix some glaring security uh issues and if you are a b2b startup then you're probably responding to endless customer security questionnaires that no one will actually ever read if this is where you're currently at or you're just looking for some other resources here are a few so there's that aforementioned glass
contact by leaf i found this to be a really good touch stone when i was first getting started as like a security team of one and he has a lot of great resources in the slides there's a company called screen that has rasp and laugh products they were recently acquired and their websites now become just a big announcement of their acquisition but i found that their marketing materials essentially were really really useful so they published these checklists sas cto security checklist cso security checklist first 90 days as a security engineer checklist they're kind of hard to find now maybe archive.org but this is the link i found to one of them that have been archived
i found these really useful also if you're unfamiliar latakora is a company that specializes in consulting um for security for startups and so their blog is really well written and has a lot of great articles i've seen them reference quite a bit and i've referenced them myself so let's say you've had this role for about a year you've impressed your boss with your security knowledge and taught employees not to respond to emails from the ceo asking for walmart gift cards and hopefully the engineering team doesn't hate you well what now so probably thinking about growth at this stage why grow it all i think it's important to consider do you actually need to grow i wouldn't advocate growing for growth's
sake um but there's a few categories i think would a few different reasons why you might have legitimate reason to need to grow a security game so the first of all first of all is if you're in security engineering cloud security engineering would be to support a growing engineering team it's going to be more code review more code to review there's going to be more need for automation to support that growth efficiently you might also in a b2b company have sales growth so there's more fun rfp excel sheets to fill out uh there's more sales calls to sit in on and there's just more volume of day-to-day work and then also missing expertise so as we
all know some job description writers might not but as we all know there's no such thing as a unicorn security engineer security professional and i guarantee whatever experience you have there's something missing or something you're not as strong in so bringing in that extra expertise could be really really valuable especially if there's literally only one of you
so what are some challenges to growth and why might you be attending a talk like this to learn more about it well of course budget is always finite and in most businesses security costs money doesn't make money you'll know if your exception to this a security consulting business for example of some kind or a security vendor but at almost all of our employers we are costing the company money to employ us there's also almost always more exciting things for leadership to invest in sometimes there's exceptions to this if a cto has some background in security and they really pride themselves on taking it seriously or maybe they lived through a company or career ending incident
but generally speaking it's much more interesting for them to invest in new features a bigger sales team a cool new office and also this is a hard truth but in almost all cases security incidents are not company ending we can all think of dozens of incidents high profile ones many of which were arguably due to negligence under investment by leadership in security and yet those companies are many of them most of them are still have gone on to ipo have high market capitalizations continue to do business so understanding the prioritization of security it's important to put that in context and also if you're doing your job well or you're just lucky then from leadership's perspective there
might be no indication that you need more money it's kind of a hard truth but security there's obviously a certain randomness aspect to it and so if you just haven't had to deal with an incident then or you've dealt with incidents well then from leadership's perspective you know we're handling things great there's no issue so how to grow i would say you know just ask for more money it's that simple thank you for coming to my talk all right well if that approach has not solved your problem in the past then i'm hoping to give you some more actionable ways to approach this problem and i'm broken them down with a pithy title begging borrowing and stealing so
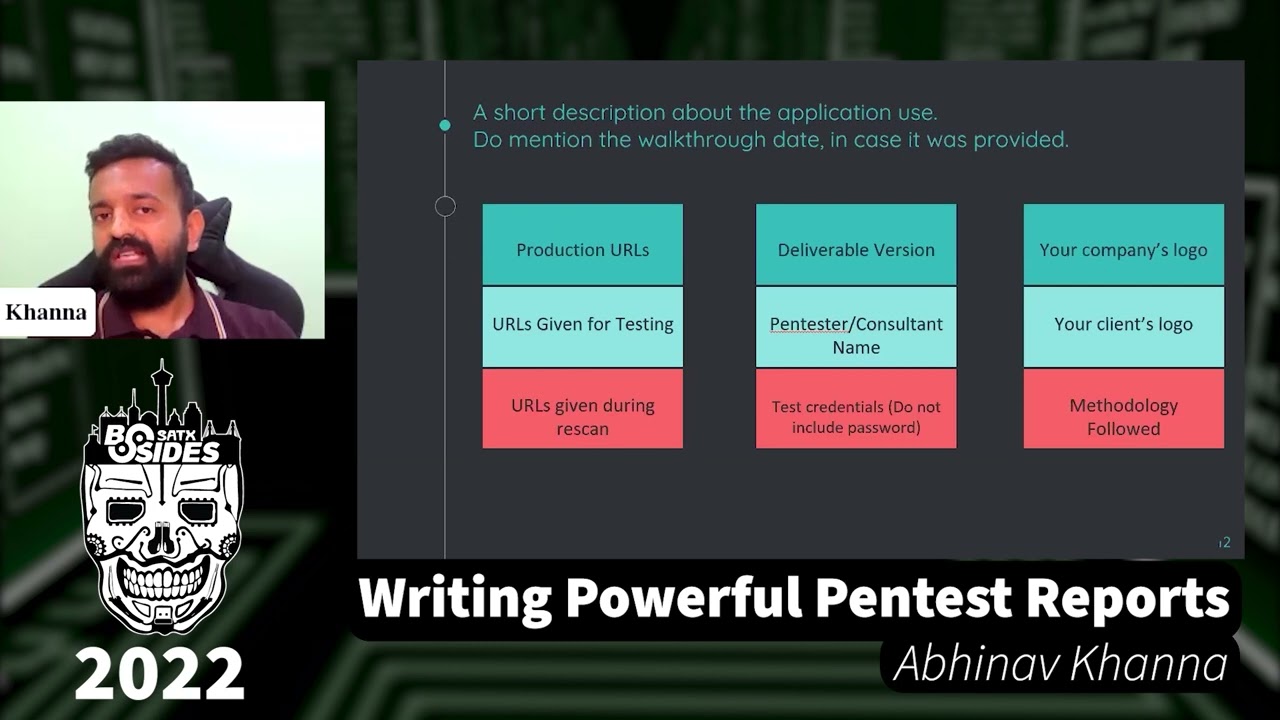
and i would describe these categories as begging is basically how to ask your boss better borrowing is finding partners in your organization and stealing is finding ethical and legal ways to save money head count
so begging this is usually the first and last step for security engineers much like my gift from earlier asking for money please you might ask your boss for a big pen test budget or that six figure bunk license that you really want they agree they take it to the annual budget meeting and they come back empty-handed this year's just uh you know maybe 2020 was a rough year maybe 20 was a great year either way there's money that needs to be invested in other things uh there's bigger fish to fry aws costs are always going up gotta get those margins down margins up so how can we as security professionals address this in a way that will actually
get the business to listen does is another one of those sort of hard truths but securities don't exist just to have good security companies exist generally speaking to make money and if you think that security is important you need to articulate why in a dollar incense way to do that you need to understand how the business thinks about money and how it goes about spending it so why might a company spend money on security here's a few reasons you may be familiar with some of these already but maintaining voluntary compliance like saktu lans customers uh obviously some of these are more b2b or some more b2c customers might also leave after a public incident i think this is true
both b2b and bsc bad press is bad in most cases bad press if you're a private company or public company can scare away investors violating gdpr or other privacy laws can lead to loss of access to markets or fines and on the flip side perceived or actually good security can lead to more customers uh that i think is an under in sensitive industries this is more like ever well realized but it can be true in a lot of different industries and that's why you see all those marketing things about bank rate encryption or military grade encryption because there's at least someone on the marketing team thinks that saying those sort of things is going to get more
customers this can all on the other on the other side sort of the way that security might negatively impact the company uh you could look at things like credential stuffing where even if there's not technically a weakness in your security if someone picks up a new story from social media about how your company got hacked that can also lead to customer return a negative press and you might think these matter more for b2b but i also really think they matter for b2c especially if you're in a sense of industry finance date of some kind healthcare okay so i'm gonna give a little bit of risk 101. if risk is your day job or you have some really strong background in
this i want to just emphasize that this is 101 um if you want to nitpick my definitions of risk and things like that i'm happy to take comments and questions but even this basic understanding really helped me so risk in some definitions or risk exposure can be represented by the likelihood of a given event in a year multiplied by the estimated cost to the business so for a ransomware attack you might say i think it'll be a ransomware attack on our company successfully every 10 years and we'll have to pay a 4.4 million dollar ransom and bitcoin so that works out to 440 000 annualized risk um also if you're not a pipeline company then
the fbi probably is not going to get your bitcoin back and then maybe the cost will be higher it's also useful when you're looking at these numbers how you come up with those costs so a bitcoin ransom number pulled from the headlines is easy it's also useful to add on to those when it comes to customer churn that you're estimating so loss of revenue as well as person hours so engineering resources and security resources are quite expensive pulling 10 people to work on like an incident or potential breach really adds up quickly in terms of opportunity cost for the company and you can represent that here you can also talk to engineering leadership legal and other departments
and ask them to come up with numbers because for one thing they might be more accurate and for another they're more likely to trust their numbers instead of you bringing them to them i think it can be useful to help them come to grips with this idea and i've had a great deal of success with that uh just by being one of the first people in the startup to really talk about risk it can also be useful to try to measure these numbers over time and say a graph or think of them like a kpi into themselves a warning though even though you sort of are making up numbers don't just make them up out of thin air
and also be clear these are estimates the people you're presenting them to are going to realize that so if you try to present these as some sort of fixed gospel it's not going to go over well so a little bit more about annualized risk so we talked about this bitcoin example where we've calculated our 440 uh thousand dollar annualized risk you can also express this of course um monthly or in a decade format but look at how we can tie spend or budget items to this risk so suddenly spending let's say 20k a year on av licenses for our endpoints that looks much more reasonable especially if you look at it as only 1.7 000
cost per month this is a really great way to present these and again that's why it's risky to just make up numbers you could be unethical and it would fall apart quickly to do so but if you have annualized risk numbers that are coming from leadership they agree with then when you put spend in this context it really shows why simple investments make sense i wanted to emphasize again that even though this is probably very basic to some of you this level of risk assessment can be game changing as startup people don't like things uh scary things like cyber security or getting hacked and they don't like spending money so asking them to spend money
on cyber security is a double whammy so even just having estimated numbers in an excel spreadsheet can really bring a new level of a new way for them to think about this and they can start thinking about risks and cyber security in the context of how can i actually fix this and prevent it not just oh it's a scary thing that i don't want to think about so talking a little bit more about risk i think we're all aware of this but perfect security is infinitely expensive here's a quote that i'm sure many of you are familiar with that i particularly love but the idea is basically there is no way to secure to properly secure a computer system
without maybe dumping it into the ocean even then maybe not and of course it won't be available then so you violated the cia try it anyway so all this to say some risk is always going to have to be accepted it's better to have conversations with your leadership about how to handle these risks and think about thinking about them in context of avoiding transferring mitigating or accepting is also great because again there's always going to be risk that is accepted or avoided and additionally you're not always preventing risks right we're mitigating them this is the book that i found very useful it gives a few ways to think about risk in a more advanced way than simply
multiplying some numbers more about statistics probability and sort of modeling of course if you're going to use something like this you'll have to be able to explain it whoever's reading it they probably won't just take your word for it but again i found it very useful risk is its own industry and so there's lots of great resources as well online via podcasts and blog posts so this is tangentially related to risk but it can sometimes be worth it to spend money to spend more money uh having a cyber security risk assessment conducted by a third party if you can get the budget for that can give you the justification you need for security investment in a lot of cases unfortunately uh
leadership might not trust your judgment that there needs to be further investment but getting a small investment in a consulting gig could show that uh there are gaps that need to be met or that you're not meeting benchmarks by your peers and these sort of assessments are often offered by firms that also do pen testing or security channel sales i was talking to a pen tester a former pen tester co-worker of mine and he confirmed this he said it was ironic but having to spend money justify spending more money with that same company doesn't really make sense from our perspective but it can for some reason makes sense from businesses perspective and therefore it can be really valuable
okay so moving on to another subject of kpis um i wanted to talk first about company kpis so what uh kpis or metrics does your company care about and you can determine this if you don't know already by looking at signs around you what kind of numbers or percentages go into a bonus structure promotion ladder in sales this is very obvious usually it's things like deals closed average size of deal a month or quarterly revenue targets annual revenue targets growth i also find it really useful to look at what gets talked about every all hands or town hall these are also often metrics around growth but they could be around other items as well and to be clear i'm not talking here
necessarily about security kpis but i will be talking about those specifically in a second so here are a few kpis that can impact security for good or for ill things like churn rate cost to acquire a customer how many monthly active users we have customer net promoter score the annual revenue of the company or the defect escape rate there's obviously more to this but these are ones that aren't necessarily tied to security but again security can have a good or a bad impact on a favor an example was customer churn we theorized that if there was a security incident of some kind or even just that example i gave earlier of reporting on say account takeovers
something that wasn't necessarily a security vulnerability but some sort of deficit that we weren't accounting for or that our customers weren't accounting for by reusing their passwords our churn could increase so customers might see that their favorite delivery app again doesn't actually have issues like this but if the perception of that could lead to them choosing to order from a competitor and i think this is true in most industries where there's a clear pier which is true for a lot of startups and then that would impact one or more of these kpis which could decrease our ability to grow so how can you impact these kpis in a good way you can implement security sensitive features or help engineering
do it to use the to use the account takeover example for b2c so you could calculate the cost of not addressing an issue for atos you calculate the number of support hours spent on ato times the number of atos account takeovers times how much the the business values their time which is probably some standard hourly wage with some percentage overhead this should be relatively easy to track down if you have a mandate to create things like risk documents but in calculating that i can quickly add up and so there's you then have in hand that annualized risk which may even be getting realized in an actual annual spend and you can then calculate how much it might cost to fix
it so one way to fix it could be those security features maybe implementing a form of mfa password meter these different approaches that you might use to drive down account takeovers therefore to drive down the spend on this inside the company and then that's the kind of win that you can talk about at an annual review of the team's performance your promotion cycle or put on a resume those are hard numbers uh also on the b2b side you can proactively security can help practically drive these kpis by creating security materials to help close sales leads there's obviously a huge appetite depending on the industry but those endless security rfps we've probably all been on both sides of them
and responding with a solid white paper with technical details can help show that your security team does have a handle on things right off the bat also can make filling out those customer questionnaires easier another thing for b2b in particular is tracking if there are prospects or customers who've been requesting security features this should be probably tracked by product in an issue tracker but you should also be your own pm in a lot of these cases talk to people inside the company talk to support talk to sales find out what kind of security features there's appetite for that haven't been implemented and then here are some security incidents or sorry some metrics that your boss might care about
so a number of incidents per year the number of pages you're getting after business hours you can show them that to show why you might quit if you don't grab the security team account takeover is in a year and then also a great one's percentage of vulnerabilities passed within your existing bug sla you don't have a bug sla it could be a great project too a number of incidents also can show poor security or just poor ability to detect issues if you have a very low number of incidents then you probably don't have enough detection in place uh i've been talking about atos a lot but to me it's a good example and driving them
those numbers was a huge win for me and the team and for both a b2b and bsc uh looking at what vulnerabilities were discovered at what point in the process is really valuable so that goes with that whole pushing left mantra uh an automation sec devops those sort of buzzwords but you're probably all familiar with the idea that the earlier you fix vulnerabilities and catch them in the process the cheaper it is and the better it is for security because you don't want critical vulnerability to be released into prod much cheaper to prevent that critical vulnerability by catching it on a developer's workstation before they even commit the code and trying to measure that both for bugs
and for vulnerabilities which you can think of like a subset of bugs is important to measure so moving on to budgeting the it's important to understand how your company and organization handle budgeting before you can effectively ask for things or at least move beyond the ad hoc way of just saying hi can i have 20k for this hey can we spend 100k on pentesting this year so some things to figure out about how budgeting works at your company is how does the calendar year look like is the fiscal year tied to the calendar year is the budget broken up into the first and second half are there discretionary funds can you get approval for some items just by
going to your boss or is there certain cutoffs where they'll need their boss or the cfo to sign off on security should probably be involved in the purchasing process but if you're not already familiar with it understanding how that looks you're going to have to get privacy legal to sign off on it how can you make that easier and prevent it from getting slowed down benchmarking i talked about this a little bit earlier with the idea of benchmarking against your peers with a third party i also find benchmarking to be a bit of a black art i'll talk about some numbers i found for startups and let's say 100 to 500 plus employee range but it's a bit of a black
car and so if you have any great numbers on benchmarking please let me know i've had the best luck they're reaching out to peers or literal competitors finding out how their security teams grow at different stages but this is my crew diagram using basically microsoft paint and comic sans to illustrate a principle that i found useful and that if you can explain this well to your leadership this can be really powerful the idea is that as a total headcount or the engineering headcount of an organization grows the security headcount will need to go along with it so you know 10 employees there probably wasn't a need for a security engineer maybe somewhere around the uh 100
employee mark they invested in you the prototypical first security engineer hire then at some later point you're now asking to grow an add-on to grow the team to more than just one uh this of course starts to beg the question in your boss's mind of well how much are we gonna have to grow how many security engineers are going to be running around here and the good news for them is that in my experience you don't need to grow the team linearly you don't need one security engineer for every like 50 engineers forever what you can do is once you reach this tipping point where one person isn't cutting it scale the team during that period of
grip some big fundraise or other natural period of growth up to maybe like some some one manager size team whereas amazon would say i get two beats a team or less and that will give you the foundation to build out things like automation and have broad expertise and you can grow much more slowly after you sort of reach that foundational point and again communicating this to your boss will help can could help convince them to invest in the security team with the idea that oh this is like this is an investment we're going to make a commitment to security but this should give us a good foundation and we won't have to just keep growing at this rate
these are just some ratios i've seen again if you have great numbers on this please let me know it goes without saying but this can vary so much uh if you're a security sensitive company and not security sensitive company if the cto used to be a cso if the cto hates security because one time they blocked him from releasing a product those can all influence how much the business is willing to invest benchmarking can be useful though if you can get numbers from peers or competitors you can engender some of that fomo in leadership and say oh well our security team is one-tenth the size of our competitor even though our revenue is pretty similar and they're going to
start thinking well what do they know that we don't they they don't want to be the ones in the breed in the news for breach while the competitor gets to tout their excellent security program so to tie together some of these themes you want to tie specific risks and asks together as i've kind of illustrated below here in a very crude budget template budget request template uh this is a way you might go about that if there already is a budget or risk template use that at your company you want to speak the language and yes this is primitive please do better but it's it's infinitely better than asking for budget piecemeal um some things that if you've
only worked at bigger companies might seem like table stakes are can be potentially like game changing at a startup just because no one's ever done them before also a tip don't just request what you think you can get request what you actually need and let the business decide what risk they want to accept this is a don't pad your budget but ask for anything reasonable you can add prioritization to that possibly as well like a high medium low obviously it's less likely that your lows are going to get accepted but it helps just from a psychological negotiation perspective sometimes to phrase things like that and of course the benchmarking can potentially be helpful as well
all right so moving on to borrowing which is a topic that is a little bit more broad i think than the ones i put under begging here's here's a few items though i think fall into this category so first of all security champions this is a concept that where designated engineers or other employees take the lead on security issues this could include weekly or monthly syncs with the security team um and it can be a good way to get information on what's going on in the company as well as to disseminate more information on maybe a new process or a category of bone that you're seeing this is purely my personal opinion but i'm not a huge fan of security champions
maybe it's the problem is me but i've had trouble making it worth the time of engineers they often have plenty to do already so adding one more meeting on their calendar can kind of just be a pain in the ass even if you're giving them free stickers or t-shirts and even if they attend and aren't interested what i've had more luck with is what i'm calling security champions and quotes if you've been doing security at a startup or you've joined a company early in its security team's growth then you're already familiar with the idea that someone's already been doing security so that might be qa doing some ad hoc pen testing or engineers who have been having to
implement authentication authorization or support doing crowd prevention if you talk to them which you should have already done if you've been at the company a year in this example uh you can also kind of get an assessment of whether they want to keep doing more security and with that communication you can find out from them if there's possible security issues in the future as well as what kind of skeletons are in the closet there you can find allies in this all over the company and i've had success in areas as diverse lots of in engineering of course but also even in legal and support where legal would end up actually looping me on risk issues just because
there really wasn't anyone else in the company thinking about risk and so when they saw issues that were even only security adjacent i'd get a heads up and could help get feedback and input and so there wasn't a meeting that we attended other than maybe a monthly sync but it was just the two of us like a one-on-one but um even then it was still very valuable caveat though don't get in trouble um by getting someone to do security work instead of their own work you don't want to just be dragging people away from their responsibilities okay so this is another one that i'll give some caveat at the end but sharing job wrecks with job postings
here's a possible example maybe your operations or devops team needs more head count uh maybe you need someone to do cloud security work or network security work or just do that sort of work for the security team because there's not enough capacity uh it can be possible to combine job postings to get more efficient use of head count this can look like they already have a couple recs open and you talk to them about some sort of compromise where you use one of those wrecks for this purpose but they still report into ops or maybe they actually end up reporting to security but you agree with security with with ops that maybe your team will take on
some of those security tickets and responsibilities that have been on their plate it can also be going to leadership together and saying hi we're trying to make efficient use of budget so if we'd like to instead of asking for two jobs uh we're gonna be asking for one again though this can be tricky because could backfire in some organizational politics way and it could be tricky for the person being hired into the role where they might get pulled then being expected to do two jobs so it can go wrong but i would say that if you're careful with it it can also be used to your advantage also interns i put them in this category
because you're sort of borrowing them from school and i also want to note you should pay your interns it's really never any excuse not to in our industry or really any industry uh so i'm not saying get free labor from interns but they can be very helpful this is also potentially tricky if you've ever worked with interns even a senior engineer it's kind of expected that i'll take them at least 90 days to be fully productive and functional or longer and an intern is only going to be there for 90 days in most cases so it's a lot to expect someone in undergrad or graduate school to be productive more quickly than like a senior engineer
but if you scope the projects really well or you have a single well scope project and even better if you can pick a project from your backlog that fits their interest and skill set by talk to them before the summer or their intern period starts then they may be able to accomplish quite a bit uh also i'd say having interns is very fun and rewarding so i'm always an advocate for that giving back and getting to um play like a mentorship role so an example of this for me was that we brought on an intern kind of unexpectedly and she actually completely knocked out of the park part of that was the planning uh that went ahead of time i'd attribute
most of it to like her work ethic and intelligence but um part of it was that we picked a good project so we presented her with a list of things she might be interested in working on she picked one that she thought would would be interesting and then over the course of summer the summer finished it it was a complete success it's not part of our product that customers see pretty much every time they use the app and a little bit more about budgets so budgets can be sort of borrowed or shared um it might be a tool that both you and i t want like an evr tool or some sort like a jam for something
or cloud security tool when you're talking to your devops or ops team these items might make more sense on their budget but only if they agree don't steal people's budgets you probably won't be able to get away with that anyway without maybe doing some phishing getting their credentials uh this works for a few reasons potentially one is that cloud spend is pretty elastic and it's almost always going to be with an existing vendor like aws or gcp so while you shouldn't go hiding things in like some sort of slush fund saying oh we're going to add this specific spend to our aws bill every month to pay for uh increased blogging of some kind or
maybe guard duty that's often a lot easier to stomach than asking for some specific third-party tool that's going to create a new vendor relationship and a contract uh this is basically exactly what we did uh and that i've done in the past is not hiding these projects but including them in existing cloud spend with existing vendors and for ops it could also be a win like implementing a sim or some sort of logging solution can help them out even more than it helps you out but bringing that uh request together shows that it's like efficient use of budget all right this one's a bit counterintuitive but shrinking to grow i put this under borrow because you can
you're borrowing capacity from other teams again don't dump work on other people these are all need to be done ethically and empathetically but sometimes it can be a win for both teams um if you're a security engineering team and you've gotten saddled or in my case for some reason jumped on the hand grenade that is i.t security consider not doing it anymore with the approval of the other team and your boss and this was a huge net win for me personally i'd spent probably a year trying to do it security and it just didn't really make sense it's not a strength for me and it really was belong more in like the at department and it turns out it didn't really want
to give it up either so we just agreed that they would handle it everyone agreed to this and instead a security team would just engage with it on specific projects um and with a monthly sync one-on-one sync but we no longer had to worry about not being successful at something like rolling out av where we didn't have the background or the capability or access to the tools to do that kind of work so to summarize this section working with your existing co-workers and teams can really get you quite a bit of capacity consider sharing budget and headcount for tools or individuals which can benefit multiple teams and also grow the security capabilities in your i.t
your ops or engineering or other teams all right so lastly i want to touch on the most potentially exciting topic of stealing so one thing you can steal are disasters whether they're happening at your own company your competitors your peers never let a good crisis go to waste don't give into fud but a little bit of fudge to be healthy uh it can be extremely persuasive to show larger companies having these incidents um we had a large competitor in our space that had some bad press and then actually a breach and showing that large companies with larger security teams than us in the same industry the same type of data could suffer these sort of attacks
showed that we needed to invest more in security and that there was good reason to do so so make sure these relevant these stories are relevant your company though you don't want to just like pull out colonial pipeline or that meat packing uh plant story that happened recently and say oh this is why we need to invest and they're going to look at you and say that's like a ransomware attack that doesn't really be anything to do with us no the more relevant the better that's why the competitors is particularly useful so other things to steal our information and strategies please steal this talk uh by using the ideas in it conferences and meetups peers on twitter
buying people launched this is just good advice in general when it comes to growing your career no matter the industry but particularly in security but when i went from being just an ic to someone who was in the process of growing and building a security team this became completely invaluable to me and also i found of course people in security are very open to helping out peers and people more junior to them so i got had the opportunity to meet with cesos and heads of security at very large companies and just talk to them and say you know at a high level here's my situation how have you successfully fought these battles in the past have
you grown a security team effectively how do you you know do mentorship effectively work with engineering effectively also worst case if things get really bad at your current company it might lead to job offers from those mentors down the road so can't hurt also negotiation isn't really stealing but i thought i'd put it in this section there's lots of great resources on negotiation i think most people probably have a favorite self-help book on the topic good places to practice of course are buying a car or selling something on craigslist but it's important to know you can always negotiate with software vendors don't settle for the list price you should get competing quotes and you should willing to walk away this was
also specific to my experience as a favor but when i joined we'd actually been acquired already and so we had a parent company that we could often get bundled pricing with your this is less applicable to most startups to a true startup for sure but i wanted to include it because it was really valuable for us it's also this is one of those topics that their entire books about and i could definitely give its own presentation on but building versus buying so all products have a build versus by decision um with security feature sets and tools products this is also relevant so figuring out whether to do it yourself or steal by buying it from someone is an
important decision there's security implications these as well right like rolling your own off versus buying some sort of sas product like cognito or all zero that there's security pros and cons to those approaches but there's also decisions around cost and research resources mfa for example there are plenty of vendors who will pay you can pay to handle mfa for you some of them though are basically just selling the ability to send emails with like a securely generated url or token you can definitely show yourself in the foot with that but it's also the kind of work that at a certain scale can be worth doing yourself so while this needs to be carefully done and the security implications have to be
considered doing something yourself can be a good use of your own time and budget also this one's the most obvious use of steel i think finding co-workers who want to join your team again be careful you can't just pull people off of their existing work without approval from your boss their boss but this can be really great one of my most rewarding experiences in the journey of growing a security team from just myself and to a few people was bringing someone from the qa team into security so they're pretty well tenured qa professional uh and at the company as well so they were a huge resource to me but i found that when i joined they were
starting to kind of handle some of those pen testing and security responsibilities because they found it really interesting so i started out just informally mentoring them but with approval that turned into a split roll where they spent half their time on qa and half on security and while there were some bumpy parts of that journey for sure it ended up working out and they ended up moving to security and sort of a lateral promotion to security engineer so that was a huge win for that person's career and their life but also as a huge win for security because that early we probably wouldn't have been able to get a job wreck for someone with that sort of experience and
of course their knowledge of the company and quality assurance was really invaluable so to summarize uh negotiate with your vendors and consider bringing co-workers from other parts of the company to security if you can figure out a good way to do so so summarize the whole presentation i'd advocate for begging by building a risk assessment framework tying your ass to your mitigations borrowing by working with other teams and stealing by finding opportunity to get head count and budget where you can find it of course i couldn't end my talk without plugging the fact that we are hiring um we'll be opening some security job wrecks to uh soon probably an application or cloud security so if you're interested please
reach out to me i'd love to talk to you about what our cso and myself and the rest of our security team are doing and we're hoping to do and we're also hiring for operations and devops folks sre so we could really uh really value your applications there if you'd like a referral also feel free to reach out to me later or on twitter but at this point i'd like to take any questions that you all might have thanks david i appreciate it um i'm not seeing any questions so far i'll uh give it a minute or two i really appreciate you coming on and giving that presentation it's been helpful for me a lot awesome
yeah you mentioned before that uh this was a topic that was near and dear to your heart yeah i'm often uh uh on a team of one or two engineers where we're building out the the security capabilities so it's uh it was real nice cool yeah and of course i'll be on the discord later today or or on twitter if anyone wants to reach out be happy to talk to folks my name is christopher hadnaggi i'm the ceo of innocent lives foundation the innocent lives foundation is an organization that i started that is made up of security professionals that want to help save children from the horrors of child abuse hi my name is shane mccombs and i am the
chief operations officer for the innocent lives foundation the vision of the ilf is to protect innocent children from anyone who supplies and trades in child abuse material we use our skills to uncover and unmask those who try to anonymously hide online while spreading producing and profiting from child abuse material we were able to collect security professionals from around the globe that are experts in their particular field we have people that have mastered osint or open source intelligence gathering we have expert coders we have expert exploit writers we have people that have really mastered these areas of their field and they have come to donate their time in order to help us unmask these anonymous child predators
well one of our core principles at the innocent lives foundation is to never do anything illegal the ilf is a non-vigilante organization so we work within all of the laws that are appropriate and in fact one of the principles that we have internally is that we work hard to remain above reproach meaning that obviously we're not going to cross the line but ideally we don't even want to get close to the line if there's a gray area we do everything in our ability to be sure that we are not in the gray area and therefore staying above reproach because the goal is to get this guy off the street and what good will it do for us to
unmask someone for him to just be turned out loose later because we didn't follow the rules if we were to perform one illegal act while catching a predator law enforcement would not be able to use the information that we hand over which would make all of that work useless and that person can walk free even worse than walking free they now may be armed with information and become even a smarter predator so as we do the work we want to be able to give them a file that file should contain the 10 50 100 steps that it took us to connect that online anonymous perpetrator with a real person one of our core goals is to make sure that we produce a
file that can walk any law enforcement agent through every step that we take legally so they come to the same conclusions that we do our main focus is being able to save law enforcement the hundreds of hours of time all the time effort and energy that they would have had to put into that case in order to find that predator when we do that then we consider that a win and we consider that a case that we can hand over so the ilf has a couple methods where a case comes to our attention first of all we have a report a case button on our website that section of the website can be used by law enforcement or even
just by civilians that know of child abuse cases or child abuse material online they can report it to us and then we will work that case or hand it over to the appropriate law enforcement agency the second way that we hear about cases is many times law enforcement agencies will come to us within those leads those are the ideal ones because we're able to lend and assist immediately upon request maybe a local law enforcement agency that doesn't have the budget for ocean experts or doesn't have the online expertise that we have in-house so they'll come to us and say hey we have this case we're not a dead end is there any way you can help us figure
out x y and z when we successfully get to work with a law enforcement agency it makes us feel so good that we were able to help them accomplish their job and from the work that we've done so far we've gotten incredibly positive feedback from the law enforcement agencies that we've had a privilege of working with and helping them close those cases but more often than not we are able to find leads by going out and looking on the internet seeing people already doing horrible things to kids those people are in the public and therefore they may become an appropriate lead we have a group of our volunteers that actually spend time looking at different forms where people
try to hide child abuse material when our volunteers find people that are uploading child abuse material we make that user name a case and then we'll assign one of our crew that will then start to oscent or look online at that open source intelligence at that username and see if they can connect that to a real-life person of course all of this work even with donated time costs some money the servers that we run the tools that we need and the people that are running the innocent lives foundation were able to accomplish all of that because of voluntary donations every cent that everyone donates goes directly back in to running the organization and being able to put predators behind bars while
working closely with law enforcement to do so donations are used to meet the needs of the technology that is used on the hunt but it's also used to help protect our volunteers psychologically to be sure that they're getting the wellness treatment that they need to help them stay balanced and emotionally fit so they can continue to do this incredible work we have done so much more because people have donated our very first year that we started ilf and we were so excited about this we were able to close nine cases that means that we had nine files that we were able to hand off to law enforcement where we were able to uncover and identify a child predator the very
next year because of all the donations and all the support that we got from people like you we were able to hand in over 75 cases that next year the increase was mind-blowing and that was because we were able to add more volunteers more technology more tools and all of that added up into closing more cases to help save more kids there's a tremendous number of organizations out there are doing phenomenal work if you feel that our mission is in alignment with your core values then we would love to have you donate to us a study in 1995 tells us that one predator may affect the lives of up to 400 children that means when the child predator you
helped unmask is a serial predator you may be helping to protect up to 400 children [Music]
[Music]
[Music]
[Music]
[Music] you