PowerShell Is DEAD — Epic Learnings!

Show transcript [en]
might also notices teams biting wheedle so we try to get to do be kind every year the team yeah so some pretty good write-ups a if you're interested but so let's get to the crook to the top so what is PowerShell and is it yet so I think a lot being percept to be sort on to save its own powers off dead don't use it anymore but I think we need to think about it a little bit more think we need to go into the cooks of PowerShell and what it actually is so when people say our PowerShell is dead from a defensive perspective does that mean sort of practice you know aren't using anymore you're not allowed to sort
of say not allowed to sorry you can't use it you know gets detect there with blocked but are they referring to the PowerShell you know the Microsoft signed binary is that what is blocked so if you if you're caught running power to act in a box it'll be one block if it's not lock that we detected in some is that what we're saying when we say PowerShell it's dead is it the DLL behind the binary it's actually power told actually just a wrapper with a system that mines went that automation DLL so if you've got good products like EDR which has treating enabled and allows you to see all the DLL loaded is it the fact that
if you run any system management automation deal or any protists on a box now that's capable of being detected so that is actually what we say when we say PowerShell is dead it's both the XE and the automation DLL or is it typically the Poli it could be the folder the Power Cells launches from so if we go and copy pouch all the XE to another to the folder within Windows and have a different name does that mean we can actually use that and that isn't blocked so kind of we need to sort of understand what people say when they say PowerShell is dead also I don't know if you're aware or not but since version four and five it's now
I've got integration within a MSI so you can see things that signature level from an AV perspective it's got things like transcript logging script logging and module logging so anything that's kind of run within the parish or run space whether that be from the dotnet management automation or directly from PowerShell you've got a chance to detect it and see it so for running common tools like Power View and power and things like that with the with the likes of shot and sorry script bot login and transcript logging you now from an infection perspective and see that within transcript and have it have a chance to see people early so we talked a little bit more about the crux of
PowerShell in our other tool where we kind of tried to mix it up a little bit so if you want to go see your talk it's there Cooper's put it up or online so the gives you a little bit more background about powershell before that than we do in this tool so it moves on gets to the evolution of Asti too so those you don't know why she - it's a PowerShell framework completely written in PowerShell at least it was to start with so both the c2 server side and the implant side was written in PowerShell so you just have that a Windows box you can deploy it on a Windows box whether that's in the client environment or not
either through the internet or not well the implant just runs purely in PowerShell originally it was literally anything you'd have to run is a PowerShell one-liner so we'd have the - II encoded command with a massive global basic support text we then went through some iterations of changes we implemented the C sharp theory which allowed you to do things like right-click get system and write that screenshot but absolutely hated it as an operator level people like Dugger myself and rather when you're using it it's just it's you want to know what you're typing in and you want to get the output back instantly you don't have to be waiting for something to happen in a GUI so kind of
scrapped that pretty quickly we've introduced the questio to slack channel so people can get on there and sort of any help or any problems that they're having or running any tools we actually ported the server over to Python as well to make it go across platforms you can now run it on Linux or UNIX flavored systems even Macs from the server side and one thing that we did was which made a massive difference with the refer like the DLL or the shell code this is based off the good work there's even fewer did to allow you to load the managed runtime CLR in unmanaged code space so now you can pour any implant from PowerShell one
line is now going into any process on an operating system so things like VC hosting got search protocol host outlook any processes running as your user or you'll use a level you can now migrate into that and be running all the same commands that you work at all so that was kind of a big thing also Rob who's here again today he really sharp socks so it's kind of one of this kind outside of things like Metasploit and cobol which allows you to now use all your tools client-side or sorry server-side when like you know tool that nmap telnet RDP so msds see you can now turn all that over HTTP beacons and it will be
relay at the other side of the implant so you can just RDP to servers all through HTTP beacons so it allows it to it allows you to be much more flexible and this is all integrated within in Charlotte in version 3 but then do some other things actually wrote some documentation which is great made it easier for people outside an area to use and also in 2019 or so around the Christmas time we released a sharp implant so this is actually now moves anything and who's completely away from either the power shoulder XE or the systems on management automation delouse we've now got fully fledged implants that don't have either of those in and we'll talk a little bit about in a
little bit fine we also added support for 2003 and XP and when I say support it more means that the sharp in but actually just works on that by default if they've got the dotnet runtime visual for which they can have if there's the latest versions of both those operating systems you might say why the hell would you back call it 2003 well you know some of our clients and even some of the big clients still have certain three legacy systems running in their network so be amazed how many times you see that and it's actually quite difficult least these days to get your tooling to work on operating system such as XP and serve
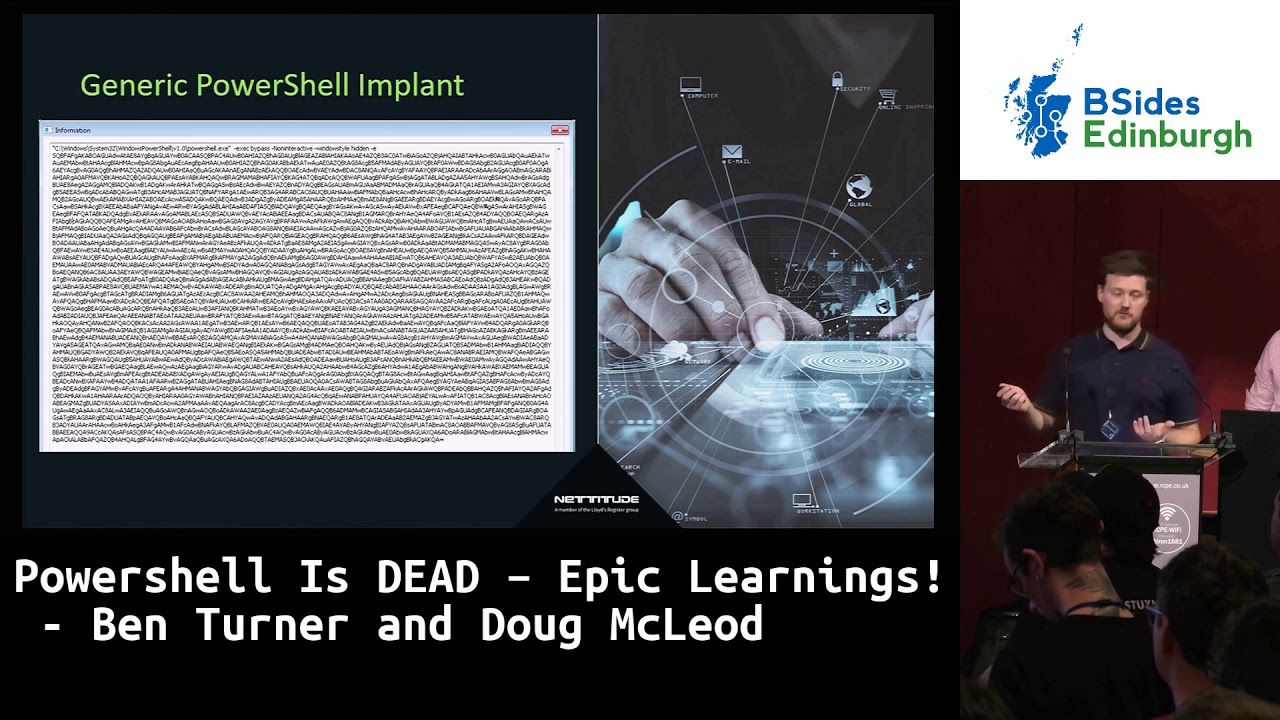
them green and in June Rob sir made some massive updates recently not pushed them yet so what's his face but sharp flux has got like uber quicker than it has before and the integration within partials going to be almost you know you start sharp stocks and it'll just instantly start you'll do all the server stuff on the back end and it's all going to be written in that cord I want to steal his thunder but that's kind of a lot of stuff that we're going to be doing and hopefully releasing in June if he pulls this finger out so this is what PowerShell used to look like so it's like partially to look like when it
first came out over in in PowerShell from an upset consideration from the defensive side this is what it would look like you would go in on a box see if it's compromised parish she'll be running you dig a little bit deeper you would see there'll be a massive global basics before you go into code that basics or you can see where all the CT URLs are you can see what the encryption keys where you can decode all the traffic very very simple to sort of debug from that side from a detection with the spent perspective especially with the integration of EDR so in carbon black and tan human life can come across you can really easily threat hunt your
estate and go if they show me everywhere where PowerShell is running and you'll be able to go and see the command line options and so if someone is using Cauchy to in your state you've got ADR on the PowerShell level really really easy to see so that's kind of where pushes you started and even when you added the reflective DLL on the shell code it's now just as simple with the likes of EDR Carmel a containing to find out where they've loaded management automation DLL so which processes so as you can see here net sh search protocol pokes SPC host all of these are actually bad malicious processes that we've started and put the implant in so again this is another
great way to threaten your estate to go and see where other people have done this it's very unlikely that process is other than PowerShell and a few of the processes that use similar versions of PowerShell that have system management automation in that aren't malicious so another great way to find PowerShell within your environment so I guess from a defensive and legacy approach to PowerShell so back in the day everyone's just like well should block PowerShell to get rid of it let's put some sort of blacklist in place and stop parish I was running on endpoints but I guess that didn't really cut it so the modern approach in the practical pro actually to allow it so things like version 5 has
much greater visibility like I was talking to you about like the transcript log and you can see everything that's in that run space you can enable constrain mode so even has language restrictions a bit like ad types you can't compile your own stuff on the fly and you can monitor for things like the system top management or automation dll in the process most vendors I think pretty much all vendors now all the bigger than fenders have a Massiah integration so a lot of people use PowerShell before to get code directly into memory so that it couldn't be scammed a lot of them now have a Mis our integration so they can see all the command lists before they go
into memory script block transcript log in a module log in again this is all great thus showing early signs of suspicious behavior on your network so I guess what this comes back to is from our perspective is PowerShell Det so if you take all the things I've just said into account it's all based off what you have from a defensive perspective so if you were going into an environment that isn't running any EDR and just running simple logging on an endpoint PowerShell is absolutely by impartial we're running no problem at all you're out of any logging any alerts even most a be some power saw lines still get around so in our opinion now it's not dead it is
purely depend on the configuration of the endpoints and the configuration of the client so with EDR it's definitely getting more difficult but you can still run system the management automation on most large EDR rollouts nowadays cause all of them have to have things like the tracing enable which takes a lot more processing power so again its usability versus security so it's all down to configuration which is key and if you didn't believe us a bt 33 corn fire I've been using it basically in the whole of 2018 it's a hack the aerospace and energy sectors there's some really good write-ups there and they haven't been doing anything clever they've been throwing HTA's envious or random emails basically again
HTA's department running power shop let you PowerShell one lies they haven't been even using sort system management run spaces just look you've been doing one-liners and they've been getting away with it and having some really good success from these blogs perspectives so if you did still think parish I was dead and I'm just going to introduce the C sharp implant so we released this in December January time this year same way as before so when you when you start pops you to you get like the two options the way to deploy it by shell code so you can deploy it however you want to deploy shell code any shell code cradle or you can just pop a DLL onto disk if
you want to so in the simplest form is going to show you how you get it going so basically just trip the DL arm disk if you don't know the entry point it's all written in the documentation or should be but if you don't open CF up explorer check the exports you can see which entry points you can modify the entry points but this one just boy pump simple and then you can do things like migrate as you could before so once you've migrated with a c-sharp implant what does that look like from a defensive perspective let's just take a simple 64-bit process search protocol how it's running on a Windows system but this is actually PowerShell sorry the
sharp implant running proxy to so what you wouldn't normally see is the dotnet assembly so no search protocol host on your system across your estate should ever have a dotnet assembly or done at runtime loaded into it as you can see here it's got a new app the main app that means got a randomly generated string inside the app domain as you can see there's two assemblies both there's assembly they don't have a location on this that is always a point that something looks not quite right and it should go and be searched of these kind of things other things that you might notice as well is it's loaded the CLR DLL all the MS Cori e dot DL out so both
of these are requirements have run basically two CLR with in runtime with an unmanaged space so as before I guess the obstet consideration will be decision time management automation DLL now it's the CLR DLL or the MS core ye AR but a lot of other systems even like silence I think I've written in dotnet so there's a lot of other programs out there across your estate now which would be using CLR that the allow so it's not quite simple to do the same we were talking about before we taenia man glad to do show me everything that's got the systems of management the automation because CLR is running a lot to programs even a lot of Microsoft
programs they're typically used on a day to day basis one thing to take note of is within the sharp implant is the help so typically the PowerShell in plan which is basically a command prompt has all the features of like changed directory copy file delete file when you let me introduce c-sharp in plan none of this is default so we have to actually recreate just a lot of the common features that you typically want to use literally like change directory that doesn't exist so you have to actually write the code behind that so we've done a lot of work on the court the allowable or Roberts also didn't work on the core DLL in written in C sharp it doesn't have
everything so what we've actually done is giving you the cradle to load any c-sharp assembly within your own one space so take seat belt take all the great work you know that Spector ops have done with ghost packets set your loads of other programs or that you can basically take any of those binaries compile them yourself I wouldn't ever take anybody up on top internet and run them and either you can run a DLL or run an XE there are kind of two main features so you can go write all your own modules all your own cordial owls and run them through this harness so all you have to take a now of is if you're
running a DLL the main difference I guess between the DLR X is the entry point so and actually should should have a main or should have a main method where the DLL wouldn't so you have to specify that as a parameter but as long as you know the class name so for example seatbelt sorry class name is program but the namespace is seatbelt so see the namespace the class and then the method and then you can run something like user checks happy days through the employment as long as it runs to console dot write line and you can we all hook that information and bring that back to you through the implant that's quite simple it is to run something like that
then push you to almost like the execute assembly within Cobalts right just dig in a little deeper won't go too much into the code but load you who do you know some dot net reflection stuff this is how basically we're doing under the hood we're going through looking through all of the assemblies that we've loaded in you know on disk so if you've loaded sharp seatbelt whatever it is we've loaded rated with the run XE we're picking the entry point and invoking it with certain arguments whatever you pass and with the DLL basically we're passing it the method name plus the parameters as well and then we're just capturing the output this is anything so although there's probably
not as fully-fledged as the power shelling plant all the coding and all the scripts behind it this does allow you to go and write your own code and just deploy it quite quickly within any c-sharp in pun again from a defensive perspective let's just take a quick look what that looks like though so again you see the app domain but also you'll see the EXCI so you want to be mindful when you're compiling your annexes what you call them so I think like C pal will then stick out like a sore thumb and people actually looking for this in the app load or this or a load assembly module and the obviously C part probably
not a good one going forward from a signature perspective so make sure you compile them and call the namespaces something different when you roll them out so I guess this is pretty much it from a c-sharp perspective well I guess it's it's hopefully helping get around other things like EDR but if you want more information on that I think Doug's gonna talk quite a bit that EDR and/or next nav now thanks Ben so obviously up to this point Ben's mentioned ez are a lot but they're actually little EDRs a end point detection response software so it's basically behavioral data and it's sending all that behavioral data through an agent back time i central and database and earthiness analysis there
so it's not just static signatures it's not just looking at one thing it's able to pick up what's the thing that's able to pull search trees and pack them apart you think about a word document with a macro that's going to kick off BBA that's going to possibly do w script and if they load up i'll is going to execute that that can all be tracked in a chain and that's the kind of power the EDR gives us that extra visibility that wasn't there before and some of the vendors your your lower carbon black silence sentinel one and before endpoint patient response was really a thing and it was there very much so head in the
sand for the blue team they had too much visibility now it's about up a role reversal as a better game changer when I'm in my red team's and I get in and I'm in a situation awareness one who says less didn't see something with had the black or Ori other that's very much so do not want I was hoping for a bit of an easy gig best time but unfortunately over happy I'm actually doing but it's not while as against Windows welcome to the everything is we're still plenty of room to play and you just got to be really careful a couple of thoughts we're going to go through a void in each directory and part in with EDR and the end deserts
they were going to have to share the bath for the DVR so avoidances as as as you'd expect that pretty much just rifle okay what EGR didn't do it don't get detected an example of this and sadly it came from a detection we got detected and we actually buy in a lot of the even got EDR products and start to research and look at them what it did before we did that we also went online and had a look see what certainly the attributes the one that caught me was carbon black we're gonna look had a look when you install and it was a lot of heat so there you can prevent so many suspicious
indicators is one of them it's got my earpiece siguiente know as well and that ends up being all the signatures that come back in the centralized database so about an RTF a moment for myself they actually began to those and you start to see pablor bills especially process execution suspicious SB sequels Payton what we were using SPC host as a as a parent and then executing things underneath that like however she'll like any description you've got has been at CSC to compile code on the fly that's all very suspicious also sent pulses headin in system seems like a really good idea but not you know that that's what EDI was watching for so avoidance stop figure out what it's
doing and then and boom do it another example Bank hmmm touched on this one if you can look through your whole estate and you can find all the binaries are one ancestor management automation pol then you'll find the signature here a companion tries to do that and it says not in these binaries these are the binaries that is fixed rates in the plane the end so someone's attempted to put the signature together or they've actually made a mistake and that is that they're not actually doing any checks on the actual and binaries at all they're not there to find both of the right once or not you can check in the process path so I can know and take one at for
Shakespeare goals drop onto the desktop call it monitoring boost or exit where system on a mantle automation inside it and that works like not on that allow anyway any trickery this is kind of so if you think about process 3 the ability years and you know they've got that visibility is trying to track that into not been able to sure exactly what you're doing that time so certain things that I've been about problem pain like parents Krypton did your Stevens was talking about that some typos in a name that pretty much an accurate mean see two known as well but the cord for it is actually this is just off Stack Overflow issue is what it
looks like you've got a start up in for X which has a structure with IPA phobias list and then you can update the Haven head and site that just here what that allows you to do is basically just say an explorer as Mark Dayton so if you think about that attack pattern you're doing this again if your animal and you've executed something previously that with a Pina appear and Microsoft work makeup in your parent but no you can actually see explore this map parent and when you think about how someone uses an operating system they're generally launched sanction Explorer not from insane or what documents us helping you bypass and what's the biggest bypass on their detections hidden pets with
them this is what it looks like it's different carbon blacks or partially to has the capability preparing pets with whom we've said sex two five two here and then and said carbon black or we've got as explode or launching SBC horse so that is just using the same stock overflow code and say that the allotted to carry this out but just proven that it was actually worked in buzz bypass things like carbon black and thick and parents whipping it can offset brought a blog post about six months ago and using adventuresome for Windows so the N event racing program booze event you've got a head or field which contains the process ID of the process is kept open event and
say that you've then got the data of the event and you'll see here just post paid and process ID nine two three four and then in the header you've got process ID line 34 that's what it should look like but if you do Haven process button pets Bookman sorry you've got four six five - is the patent process here but it was actually launched by process ID 1934 therefore you can say that's a detection you just identified hidden pets equipment they have process arguments within something clever and cobalt right official at the argue anybody familiar with us proper people basically every process how I should actually mentions work so I would forget the whole people like when you've done
something but well world were kissed on the top and red team in the rh2 looking folks you go check it covers process arguments button as well but inside each process I has a pair a process environment block which tells you a lot about the process and as a structure much like less here and say that structure with RTL a user process parameters and then say that you got command-line arguments so you can actually go and look through the memory usage structure to parse that and identify where your command-line arguments are in your process this is important because we can use and abuse as as attackers so if we create a process suspended with fake arguments
you can create wherever you want a powershell one-liner for example not endorse that necessarily but identify the pay abuse in NC query process information then we are going to parse the pet with the structures to find out where the command line structure is then going to overwrite the command line structure using great process memory then resume it or actually happens when that's happening as the windows and a lot of programs and side windows will actually take the event a snapshot there then add a payment which is being created so that's when it's suspended so if your appearance exists they're not not the bill arguments which is what it's going to look like min at once but
there's multiple to like they'll to actually do this as I mentioned they argue and say COBOL straight one thing was a really cool tool and fuzzy sake put together I just wanted to give you some code you could actually go look at to see how this is bottled specifically but in this example we're going to use swamp thank the launch command prompt we're going to get the P arguments of echo hello sailor and real arguments of echo will be seized what we see here is actually as echoed will be safe because that's the view arguments not what we wanted it to do for us were carried out after we actually looked at process hacker and look at a command line access
for little sailor so we can start to throw off the blue team with their own Toulon and if you think about how we're going to use that or you can use it for execution potentially bypassing and some detection you've got our owned execution or lateral movement probably obey throw one if you're going to move for one post-it make it look like you move to another then the blue team will be looking to this other horse while you're on vessels doing what you want there's quite a lot of good things you can do with that a nice lady please harden with you dr Ethier is not going to go away is honest estimate just seems to be getting stalled by more and more
systems he's these as well but runs the system as well and so I have more power than you generally on on an endpoint when you get there so you're going to have to share the basketball with EBR but the talk about how you are and what it's actually do some of the some of that tackle methodologies to migrate processes but many reasons why we do that but I just want to cover over some of the API positivity do it and then we'll look at how EDR is going to defend against that paper thing so migration basics will take a handle and another process with an allocated memory and that's how the process uses virtual allocate Olalla text and I'm going to
write our shell put then use invite process memory and then we're going to create a remote thread on that and that's going to kick off our M plan and save another process run another single thread so again point no-till inject all things it's got a lot of different API calls inside that it showed you how to build up some of the migration techniques and however there's many things you can actually use a migration techniques so create more threads one and in certain cases EDR has detected that but actually RTL create user thread is another the buzz exactly the same thing that wasn't detected by specific EDR so we were actually able to bypass some of the Ethier's just by using that
API calls and how does this actually work and this is my diagram of us together not 100% accurate that's how I see the world so you basically got your process which is going to call gotcha lollicakes which is then and I'm gonna call said bubble you allocate partial memory and that's actually the call that makes this s calls over to the kernel that's where actually happens and EDRs gonna try to offset that and there's going to intercept a pipe in event called quicken and in short hookans a technique that allows you to alter or augment the behavior of an operating system if you think about old-school gaming when you could hook the game and give yourself anything apply for extra
money this is exactly that and that's what EDR is doing so we just have a look at the same diagram again what you dr's going to do is it's going to inject the DLL into your process and then it's going to air hot patch with a jump when you call ZW allocate virtual memory it's actually going to call it's going to put a jump instruction there jump its own DLL and then it can monitor everything that's called and saved your process or monitoring down at what's going on determine if it's bad or not so that's all sounds about my typical me I'm not that great with Windows Intel's these days are better and other people in the
office as well if you just let them breather but I just want to show it if you sure have easy and accessible actually as so this is before EDR unless is you can use a debugger and a lot of program that's going on the CPI policy can see what it looks like which is a quick death so we're going to say our breakpoint down the bottom we've already loaded our binary set a breakpoint on ZW hate thread X which is create more threads and if I call and you'll see move our 10 it's our CX that's what it should look like however if we call install silence on my on a VM and do exactly the same thing
open up our injector program and put a breakpoint and jump to that break point will see that now we've actually got a jump to a from this side then they have 64 it'll just remember it's no basically this is what it's done it's hot patched your a process another jump in pity a DLL and it's not it's not all miss islands that works like that there's a lot of different in the arts and they all do very similar things this is an example a sensible one secondly our DLL and save your process if you actually again look at it with no got a jump instruction out said that will you create credits we should jump
it into the a DLL so they can monitor what you're doing when you make those calls but the great thing from our perspective and bringing back the good things is actually we are in that process so our process they've given to edited our process and we can just could be Patchett and cut them back out so you can return to all that code to the old boots or got repack memory to I jump into the original good I'll pay them for address table two points the correct function create a stub to carry out the same system pause which means you never have to call those windows API key and calls anyway or use something like free
library to remove interfere in the air the bypass on silence is already been covered before by whole Hawaiian you opens inaccurately here so you have a look at that as a really good one what we didn't want to just show you a demo but someone else is already been researching so some stuff we were actually working on yesterday there one feel about bugger mode it shows you a before and after so this is going to be we've already got empires import situ or want to my agree and Sentinel one is going to catch house migraine and then we're going to go cut it out this is us first and foremost and they get there's a bit slow but
basically up here for anyone who's not use horsey to these are two and pounds of already got n say but I've already bypassed and EGR to get our Empire is running on a box sent no one with an island user and this one and say ped two three three six and we want to click to make it go faster but that's not going to work so and safe process Explorer now we can go get a pet we can go account and you can see that net SH is running and then Satan a sh will be able to see the center of one dll's so they focus it so now when we go back and we want to
migrate and we want to use the same API calls what we should see a Centon or once you catch us and we'll be protected for it so an N or C to quite simply migrate will migrate you to you don't have to give any additional parameters it or migrate dealer migrate another nature thing by default and obviously all our commands are on their side everything else comes back on their safe so we'll see that the migrate command actually come back and after check sent and want a five-second deacon at the moment as well so it's just a hunk that's more so that's that it's know migrated we're actually going to get a shell at morning because Sentinel one
can install them detection mode only not blocked in would which is also something we thickens I can't remember when we're doing red teens right team as the f you actually get something the blue team may be well on tell you about that point put everything blanc original something's going on so they can silently watch what we're doing anyway right now with no go at an additional hemp I'm n for jump back to here you like this either in the bottle we've had a threat detected form our migration and where my pecs are off so there's our threat within detective blue team and I want to is it won't be long before without a lot of IDI our products
have actually got isolation people don't and things like that as well so as soon as you've done that you your own missions isolate the new at the network the next one hold flu have split up and it's a bit quicker but basically this is the same again we've got an endpoint here dirt running then head seven over five sex but that's time what we're going to do on the other side is we're going to hook it or unhook it sorry we're going to attach it to a debugger again just showing that is definitely an SH it has Sentinel one dll's in it we're going to open up a debugger were then going to stop it we're going to hit
power function now we're going to modify it back to what the original code looked like says he's out what we're doing no we're just going to attach sin that Sh there's our great point record the jump instruction is going off somewhere else it should shouldn't be doing that sort of following a disassembler we're then also going to look out aid yeah though yours the Dom which gives you the base out that had that Mary address what we're going to do is we've already worked so exactly the way put we're going to put back in their PC is assess call specifically for that's personal windows to do the WX once we put that back end will be back to move ten RCX
and movie X ABC that's exactly what it looked like before they had got it or about it hands on it and and modified it and made it and so now what we're going to do is we're going to detach from this we're going to prove that the Empire is still running and memory so it's not broken in any way and then we're going to migrate again
that's all run a quick PWD just to print the working directory for our implant I'll come by down here and tell us the working directory we're then going to run migrate since just exactly synthesis last time we'll successfully migrated another shell or comment as it has no there it's here an open we jump back to our VM there is no detection because Sentinel one just doesn't see it hooks under the very start when you kicked off the protest but event continue to monitor that on an ongoing basis so they that in our process so you just undid it and I think yeah now so actually new something to a needy are also in do some cool things as
well this is some of the problems we've come up against the way and we face them on a regular basis but some things when you're doing this is then your cat and mouse in terms of we want to forget then they start to look at least it stopped you've been able to pick it a lot of different reason what you can play in and welp in a couple of some additional ones and okay um series we've just been discussing has red teamers on our way to the objective the certain things that you have to do you have to migrate you have to persist on boxes and I mean we just socially just can't run again me
the whole time so I so I just sort of seen EDR is getting pretty good at spotting what we're doing we've found as well that you know there's also seems to be a bit of behavior about the one of a better term behavioral signatures coming along now so you're kind of the example Doug gable the sort of the canonical migration of opening a handle for a process allocating memory coding your mo thread there's other examples too such as you know downloading a file or opening a connection out to the internet writing a file down and then executing code you probably going to get pinned as being a downloader other actions as well like opening our
Pels sass and then and dumping all of your memory you're probably going to get pinned as mini cats so what essentially what can we do well is it there's a few things realistically and we can learn the detection mechanisms we can learn what's what's going on we can use the live off the land strategy and we can abuse built-in functionality now some complex engagements have done that I have been doing recently it required us to kind of look back and instead of look at some functionality in Windows has been around for a while and it's basically we've had to become best mates book calm because most of this functionality is essentially accessible viral so being that it's a 10 to 15
minute talk or my section is at least no way in hell that I can possibly begin to describe what it is and James Paul Shaw did a talk at infiltrate it was last year common six minutes absolutely brilliant and probably the best kind of hope that I've seen you know that they don't yeah that that will get you into devices but there's two main takeaways that you can kind of hug them this is that comm is not a language it's a way for languages to essentially talk to each other you can build components and then one and in one language and then another language can consume also the way it's implemented it haven't uses the
registry underneath so as we're kind of going back to well we're on our red team we've sort of landing somewhere now I'd love to say that we had like this massive stash your browser zero days and that's what we're using to get in but it's just not the truth quite often we'll sort of end up in a process that shouldn't be talking out to the internet shouldn't be executing code shouldn't be you know you shouldn't have system management automation that loads of different things that it just shouldn't do so what we need to do that is to move into a process is you know a bit more doing look looks more like what we're doing so you can try and hide what
we're doing I use a great candidate because it's installed everywhere that's quite often open and it's talking out to the Internet I did a to the talk last year it's still called common power thief which I sort of the least it's all how you post exploitation ID there's a little section on there about actually being able to migrate from one process into entry without using any of the traditional mechanisms now why this is key because it very the attribution between you won't have this sort of suspicious parent-child relationship ie you've landed in where that's where executing code and then it's suddenly called by or something else you know you haven't sort of seen it an open process you haven't seen
anything else and so how does this work so the key to it is a concept known as Junction folders this was a technique that was leaked in the vault seven dumps haven't been through it of course better selling the Internet very very interesting read it forms the basis of sandbox escapers recent I think about a week or so ago the sandbox escaped out to be the needed integrity ie process and essentially you can add some registry keys and then you can build a folder within a certain format that if you navigate through it it's then going to load a DLL of your choosing within that process so is there a legitimate use for this absolutely and it's a
little bit of hack but so if you sort of look at the top left hand corner day you'll see an icon that looks like a control panel but it's actually not what it is it's a folder that's been named in the particular format so if you sort of see the middle red box there it says something like file folder and then it's got a dot a squiggly bracket and buried and then a squiggly bracket on the end now what that means is as soon as you try it as soon as you navigate to that and windows will actually then look up that particular value in the registry and which happens to be under eight hkey
classes root clsid and then reviewing and then however those registry keys is set up it'll it'll then essentially load what's there so in the case of control panel it'll go and load shell 32 dll and then internally how the registry keys out and all the local control panel so can we use this absolutely we can don't create a run now in order to be able to create a HQ passes route you have to be admin but thankfully you don't have to create them there we can also create them under in a to hkey current user which is essentially have access to so if we wanted to build our own switch we've done here you'll sort of see in the first
screenshot he had default running off to Val DLL which is evil file and now the beauty of this is you don't have to call it dot DL Doxey better just load it whatever as long as this kind of aden ends at heaven whatever if he's going to get loaded the second bit just shows some other values that you have to set up they're there to be recognized so how could we use it well if we can get access to essentially if there's an IE window that's probably open we can get a reference dollar and and if we can get a reference to that will in chrome and we can then call this method calls navigate to now don't
navigate to takes urls in this specific format which is shell triple : squiggly bracket the guild and then screw the bracket at the end now if you trigger the navigate on that on ie II's going to read that registry key pick up the DLL and then load it into that process oh so how do we get a reference to our ie window that's open well thankfully there's another common class which is great one to cochon will show windows and what this allows you to do is enumerate all of the open ie and explore and Windows Explorer windows that are essentially currently open so there is essentially activate that windows property on that which is an Iranian
just those book or which one's the one we want and then you will navigate so has power shows dead here's an example and and this is it essentially being done in PowerShell what we first do is build up a big you--it and that just happens to e so the big word there is actually a specific one for show windows that's actually even certified out in the registry and now we create a type we've got a net from that you create an instance of it and then there we just picked the first one so we've basically just in zero indexed so what this essentially will rely on if there's an least one Internet Explorer window running at this point in time and if
you've got just a wouldn't you know it's for a window it's this particular example doesn't support every day - but then what I've also done then is I've built a a junction folder with that gooood and so as soon as you hit that you'd never get to known that that will then go and you know I eat will essentially know that the alarm the process and now we essentially have no relationship between it because it's all gone through calm so is that weaponize herbal you know in a way that you might be able to land in an environment absolutely and you can actually do this in VBA the program with VBA and is there isn't really any easy
way to do registry function yeah this sort of leaves or anything else but thankfully it has a concept of platforming boat just like net dozen that you can talk to and call essentially the low-level wind produce or api's so what I've done there is just essentially defined function prototypes which relate to the actual low-level wind 32 api's which all of those basically sort of you know you create and set and registry keys and then from there we've got some more VBA which just goes through and essentially create sort of the the registry keys like before and then we have our final piece of the puzzle which we create the shoulder the application you then go through all of
the basically loop through the windows look pretty anything that has a full name of I explore and then based on the clsid we had you build up the show triple colon that's really thing and then we call navigate and then that's gonna launch out so do you have to write just standards native C++ details now I spend about seven years of my life for any super spice and I'm I'm kind of over now I'm like the first sort of c-sharp book and thankfully yeah you don't have to because also as well not everyone knows C++ and it's quite a massive loan you heard there is a function we've got net called conquerable wrappers and now
these these are really really hardly they allow you to essentially choose well build a don't know don't go to the way so consumed from a comma where language and absolutely not enough time to go through in more detail but there's a really good link on the MSDN on how it how it works but essentially you Stan she ate your object like you would any other column net run Constance started with the others loaded it calls the constructor and then you can start interacting the essentially the object so how do you build one all we really need is basically just the dotnet assembly with a class that implements an interface and then we need to set up
some registry please an interface is a kind of a very important concept within calm essentially it sets up a binary content contract between objects to sort of say you know I support this function yeah so the first thing we have to do is we have to build up our interface and so in this case here which is got a namespace vegetable pretty much everything you need will be in the system that runtime got integral services namespace and we just have to hannett 8ao our interface as con visible have to give the gooood we just give it a ten interface type in for this we just live in two places just over those and then and then we have our main class what's
kind of not shown on here because the Constructors is too much code I would actually have to provide a function definition for that test method which is defined in the interface if it didn't do that then it would compile of the break so what we're essentially doing here is just using once again sorry we've got a marketer's con visible true give it a gooood we give it a program ID so if we do want to create it we can create it by that name rather than having to use or using period and then from there yeah so in the constructor when there's a deal that loads we're going to have just you know message officers say I uh I've also
got like I'm not slide in the shell code and that'll run so so I did say it is registry keys so if we didn't want to be able to use it the previous technique of actually the junction folders we've got to go into census record what those registry keys up so unfortunately the next year I've got it kind of goes up the process monitor pretty quickly on but I'll just explain what I've done is essentially I'm looking for and anything that writes to a cheap prices route and buyer in this village because msbuild essentially was gonna go build and register than everything else so here we go so there's my filters essentially clean the project we build it and then
from there I know so sorry is well yeah if I didn't mentioned you have to run Visual Studio has has a lot of roads to be able to like take beta key classes route so there we can see it's kind of written out I'll just you jump to impress a small over there proto jump straight to the register key that's been written and so from there you can sort of see the code base upon settlement here though there's a whole bunch of other things that it'll set up okay so then if we want to use it in the the junction folder scenario what we've got to do no no how with a lot to be honest I mean
basically all we have to do is just change H key actually parcels root to just be actually part either and then we can essentially put that into into the registry very important points is that John Windows 64 you have to import it from the 64 bit process or use the explicit 64 bit registry key otherwise it's going to end up in there the windows 32 node and it might appear there then you use regedit and you waste a lot of time looking for it there's a good write-up just don't rest on that link there and so now so in this example I've tweaked my Explorer internet explorer shortcuts slightly and so this kind of demonstrates a bit of a
persistence mechanism just wait for this one that surrogate explained
should be yeah yeah so there you go just picked by E and that means that the dll is basically though that this button picked off and got a message box and that's one of the other code I've done if we're going to approach this Explorer and then just view the PLL's we can essentially see that's loaded okay so remember this script from earlier you know allows you to essentially launch a DLL well we can tweak it slightly so what happens if you've got an explorer window open instead so in this case we're just assuming a Windows Explorer and in this case here what we're going to do is just navigate to powershell we'll see what happens so here we are in
link pad which is our favorite development tool and all I've done is just look well what I'll do is just launch a PowerShell window I'll copy that previous script paste it in and then we launch another power shelving there now the important point here is the parent process so yeah it's actually launched from the store rather than any of the others so rather than having a nest around the load code from Stack Overflow or anything else then just call a couple of common objects then BOOM we've moved into another one and I've sort of been having a look at this from an etw perspective and I think it kind of gets around the the previous
discussion part putting your concern so if we look at this we can see the circular one has essentially been launched from Explorer rather than the app and so you've broken the attribution between processes now the beauty of that also being on is you can pretty much that's it understands that ie speed a VBA all of them so cool so kind of a summary on media and it's not a silver bullet as you can see we've got our bypasses but raise those like something's rather than others it does give you incredible visibility and there's a very very good points and but but as that everything has old technology there's a complementary piece and exactly you shouldn't eat so little
item and yeah we're all about sort of pea processing technology and also as you can see - this is a constant hours race so huge predictions yes I'm just some future predictions as Rob said bit over reliance on EDR it's not the Silver Bullet customers have broken all their attention focusing all their attention on the endpoints and not actually the critical data so probably going to see a push from that perspective to make sure that's all blogged and monitored a bit of a move to zero trust networks and MFA everywhere that's kind of a bit of prediction machine learning so a lot of investment into people and process so if you can understand you know your processes
internally and the attacker isn't going to know those processes so anytime you avoid those processes from a behavioral perspective you can sort of see that and talk catch people out quite early I think it's going to be a bit of a shift to see two frameworks using Warsaw native C++ code MSF you know could even be revived for red teaming and IJ is doing quite a bit of work in that space all standard Eve a B and E D our vendors are starting to adopt a BIA and am si not prediction but Windows seven is going to be under life in January so what sort of space Windows 10 has removed net v2 so all the PowerShell
version two stuff is completely gone now in the later versions in Windows 10 and I think roll bass and all bins I think again they're a finite list so from an execution perspective people are sort of there and away from them now because a lot of IDI arts or vendors have got those signatures in place who's slightly better to move around them and use even like an executable so it might seem quite simple but actually that's not on their list of known bad things so be not on that list then you're probably going to get through and that's they just leave you with find a job you enjoy doing and you'll never have to work a
day in your life thank you very much for listening we doing some training at silicon