BSidesIowa 2019 "DevSecOps Key Controls for Modern Security Success"
Show transcript [en]
welcome welcome it's 11:00 so you are in the room where we're talking about dev SEC ops is everybody aware that you signed up for this so just remember that an hour from now so in this discussion my primary goal is to introduce you to what I think are the key security controls that you need to be aware of to succeed if you're trying to lock down code in an organization that's moving very quickly there's anybody in an organization that's moving very quickly ie deploys changes all of the time without telling you about it that would never happen in real life wouldn't always in production I miss the days of development where I could just change
code in production but hey I absolutely throw it over the wall right that's one of the key components of DevOps let's see let me introduce myself I've met quite a few of you in here before so good to see you again for those of you that I have not hung out with my name is Eric Johnson I am a local here in Des Moines technically West Des Moines by trade I'm a coder so I love code you'll hear me talk about you know development related topics quite a bit in the world of work I did let's say ten years time in the enterprise world in financials and if you want to talk about slow moving traditional security oh yeah
that's what you're talking about they're very adverse to the cloud very adverse to working together without those silos we just talked about so I lived and breathed traditional security for about ten years did the evil security thing where I would run those security scanning reports and pop out a 10,000 page PDF with all sorts of bugs in it and I would slap it on your desk and say I'm going to happy hour good luck right and because that wasn't on my job description I wasn't supposed to help you fix the bugs and we know how that works out right the PDF gets uploaded to some portal and it sits there for a year no one actually looks at it so that's
kind of the world of InfoSec that I did for quite a bit I started teaching for about six years ago and wrote a few classes mostly around secure coding we developed a dev sock ops course myself Jim Bird Ben Allen and Frank Kim that we've been running around with for the last two or three years and it's been pretty much a regurgitation of what we do with our consulting world in my day life at the moment I do lots of modern static analysis kind of coding looking for evil code telling you about it as soon as you maybe type it that'd be better than the PDF report when it's in production already just saying you know
so that's what I do with my nan sands time I usually split maybe 6040 between doing real work and teaching so I get a lot of different perspectives on what people are doing in the real world inside of their organizations and then we can turn around and try to help folks see the maybe the light a little bit in terms of shifting security to be a little more lean and a little more agile in the way that we do things so contact infos up on the screen you can find me at a.m. John 20 on Twitter Eric Johnson at Pumas can calm so shoot me a note if you have questions about anything just a
little housekeeping note you can take all the pictures you want these slides are up on the Pumas can blog the PDF is there so you don't have to take rapid-fire pictures the entire time some of these slides have a lot of different links and tools and references on them so don't feel like you need to read and take pictures of them all you can go grab the slides later so I will tell you the story behind them here's your agenda leading up to lunch so the whole goal here really I'm going to give you a few resources from a cloud and dev SEC ops perspective before we dive in and talk about my version of the four key
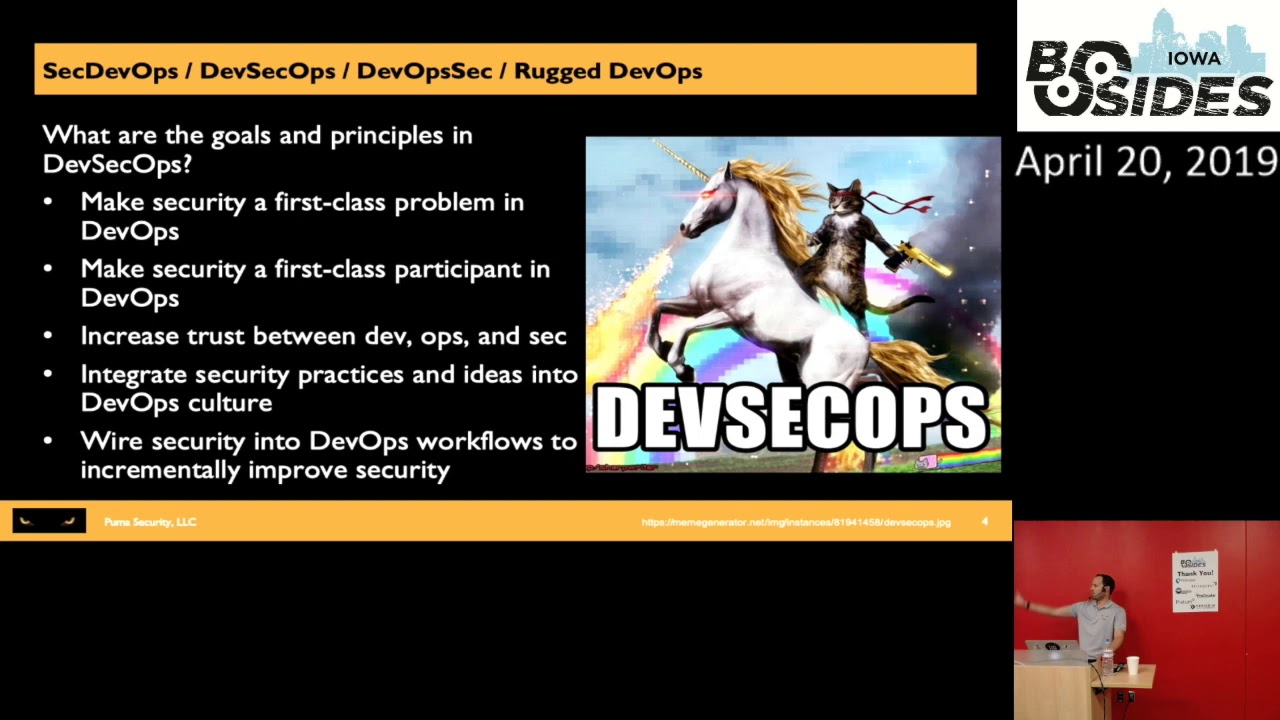
controls you need to have in place in order to try and keep up with the DevOps world sound exciting rock and roll right let's do this okay this is my favorite meme on the internet right now the question that I get all the time is Eric what is dev sec ops and this meme sums it up is it a horse is it a unicorn is it a cat with a nine millimeter a gold one nonetheless who knows and a fire-breathing dragon all at the same time and that's pretty much the loaded concept that you're looking at so the answer is really it depends on who you're talking to it depends on what they do for their job within the
organization if you talk to dev folks how many of you were DV folks inside and out anybody write code all the time alright my people there we go so you talk to dev folks in dev SEC let's just say that's typically application security stuff we're doing our code scans are we doing our dynamic pen test we've got Jared and Brad over here trying to bang on the front end of your website and find bugs that's the a player that we're living in from the dev side and if you talk to folks that go to the O wasps meetings all the time and you talk about dev seccomp all they really talk about is let's run
this scanner on that scanner and that scanner against the Java the c-sharp the node the PHP code etc but it's so much bigger than that so take it to the next level where's my ops folks at anybody on the ops side you all don't give a crap about Java or C sharp code do you you shouldn't write it's not doing your job for you so what is well you're laying the groundwork for the job on the c-sharp to run on top of it but the problem and really the reason dev ops came to be is because dev does these weekly sprints and they bundle up changes every Friday for the ops folks to deploy it and when
you stack those up for 18 months while you build out your windows 16 server to run it problems happen right yeah so ops is a different conversation it's how do you move quick enough to keep up with dev so you talk about operational security what are you doing in the world of automation to automate operations how many of you love using tools like chef pup and ansible salt sack or even cfengine to automate config management and build out your machines for you nobody raised their hand love that's a good point I did say love how many of you use them because you can move more agile and more quickly in the world of operations so those tools the
dev sec ops part of that conversation is what are you using to do the same pattern as the dev side there's static code analysis tools for puppet and chef recipes huh that's interesting right there's automated security acceptance test tools they can actually let you spin up a quote gold image and certify it to make sure it's CIS level one benchmark before you've actually launched it in your org instead of going through that checklist manually and making sure all the points add up to your minimum requirements crazy right so using the same process automation you can lock down operations from a network perspective how many of you used in API potentially on necess or whatever your
net sec scanner is to actually run continuous vulnerability assessments making sure that you never bleed away from your requirements instead of actually having some human being push a button once a week or once a month to try to run the scan same process right different conversation then you got the cool stuff on the security side I have had so many students over a week of talking about this that walk away and they're infer incident you know forensics or Incident Response something like that and they'll walk out and say I'm so glad you taught me how to use Jenkins all week and they're not building dev code they're walking out building an automated pipeline to actually use some workflow to parse
images in hard drives and staged them up for forensics analysis or use these sorts of concepts to actually automate going through log files and looking for patterns and loading that data back into some sort of information management system the concept of this unicorn or dragon or whatever it actually is on the board that's how far we can go with this in why we love the tools itself because it enables us to do all this work so the answer is really let's make security a first-class citizen and discussion and whatever it is we're trying to secure and make it part of the workflow very high level but that's what we're looking at so resources we built a poster now I
don't have anything any of these on me because I suck at marketing but you can go to this link that's on the slide it's a short link and this is really a sec DevOps practices just into end we broke the methodology down into phases so pre commit commit acceptance production operations and we splattered between about six of us every open-source tool that we're aware of on the planet that can support you in that moment into this poster so it's a way for you to build out your dev sock ops program at a zero dollar cost it's crazy right so a way to get started we've also got a cloud security top ten list on it now Ben
Hagen who did last year sans had an insecurity summit for the cloud he kind of started the conference off with here are the top ten mistakes that we make going into the public cloud with our data sounds like an interesting list to check out right you know that whole s3 bucket on the internet problem yeah that's on there along with a bunch of other stuff so that's described on the poster also ory Siegel who works at pure sec created the first version of a serverless security top ten how many of you have functions running out in the cloud that are just doing work anybody oh come on functions as a service we love that stuff right what could go
wrong it's still code so the same sort of issues are re surfacing we'll say in a little bit different context so this is actually now a beta wasp service top ten project the PDFs out on the O ASP org mainly from Ori from Pierce X so kudos to him for contributing this so that's also on the poster good resource so just check those out if this space is new to you this is Eric's version of the critical security controls reinvented with a dev sec ops focus so across the entire into an workflow there's a lot think about here and there broken down into pre-commit commit acceptance prod and ops and all the different automation techniques you can use from a security
perspective to start to chip away at building out your data set cops program the remainder of this discussion is going to shift to the four things that you need to think about in order to start picking those controls off kind of high-level but things that I know that if they exist you've got a better shot at keeping up with dev and ops when they're moving this quick so number one the paved road what the heck does that mean don't worry I'll tell you all right what is that of course there's a picture of a paved road here of course now the gates to guardrails conversation how many of you of you have read kind of the
white papers of the case studies from kind of their early DevOps adopters such as Netflix or Amazon or Etsy or Google you know just a couple of really small Silicon Valley companies that's suddenly are billion-dollar companies using these concepts what they did is said look in order to move quickly we need a way to do it securely by default so if you are working in one of those orgs they've pre-built the operational paved road for you they've got automated pipelines that are building out and certifying and publishing gold images and those are all we scanned and looked for for you know in secure packages maybe in secure versions misconfigurations etc if you pass all of
their automated security checks the gold image flies out the door and it's ready for the dev team to pick it up and run with it on the dev side then they've got automated pipelines that look for misconfigurations in code so my dev folks let's say you're starting a brand new API you want to write some awesome micro service and launch it out into the Netflix ecosystem you're going to do a file new secure web api template and guess what it's got all of the security configurations that we constantly screw up you know like turning HTTPS on or sending out those security response headers etc all of the security packages are pre-installed pre-configured ready to go on then there's this comment in
the middle of it that says Eric write your code here and do not touch anything else sounds crazy to think about rain so that's the ops paper of the dev wave road we've got the ability from a security perspective to build out centralized security scanning pipelines that's the security paved road here's all the tools we're using all of its automated ready to go ready to ingest some artifact certify it scan it and send the reports out as artifacts at the other end so we can pick them up look at them and make sure everything's good if you do this ahead of time now those of us that are jumping in too late here you've got some work to catch up on here
so we've got a lot of security technical debt but does that mean that there's not value and happiness it becomes really easy from a find and seek perspective to look for people turning those security switches off - from a code analysis perspective if you know what they should look like and suddenly it's not there we can start dropping builds or pausing and saying what happened so on the ops side some things to think about one of my favorite conversations from the ops perspective does anybody have hardware devices palo alto cisco junipers etc etc running around on their network from a hardware perspective now we said we don't like those config management tools like ansible I'll throw that one out there
but has anyone used ansible yeah mo playbooks to configure a firewall before you can do it you can legitimately with code with templates have a pipeline that reads down our code repository takes an ansible yamo file and it customizes configures and sets up all of your firewall rules for you can you imagine that you do a git add a git commit and a git push in a pipeline automatically reconfigures and provisions thousands of firewalls across your organization that's a paved road for network secure right there everything you do in that case is automated it's tracked and it's inside of a code repo so you've got history on yeah Jarrod screwed the firewall rule up we can scream at him
when he messes something up instead of the administrators that in the traditional sense go to that little web portal for each individual firewall and we click a bunch of buttons and change some things and hope that we do it the exact same way every single time it's crazy right you can do that with network as code with all of your firewalls your switches your routers all of that on Prem hardware just one example of the paved road for that gold images same drill use that same template increate all of your gold images and spin those up into your Amazon or your as your VMs so all of your engineers are using a pre harden pre certified gold image does anybody
use containers those things would never have any problems would they no what could go wrong here so you can use instead of downloading the docker image from a stranger on the internet through docker hub you can create your own docker Gold images using the same technique now you know your Gold images for docker are secure you can build deploy and provision an entire cloud infrastructure using about maybe a thousand lines of yam all suddenly all that cloud insecure top ten list I talked about has gone away because you know that that centralized paved road for cloud infrastructure is sitting there we get a request for a new sub account this new dev team wants to do
something cool we point and shoot the entire paved road cloud infrastructure out into Amazon everything is there harden sitting there waiting for those engineers to just launch the little micro service out into that account and we're good so the ops side the paved road here is tremendous it's a lot of work years long journey but you can really take control from a security perspective I'll tell you a story this is some code I kind of pulled a little bit of it out of our paved road for our Amazon infrastructure this is cloud infrastructure as code did anybody have a moment in early February where they announced a CV II in the Runcie library for the docker
engine where suddenly your your stomach drops you're like oh my gosh we've got hundreds of different VMs running docker on it powering most of our application stack we've got a Patchett right zero-day 101 this is some code that I did a git clone across my paved road cloud infrastructure and then there's that little it's probably kind of hard to see here I'll zoom in on it so you can actually see what's going on line five there's this image ID that's the gold image and right now my gold image is vulnerable to that Runcie issue that CVE that popped out our organization we've got hundreds of servers running that gold image it was as easy as they
get clone edit that image ID get add git commit get push with hey Eric's awesome today I'm patching a hundred servers and five clicks of a button like that's how I like to do work I'm lazy and I let a pipeline go out and Reaper vision all of those instances it immediately spends up new secure images and tears them all down just by changing one line of code it was maybe an hour journey for me to run some smoke tests and make sure that the infrastructure is patched that's the dev our behind the whole network side so just an example of how that paved road can help you achieve security in a completely unrelated dev style
conversation it's fun right now you have to understand version control and we'll get into some of that stuff the dev pave road is harder number one because the devs love to download the latest and greatest hottest JavaScript framework that's published by some company on the internet every week so now you've got many many paved roads to build we cannot really keep up with this but it's worth the effort what I would recommend is pick the language that's representing the largest portion of your codebase start with that one so if you wake up and you're like you know what I don't know why but people are using Java spring boot for 90% of our services let's build the spring boot paved road
template make sure you've got all the secure packages installed your C surf your cores configs all of those sorts of web app security related problems they're pre-configured and hardened in there and everybody's got to start from that centralized repo to spin up a new project we continually suck at storing secrets and places that are designed to store secrets so this is crazy to say out loud but what if in your template you had an example of reading a database or something credential at startup into a variable and you showed everyone in the organization how to do that and how to do it securely do you think they might follow your pattern just food for thought all authentic Asian
authorization validation and coding all that oh ah stop ten stuff if you have examples of how to do each of those things in that template guess what they will follow the pattern so that's the dev site oops my badge tick on a beating here all right this is just an example and this is something I yanked out of one of our templates this is a dotnet course start up configure services method but it's got some pretty interesting security settings in it hey look there's password configuration in the top block we're setting our length complexity etc we've also got locking down the service so no anonymous calls can drop in we're also going in and making HTTP the default adding all of
those you know security headers like your strict Transport Security is your XSS protections your content security policies all of that is being pre-configured in here now the devs don't really need to understand all of those security controls as well because it's taken care of ahead of time we get out in front of it and we can start to win so that's the big takeaway how are we feeling about the paved road I just gave you three years of work to follow up on enjoy so we're done right so number two is leveraging automation and we took on some interesting comments with a conversation on Twitter this week where we said all of InfoSec needs to learn
how to code Jim Monaco was out at his Hawaii conference loco moco sec and honestly I'm on board with his comment and it's not to alienate people it is not to you know say if you don't know how to code you don't have value but it's to pick up the concepts learn how to use version control learn how to use these automated continuous integration and delivery systems because this once you have the paved road is the only way to keep up with the changes that are going to happen once you hit the ground running afterwards so prerequisite number two then pick your poison here there's a thousand of these CI and CD integration and delivery tools is what
they're called to play with Jenkins and if you love using Jenkins I did say love there I love using Jenkins but I'm weird so there's lots of options Jenkins circle CI team city hazard DevOps Amazon's got their own code pipeline I don't really care which one you use if you do this long enough you'll end up using all of them and you'll hate them all equally at the end it's fine but the idea is is to start taking your manual checklists whatever you do to get something into production and start automating that workflow just and do a sequence of steps these CI and CD tools help you make that checklist happen in the right order and if something happens
in the middle of it you can stop look at the results of a report and actually figure out what went wrong and you can fix it and play the game again now there's a lot of benefits to doing this in terms of monitoring and audit logging and compliance I just gave away where we're heading after this conversation by the way so this is an example I pulled this off of one of my vm's that's got a pipeline on this is actually spinning up an entire AWS cloud infrastructure from the ground up VP sees sub nets network access control this security groups API gateways with throttling and hardening enabled spinning up container clusters this pipeline is actually creating more
pipelines in the cloud to deploy kubernetes clusters and that's getting into a much larger picture of what I'm referring to here but you can build all of that in an automated fashion which allows you to wire in security controls you knew I was going somewhere with this right okay so security controlled number one this I found with a very lightweight grip and I said look your load balancer and I'll zoom in on this code a little bit so you can actually see it this is something I pulled up out of a scanner and it flagged me and said your load balancing pollers policy is terrible we're supporting TLS 100 a no-no in encode we can upgrade
that to the TLS 1.2 policy and then you play the game get add get commits get push and it reprovision x' all of your load balancers to force your clients to use modern browsers that'd be a good start right and this is all audited I know who committed this Jared probably the very first time and said one dot o is what you would like to run into an append test right for sure yeah good stuff and we know who did it and if this comes across your desk maybe via a pull request where I'm actually trying to roll it back you have to approve it you can leave feedback provide comments and say no Eric don't do that
that's silly you can reject it force me to fix it all of that auditing and visibility's just managed by your version control provider for you before code has ever actually reached any sort of real system you fixed a bug so that's the power of doing version control and code driven Network and cloud infrastructure is that you playing the dev game to do peer reviews security reviews you can notify people if really important files change you've got that part covered now we get to talk about automated testing folks that love DevOps just usually only talked about this part which is the automated piece we've done a lot of work before he to get to the point where we're running
this scan but this is actually running a static code analyzer and it's not a normal one we're not looking at Java and c-sharp code we're actually analyzing yeah Mille that's building cloud infrastructure and it's saying Eric you suck at writing cloud infrastructure your CloudFront distribution has no logging you've got an iam policy with star star on it which means admin and AWS for those of you that don't use that that's not a good feature I've got a bucket showing on the internet not cool security groups basically let anybody in lots and lots of things that's yelling at me about and we've caught it before we've even built the cloud infrastructure the pipeline has stopped and said no we have some
issues let's go fix those this is running a tool called CFN nag has anybody runs CFN nag before it's a CloudFormation template scanner open source maintained by stella Junt customizable you can fork it and write whatever rules you want to flag stop and complain about things in your pipeline pretty sweet right so it's leveraging the dev code analysis concept and boom now we're analyzing our infrastructure code the other part how many of you are auditors and you walk in and you say hey I've got my checklist I need all of your audit reports all of your scan reports these CI and CD tools are capable of storing them for you oh look at that now
they're sitting right next to every single build certifying your environment continuously that you're meeting your security requirements and you can just go download those whenever you want so that's another awesome feature we can pick up by just using the dev tools to automate security for us just getting exciting right all right I'm a junkie for CI CD tools so if you want to talk about that more find me at lunch somewhere next up item number three this could be a full-day conversation I'm going to jam it into about ten minutes because I think we have to be done one at 11:50 all right supply chain security this is such a loaded topic anymore in my opinion probably the number one
challenge that we are facing in IT secure at the moment historically this has been something that we've blamed the devil because they like to go download packages from strangers on the Internet via nougat maven the node package manager we just pull in open source packages and we spin them up as part of our apps and we run them on our production servers and we hope that nothing can go wrong here has this bitten us before yeah Koff coughed struts COFF COFF by the way if you're running struts in real life unplug that server just decommission it move away from struts it needs to be deprecated the same issue this is where it gets exciting I'm going to tell you
about some other ways we have supply chain issues now you can go in to Amazon or Asher's a virtual machine marketplace and you can download gold images for your production servers from strangers on the internet now they're not just node packages now it's your entire machine being compromised before you've even put the node app on it nothing could go wrong there could it should we keep playing this is gets really fun your chef recipes and your puppet manifest you're using to maybe in an automated fashion build your on-prem gold images there's a chef supermarket that is an open source repository of chef recipes for you to use also published by strangers on the internet what could go wrong there same game
right let's keep playing docker images has anybody downloaded an image from docker hub before has anybody actually scanned one of those four known vulnerabilities in the libraries inside of the docker image you know what I'm going to say next right strangers on the Internet okay let's keep playing there is a market place inside of AWS that lets you download web application firewall rules published by strangers on the internet and install them in your AWS laughs what could go wrong there even better service functions there is a server 'less function marketplace where I can publish my own little Python serverless function and say I promise you this is safe and you can run it and install it inside of your
AWS org it's getting kind of scary right this is what we're dealing with so our whole solution and I'm saying solution in quotes because this is not that great of a solution is at least to inventory and scan these things for known problems and what tools you use to scan with kind of depends on what the actual open source package is the app world is way ahead of everyone else because they were the first ones to kind of have fingers pointed and say don't do that so Jeremy long who was a mentor of mine started the wasp dependency check project many many many years ago that's probably your best free open source package for saying look what nodejs
packages or Java packages or dotnet packages are being referenced and then turning around and comparing those against the whole mitre CBE database to say you're referencing struts one dot X your servers in big trouble and it gives you a report that says here's what your vulnerabilities are that's kind of like prerequisite number one if you're not doing anything right now start running that that's free there's no excuse there NPM audit which basically was retired Jay s pulled into the node package manager now gives you node package auditing during your build process to say if you're leveraging packages with known issues in them and there's so many stories we could talk about here but we won't fit it in in time so maybe five
time at the end remind me to tell you the node package problem story PHP security checker same drill you can wire these into your automated builds - so now we're leveraging prerequisite number two which is automate your build pipeline suddenly use stuff in the package scanning tool right in there and you can start stopping builds if you figure out you've got some CVE with maybe a really really high score which means there's probably an exploit and exploit DB sitting there associated with it and now you know your servers in trouble so that's a screenshot of dependency check running against a Java app which explains why there are so many Seabees associated with it next up container images open source
tools for scanning your container images this is a must-do it's estimated that 30% of the images in docker hub have malware in them 30% with malware that's not the ones with vulnerable packages that number I don't know what it is it's probably up in the 90s because new CBE's come out every day and those images just sit there and get more stale over time every single day you can use a tool like encore which picks apart all the layers of your images and gives you all of the libraries with CVEs associated with it in the same fashion that is a must scan if you're using docker images now claire is another great tool i ran for a while
Claire was maintained by core OS core OS got acquired by Red Hat and then Red Hat got acquired by IBM so now it's called IBM Red Hat core OS Claire and I have no idea if the maintenance here is going to continue in the open source model or if it's going to become a more commercial kind of part of the openshift platform so Falco's another one it's got some kubernetes scanning support as well all good free open source tools for managing supply chain with container images check run one of those here's encore in a Jenkins pipeline very simple to set up go scan your base image you're going to be terrified when you see how many
results come back from a base image in this report it's shocking next up the infrastructure is code problem now we're still downloading hardened chef manifests or chef recipes and puppet manifests from strangers on the internet here these just happen to be strangers that have been very heavily vetted by the security community and the templates have been reviewed by lots of security experts in order to become part of these repositories so instead of going to the chef supermarket I would highlight this or write it down on your notebook or whatever the dev sec project is amazing this is all about DevOps in network security this is a project commissioned by Deutsche Telekom and it's got a bunch
of support just from chef in general it's got pre hardened pre-built security templates using chef ansible and puppet for linux windows ssh dr kubernetes Apache and nginx all certified ahead of time to be compliant with things like the CIS benchmark so you can go out there and say I need a CentOS 7 image compliant with CIS benchmark level 1 and download that chef recipe and now you can spin up a certified image using that code could that be any easier moving down the line a little further hardening from the sim project this is puppet specific but this is meant to actually satisfy some of the DoD regulations it was commissioned by the NSA because they
needed infrastructure is code to meet FIPS 140-2 NIST 853 deesis gig scab etc you can go download those templates from the simple project and those are sitting there waiting for you hopefully it goes without saying you still need to read these and make sure they do what you need them to do but this is a really good starting point from a compliances code perspective next up my favorite one serverless functions now it reinvent this year last year 2018 Amazon announced this new concept called layers what a layer is and the diagram kind of explains it here you've got your lambda function right here at the top and what we used to have to do is if I had a node
pack or a node function and I referenced a bunch of packages I had to do a build and zip up my code along with all of the packages and bundle it right inside of that top layer lambda function to make sure they were there at runtime what a layer provides is the ability to actually side load libraries into the execution environment so you don't have to include them all in your zip file only the function would be deployed and the libraries would already be in those layers in a shared library directory inside of your container execution environment does that make sense this is where you start thinking this through a little bit the first time I
read about it said that's cool so from a security perspective you could have a centralized layer enforce all of your engineers to use your layer and they're not allowed to include any packages on their own inside their function so you could in theory have approved these ten packages and these ten versions already from an InfoSec perspective and know I've got control over the supply chain inside of the layer kind of a cool concept right you can even have your build pipeline if it detects additional libraries that they're trying to sneak past you in the function deployment package guess what we can stop the build you have to come back through us to get your packages in
there sounds like a positive attribute right here's where it gets fun there's also the ability to create your own layer and publish it into the layers repository and share it with other AWS accounts so now you can download layers from strangers on the internet with who knows what package inside of it this sound interesting so Jared's gonna sideload his package completely full of malware and just hope that you spin that up in your function execution environment so he's got command and control back to his centralized server kind of scary right so now we've talked about a positive trait and a negative trait so you need to verify where your layers are coming from as well to projects I'll mention
the pure sec team that did the server list top ten actually published a hardening package called function shield that you can side load as a layer and what it does is it actually hardens your execution environment so it's a library that you can install you configure it in the top of your function and you can say you know what let's make the execution environment filesystem read-only so if you have an injection bug I can't write to the temp directory because function shield is blocking all right attempts to the OS that sounds like a cool feature right it also has a feature to block all outbound connections so that way Jared's malware in the other layer that you
downloaded from him on the internet makes a connection outbound to his command and control server and function shield will block that call and say no no outbound connectivity is allowed from this thing so that's a another positive on the layer side that's open source I think it protects nodejs and I think Python might be in the works I know it works across Google and AWS asher is not supported at least the last time i looked but that's a way that you can start to inject security into your function execution environments bottom ones commercial and i mentioned it because twist lock is a really good container and function security company they've got a new defender tool very
similar to function shield but if you have a relationship with twist lock already start spending that thing up because it uses layers from a security perspective to do good things protect the world right all right how much time we got nine minutes can we talk about continuous security compliance in nine minutes yeah will rip through this here's the thing everything I just described to you over the last three keys is all summarized in here you already know how to do it it's just do it so take your compliance folks introduce them to the code the version control the continuous integration tools we've talked about and start automatically certifying your environments on every release so it's
using api's who loves api's everyone should be raising their hand to this all of the security vendors that I work with at this point if they hand me a tool and it has a graphical user interface where I have to do work inside of it by manually typing things and pushing buttons I immediately in the conversation unless they offer a compatible API that does 100% of the functionality through automation that's the prerequisite to play in this world once you find the vendors that will do that then you can start to automate every single security task that you've done historically on your own manually through scripts or through the Python package or whatever you know pick your language
flavor of the month you can use whatever you want to invoke there api's then you can start to run your compliance scans this is a subset from that poster of the compliance driven tools that basically give you desired state config on your environment all of the time and if something ever deviates Jared pops your server and launches the count process which isn't normal these tools can find it they can alert you or even correct it depending on what's going on so number one in spec this is very heavily coupled with the dev sec project that i mentioned in the last section in spec is commissioned by chef it's an automated way to certify that all of the OS settings the packages
the libraries etc meet your desired state configuration if you need to bc is docker compliant on your docker host you do an inspection give it the docker profile that they have created and it gives you this big report of all passes and all failures against the CIS docker benchmark who knew compliance was so cool right I can be a compliance auditor and know nothing about compliance because that project has done all the work for me OpenScape is another freebie that is able to run maybe red hat or CentOS style benchmarks using PCI requirements using CIS requirements whatever it is is anyone used cloud custodian before this is a cloud desired state configuration policy management tool that is open source to us by
Capital One what happened is Capital One started using AWS config in the cloud for desired state configuration and they realized that it was way too expensive and they built their own tool that they could run from on-prem which is cloud custodian so this has great support from the open source community because Capital One is dogfooding cloud custodian internally to monitor all of their own cloud and then sharing it with us you write policies it's just a little yeah mole document and it says no bucket should ever have the public read at you'd set on it and if cloud custodian detects that it will alert you and if you set it up to do so kill bucket the
second it finds it and it's just continually monitoring your entire cloud for those sorts of mists configuration issues AWS very heavily supported inside of it asher and google quotes supported as experimental add-ons because they're not really heavily in those clouds yet but the community is tacking those on there scout sweet and AWS benchmark scanner just more cloud security tools that you can use to enforce continuous compliance some cool stuff there so check those out here's my docker run chef in spec baseline scan this actually is scanning a docker image for compliance against a boon to baseline so this is a way you can use then this is getting creative I love containers where I'm using a
container to stand up as an inspector scanner and then it runs a scan generates a report and then it just dies and goes away so I don't have to keep an inspect server running 24/7 but the outputs on the bottom of the slide it says Eric you failed some of the file permissions it's issues on this Etsy shadow file and it'll tell me immediately if I did something wrong with my configuration and I can stop a build potentially if I need to now that command or console output does me no good ideally I would export it and this is getting into CI and CD again to age a unit or X unit formatted XML file so
then I can get this nice pretty visualization dashboard inside of my audit pipeline so it's taking that console output and making it digestible to the tool so the auditors can look at it and say wow Eric you did some great work today and that's all you're really trying to achieve right make it simple so this game clearly is not doing well 53 passing cases on my gold image this is just cloud compliance just stacked on top of it running the AWS CIS benchmark via config to continuously evaluate cloud security compliance how are we feeling that's compliance in a three or four-minute nutshell right there from the dev sock ops perspective so that my friends is the intro or crash
course into the prerequisites the key controls for securing the modern dev ops environment a lot of work to do there hopefully I gave you at least a few resources to play with as you walk out of here at this point we've got about three minutes for anyone with questions etc I'll be hanging around to later oh
yeah there any real questions or should we tell a story stories are fun note packages by the way there's a lot of transitive dependencies associated with those so if you download a package like es lint for example you actually get like 75 sub packages inside of it there's been some problems with maintainer x' of these things kind of getting like disgruntled because you know no one's paying them to maintain the open-source version and one of the maintainer x' at one point for a node package kind of got social engineered so this is kind of cool somebody reached out and said hey I noticed the activity on your node repository kind of slowed down like are
you you know thinking about maybe just not maintaining this or do you want some help or hey I would even volunteer if you're tired of this to take over the maintenance of your project for you and then that person ended up being an attacker and they just back loaded that package with malware put it on the internet and then suddenly millions of people not downloading it directly but downloading it through a transitive dependency suddenly installed malware on their machine all over the world whoops that would never happen in real life wouldn't so just a very good example of supply chain security why it's hard to deal with I don't think will win here but we can at least control it right
yeah that's good reminder well she got bring it on you ready for lunch I understand yep find me afterwards thank you





