An Evolving Era of Botnet Empires - Andrea Scarfo
Show transcript [en]
okay our speaker this evening is Andrea scarfo security analyst at opendns 12 years ago she got her teeth as a sysadmin and now she's a malware hunter so please give a warm welcome to Andrea
thank you guys hear me okay okay yeah so the first security conference that I ever attended was actually a b-sides in San Francisco and now this is my first time presenting in at bsides again so go besides so the title of the talk in involving evolving era of botnet empires just a little bit about myself again I'm an analyst on the security research team at Open DNS in San Francisco before that I was a sysadmin for 12 years and then my free time i enjoy rock climbing playing video games and surfing in the ocean not online but I like that too so the agenda for today we're going to start with a history of botnets just uh
overview the birth of botnets move on to the life cycle of a bot highlight some botnet network architectures then move on to what a bot can do botnet functions its highlight some different malware that BOTS usually drop highlight some famous botnets some detection methods so ones that we use it open dns and then a manual analysis of a botnet domains from DNS traffic okay so to begin with what is a bot what's a botnet it's a network of computers infected with malware they're controlled as a group a bot will perform automated commands and they're controlled by a community control servers controlled by a blunt master and then in this talk we're going to focus on domains that are associated with
planets so to begin with bots we're not always malicious started out in IRC channels here's an example of a non malicious but that would you could just play a nice little trivia game with in an IRC channel and it would even serve you a cold beer so when I watched first started to move on in IRC in 1999 notable ones is called a egg drop this one was designed to control user banned lists and help prevent channel floods from happening and it actually had a feature that was called botnet and it would which linked the bots together between the rooms and you know we see that features evolved today with linking lots together pretty park I was able to
download files and execute them different IRC channels and then one of the most famous a GoBot which was one of the first customized BOTS to order so from the coder you could get a bot designed with specific exploits that you wanted when the most famous was the elsass exploit and which actually got the attention of Microsoft and law enforcement and to find the decoder so they could shut that down this is a example of a part of the code that was in a gavotte when it was first seen and the source code was actually released on the internet which led to a lot of bots barring that making them their own so it started out with just spots
participating in a targeted IRC attack so denial service attacks in channel floods in 2003-2004 there was a boost in malicious bots on on the net and they started to move away from just communicating through IRC to http just because with firewalls you could just block a ir c traffic but with HTTP it's usually always allow through a firewall so the life cycle of a bot it'll start with the infections and then spreading so infection that what they use for infection use spam so though initiate a spam campaign and send malicious attachments to to lead to the download of the bots or through injected code on a compromise website which would lead to to an exploit kit and also through
vertising so with malicious ads and then from there a bot needs to make contact with the command and control server so there's different rallying techniques that they can use less common is a static IP list in a config file on the bot just because it's easy to figure that out so they've moved away more from that to using a domain flux so through a DGA a domain generation algorithm it will produce thousands of domains based off of those dj's and then only one of those thousands will be will be used actually as the command and control server and then they'll use IP flux so they'll be constantly changing the IP that the domain is resolving to and then
from here once it makes contact it's ready to accept commands and report back so from here can be used as part of a ddos attempt it can be used to spread as a spam bot to spread more spam so further the infection and make the botnet grow larger or can just become a nympho stealer to steal from information from the machine and then the goal is to maintain that that bought keep keep it very vague detection and they'll use the same rallying techniques with a domain flux and the IP flux some of the network architectures that are used the first was a centralized command and control topology here so also through IRC HTTP there's just one command and control server
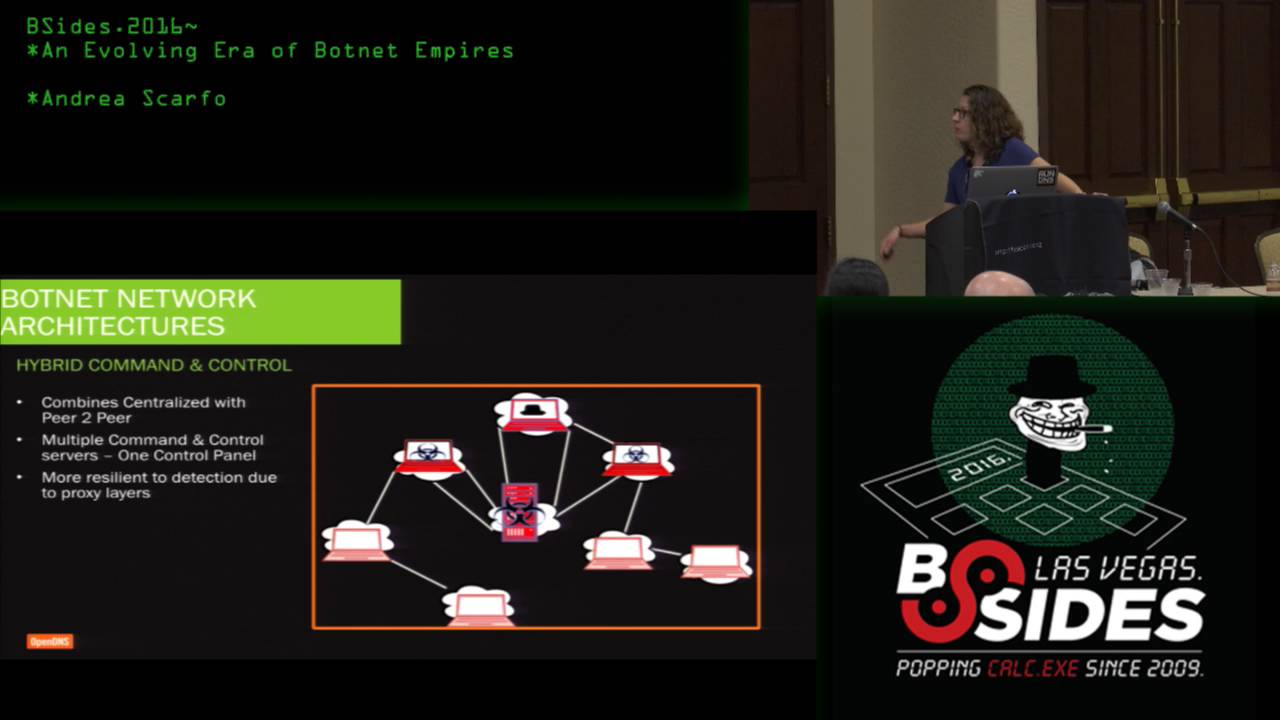
controlled by the bot master and so just that one server would send out commands and store the stolen info there next is a peer-to-peer infrastructure so the infected BOTS can share and sending the commands and the data to from the community control server and then it's using a file sharing protocols TCP UDP ICMP and then there's the hybrid one which is the most resilient and the most popular one nowadays such as combines centralized with peer-to-peer but and there will be multiple command control servers and then one control panel that's controlled through because of the multiple community control servers can act as they act as proxy so it makes it harder to detect so botnet functions
what can I bought do so I've said before you can it connect as a spambot to further infect more computers it can be a act as a forum grabber on a computer so in the config there would be a hard-coded URLs that it's going to to search for a traffic going there and then it will grab what's entered into forms on on those sites take screenshots of a machine just to grab personal data redirect HTTP traffic you're trying to go to a legitimate site and you get redirected to a fake phishing site where it can steal your credentials keyloggers to steal passwords they have VNC modules where attacker can remotely control your pc as if they're physically there and then
stealing cookies so participating in session hijacking to gain access as authorized user to a site and then the wats will after they get infection start an infection on machine they can also drop different types of malware so for again a form grogger form grabber this is an example of an old older version of droid x with pre-configured urls that's it's going to spy on we used as a trojan backdoor to intercept any network traffic the most famous right now is the with crypto ransomware which encrypts a file system and then pulls a decryption key for ransom banking trojans Mike droid x just spies on banking sessions a quick fraud bot so like the bead app
trojan just to generate revenue by clicking on ads and then of course as a dee da spot so one technique that the malware where we use once it's on a system is a code injection this screen capture here is the angler exploit kit using code injection on a compromise website and we've seen that angler exploit kit as part of the knee curse botnet so here this the screenshot captured show mean I a dll file that gets injected into the browser process and the OS sees it as as a safe process so it allows it to run and then at that point the exploit kit can take advantage of any plugin exploits that the machine has so through a Silverlight flash or
java once once to execute that code then it's going to download knickers bought on the machine and it will be enlisted into the botnet I'm famous spots dried X it uses the hybrid peer-to-peer network architecture first spotted in 2014 mostly stealing credentials to targeted banking sites today it's mostly spread through spam and embedded Word documents with malicious macros embedded originally it had a centralized network architecture switched to the more resilient a hybrid peer-to-peer a lot of numbers out there for the estimated amount stolen but 30 million is one of them and it was the target of an attempted a takedown operation in 2015 which wasn't very successful so here's an example of the different layers that are seen in the
hybrid peer-to-peer layout here the first layer is comprised of infected users computers so this is where tho except and carry out the commands the second layer will call nodes that is more infected users but these users can act as HTTP proxies and that's between the the bots and then the front-end community control servers which are next and then the proxy layer is made up of compromise servers and that's going to act as another proxy between the back end where the control panel is where all the stolen data will be held so I have a visualization a movie here using open graffiti it's an open source tool my coworker tebow can't really pronounce his last names I
won't try this tool Tebow made this tool it's a 3d data visualization so will visualize graph data sets so what you can do is take a JSON file that has the relationships of the eyepiece hashes URLs domains seen and put it into open graffiti and then we'll get a visualization here so this is showing all the relationships what the information I gave it here was see two servers at a time between twenty fifteen and twenty sixteen of the dried exponent so the blue the blue nodes are the IP addresses of the command and control server scene and then showing how they're related to urls that we're seeing and that in the orange color and then on the purple color its hashes so a
lot of these mostly just the dried x trojan and what this does it helps us see the patterns in in there under infrastructure and you can see how some of the IP addresses are related to each other through through the hashes seen and others are just out there on their own and other the ones related to have some pretty large clusters
okay another famous botnet knickers it's also a hybrid of peer-to-peer botnets so they use they also will use a dj's that they can push update through the peer-to-peer network so they can have the DJ's sign different CNC servers out through the botnet and though they'll generate a lot of these just just create noise so there'll be thousands of domains out there and they'll only register actually one of the domains the rest women would just be NX they knickers has been seen spreading locky and dried x or spam it's also been related to the angler exploit kit and just recently it's been seen as part of hosting the alert community control servers this is a new banking Trojans
estimated to have stolen 45 million dollars already so here's another visualization using open graffiti of the knickers botnet so these are the command-and-control servers that we saw and how they're related to the hashes the hashes I got from a virus total and these particular ones here are showing that they were seen associated with lurk server and beat up so both of these botnets have been the focus of some takedown attempts knickers had a bunch of their community control servers sinkhole on june first they actually went completely silent for about 24 hours and during that period 1 million host we're seeing trying to attempt to connect to the to the command and control servers they've resumed full
activity already by the end of june and are taking part in more spam campaigns with dried x so there take down the temp apt it happened in october 2015 really big refusing an activity a week later just due to its hybrid a network there so it's still spreading the tried extra trojan and it's actually been doing something new lately where it's participating in spreading of the walkie ransomware through through spam and it's usually through a javascript exploits in the email so some detection methods these are through analyzing DNS traffic so at a token dienes we see 80 plus billion DNS requests a day from the customers are using our DNS resolvers so then since we get all those requests
were able to see the traffic patterns of queries going to the domains and then we have the history of a domain so we'll be able to see the history of the ip's the domains been associated to the name servers ASNs we have a we have a tool that i use and it's called investigate so we'll use it in when we're investigating domains to see the DNS requests and then pivot off of the different data that we have that's a screen capture of it so one way one detection method is through detecting domain generation algorithms so again that's where it will use random characters and combine it with some type of dynamic component to generate just random domain names it
might be a number combined with their current time and just symbols it makes a new domain each iteration and then the purpose is so that the the bot has a way to contact the command and control server so very few of the domains are actually registered out of the thousands that it will generate just create noise makes it hard for the analyst to to know which one's actually being used but it's easy to detect a DJ domain name just by using lexical filters here's an example of some angler exploit kit DJs so here I guess so they're doing there there's a letter a number and then an animal name and these and they're all registered at
on the dot top TLD these are example of the timba banking charge and DJs so it is possible to reverse engineer the algorithm to find out what the with what the next I mean is going to be that's registered and then you can we can pre block all the all the domains and then this is an example of some beat up djs so in other ways by detecting traffic spikes in the DNS requests that we get so if there's a sudden surge of queries from the clients will see that sudden surge in a query request but you know since a sudden surge in traffic it doesn't always mean that something malicious is happening it will also run
that through other filters so looking at the domain history of it so the IP history like if there's been abrupt changes the domain has changed ip's just numerous times the query volumes that are actually coming in and then the geolocation like the distribution of the queries and then if this spike has happened before like is it a normal thing for this domain to suddenly have a spike in traffic or not so this will lead us to domains that are associated with exploit kits fishing campaigns and then help helps us find the DJ's that are associated with the botnet so once these automated tasks run then the analysts we can do a manual analysis on the domains and then we can find
additional bad domains off of the IPS associated or the name servers or the hashes that the malicious hashes as seen making a call out to those domains and then we're able to give them categorization by using all of these different indicators this is an example from investigate of just showing just a sudden spike in traffic where as there was no traffic before a sudden spike in the queries so manual analysis so here is a this domain spotted on July eighteenth so all this data here is what we've seen on July eighteenth I think it's since been sink cold after that date so we see a sudden spike in traffic here and it also hit the DGA filter just because the
lexical filter on the domain there and then an investigate I can also see that that this domain has been associated to these malicious hashes through a threat grid integration and then these hashes are are seen to be locking ransomware and then I can go then further and see the different domains that domain call-outs that the hatch actually made different network connections that attempted to make so here's an example of some more network connections that the walkie sample was seen making some dns call outs to and you can see they they also some of them look like more dgs this is just a example of currying the investigate API so it's a it's querying just a given domain and getting
back the the hashes that have been seen associated to that domain and then showing all the associated network call-outs that get made off of that malicious hash and also work more djs seen there another way is we can pivot off of the domain email registrants so we have a registrant here that scene just registering a lot of domains that are DJs all from the same email address and there also it'll show me that they're associated to other other malware attacks and then if I go through and click on those different dj's that the registrant has registered I can see some odd traffic spikes on those DJ domains so if they have a similar pattern of
spikes I can see if they're related another way is by the co-occurrences off of those domains that are all under the same registrant so co-occurrence is when a domain request two or more domains within a very short period of time like seconds so here's this DJ domain that's registered through this email address it also has co-occurrences that are more djs and then using some more some more sources I can you know look on virustotal get some P caps of network traffic that's showing more malicious activity that's seen off of these domains so I can figure out what the attack is and then lastly just connecting the the registrants through to the different attacks helps so the
email registrants associated to their attacks through them the malware so the malware will make a call out to the domains that the are associated to the email registrant and then we're able to connect them to other registrants through their domains as well so it could be dropped from one domain so its associated that way and it makes some call-outs to another domain that's a DGA registered as part of a botnet so here we've got the like knickers botnet connected through a registrant that's also spreading angler on their domains and that's it so anybody have any questions
so you mentioned that these people who write these things will register a bunch of domains for i guess like obfuscation are they actually what are they doing with these domains that that actually get in the way of malware analyzers so most of them won't actually be registered it'll be generated and like but the bots will try to make a call out to it but it's just an NX don't domain it doesn't exist anywhere so you'll see it in the DNS traffic that it's trying to connect to it but it's not actually registered it's only one out of thousands or tens of thousands
so I'm more secure if I use opendns than Google DNS block tGI's yes good point
hey thanks guys





