Security Circus

Show original YouTube description
Show transcript [en]
I really have to want to say I want to say welcome everybody for coming and we have one big announcement we're making that besides Charleston is now an official 501c3 so we are now a non-profit here in Charleston so we are very excited without take us so come give back to the community help us grow let's show people the Charleston really has some cool stuff going on with it and laughter ado I let you choose yourself because no one's teeth better about themselves in themselves oi yeah there's hey everybody I'm Kevin hi Kevin uh so uh the one problem i have is they've told me i have to stand somewhat behind the podium so I'm trapped right I'm one
of those people that I wander all off so if I wander and you're watching on the video oh well so we're going to talk about security circus this is ok so we don't talk about security circuits this is something that I've ranted about quite a bit on Twitter and Facebook and LinkedIn and you guys get to sit here in a room and hear me rant again um I feel like we as an industry are shooting ourselves in the foot and that's probably not a good idea especially since what we do is so important at least I think it is I may be biased you know I'm a greedy capitalists and my entire business depends on people
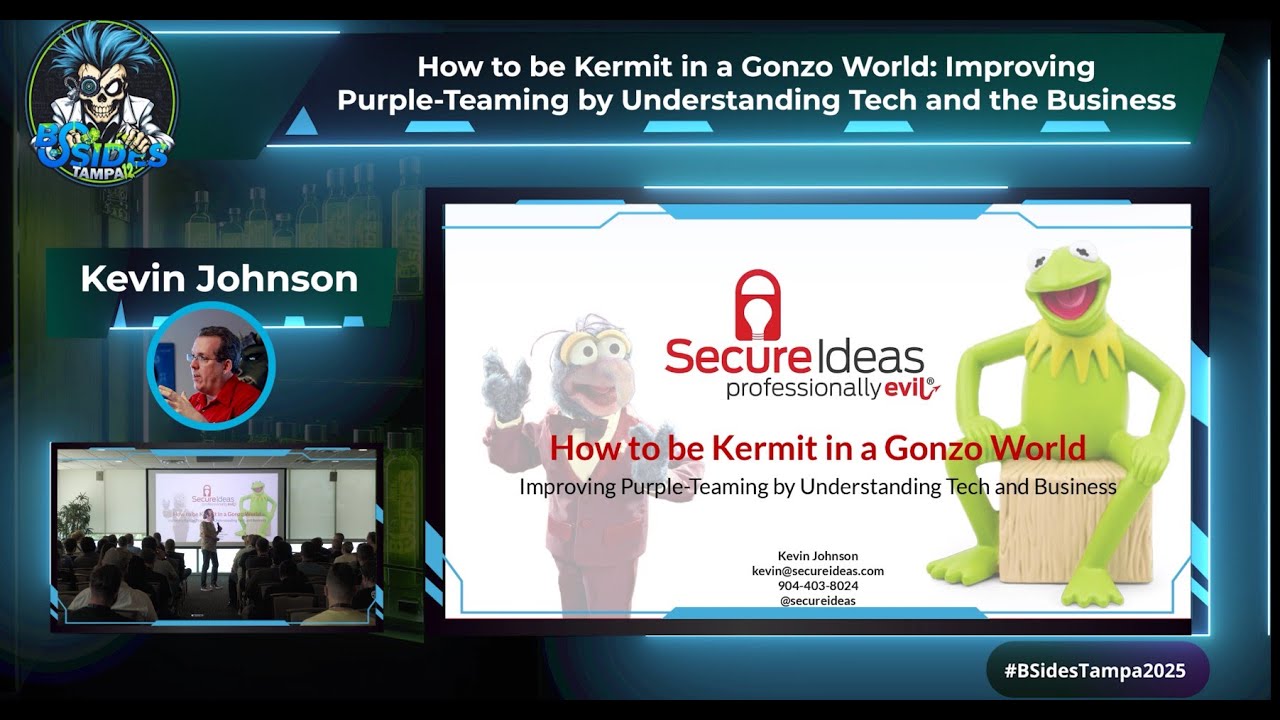
thinking what we do is important so I keep trying to push that motto so I'll give you a little bit about myself basically I'm the head nerd at secure ideas a company we formed accidentally just over five years ago was one of those things where people just kept calling and saying hey will you do this on the side and I kept saying yes my wife says I have a problem with that so uh yeah we could do that no problem I've been around the IP field for too damn long i'm an old fart i started about 25 years ago started insecurity about 15 eight years ago I became a consultant now secure idea is we do Red Team we are
part of the problem probably right our job is to come in beat you up tell you you suck and Lee it is the world's best job right people that's all the time like hey do you fix them no we pointed you in laughs but you know one of those things we also do training and all that kind of stuff I'm anions faculty member if you don't know about ions it's awesome but again i'm biased I've written a whole bunch of course where for example i wrote the web pentesting curriculum and the mobile security curriculum for sans institute that's what people yo people seem to like it you know one of the things I've been with them for about two years now
so I guess that's okay um and I have what if my wife says is the nerdiest thing I've ever done I pointed out to her that she met me when I was 26 so she doesn't know um but I'm a member of the five hundred and first we are a star wars costuming charity group so there's about 8,000 members worldwide we build screen accurate costumes hence the clone trooper helmet I didn't want to leave on the table I knew if I left it on the table like I'd look out in the audience and somebody be wearing it so I'm like okay no that's not happening Oh so we build screen accurate star wars costumes and raise money for charity we go to do
hospital visits and things like that you've probably seen us around if you've been anywhere and there were Star Wars characters there last year my understanding is we raised 12 million dollars for charity worldwide so it's one of those things where everybody laughs when you say Star Wars costuming and then you say 12 million dollars they call oh maybe that's reasonable right so and you'll hear a lot about my kids because I think that my kids are one of the reasons why security is such a big deal to me right uh being the guy who's oldest daughter who's now 13 but when she was nine her identity was stolen because the hospital she was at was
breached and they got her social security number her date of birth and everything else now of course it's okay because we got the letter that said they take security very seriously Oh which I'm sure they do right oh and they gave her a year of free credit monitoring was problem with that way she was nine she was an author I eligible to actually sign up for the free credit monitoring so that's a scam the hospital paid for a years she couldn't use it so they still got paid they still got paid right that's a business you want to do right here pay me for something you can't use thanks but oh well right but security is a big topic I
mean there are actually TV shows dedicated to what we do you know I thought we had it made when in the state of the union address they mentioned cybersecurity and yes by the way for the people who are cringing I've given up fighting on the word cyber right I I know okay coffee and uh huh right but I thought when the State of the Union mentioned cybersecurity I was like wow we're real we matter and now there's a CSI cyber which I've not seen I've heard it's awful but I mean come on we couldn't have expected much if you ever watched any of the CSI shows I believe that most investigators turn on lights in the rooms they're investigating but
for some reason in the TV show they never do always irritated me when i watch the show turn on a light you can find the evidence better but you know so but everybody talks about security everybody does oh you I knew we had a problem when my grandfather asked me about security right when my father in law is talking about malware and phishing and things like that not understanding any of it but you know he asks about it right oh by the way I gotta warn you i'm full of jokes and tangents right and full of lots of things my eyes are brown um i do want to point out i did not say good jokes i
just said i have jokes like i'm a current favorite joke do you guys know why Walmart wasn't hacked exactly it wasn't a target right I got a bucket list item I got to introduce the CIO of Walmart and I told that joke in his introduction he didn't shake my hand right like hey he went like this and walked around I whoa so but security is a big deal right everybody talks about it everybody's worried about it we have PCI you know that you must be this tall to ride the internet we have hip hop which is filled with one not too but there's also tons of issues every time we turn around somebody is announcing a new flaw right we somebody
just said it to me this morning right where an industry run by Google searches right every and I thought it was actually he's right you know that is how people find out about us and one of the things that the security field does is we try to drive as much attention in in many cases we do it in the wrong way right there's this idea that well if I hack it people will pay attention to me right if I attack that system if I find this flaw I must be important right and it's not and in the worst part is every single time we do this when we start to go after systems that aren't our systems
we don't have permission for systems that we don't control we're actually causing more problems than we're helping and that's not a popular opinion right as as you can tell by the Twitter replies when I say it right it's amazing how upset people get when you tell them that their job sucks hey what you're doing is wrong what we're all doing is wrong in so many ways and we make our jobs more difficult and one of the problems that we have to address and this is one of the reasons why stun tacking and I really don't like that term right because most stunt hackers don't have air bags and well in the Jeep they did I guess but uh sorry Charlie we
have to figure out ways to protect ourselves and protecting ourselves includes knowing where the flaws are right it's one of the problems is if I don't know where the plies how can I protect it right in the example I always give because we've done such a good job of telling people that what we do is important but we don't do a really good job of explaining why or what the threats are you know years ago I was teaching this class and I'm teaching people how to crack passwords right and I got a guy in the room and smart guy and he says to me I'm not worried about people cracking passwords but why not he
said cuz I've got the strongest password really that's awesome let's not point out the fact that he used the word password singular right so he has the world's strongest password so it says it dude I say dude way too often for someone who doesn't surf but I say dude what is it and he told me so that's a problem right and I'm like we was a four-letter word and it was a name so I was kind of like how did you possibly think that's the world's strongest password he's a Kevin I'm 52 years old and that was my dog's name when I was five nobody knows my dog's name from when I was five and you know something
we laughs right because we know what the attack is we know what people are doing with accounts and passwords and usernames but in his mind the way he understood it was it somebody was going to go I'm gonna hack him and they were going to target him and they were gonna go after his system and after his computer and after his account and while I won't sit here and tell you it was a strong password I will agree that if that was the threat if that really was the attack that's stronger than you would think right again not a strong password but stronger than you would think so i sit down i explained to the
guy nah dude that's not what it is right this is the attack we do and by the way we need to stop saying dictionary lists because they're not dictionaries their lists of strings that could be passwords and I know that's harder to say but right but the problem is people go my password is not on a dictionary it's be 45 backwards three that's me by the way capital b @ symbol 1l that's not in a dictionary but we all know it smells baseball right we all know every password cracker we use would do that password right but they don't so I'm at winning this guy and I'm like dude this isn't how it works you know we do this
this is this is how the attack works and as I'm talking about it his forehead actually started to sweat I did not know your forehead could sweat right and he got all freaked out and he ran out of the room about 45 minutes later the dude walks back in like I said way too often I say dude right it's like everybody else's um I say dude but the guys like comes back in and he's visibly shaking and a breaking point I walk out on my kilt yo can is it man you you scared the [ __ ] at him by the way pg-13 but uh he says you scared the [ __ ] out of me i
went i changed my password again singular I really yeah did you pick a good one he's like yeah I got a really strong one now and ask what is it he told me so late we fixed part of the problem right but we do so much attention on the cool hack we pull off that we don't actually explain to people what the vulnerability means what it means to them right and let's not even get started on what auditors look at right I I am so tired of writing findings that say your website doesn't have autocomplete turned off but I have to write it because all of the auditors will ding them for it but I have to then
say to the person yes I'm well aware of the fact that every modern browser ignores that setting but because you don't have it your auditor is going to have a hissy fit and if I don't write it up I'm the guy that missed a serious find it anybody let me ask how many people in the room or pen testers ever done a pen test ever done a security test right how many people in this room have ever compromised somebody because they visited a website that had autocomplete turned on anybody anybody yeah I didn't think so I'll do the Bueller thing right all right nobody I don't know anybody who's been hacked by that but pc i explicitly calls it out
what the hell right every order I've ever looked at says autocompletes on that bad really what are you done with that nothing but we worry about it we freak out about it we yell at people about it right we have to start talking about how we find the vulnerabilities how we understand them but then we start talking about what what systems do you control right do you own the system are you allowed to test the system I'll tell you right now I was doing a test for a customer i was using amazon instances and i know right amazon instances you're allowed to Penn Tesla did you have a form you have to fill out right you give
the date and where the pen test is coming from in the time frame and all this kind of stuff and you send it to amazon and amazon blesses it oh yeah so you're allowed to penn des right but didn't fill out the form because i wasn't testing amazon i was testing from amazon so if you're doing a test and of course this was a test where we were we were trying to determine if the person could detect us right after about a week and a half they detected us and they reported us amazon and i get the letter from amazon saying your instance may be compromised no it wasn't company so i was doing that right it was me before I
went back said no no it's not compromised I was doing a bend test and they right back in there like oh if you pen test amazon you have to let us know oh my gone oh different directions right i was been testing from amazon like oh no you have to let us know really okay so you got to figure out do you control it right do you own that ipod where you can root it or jailbreak it or whatever else you want to do with it right do you own that car you want to hack you know all of this stuff is things we have to talk about and if we look at we had to
have some cool logos right vota days I'd never knew we've hit the day where we needed vulnerability logos I'm waiting for theme songs would be awesome right here's cool new vulnerability sing along with me but uh all right artists needed work I guess yeah it's all the Liberal Arts degrees but they had to get logos for vulnerabilities that we start talking about old man how many people here were vulnerable to poodle everybody how many people cared yeah I didn't see him in right by the way let me ask why poodle it's not scary and I know somebody told me that poodles are really mean dogs they're just not scary looking right but okay right shell-shocked heartbleed all
these things we have devices out there now how many people here play around with the nest anybody my wife won't let me get one she said if i get 1 i'll play with it when i'm on trips and she's right i think i get in san diego turning the heat on in jacksonville right but we start seeing all these flaws when these flaws came out and started being talked about everybody everybody talked about it right oh did you hear about heartbleed yes what are you gonna do about it arnhem patch right it's what you do right oh no guys see this one I laughed my ass off of this this was headlines just a few maybe a
month ago these researchers by the way I hope you heard the italics in quotes on these researchers in the UK determined there's this kettle that it's wireless it connects to your internet and you have a mobile app two canoes are people that like tea rightly good I need to make sure my team's okay but they have wireless kettles and these researchers did some research and they determined and I know anybody who's been in the scary along the industry longer than a week will know about this vulnerability um if you d off a wireless client and then you have a wireless antenna broadcasting the SSID that wireless device was connecting to that's stronger than the antenna that's in the building
the wireless device will authenticate to the fake access point now most of us read that and go no [ __ ] but in the UK they had to research it and they published an entire paper that said oh my god RT is going to be screwed up and they did on his research and it was in the headline Brian climbing BBC had an article about it and I actually had customers called me and say Kevin what do we do about the kettle's I don't know fill them with water I like I'm not really clear how to answer that question will do you have one of these kettles on your network and one of the guys is like no like we didn't don't
worry stop reading those articles stop clicking links because you know that's what they did write it click the link it's awful but don't click [ __ ] but the one guy says to me how would I know how would you know what how would I know if one of these kettles is on my network so my only answer I come up with is walk around and listening to the steam because I'm hoping that whistle right like those details with soul look for that but I'm trying to talk to these people I'm like these is not a new fall we have known for at least 200 years that wireless access point I might be exaggerating but this isn't where the
problem is yet we got headlines I had to waste time answering questions about tea kettles because somebody thought they were cool somebody thought hey I'll get it and they did they got attention we're sitting here talking about it right but what real risk does that cattle have on you and I know I know I know I've heard this stupid-ass argument well if we can't program our kettles right how can we program anything else right and I hate to disagree I'd like to believe and I know many of my customers have proven me wrong but I'd like to believe that people take security seriously in applications that require security I honestly don't care if you can hack my
tea kettle I really don't i don't care if you can hack my nest that was the one was fun right did you remember that one about a year ago maybe they can compromise the nest how do they do it well they have to take the nest off the wall they have to flash the eeprom or some of these like they have to actually physically touch the device to load a compromise firmware onto it how about you but if people get into my house to touch my thermostat I have bigger worries right there in my house I've got better things for them to grab than a nest that they could buy right then hey we see a lot of
people talk about self-testing we should be able to test ourselves the problem is a lot of people don't know how to test themselves right how many people here and know how to run Nessus what I thought how many of you know how to validate what Nessus is doing on the script that it ran against that system fewer hands went up right how many people here know how to write their own nazil scripts to test something custom for themselves even fewer hands so we have to test ourselves and I'm picking on Nessus just because it's a well-known popular device not be a software not because there's anything wrong with Nessus right but most people don't know
how to test themselves it's because of that a lot of people like you know what for the greater good I will fuzz the internet will just attack anything we want hey the argument I've heard right from this guy how do you people know Rob right Robert Graham really smart guy really smart guy I respect this guy greatly but also point out that when shell shock came out he scanned the entire internet for shell shock and he posted this picture of a system that was vulnerable to shell shock now many of you may not recognize that that's a Wireshark window right it's got the full IP address of the device that was vulnerable and it's him running a ping
command against himself so the way he determined that the system was vulnerable is he ran an arbitrary command yes when I talked to him on the Internet by a Twitter that's the best place to have an argument um his answer was it wasn't arbitrary he meant to run ping that's what you're using you to not understand what it means right I a he's running commands on people's servers yes I will acknowledge that running a ping command is not going to hurt anybody but the guy who runs that system now has to respond right because they don't know who Robert is and even if they do even if they know Rob they don't know that all he ran was pain the other problem we
have is I said to um okay so okay we'll ignore the fact that we now have declared an instant will ignore the fact we have to do instant response we ignore the fact that many of these companies then had to hire somebody to come in and determine if the systems were compromised well let's ignore all that how do we know you didn't do worse right well because I said I didn't okay so let me ask you the next question did you tell this person they were vulnerable the shell shock you're doing this for the greater good right you're scanning the entire internet to identify where all the vulnerabilities are have you notified a single one of the systems
that were vulnerable and the answer he gave was no they should come to my website and read my blog I didn't realize you were famous right I didn't know that paparazzi followed you around that everybody knows you because that's the attitude right if you don't look at my site if you don't read my blog if you don't know what I'm doing then that's your fault not mine we're not doing this for the greater good in the most cases this is an industry circle jerk we all like to sit around and tell each other how cool we are this is what I did today what did you do today oh I'm a badass i scan the entire internet screw you
hippie right that's not the way to do it and we start seeing things if I can hit the button Jess remember this one a researcher in Turkey took down the apple developer Network right he'll remember because it was down we week and a half almost two weeks right did not have access to it I know this because I was testing some iOS apps during that time and couldn't get to the documentation that i was trying to research to help my client better develop their software because the apple developer network was down pissed me off right this guy he's like I wouldn't you know you talked to him when you talked him on Facebook or Twitter or wherever
his answer was well my hero Apple shouldn't have been vulnerable okay you're right that building shouldn't have been flammable um and his answer was was okay well fine they should have been vulnerable I'll agree with that but why did you pull 100,000 records I had to prove the vulnerability existent my answer that is [ __ ] glad you pen tense all the time and I don't pull 100,000 records to prove the sites vulnerability co-injection I don't have to i can run a count of the records i would have pulled and tell my customer i could have pulled a hundred thousand records right well i can show them look I do this this this this the error
message changes you're vulnerable now I'm not saying that I don't go and pull data if it's in the rules of engagement and it's within scope I will pull data I'll pivot through that sequel server Microsoft's or whatever right to get onto the internal network if that's in the rules of engagement you know there's this paper that has a signature this is I'm not going to jail for doing this it's a nice paper to have right this guy didn't have it you didn't need to pull a hundred thousand records to prove it he had to pull 100,000 records so he could do a cool blog post and get attention that's why he pulled a hundred thousand
records right but don't worry he posted this on Twitter Apple this is definitely not an hack attack I am NOT an hacker I do security research here's my youtube video now couple problems with this will ignore the grammar he's from Turkey I'm assuming English is in his first language right um but one problem I'm not a hacker it's amazing last night I robbed a jewelry store I gun on the guy who said don't worry I'm not an armed robber he still gave me the money you can't self-identify as safe you say a hundred thousand records guess what you are a hacker this is a hack attack you may not be malicious you may just be stupid right the other problem
with this is Apple is following this guy least according this guy because he didn't tag them in the tweet his assumption is he is so important that Apple follows him right no they don't they don't follow any of us probably right except for Bill everybody follows bill yeah no Chris you know he had to prove it further Google Play crashed right after that twice wasn't enough to crash at once he had to do it twice why cuz he had to prove it was real no again all you're doing is dick waving I mean all it is on bigger than you are hahaha look what I was able to do I'm sorry this is why we have a stereotype that we
live in our parents basement any pizza and can't get dates and that's a stereotype I'm not saying it's true but this is why because we do stupid [ __ ] like this and we encourage it right I'll guarantee you that there are people up on this slide their images up on this side that you look at and go [ __ ] and there are also people up there that you look at and going yeah he's awesome right personally we've that's the first one for me right is just my opinion not saying it's yours right my opinion I immediately think [ __ ] the gesture i live in coke yeah do it stay frosty right but the reality is there's not
much difference between either of them from a perspective of what they're accomplishing right there different people they have different personalities and gesture of course is an entire nation state in and of himself my opinion right but we look at these things anonymous how many people here look at a naught amiss and go yeah that's a good thing right the one that ideas came out with that they just came out with writers are releasing KKK members I don't know many people who can look at the idea that we're outing clan members that are in positions of power and think to ourselves you know those poor clan members that's so sad nobody says that accept clan members right most of us I
hope look at and go yeah shoot him racism shocks and I say that is a white guy right but the reality is most people go yeah that's fine go out out clan members that's a great idea well except you know a week before they were supposed to release it another [ __ ] released a whole bunch of other names of people and pretended to be anonymous because you know how your anonymous you say you are right who's in charge of anonymous nobody so a guy releases a list of names a whole bunch of the names that one of them was a Hispanic mayor over in like LA or something like California la is if it's a entire state
oh right Southern California Jesus according to the people who talk about it she's this wonderful lady and I don't know about you but I don't know many Hispanic clan members right I just it's a guess but she was out it is a clan member and she puts it like supposed to the city of course my favorite part was she said in her post right please take this down you know that doesn't work Barbra Streisand it doesn't happen but that got released that way the same group Anonymous and I'm well aware that like I said anybody can be a member of anonymous for awhile they were releasing undercover police members names addresses and phone numbers and I don't care what your
opinion of the police are it's probably not a good idea I have a friend whose husband was a cop it was a detective his name was released by anonymous there were people showing up at her house there were people banging on the door throwing stuff at windows and she's there alone right because he's on shift he's working so the question becomes is that okay right and I don't know the answer I really don't know the answer I can't sit here and say I'm okay without in clan members I'm not okay with outing police officers so some of the times you're decent how does that work what's the morality we've decided on what's the ethics we've decided on right so what do
we do as people now I'll be very clear I'm not going to talk about what do we do as researchers because i think the researcher title is [ __ ] most of us who call ourselves research to researchers are wrong we're not doing the research most there is no research necessary to understand that putting a single quote in that form field called a sequel error that's not research we've known about sequel injection for 90 years right again small exaggeration may be right that's not research that's not how research works research is finding a cure for cancer right researcher research is finding a brand new classification of vulnerability that nobody knew existed that's research running messes or acunetix against a
website is being a script kitty says the guy who regularly gets emails for my website because some [ __ ] ran acunetix against it right enjoy yourselves that's not giving you permission to do it you probably want to piss off a pen testing company just an idea if you want to have fun go click on exploit securities com and run every single thing it tells you to but so I'm not going to talk about what to do as researchers because in my opinion you're not researchers I get it we want to find vulnerabilities and I have no issue with that I have no issue with buying a piece of software and testing it yourself in
your own lab I have no issue with buying the car and testing it yourself in your own lab your system okay but what do we do is the people who have to respond to this what do we do is the people who have to manage the systems that are under attack and how do we determine that the guy from turkey isn't a hack attack as he put it how do we keep track of that how can we possibly determine that and I'll tell you that in most industries are saying that it's probably Rob is not enough when we go to management it's not enough when we go to the auditors it's not enough when the
next breach happens and they say why didn't you respond to the previous one I assumed it was robbed why that's what he does right I know his IP address he's a 127 dot five dot five dot six right it's an evil hacker at that IP address so what do we do there's number of options this of course is the first option I don't recommend this one right panic run around screaming yeah what attack shut off the internet it's always my favorite don't worry we have the darknet I couldn't do it with this very face I Drive don't knit that's when you browse the internet with the lights off yeah like blind single injection its sequel injection but you keep your eyes
closed but so panic right runaround threat this is what our management does how many people here have worked for an industry a company and had the owner of the company or management come to you and say are we vulnerable to something right my old boss might poor always tells the story where he was there in this general walked in and the general said how many false positives did we see today and he's like I'm ten right whatever the number was good how many false negatives did we see none good right because it you see the false negative it's not a false negative anymore just where it is it's like that vendor you guys remember the vendor that
used to advertise I don't know the name of them- day protection here's know they had t-shirts they said negative did you remember the vendor who it was oh I mean we got to pick on them because i like i love it right zero day we all agree that a zero-day is a vulnerability that exists there is no patch for right that's a zero day but one definition of a zero-day so a negative day would be a vulnerability that doesn't exist pay me money I guarantee you I will protect you against all non-existent vulnerabilities and the best part is it's agentless its cloud-based awesome right done if you're not vulnerable to attack I will protect you against that attack right that's
what the vendor was basically announcing total different story right but we could panic not a good idea we could deny the problem can anybody say Cisco Rick fire OTT no it wasn't us we weren't hacked but picture for the people who don't know is Barbra Streisand's house so it started the whole Streisand effect I actually didn't know what the story was I've used the term Streisand effect forever and never knew the story until I was writing this talk I actually went out and researched it turns out some guy got in a plane and he photographs the entire coastline of California and he posted it online right and Barbra Streisand or parva Streisand people right somebody associated with Barbra
Streisand said take that picture down that's her house we don't want people seeing it on the beach boats see it right so they asked her to take picture down before they asked them to take the picture down according to the website six people had viewed that picture four of them were her lawyers or two of them by the way wait one or the other for two or her lawyers before the cease-and-desist strengthened before the takedown notice after that well it's in my presentation right like everybody when I want to see that picture what is it what's going on right it's the striatum at the movie you say don't don't look over there I'm actually trying to figure out what kind of thing
could we tell people to stop talking about secure ideas just to get us attention right like that's marketing but that's what I have a barber's fries han fire i did it how many people here remember the black hat pictures and videos of Cisco ripping pages out of why I swear that's why black hat doesn't give printed manuals anymore right but there's video of the cisco people ripping pages out of the the conference guide how many people here saw that talk after that right i got copies of this stuff aaron's be more like I've got one without the pages ripped out it's worth money right put him on ebay and stop it was crazy but it got more attention to
the vulnerability then letting the talk run would have gotten the same thing how many people here remember when Ashley Madison got hacked right what was actually Madison's first response we won't hacked that's not our data that is right it is your data oh yeah well maybe we were hacked but it wasn't that bad well it was all our data yeah okay so it was bad this is the process people go through either go back when I worked in guardians right Dan Kaminsky got hacked guys remember one day in Kaminski got hacked we ran into a problem that one of our owners Jay actually use one of the end servers to do a pen test of one of our customers
and he hadn't cleaned up after himself and I'm not revealing its in the dude the informations available right and so when they dumped dan kaminsky servers there was a whole bunch of information about one of in guardians customers right oh [ __ ] when we do the first reaction when should we tell me what sauce know our name is right there all right I listen if I can't do that enemy let's be honest it wasn't a serious conversation about should we not tell them right but then what you have to do is you have to respond right because no matter what you do people are going to talk about it people going to out it
people on a spur on Brian Krebs is going to have an article about it and by the way Brian crab should not be your intrusion detection system right I mean I know companies to do it right Brian will tell us if we get hacked Scott like I worked at this company that owned a nameless blue cross the Florida and two groups of FBI agents showed up on the same day to arrest people they met in the parking lot when group is bringing the guy out / parking him right I was one of the people walking out with them I was not the purport person just to be clear right as well walk it out another
group of FBI agents walked in hey all we got this guy what are you guys are we getting another guy is this is weird cut we should have carpet but both cases Blue Cross had no idea this was happening it was FBI IBS right that's not how you want to run so you want to be able to respond you want to be prepared you want to know who is going to respond what is your answer are you going to do a press release do you do you know who gets to talk about it and oh by the way if you're the people that have the sequel injection fall in your website do you have clear lines of
communication from the outside world good friend of mine Tom Liston runs a honey pot it's really fun because everyone saw I log into it and leaving messages but I keep threatening to out the address of his honey pot in one of these talks but it's not today but right and Hugh reaches out to companies all the times is hey your website is been hacked it's hosting cialis ads which I don't know anybody who buys cialis from a website I or anybody buy cialis now it doesn't matter but I told you 10 I never understood the cialis ad the two tubs if the cialis is doing its job which might be the same tub I don't know but he
contacts people all the time and people say to him my web sites not hacked no no it is right I'm on it right now it's posting malware it's doing that no don't you think my admin would let me know if it was hacked no because they don't know right this is part of the problem you need to know who to contact do you have an abuse act do you know how much it pisses me off every time i go to look at a domain it's got a private registry i'm sorry you're not that important get a spam filter because there who is registry is for me to be able to reach out to the person in charge and say
you've been screwed here's how you fix it but instead i got the private registry i get to email godaddy who never forwards on anything they say they do you pay for them to may be right and then we need to start improving we need to start fixing this stuff do you know which it irritates the piss out of me to test the same site every year and just basically change the date on the report you'll have hold ability i told you about 10 years ago you're still vulnerable to it you know when i told you you need an abuse that contact and you still don't have one or it goes into an empty mailbox that nobody checks you
open that email box up lately how many messages are in it right we need to start getting better we have to become part of the business right if we're not part of the business if we're not truly understanding what's going on with the business we can't possibly truly give them recommendations on how to fix it about to see researchers doing that I'd like to see more researchers looking at defense right let's talk about how to fix things let's talk about how to stop things let's talk about how to make things better because as I said when I started this talk and I mean this with kids my daughter Brenna is going to grow up with a life of having other people
have her identity for the rest of her life she's going to have to deal with the fact that other people are using her social security number why because a hospital screwed up we can't fix all the screw-ups let's try to get better at it let's make it a little bit harder for the attackers right when Gil and I are sitting there and we get domain admin rights on your network from the internet in 37 minutes you suck let's make it two hours okay it's something I don't know let's do something better let's start building out some standards right I actually think we should start licensing I know it's not a popular opinion but how many people let me ask how many
people have ordered a fast-food job Jeff to pee in a cup yeah I almost every fast food restaurant I've ever sort that I had to go pee in a cup right how many people here do serious security work how many of you had to pee in a cup for your job a couple few not many right how many people went through a background check right did they tell you the results what were they looking for we the customer come to us once and say hey do you drug test your people and our answer was no we don't why because I don't want it right I trust my people they said we'll do this job you have to drug test your
people I'm like okay so we said fine we call the drug testing company we had to look them up Google right call the drug testing company they're like what do you want to test for Mike drugs right and the country's like whoa which drug test and like [ __ ] i don't know if i called the customer up hey what drug test should we be doing their answer was we don't know what do you mean you're the one requiring it so my drug test was easy what kind of drug is a white powder you snored up your nose anybody you pass the drug test right that met the standard the customer had that's a problem right we need to build up
awareness we need to have people understand what the flaws mean we need us to understand what the flaws mean we need to be aware of how the business works and how it impacts things we have to have a true understanding of this stuff and then finally bug bounties how many people here have a bug bounty at their company nice let me ask you question I'm put you on the spot you raised your hand and by the way you're the only person in the room raised your hand let me ask you a question how much security testing do you do for your company good how well do you fix things you find good you deserve a bug bounty
program if you have a bug bounty program and I find cross-site scripting in the search box in your website you fail a bug bounty program should be I have a built well done security process now let's go see what else we missed a bug bounty program should not be the first step right too many companies do it we have a bug bounty program really what other security do you do when we accept submissions no no other security right what's your sdlc what is your monitoring process do you have a handle on what systems are even on your network right start looking for real security before you start doing this kind of stuff and then go do this kind of stuff right but
if you're not doing security well at the beginning why bother with this hell let's be honest if you're not doing security well in the beginning why even hire a pen tester right if I come in and I find vulnerabilities if I find ms 08 06 7 on your network right you've wasted your money and time hiring me right because you should be able to find that yourself you shouldn't need somebody like me right so that's my rant for the day you know I hope you guys have a great conference and I really want you to think about how do we do better how do we as an industry find vulnerabilities find out where the weaknesses are but do it in a way that
we're not screwing the entire world for our own edification right that's all I want to know so thank you very much everybody enjoy yourself
really